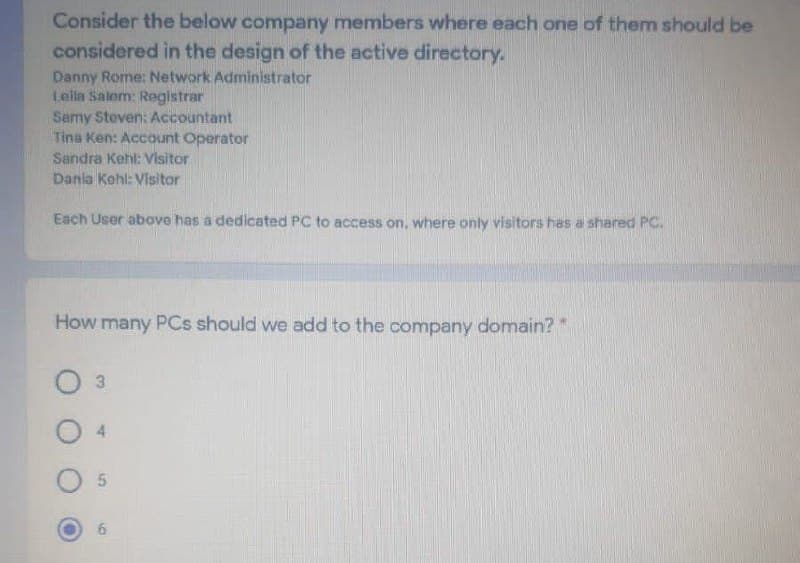
Danny Rome: Network Administrator Lella Salom: Registrar Samy Steven: Accountant Tina Ken: Account Operator Sandra Kehl: Visitor Dania Kohl: Visitor Each User above has a dedilcated PC to access on, where only visitors has a shared PC. How many PCs should we add to the company domain?* O 3 O 4 O 5
Q: Below are some statements about Domain Name System (DNS) and how it works Select correct…
A: Choosing the correct options. In next steps correct and wrong statements wrt DNS are explained…
Q: An ISP has purchased address domain 200.100.0.0/20. If this ISP has 5 customers who want 120, 350,…
A:
Q: 1.Classify the following IP addresses as A, B, or C and label the network and host parts of the IP…
A: As per answering guidelines solving the first part and solving first three sub question of first…
Q: 47- An organization currently requires 40 hosts for its sales department. Given the IP Address…
A: given: 194.12.1.0/24 : this is 32 bit ip //4 octects: first octect:194, second octet :12, 3rd…
Q: Block Address : 192.168.16.0/24 LAN1 Usable #of Hosts: 100 Users Network Address; ? |
A: The answer is...
Q: Visit http://centralops.net/co/domaindossier.aspx (Links to an external site.) and enter a domain…
A: According to the information given:- We have to follow the instruction to perform the task.
Q: 5. Register Columbus State University to EDU domain, and also register CSU web server, email server…
A: Domain Name Server which states that it is called a Domain Name System or DNS. In the simplest form,…
Q: An enterprise wants to use a network infrastructure that complies with the class B IP addressing…
A: For Class B addressing , 16 bits are used for network ID and 16 bit are used for Host ID From given…
Q: requires 40 hosts for its sales department. Given the IP Address 194.12.1.0 /24, design an optimal…
A: 194.12.1.0 /24 Here /24 means number of network bits is 24 and therefore number of host bits is 8.…
Q: An organization currently requires 40 hosts for its sales department. Given the IP Address…
A: A subnet, or subnetwork, is a divided piece of a bigger organization. All the more explicitly,…
Q: 21. Select from the list 3 ip address which belong to class C private (choose 3) 10.75.0.254…
A: As given, we need to find out the 3 ip address which belongs to class C private.
Q: 7. In computer network nodes are a. the computer that originates the data b. the computer that…
A: Given that , In computer network nodes are (a) the computer that originates the data(b) the computer…
Q: Find the class of the following two IP addresses (both are classful addresses), as well as their…
A: Given IP address - a. 104.37.3.6 b. 208.34.54.12
Q: An organization currently requires 40 hosts for its sales department. Given the IP Address…
A: 194.12.1.0 /24 Here /24 means number of network bits is 24 and therefore number of host bits is 8.…
Q: Q.4. In a given scenario, A PC with an IP Address=192.4.10.18 wants to communicate with a website…
A: DNS stands for Domain Name Server. It is used to resolve the names of internet sites with their IP…
Q: For example, Computer A can communicate with computer C by using TELNET. At the same time, computer…
A: Note : As per guidelines we are authorized to answer first question when multiple questions are…
Q: DNS is delegated hierarchically by having, e.g., the root nodes tell resolvers which servers to…
A: Given the statement we have to answer in true or false .
Q: connection
A: Dear Student, 40<= 2^6 Thus for 40hosts , we require 6 bits of network. Now , Number of bits…
Q: A service delivered to users through a cloud-hosted web server has a target response time of 200…
A: We need to find the percentage increase in the amount of time for processing the response is…
Q: Transcribed Image Text 2. You are required to design IP addressing scheme for the Pantai Siring's…
A: EXPLANATION Below is the answer for the given question. Hope you understand it well. If you have any…
Q: Question 2: Suppose now one person connect to the Internet, and want to download the home page of…
A:
Q: Gy 25 hosts X.X.X.X/Y apt Fa0/1 1. What will be the 12th Host IP address in Engineering LAN? 2. What…
A: Given IP address is, 172.10.0.0/16 Number of network bits= 16 Number of host bits= 32-16= 16 bits…
Q: 158. ______ is a network that covers geographic areas that are larger, such as districts or cities.…
A: According to the Question below the Solution:
Q: 4.3-3. What is an IP address actually associated with? Which of the following statements is true…
A: The Answer is in step2
Q: An organization currently requires 40 hosts for its sales department. Given the IP Address…
A: Given, IP address = 194.12.1.0 /24 Number of hosts required = 40
Q: Q2/ if we have the IP address 192.168.1.0 /24 (class C address) with the following requirements
A: The IP address is 192.168.1.0/24 /24 means number of network bits is 24 and number of host bits is…
Q: 1. (a) Complete the frames (1 and 2) shown below with appropriate addresses. The sender A is…
A: Given that, Frame 1 is send from sender A to web server Frame 2 is send from web server Host S.
Q: rk address 172.16.0.0/19 provides how many subnets and hosts? A) 7 subnets, 2046 hosts each B) 7…
A: Given: The network address 172.16.0.0/19 provides how many subnets and hosts
Q: Q7. Suppose we have the following IP addresses for two different organizations, we have to create 5…
A: a. 17.23.120.8 The range of first octet of Class-A network = 0-127 So, the above IP address falls in…
Q: * * How many subnets are created by the ?address 192.168.1.0255.255.255.248 16 O .8 • 32 .4 If all…
A: Please refer below for your reference: Number of subnets created is given by: Ip address :…
Q: öne is A. centralized "programming" difficult: compute tables centrally and distribute B.…
A: Here, I have to choose an option for the above question.
Q: Which of the following does NOT constitute an objection to the use of static routing? O. Additional…
A: Static routing A type of routing known as static routing happens when a switch depends on the data…
Q: Q6: The web server in the below diagram cannot response to all requests come from different users in…
A: Solution: Given: The Web diagram below, To Find: To find the solutions for response to all…
Q: 4.3-3. What is an IP address actually associated with? Which of the following statements is true…
A: The Answer is in Below steps
Q: Determine the correct class of the following IP addresses: Address Class? 191.107.2.10…
A: ANS: the correct class of the following IP addresses: IP ADDRESS ADDRESS CLASS…
Q: Block Address : 192.168.16.0/24 LAN1 Usable #of Hosts: 100 Users Network Address; ?
A: The answer is as follows
Q: In CSMA/CD, after the fifth collision, what is the probability that a node chooses to submit at time…
A: Ans:) The answers with explanations are given below.
