D Question 6 What is the smallest value that can be stored using 16 bits and signed notation? O 65,535 -128 00 -32,768 O-2,147,483,648 5 pts
D Question 6 What is the smallest value that can be stored using 16 bits and signed notation? O 65,535 -128 00 -32,768 O-2,147,483,648 5 pts
Fundamentals of Information Systems
8th Edition
ISBN:9781305082168
Author:Ralph Stair, George Reynolds
Publisher:Ralph Stair, George Reynolds
Chapter1: An Introduction To Information Systems In Organizations
Section: Chapter Questions
Problem 1WE
Related questions
Question
Transcribed Image Text:TIOBEI
Class C COM 2 SF History What is SF JOHN SF JOHN a What i
du/courses/450974/quizzes/1520395/take
● True
O False
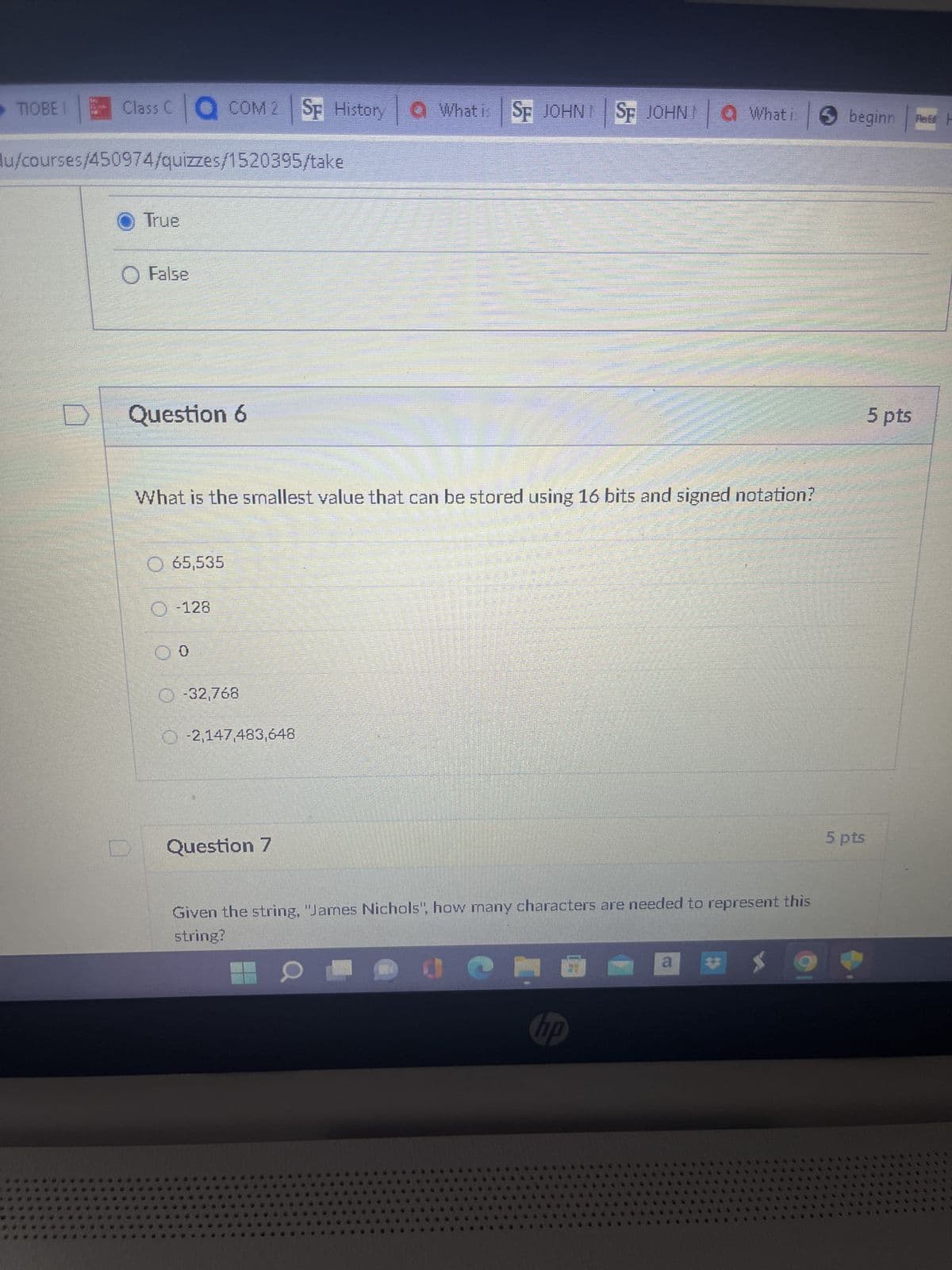
Question 6
65,535
Ⓒ-128
What is the smallest value that can be stored using 16 bits and signed notation?
00
Ⓒ-32,768
-2,147,483,648
000
ODNO
MONTAN
Question 7
20
सantits
C
Given the string, "James Nichols", how many characters are needed to represent this
string?
X
hp
a
beginn Red F
5 pts
5 pts
Transcribed Image Text:History
TIOBEI Class C COM 2 SF History a What is SF JOHN SF
sfcollege.edu/courses/450974/quizzes/1520395/take
ents
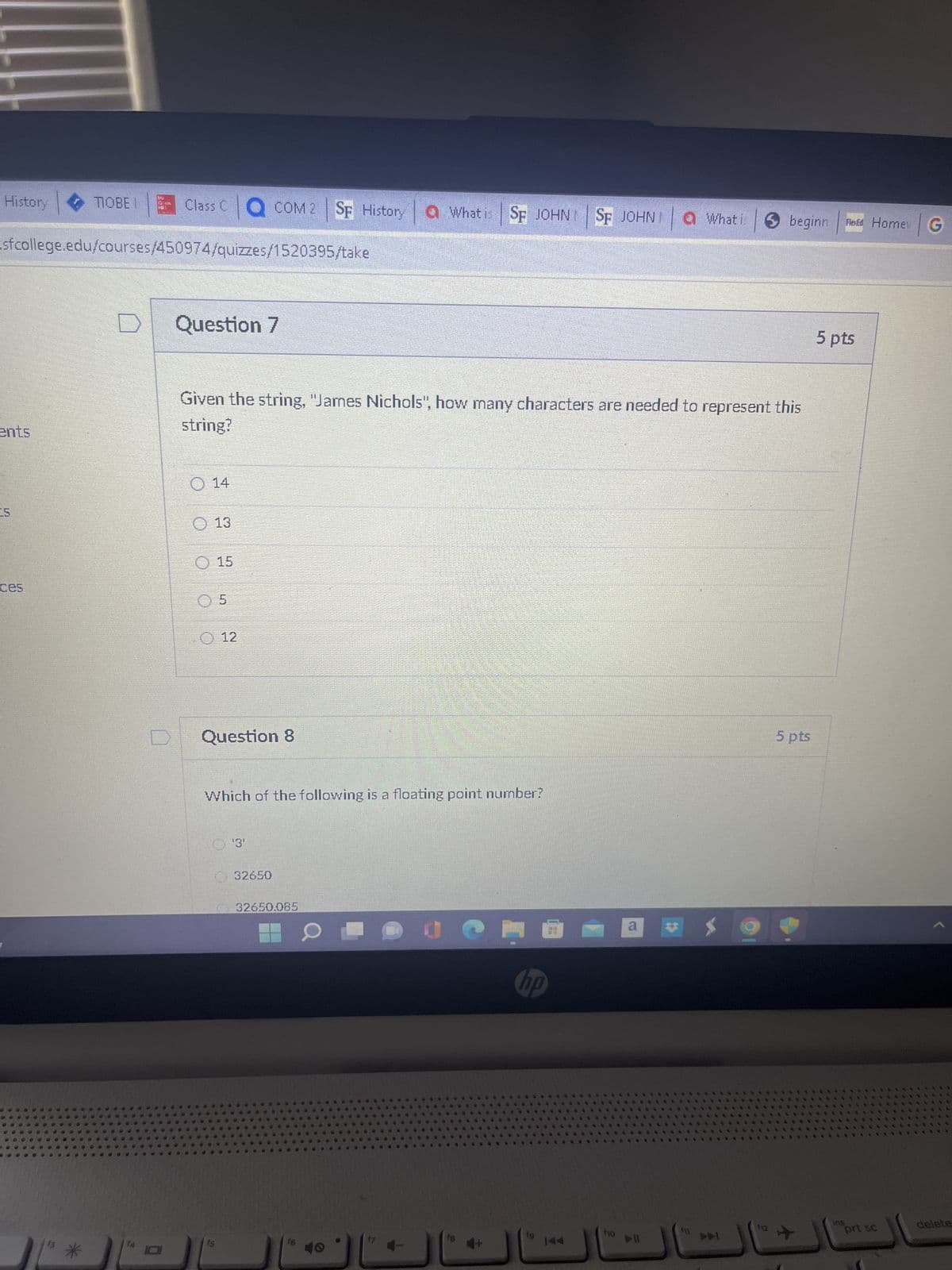
Question 7
Given the string, "James Nichols", how many characters are needed to represent this
string?
O 14
13
15
0 5
J
12
Question 8
Which of the following is a floating point number?
'3'
32650
32650.085
16
30
Jem
JOHNI
SF JOHN What i ✪ beginn
hp
f10
a
▷II
**
F11
f12
5 pts
**
Told Home G
5 pts
ins
pri sc
delete
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Fundamentals of Information Systems
Computer Science
ISBN:
9781305082168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Fundamentals of Information Systems
Computer Science
ISBN:
9781305082168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning