Create a function(or you can do this on your main function) that users input a string, interger1 and integer2 (index, length) and output the substring based on index and length. For example the user will have to put Example1) hello world my friend, 14, 7 have to output friend" (you can ignore") Example2) hello world my friend, 0, 5 have to output 'hello' (you can ignore") Example3) hello world my friend, 14, 15 have to output' friend' (you can ignore")
Create a function(or you can do this on your main function) that users input a string, interger1 and integer2 (index, length) and output the substring based on index and length. For example the user will have to put Example1) hello world my friend, 14, 7 have to output friend" (you can ignore") Example2) hello world my friend, 0, 5 have to output 'hello' (you can ignore") Example3) hello world my friend, 14, 15 have to output' friend' (you can ignore")
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter6: User-defined Functions
Section: Chapter Questions
Problem 17SA: Write the definition of a function that takes as input two decimal numbers and returns first number...
Related questions
Question
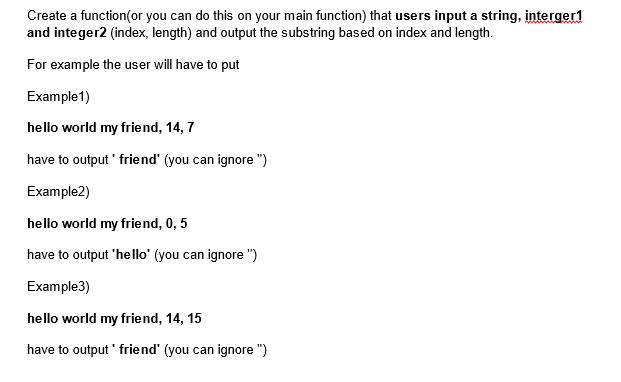
Transcribed Image Text:Create a function(or you can do this on your main function) that users input a string, interger1
and integer2 (index, length) and output the substring based on index and length.
For example the user will have to put
Example1)
hello world my friend, 14, 7
have to output friend" (you can ignore")
Example2)
hello world my friend, 0, 5
have to output 'hello' (you can ignore")
Example3)
hello world my friend, 14, 15
have to output' friend' (you can ignore ")
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr