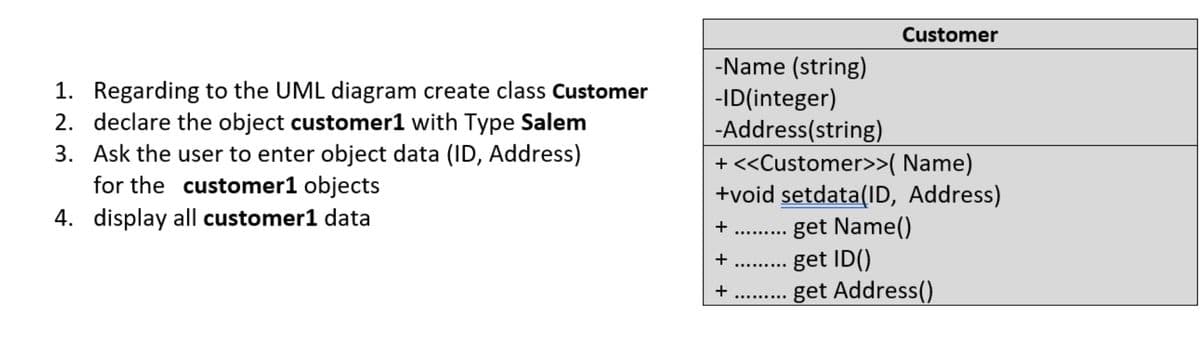
Customer -Name (string) -ID(integer) -Address(string) + <>( Name) +void setdata(ID, Address) get Name() get ID() get Address() 1. Regarding to the UML diagram create class Customer 2. declare the object customer1 with Type Salem 3. Ask the user to enter object data (ID, Address) for the customer1 objects 4. display all customer1 data + ......... + ......... + .........
Q: Subinterface G0/1.10 on R1 must be configured as the default gateway for the VLAN 10 192.168.10.0/24...
A: To route between VLANs, the R1 GigabitEthernet 0/0/1 interface is logically divided into three subin...
Q: What is regression testing?
A: Introduction: In this instance, regression refers to a previously fixed software bug that has return...
Q: Network maintenance is an important task in organizations today who entirely rely on their network i...
A: Answer:- Introduction: Here we are required to answer the three questions asked above about network ...
Q: lass C” network is div
A: Subnet Mask and IP Address On an IP network, a 32-bit IP address uniquely identifies a single device...
Q: A young family is relocating to a new residence. They want to utilise the network for online educati...
A: Introduction: LAN: It is a group of computers and peripheral devices linked in a confined area like ...
Q: Write a C++ program to take an array of ints, print true if the sequence of numbers 1, 2, 3 appears ...
A: C++ Program: #include <iostream>using namespace std; /* sequence() function of boolean type fo...
Q: What changes or benefits have you experienced as a result of information and communications technolo...
A: Introduction: ICT: Information and communications technology (ICT) is a branch of information techno...
Q: What are the drawbacks of file processing systems?
A: Answer: Definition: A file processing system is a group of files and programs that is used to access...
Q: : write an algorithm and draw a flowchart to input and display the sum of 20 Integers.
A: Algorithm: An algorithm contain set of steps helps to understand how to develop a program. It is eas...
Q: d read the information from the file (reversing what writeEmpToFile does), create a new employee and...
A: The implementation of the question is given as,
Q: In what capacity does a router function?
A: Capacity: A home router might theoretically have 254 devices connected to it. This is due to the IP ...
Q: What difference does clustering (k-means) with and without normalisation make?
A: Introduction: K-means clustering is a vector quantization method for dividing n observations into k ...
Q: What is open source software and how does it differ from proprietary software? What is the differenc...
A: Proprietary software is software that is owned by the person or firm who created it. The term "open ...
Q: What does portability imply when we're discussing C++ and our code? Kindly elaborate.
A: Portability: It is a programming language feature which means code written in one place can be porta...
Q: 4 A combinational circuit is defined by the following three Boolean functions: F1(x,y,z)=x'y'z'+xz F...
A:
Q: When keeping passwords in a file, why is hashing passwords preferable than encrypting the password f...
A: Introduction: Encrypting the password is a possibility. However, this poses a security problem becau...
Q: What kind of computations are expected to be carried out exclusively by artificial intelligence unde...
A: Introduction: Not everyone was aware of what it was or how it might affect their firm. They were awa...
Q: What are the chances that a user's effort to add data to the database would result in the creation o...
A: Introduction: A database is a collection of structured data that has been logically organised and is...
Q: 1. Is T;(n) E O(T,(n))?, Is T¡(n) E N(T2(n))?, Is T;(n) E O(T;(n))? • T:(n) = 6n?, T2(n) = n² log n ...
A: Answer the above questions are as follows:
Q: Alice signs the hash of a message. Suppose her hash function satisfies h(x) = 2ª (mod 101) and 1< h(...
A: Hash function: Hash function appeared in all information security application. It is a mathematical ...
Q: Computer Organization Single Cycle Data Path Assembly in RISC-V Draw a picture showing the ...
A: Draw a picture showing the data path add t2, t1, t0 Explain what is happening in each functional un...
Q: are some of the difficulties encountered when testing the Firebase application
A: Lets see the solution.
Q: Explain the concept of application virtualization and why it's important.
A: Application virtualization: It is a type of virtualization in which users can access and use applica...
Q: List out the benefits of biometric authentication?
A: Biometric authentication: It us used to identify the person’s authentication by using physical part ...
Q: describe how to setup a switch to monitor traffic passing across its ports.
A: Introduction: Using specialized gear and software, traffic monitoring, also known as network monitor...
Q: Why does the company want to link the PCs of its employees to a network? List the many computer netw...
A: Introduction: Topology refers to the network's structure and how all of the components are linked to...
Q: number of addresses of a network whose one of the IP addresses is 72.250.220.112 / 27.
A: IP address An IP address is made up of a series of integers separated by periods. IP addresses are ...
Q: When installing new software, one of the most important factors to consider is the hardware.
A: Software Installation : The Installation process for software or apps depends on your operating syst...
Q: Simplify the following Boolean expressions to a minimum number of literals: (a + b+ c')(a'b' + c) (a...
A:
Q: 1-How can the CPU recognize the device requesting an interrupt ? 2-Since different devices are likel...
A: The CPU has numerous interrupt lines, and if you need more than that, there's a "interrupt controlle...
Q: Q3: Use C++ for loop to solve the following sequence: 1 Y=1 + 2 1 +...+ 4 1 1 + + 3 п n=20
A: We need to write a C++ language program using for loop to solve the given sequence. The given sequen...
Q: 1 CNF Step 1 Perform step one of converting the following CFG into CNF by adding a new start state S...
A: According to the information given:- We have to convert following CFG into CNF.
Q: In what ways does Android Pie have drawbacks?
A: Introduction: Android Pie is in ninth version of the Android operating system. Large-scale software ...
Q: Activation is a technique for loading distant objects into a server on demand (that is, when a clien...
A: Introduction: During the course of a single procedure execution, the information required is handled...
Q: Computer science What issues do you believe may occur in extreme programming teams when many manage...
A: Introduction: Extreme Programming (XP) is an agile software development approach that attempts to de...
Q: Differentiate between fully associative caches and direct-mapped caches.
A: Associative Mapping :Here the mapping of the main memory block can be done with any of the cache blo...
Q: Investigate the internet for one incident of a security breach that occurred in connection with each...
A: The Alberta Motor Association filed a major complaint against the former Vice President of Informati...
Q: Describe the factors that contributed to the evolution of computer security into today's information...
A: Introduction: Computer security, also known as cybersecurity or information technology security, is ...
Q: 1. Write a program that creates the following GUI Test Swing Features Three Buttons Left Center Righ...
A: import java.awt.*;import javax.swing.*;import javax.swing.border.*; public class TestSwing { publ...
Q: Give examples of the distinctions between the point-to-point, ring, and mesh network topologies, as ...
A: Point to Point Topology: When two host are connected each other through a dedicated link(either phys...
Q: In terms of encryption, what is the difference between file encryption and disc encryption?
A: Introduction: File encryption File encryption protects individual files or file systems by encryptin...
Q: What is a Cloud Technology?
A: Users can access storage, data, software, and servers over the cloud using any internet-connected de...
Q: I have a code for an assignment, but the code isn't working please help me. The code of the resourc...
A: The exception shown in the picture occurs when we try to access the file which is not available in t...
Q: 7+8 la Prefix (b). postfix
A:
Q: Computer science What are some of the most fundamental database functions that a spreadsheet can't ...
A: Introduction: A database is structured in a logical, consistent, and internally consistent manner. F...
Q: PLEASE HELP ME WITH THIS WHOLE PYTHON PROGRAMME QUESTION USE Bivariate Barplots Activity 2: Create...
A: Requirements: To create two sub Dataframes from the main dataframe where one data frame holds only m...
Q: Because of the technological progress, most appliances can now communicate wirelessly. Do you believ...
A: Introduction: Wireless Technology is a type of technology that allows for communication or any proce...
Q: Scenario Fill in the blanks in a program. After this, test your program (just run it). Your version ...
A: As per the requirement program is completed. Algorithm: Step 1: Write the main() method Step 2: Defi...
Q: Take, for example, the information contained on your computer's hard drive. Do you have information ...
A: Introduction: "Yes," said the majority of individual users, who keep sensitive and secret informatio...
Q: Which of the following terms refers to the technique of grouping redundant resources such as servers...
A: Kindly Note: As per our guidelines we are supposed to answer only one question. Kindly repost other ...
Java
Step by step
Solved in 2 steps with 4 images

- A Person class has four attributes SSN, age, gender, and address. Normally, SSN and gender are not expected to be changed after the values are set for a person object. What design pattern can make this feasible?Why is it necessary to put in additional effort and code in Java programming (or object-oriented programming in general) in order to prevent having classes that are unnecessarily linked? Give three essential grounds for your position.Suppose you were asked to define a class MetaDisplay in Java, containing amethod static void printTable(String r); the method takes a relation name r asinput, executes the query “select * from r”, and prints the result out in tabularformat, with the attribute names displayed in the header of the table. What JDBC methods(s) can get you the required information?t?
- Computer ScienceQuestion: Draw a sequence diagram to illustrate the interaction that takes place between the Client, the TumbleDryer and Bosch objects, and System.out when the describe() message is sent. You will need to read through the code of the TumbleDryer and Bosch classes to trace the sequence. The sequence diagram should be in this format like the diagram below. Client Class public class Client { public static void main(String[] args) { Implementation impl1 = new Bosch(); Appliance apl1 = new TumbleDryer(impl1); apl1.describe(); } } Appliance Class public abstract class Appliance { Implementation impl; public Appliance(Implementation impl) { this.impl = impl; } public abstract void describe(); } Washing Machine Class public class WashingMachine extends Appliance { public WashingMachine(Implementation impl) { super(impl); } public void describe() { System.out.println("Washing Machine");…A Person class has four attributes SSN, age, gender, and address. Normally, SSN and gender are not expected to be changed after the values are set for a person object. What design pattern can make this feasible? Also, Show the UML class diagram for this Person class.Suppose you were asked to define a class MetaDisplay in Java, containing amethod static void printTable(String r); the method takes a relation name r asinput, executes the query “select * from r”, and prints the result out in tabularformat, with the attribute names displayed in the header of the table. What do you need to know about relation r to be able to print the result in the specified tabular format?
- Create an object-oriented information system for a RESTAURANT. Requires all OOP concepts: With different class 1. Inheritance 2. Polymorphism 3. Encapsulation 4. Abstraction - (includes implementatio of inheritance) Program must: Read and Display, and Write operations (has transactions(shows bill and change), display data) Static only (previous transaction not saved, one time run only) -Terminal only(no GUI, no Database)For this project, you will implement an email client-server simulator using the object-oriented design diagramed below. The class diagram above shows class attributes (members) and methods (operations). Operations are denoted with a plus. The diamonds indicate an aggregation relationship between the connected classes. For example, a mailbox list can have one or many mailboxes. A Mailbox can have one or many messages. You will therefore need data structures container objects (lists) to contain these types of objects, as we have seen in previous exercises. All class attributes are private unless denoted otherwise and therefore must be accessed with constructors. getters, ord setters. Constructors are a preferred way to set class attributes. Constructors, setters, getters, and toString methods can be generated by IntelliJ. Check the IntelliJ documentation for how to use the Generate feature. Messages are simultaneously sent and received. Therefore, a Message is…Why is it vital in java programming (and object-oriented programming in general) to put in extra effort and write additional code to avoid overly entangled classes? Provide three fundamental justifications.
- Why does object-oriented programming need more effort and code to prevent unnecessary class links? Your three major arguments?While mapping an object model to a relational database, we have two options for realizing inheritance: vertical mapping (using a separate table for the parent class) and horizontal mapping (duplicating columns). In which of the following cases you prefer vertical mapping? I. You anticipate that the parent class will change often in the future. II. Query response time is not a major concern. III. Run-time efficiency is the main design goal. IV. Modifiability is the main design goal. A Only III B II and IV C I, II, and IV D I and III E All of themCode this in c sharp ,As the following UML diagram illustrates, an aggregation association appears as a solid line with an unfilled diamond at the association end, which is connected to the whole that represents the aggregate, implement the UML diagram. inside the CylenderTest class first create a Circle object then use it to create a Cylinder object, after that print out the volume and area of the Cylinder. Area of a circle A = πr²

