Create a function that takes one, two or more numbers as arguments and adds them together to get a new number. The function then repeatedly multiplies the digits of the new number by each other, yielding a new number, until the product is only 1 digit long. Return the final product.
Q: Write LDA Tuning code Finding the Optimal Number of Topics?
A: Finding the optimal number of topics in a topic model is tough, given that it is like a model…
Q: Why is it so important for systems analysts to keep track of end users' requirements?
A: Introduction: Understanding user requirements, as well as system design, is critical to the success…
Q: What tactical options do you have for the development of older systems? When would you choose to…
A: Start: A legacy system is a functional system that was created, put into place, and deployed in an…
Q: Why may it be so challenging to distinguish between the three fundamental types of software…
A: We need to discuss, why is it challenging to distinguish between the three main types of software…
Q: What exactly is a poison packet attack and what happens during one? Give two examples of this kind…
A: In a DNS cache poisoning attack an attacker takes advantage of flaws in the DNS protocol to load bad…
Q: How effectively are servers, desktop computers, and laptops protected from network threats under the…
A: perimeter firewall for networks Stumbling blocks at the perimeter regulate how system activity flows…
Q: Why is security considered to be a more challenging system challenge than safety?
A: Both safety and security are requirements for the system, but when we compare the two, security is…
Q: Their definition and explain little bit. (professional ethics).
A: BOT: Definition: It is a software program that performs mechanized, automated, and pre-characterized…
Q: In your packages, why would you want to add javadoc comments?
A: Javadoc:- Javadoc is a tool which comes with JDK and it is used for generating Java code…
Q: Where are the alleged advantages of 5G compare to those of a 4G network?
A: Definition: A wireless technology that referred to as 5G and is in its fifth generation and was…
Q: Which three types of physical media are most often used to connect devices?
A: The question has been answered in step2
Q: What is World Wide Web
A: World wide web: It is also known as web. World wide web is an information system which enables…
Q: What are the many dangers that need to be taken into account while creating a resilience plan? Give…
A: Strategies of A Company: A strategy is a long-term plan that you create for your company to reach…
Q: Distinguish the following concepts: Earliest start time (ES) vs Latest start time (LS)…
A: Earliest start time means the earliest point of time at which a task begin in the schedule. Latest…
Q: What different logical layers can an application with a distributed client-server architecture have?
A: Given: The client-server architecture is the most common distributed system architecture which…
Q: The distinctions between a GPU and a vector processor and how they function will be discussed in…
A: GPU: A device known as a GPU processor is one that can execute a single instruction on multiple data…
Q: You've been tasked with creating and giving a presentation to a non-technical management to support…
A: Given: Given that we have been asked to prepare and deliver a presentation to a non-technical…
Q: Problem 2 Program to compute for the bill: An inn charges for room use (per night) at PhP 500 per…
A: Programming language:- Computer instructions are the main component of most programming languages.…
Q: What are the two most popular storage device kinds and how do they vary from one another?
A: Data Storage on Computers: The term "storage" comes from the field of computer technology and refers…
Q: According to us, the service model of a network layer "defines the characteristics of end-to-end…
A: We need to discuss the role of network layer.
Q: What is the use of boot block?
A: A boot block is a region of a hard disk, floppy disk, optical disc, or other data storage device…
Q: Given the SampleClass, what is the output of this code segment? SampleClass s = new SampleClass();…
A: 1) Code segment in question does below activity It defines a class SampleClass with two methods…
Q: What kind of memory is being utilized for the main storage?
A: Information Storage: A computer storage device is a component of a computer where data may be saved…
Q: What feature unites all architectural designs geared at delivering software fault tolerance?
A: According to Wikipedia, "a set of design principles that govern the kinds of modules and connectors…
Q: The development of the control software for a radiation treatment system used to treat cancer…
A: According to the information given:- We have defined the development of the control software for a…
Q: The development of the control software for a radiation treatment system used to treat cancer…
A: Radiation Treatment : Intense energy beams are used in radiation therapy, a sort of cancer…
Q: Give an example of how you would verify a password security system for a software you have built.…
A: Given: The project is a security system that provides password-protected users with only permitted…
Q: 5. What are the allocation methods of a disk space?
A: Introduction : What is Disk Space : Disk space is the amount of storage space allocated by a web…
Q: As a software project manager for a business that specializes in creating software for the offshore…
A: To suggest establishing a program to analyze the maintenance procedure and determine the suitable…
Q: notation). What is the range of block?
A: The answer is
Q: List the benefits of reusing software, and why should the expected lifespan of the program be taken…
A: We need to discuss the benefits of reusing software and why the expected software lifetime must be…
Q: What LAN security procedures are currently in place? Give four instances, each accompanied by an…
A: Introduction : What is LAN : A local area network (LAN) is a group of devices that are connected in…
Q: What are the structures used in file-system implementation?
A: For the purpose of implementing a file system, many on-disk and in-memory configurations and…
Q: What steps should you take to create a threat model?
A: The answer for the above mentioned question is given in the below steps for your reference.
Q: What are the two most popular storage device kinds and how do they vary from one another?
A: Information Storage: Information retention is referred to as storage in computer science. Data is…
Q: uery may use any one of six LINQ operators
A: Let's see the solution.
Q: software engineers who define and implement safety-related systems be cre sed in any way? What…
A: Let's see the solution.
Q: Why is security considered to be a more challenging system challenge than safety?
A: In system point of view security is most important than the safety because every bit of data in…
Q: What other kinds of computer hardware are there?
A: Computers have brought revolution in this 21st century.
Q: 12.Define rotational latency and disk bandwidth.
A:
Q: In your packages, why would you want to add javadoc comments?
A: Computer programming: Is the process of creating and implementing an executable computer programme…
Q: How can class fields be protected against unintended alteration is the question.
A: Introduction: Computer security is safeguarding a computer's hardware and the information it stores.…
Q: Briefly respond to the following question. What advantages does ECC have over RSA in terms of…
A: Elliptic-curve encryption (ECC) Despite being effective, elliptical curve cryptography is a…
Q: What is cyber security? What are the many sorts of cyber-assaults?
A: Cybersecurity is the protection of internet-connected systems such as hardware, software and data…
Q: What other kinds of computer hardware are there?
A: These question answer is as follows
Q: What Presumptions Apply to Cybercrime?
A: Assumption 1: Digital privacy may be maintained inside organizations. When it comes to the prospect…
Q: What will be the next malware and virus dissemination method that takes use of people's curiosity?
A: Cyber attackers use malware to infect computer systems by exploiting their security flaws. Human…
Q: Which of the following loT device features allows for remote control, programming, and power-off?
A: Internet of Things (IoT): IoT is a system of interconnected computer devices capable of completing…
Q: It is theoretically possible, when using model-driven architectures, to create functioning programs…
A: To go through some of the present issues that prevent fully automated translation tools from being…
Q: The Dirtcheap Software Company is planning to produce an assembler for a computer with a 48-bit…
A: An assembler is a kind of computer program that takes basic computer commands and…
Type in js
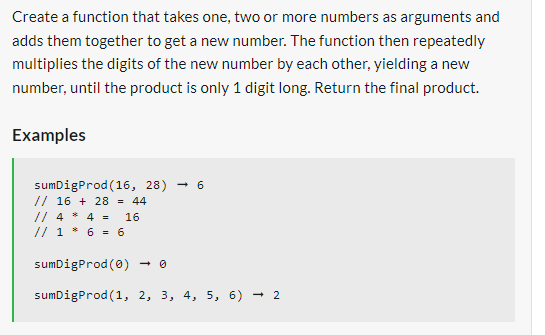
Step by step
Solved in 4 steps with 2 images

- (Numerical) Write a program that tests the effectiveness of the rand() library function. Start by initializing 10 counters to 0, and then generate a large number of pseudorandom integers between 0 and 9. Each time a 0 occurs, increment the variable you have designated as the zero counter; when a 1 occurs, increment the counter variable that’s keeping count of the 1s that occur; and so on. Finally, display the number of 0s, 1s, 2s, and so on that occurred and the percentage of the time they occurred.‘Write a function get_names(), which prompts the user for a sequence of names, where each name can contain an arbitrary mix of uppercase and lowercaseletters and space characters, until the user enters "exit". The function should then return a list of capitalized names, whith no leading or trailing space, and with‘one space character separating adjacent words, Write a main() function to test the get_names() function. For example: Enter a name (exit to stop): bill clintonEnter a name (exit to stop): john tigER sMith Enter a name (exit to stop): mary beautiful Graceland Enter a name (exit to stop): exit [Bill Clinton’, “John Tiger Smith’, ‘Mary Beautiful Graceland’ ]Create a function sumofAllOdd(s,e) that will return the sum of all odd numbers in a range of inputted numbers s (starting number), e(ending number). For example: Test Result sumofAllOdd(22,55) sumofAllOdd(5,10) Answer:(penalty regime: 10, 20, ... %)
- Toll roads have different fees at different times of the day and on weekends. Write a function CalcToll() that has three arguments: the current hour of time (int), whether the time is morning (bool), and whether the day is a weekend (bool). The function returns the correct toll fee (double), based on the chart below. Weekday Tolls Before 7:00 am ($1.15) 7:00 am to 9:59 am ($2.95) 10:00 am to 2:59 pm ($1.90) 3:00 pm to 7:59 pm ($3.95) Starting 8:00 pm ($1.40) Weekend Tolls Before 7:00 am ($1.05) 7:00 am to 7:59 pm ($2.15) Starting 8:00 pm ($1.10) Ex: The function calls below, with the given arguments, will return the following toll fees: CalcToll(8, true, false) returns 2.95CalcToll(1, false, false) returns 1.90CalcToll(3, false, true) returns 2.15CalcToll(5, true, true) returns 1.05 need help with code in c++Write a function NumberOfPennies() that returns the total number of pennies given a number of dollars and (optionally) a number of pennies. Ex: 5 dollars and 6 pennies returns 506. #include <iostream>using namespace std; void NumberOfPennies(int NumberOfDollars, int NumberOfPennies){if (NumberOfDollars == 1) {NumberOfDollars = NumberOfPennies * 100;}}/* Your solution goes here */ int main() {cout << NumberOfPennies(5, 6) << endl; // Should print 506cout << NumberOfPennies(4) << endl; // Should print 400return 0;} Please help me with this problem using c++.Write a function which will take 4 arguments. They are: starting value(inclusive) ending value(exclusive) first divisor second divisor #First task is to take these arguments as user input and pass these values to the function. #Second task is to implement the function and find all the numbers that are divisible by the first divisor or second divisor but not both from the starting value(inclusive) and ending value(exclusive). Add all the numbers that are divisible and finally return this value. Print the returned value in the function call. Input:104047Function Call:function_name(10, 40, 4, 7)Output:210
- Write a function that asks the user for their birthday month and day and then the function should call a nested function to find out the person’s zodiac sign. Test your program with some user input. Aries: March 21 - April 19 Taurus: April 20 – May 20 Gemini: May 21- June 21 Cancer: June 22- July 22 Leo: July 23 – August 22 Virgo: August 23 – September 22 Libra: September 23 – October 23 Scorpio: October 24 – November 21 Sagittarius: November 22 – December 21 Capricorn: December 22 – January 19 Aquarius: January 20 – February 18 Pisces: February 19 – March 2014. In written text small numbers are often written out, e.g. you'd write 'I have twobrothers and one sister', rather than 'I have 2 brothers and 1 sister'. Here we want toimplement one (1?) function that helps us realize this. Write a function smallnr() thattakes a number x and if x is an integer between 0 and 6 it returns the name of thenumber, otherwise it simply returns x as a string.>>> smallnr(2)'two'>>> smallnr(0)'zero'>>> smallnr(7)'7'I JUST WANT TO MAKE SURE IF MY HOMEWORK ANSWERS ARE CORRECT C++ HOMEWORKS Write the program Write a function to output a pyramid like this * *****. ********* Answer: #include <iostream> using namespace std; void printPyramid(int n) { for (int i = 0; i < n; i++) { for (int j = 0; j < n - i - 1; j++) { cout << " "; } for (int j = 0; j <= i; j++) { cout << "*"; } for (int j = 0; j < i; j++) { cout << "*"; } cout << endl; } } int main() { printPyramid(4); return 0; } Write a function to count how many numbers in one string.. Answer: #include <iostream> #include <string> using namespace std; int countNumbers(string str) { int count = 0; for (char c : str) { if (isdigit(c)) { count++; } } return count; } int main() { string str = "Hello, World,…
- PYTHON!!! Write a function that receives 3 assignment grades, a1, a2, a3, and a final grade, f, for a student and returns the corresponding letter grade of the student. The weights for the assignments and the final are 0.2, 0.2, 0.2, and 0.4, respectively. You can use the following table for matching grades to letters: 95-100 -> A1 90-94 -> A2 85-89 -> A3 80-84 -> B1 75-79 -> B2 70-74 -> B3 65-69 -> C1 60-64 -> C2 55-59 -> C3 40-54 -> D 0-39 -> F For example, compute_letter(80, 60, 40, 70) returns "C2" because 80 * 0.2 + 50 * 0.2 + 40 * 0.2 + 70 * 0.4 = 62 and 62 corresponds to C2. Note that, you are expected to do rounding. For example, 39.4 is F, whereas 39.5 is D. You can use the builtin round() function for this. Please google this function and learn how to use it. """ def compute_letter(a1, a2, a3, f):NEED HELP WITH THIS import random print(random.randint(1,6)) #prints a number between 1 and 6. #or: x = random.randint(1,6) print(x) #prints a number between 1 and 6. write a python program that simulates a game with two dice roll based on their sum and value. Your program should: Define a function try_your_luck(dice1, dice2) that takes two arguments i.e., the numbers generated by randint() function (use randint twice). The random numbers should be passed to the function as argument The player wins some money, when: a. Sum of both dice is divisible by three, player wins $5 b. Same number on both die, player wins $10 c. For all other cases, print "try again" Player loses the game, when: a. Sum is greater than 10 and odd b. Sum is 7. Display an appropriate message for each case (player wins or loses).Write a function convertQuartersToDollars that has the noOfQuarters, noOfDollars, and remainingCents as formal parameters of data type int. The noOfQuarters is the number of quarters to be used to calculate noOfDollars, the number of dollars that the total number of quarters can be converted to, and remainingCents , the remaining cents. The noOfDollars and remainingCents are returned from the function,