Q: Direction: Choose from a peer-to-peer or client-server network. In each case you must provide an…
A: First of all let us understand some of the basics of peer-to-peer network and client server network.…
Q: An ISP is granted a block of addresses starting with 150.80.0.0/14. The ISP wants to distribute…
A:
Q: Explain working of a Proxy serverby functionality i.e., by providing secure Internet access to…
A: Proxy Server basically acts as an mediator between the user and the server. For Example: Lets say…
Q: 11. What is the destination port for the DNS query message? What is the source port of DNS response…
A: Domian Name System:- Its a naming system for computers, servers connected to the internet, In…
Q: 4.3-3. What is an IP address actually associated with? Which of the following statements is true…
A: Here is the answer with explanation:-
Q: stion1: (Computer Networks) a) A web page consisting of 13 objects in total will take ____ ms to…
A: A web page consisting of 13 objects A web page consisting of 13 objects in total will take 252 ms to…
Q: addressing. Answer each question by selecting a matching answer. Each answer can be used to answer…
A: The following questions are concerned with subnet addressing: the three subnets below, each in the…
Q: An ISP is granted a block of addresses starting with 150.80.0.0/14 . The ISP wants to distribute…
A: The first group has 50 customers, each needs 1024 ip addresses so, each host will contain (log21024)…
Q: 55. ________ is a collection of many separate networks. a. A WAN b. An internet c. a LAN d. None of…
A: So your question is 55. ________ is a collection of many separate networks. a. A WAN b. An…
Q: QUESTION 10 The condition (w>8) is equivalent to which of the following conditions? O wc-8 w=8
A: As given, we need to find out the equivalent condition from the given options, for the given…
Q: Ruilding 1 Ruilding 2 Floor Clients IP/Networks Floor Clients IP/Networks 1 40 192.168.1.1 1 22…
A: Answer 1) in this scenario we take class C IP address.because class c octact value lies(192-224).so…
Step by step
Solved in 2 steps

- You are a network administrator who is in the process of building an Active Directory network and you have to create user objects for the 75 users in the Inside Sales department. The Human Resources department has provided you with a list of the users’ names and has instructed you to create the account names by using the first initial and the last name. Each user object must also have the value Inside Sales in the Department property and ABC, Inc. in the Company property. Using the first name in the list, Oliver Cox, as an example, which of the following command-line formats would enable you to create the 75 user objects with the required property values? dsadd “Oliver Cox” -samid ocox –company “Fabrikam, Inc.” –dept “Inside Sales” 2. dsadd user CN=Oliver Cox,CN=Inside Sales,DC=ABC,DC=com -samid ocox –company Fabrikam, Inc. –dept Inside Sales 3. dsadd –company “Fabrikam, Inc.” -samid ocox –dept “Inside Sales” “CN=Oliver Cox,CN=Inside Sales,DC=ABC,DC=com” 4.dsadd user…You are a network administrator who is in the process of building an Active Directory network and you have to create user objects for the 75 users in the Inside Sales department. The Human Resources department has provided you with a list of the users’ names and has instructed you to create the account names by using the first initial and the last name. Each user object must also have the value Inside Sales in the Department property and ABC, Inc. in the Company property. Using the first name in the list, Oliver Cox, as an example, which of the following command-line formats would enable you to create the 75 user objects with the required property values? dsadd “Oliver Cox” -samid ocox –company “Fabrikam, Inc.” –dept “Inside Sales” dsadd user CN=Oliver Cox,CN=Inside Sales,DC=ABC,DC=com -samid ocox –company Fabrikam, Inc. –dept Inside Sales dsadd –company “Fabrikam, Inc.” -samid ocox –dept “Inside Sales” “CN=Oliver Cox,CN=Inside Sales,DC=ABC,DC=com” dsadd user “CN=Oliver…An enterprise is deploying APIs that utilize a private key and a public key to ensure the connection string is protected. To connect to the API, customers must use the private key. Which of the following would BEST secure the REST API connection to the database while preventing the use of a hard-coded string in the request string? A. Implement a VPN for all APIs. B. Sign the key with DSA. C. Deploy MFA for the service accounts. D. Utilize HMAC for the keys. ~If you could explain why for the correct answer, I’d really appreciate that. Thank you!
- QUESTION 9 Which Active Directory component is responsible for authenticating users when they sign in to a workstation? a. Domain controllers b. Trees c. OUs d. ForestsAn enterprise is deploying APIs that utilize a private key and a public key to ensure the connection string is protected. To connect to the API, customers must use the private key. Which of the following would BEST secure the REST API connection to the database while preventing the use of a hard-coded string in the request string? Options: A. Implement a VPN for all APIs. B. Sign the key with DSA. C. Deploy MFA for the service accounts. D. Utilize HMAC for the keys. ~ If you could explain for the correct answer (not in a situational way), I’d really appreciate it. Thanks! Also, please state the letter of the correct choice.An enterprise is deploying APIs that utilize a private key and a public key to ensure the connection string is protected. To connect to the API, customers must use the private key. Which of the following would BEST secure the REST API connection to the database while preventing the use of a hard-coded string in the request string? Options: A. Implement a VPN for all APIs. B. Sign the key with DSA. C. Deploy MFA for the service accounts. D. Utilize HMAC for the keys. ~If you could explain why for each choice, I’d really appreciate that. Thank youuu
- 31. If you are accessing Internet through a proxy server at your campus, in which of these scenarioswill your requested file be likely provided by the proxy server instead of the origin web server?(Select ALL that apply)a. The file was recently requested by you and now you are requesting the same file againb. The file was recently requested by you at your home and now you are requesting the samefile againc. The file was recently requested by a client on the same Local Area Network as you areand now you are requesting the same filed. The file was recently requested by a client in the USA and now you are requesting thesame file 32. Which of the following statements about Selective Repeat are TRUE? (Select ALL that apply)a. It discards a corrupt packet and buffers all subsequent packetsb. It is simpler to implement than Go-Back-Nc. It does not require a buffer at the receiverd. It needs a separate timer for each packet to keep track of their timeout valuesIn this lab, your task is to use Active Directory Users and Computers to complete the following actions on the CorpDC server: In the Users container, create a group named Managers. Configure the group as follows: Group scope: Global Group type: Security Make the following users members of the Managers group: Organization Unit Username Accounting Mark Woods Research-Dev Pat Benton Marketing\MarketingManagers Juan Suarez Research-Dev\ResearchManagers Arlene Kimbly Sales\SalesManagers Mark Burnes Support\SupportManagers Shelly EmeryLinux - Ubuntu Create a file named <yourdomain>.db in /etc/bind/, this file will containall the resource records for that domain. Edit the created file in the begining of question and add a SOA resource record. Consult and before setting the SOA values. Next set up an NS record and a corresponding glue record. Allocate one of the IP-addresses you created in porpose of building the Dns server to each subdomains NS. In the attached picture is the name of the domain . Would you attach the anwser with shotscreen for each step . Thanks
- You have the option of categorizing DNS records by category. Every single one of them has to be segmented into manageable pieces and accompanied with examples and arguments. Is it possible for an organization's email server and web server to have the same hostname?In a Windows domain environment, detail the steps involved in setting up Active Directory Federation Services (AD FS) for single sign-on (SSO). How can this benefit software development projects with authentication and authorization requirements?Say that the Top Level Domain .gov were to suddenly lose all its name servers due to a system crash. Now say that a user on a host example.school.edu wants to FTP to a machine called host51.defense.gov, with which they have never communicated. a. Explain the process that would occur starting with the user’s host until something goes wrong, and explain what would go wrong. b. Now, say that the user had already FTPed some files from host51.defense.gov 10 minutes before the nameservers at .gov crashed. Would connecting again likely work? If so, how would the process that occurred be different?

