create a Java Complier that does the following
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter2: Problem Solving Using C++using
Section2.3: Data Types
Problem 1E: (Practice) Determine data types appropriate for the following data: a. The average of four grades b....
Related questions
Question
I need to create a Java Complier that does the following in the picture provided below. It needs to be capable of solving all of the steps. Please post the results and give me an original answer.
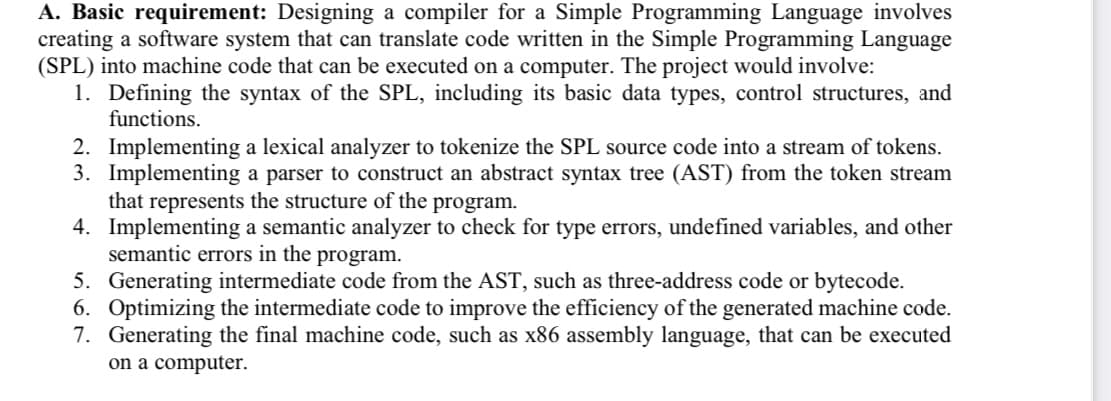
Transcribed Image Text:A. Basic requirement: Designing a compiler for a Simple Programming Language involves
creating a software system that can translate code written in the Simple Programming Language
(SPL) into machine code that can be executed on a computer. The project would involve:
1. Defining the syntax of the SPL, including its basic data types, control structures, and
functions.
2. Implementing a lexical analyzer to tokenize the SPL source code into a stream of tokens.
3. Implementing a parser to construct an abstract syntax tree (AST) from the token stream
that represents the structure of the program.
4. Implementing a semantic analyzer to check for type errors, undefined variables, and other
semantic errors in the program.
5.
Generating intermediate code from the AST, such as three-address code or bytecode.
6. Optimizing the intermediate code to improve the efficiency of the generated machine code.
7. Generating the final machine code, such as x86 assembly language, that can be executed
on a computer.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr