Create a State Machine Diagram for a “Prescription” (The class that represents the prescriptions that customers must upload if they are buying prescription-required medication).
Create a State Machine Diagram for a “Prescription” (The class that represents the prescriptions that customers must upload if they are buying prescription-required medication).
Principles of Information Systems (MindTap Course List)
13th Edition
ISBN:9781305971776
Author:Ralph Stair, George Reynolds
Publisher:Ralph Stair, George Reynolds
Chapter12: System Acquisition And Development
Section: Chapter Questions
Problem 3TA: You and your team have been hired to perform a system investigation for a fast food restaurant that...
Related questions
Concept explainers
OOPs
In today's technology-driven world, computer programming skills are in high demand. The object-oriented programming (OOP) approach is very much useful while designing and maintaining software programs. Object-oriented programming (OOP) is a basic programming paradigm that almost every developer has used at some stage in their career.
Constructor
The easiest way to think of a constructor in object-oriented programming (OOP) languages is:
Question
Create a State Machine Diagram for a “Prescription” (The class that represents the prescriptions that customers must upload if they are buying prescription-required medication).
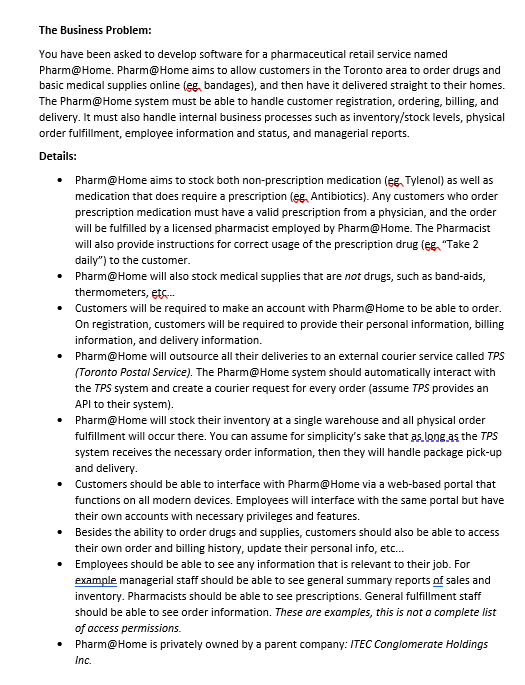
Transcribed Image Text:The Business Problem:
You have been asked to develop software for a pharmaceutical retail service named
Pharm@Home. Pharm@Home aims to allow customers in the Toronto area to order drugs and
basic medical supplies online (eg, bandages), and then have it delivered straight to their homes.
The Pharm@Home system must be able to handle customer registration, ordering, billing, and
delivery. It must also handle internal business processes such as inventory/stock levels, physical
order fulfillment, employee information and status, and managerial reports.
Details:
• Pharm@Home aims to stock both non-prescription medication (eg, Tylenol) as well as
medication that does require a prescription (eg, Antibiotics). Any customers who order
prescription medication must have a valid prescription from a physician, and the order
will be fulfilled by a licensed pharmacist employed by Pharm@Home. The Pharmacist
will also provide instructions for correct usage of the prescription drug (eg, "Take 2
daily") to the customer.
Pharm@Home will also stock medical supplies that are not drugs, such as band-aids,
thermometers, etc....
Customers will be required to make an account with Pharm@Home to be able to order.
On registration, customers will be required to provide their personal information, billing
information, and delivery information.
Pharm@Home will outsource all their deliveries to an external courier service called TPS
(Toronto Postal Service). The Pharm@Home system should automatically interact with
the TPS system and create a courier request for every order (assume TPS provides an
API to their system).
• Pharm@Home will stock their inventory at a single warehouse and all physical order
fulfillment will occur there. You can assume for simplicity's sake that as long as the TPS
system receives the necessary order information, then they will handle package pick-up
and delivery.
• Customers should be able to interface with Pharm@Home via a web-based portal that
functions on all modern devices. Employees will interface with the same portal but have
their own accounts with necessary privileges and features.
• Besides the ability to order drugs and supplies, customers should also be able to access
their own order and billing history, update their personal info, etc...
Employees should be able to see any information that is relevant to their job. For
example managerial staff should be able to see general summary reports of sales and
inventory. Pharmacists should be able to see prescriptions. General fulfillment staff
should be able to see order information. These are examples, this is not a complete list
of access permissions.
Pharm@Home is privately owned by a parent company: ITEC Conglomerate Holdings
Inc.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781305971776
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781305971776
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning