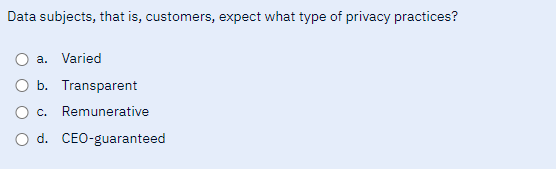
Data subjects, that is, customers, expect what type of privacy practices? a. Varied O b. Transparent O c. Remunerative O d. CEO-guaranteed
Q: Note: Use Ruby language to write your code. Task Assigned: Write a program to read input two strings…
A: Here, we have to write a program in the Ruby language to read input two strings sp_top, sp_bottom…
Q: As a corporate trainer, you'll be responsible for covering the following ground while discussing…
A: As a corporate trainer, I would begin by explaining how a switch learns MAC addresses and builds its…
Q: In a few phrases, you can sum up the seven design considerations for OO languages that were covered…
A: Security Policies: Every company sells something. Someone may want that item for himself or to deny…
Q: In terms of machine learning and deep learning algorithms, how does today's age of AI compare to AI…
A: Given: How has AI changed over the last 50 years in terms of machine learning or deep learning…
Q: Why do we often confuse segmentation and paging? What does it mean to thrash?
A: Thrashing, a state of excessive paging opera, occurs in a virtual storage system. Why is paging…
Q: Does the JVM's method region serve any particular function, and if so, what is it used for? There…
A: Wireless data connections are used in a wireless network to connect network nodes. Mobile phone…
Q: Find the appropriate website or social networking site that fits each of the following criteria.…
A: The locations must be matched appropriately. -The choices are: platform for social networking…
Q: When someone says they use a "operating system," what precisely do they mean? Describe the two most…
A: An operating system (OS) is a type of software that manages a computer's hardware and software…
Q: Note: Use Ruby language to write your code. Task Assigned: Write a program to read input two strings…
A: According to the information given:- We have write a program to read 2 string sp_top and sp_bottom…
Q: Which VLAN is intended to provide administrative access to network devices?
A: .
Q: a. Design and implement a method height for BinarySearchTree that returns the height of the tree…
A: A binary search tree (BST) is a data structure that consists of nodes in a hierarchical tree-like…
Q: How do the various types of databases vary, and what kinds of information may be kept in each?
A: Structured Query Language (SQL) is a standardised programming language for relational databases that…
Q: How does the employment of a function improve things?
A: FUNCTION: A function is, in its most basic form, a collection of modules that may operate…
Q: Learn the proper phrase for digital data stored on an optical medium as opposed to traditional media…
A: Your answer is given below.
Q: Part 2: Functional Requirements You are expected to write a total of 25 functional requirements.…
A: Functional requirements refer to the specific features and behaviors that a software system or…
Q: When someone says they use a "operating system," what precisely do they mean? Describe the two most…
A: The OS performs two main tasks: Control and management of the computer's hardware (including…
Q: I'm eager to find out what each of the three primary frequency bands is called in wireless networks.…
A: A group of frequencies known as a frequency band is employed for a certain function. Frequency bands…
Q: What parameter must be set when redistributing a route into EIGRP? Many factors, such as the…
A: Introduction: EIGRP (Enhanced Interior Gateway Routing Protocol) is a protocol used for routing data…
Q: are not discussed elsewhere in the book. The bitwise-manipulation operators perform simultaneous bit…
A: The main method generates and displays all power-of-two numbers in the range +128 to -128, using…
Q: What is the impact of quantum computing on the field of computer engineering, and how do engineers…
A: Your answer is given below.
Q: How may you utilize context pointers to suggest items to customers? Provide a concrete example and a…
A: By incorporating accessible contextual information into the recommendation process, a context aware…
Q: I need help with my code Ask the user for a filename. Display the oldest car for every manufacturer…
A: We have to solve the error in the program. Error: Enter filename\ncar-list-3.txtENTERException in…
Q: Input techniques, such as batching and real-time processing, need specifications. Provide an example…
A: Batch input technique: The batch input method, which is defined as follows, may be used to transfer…
Q: The phrases "wide area network" (WAN) and "local area network" (LAN) are commonly used…
A: We have to explain "wide area network" (WAN) and "local area network" (LAN) are commonly used…
Q: Complete the method “readdata”. In this method you are to read in at least 10 sets of student data…
A: The task is to complete three methods - "readdata", "printdata", and "printstats" in the Java…
Q: The three-circle paradigm of system administration is briefly explained below. Are alternatives to…
A: System Management: The three-sphere model of system management helps business, organisation, and…
Q: There are a few broad classes into which one may classify the protocols used in networks.
A: A protocol is set of rules and regulations used to manage data flow in internet. A network is…
Q: Please help, the selected answer is incorrect. Will give thumbs up Suppose you have lost (or…
A: Solution and explanation are provided below:
Q: Provide some examples of session hijacking techniques. If you were attacked in this way, how would…
A: Depending on the attacker's location and attack vector, the attacker has a variety of methods for…
Q: Explain what spoofing is and how it might be used against an unsuspecting target.
A: Introduction: Importers, or spoofery, steal private information by impersonating trusted contacts or…
Q: Show how dynamic programming may be used in the real world with the help of examples.
A: With dynamic programming, we can only proceed with the preparation of each individual component…
Q: Consider the snapshot isolation used in the database of a large airline. What are some cases when an…
A: Analysers of systems The people in charge of creating and designing an information technology…
Q: If you're attempting to protect yourself against malware, what's the point of having file extensions…
A: File extensions are crucial because they inform your computer and you what icon to use and what…
Q: Identify the function of a file extension and how it affects your workflow.
A: Hello student. Greetings Hope you are doing great. Thank you!!! A file extension is a set of…
Q: Wireless networks are crucial in today's developing nations. They're important in the developed…
A: Yes, both in developed and underdeveloped countries, wireless networks are essential in today's…
Q: write a java program to print the mirror image of right angled in x-direction after taking number of…
A: Required:- Write a Java program to print the mirror image of right-angled in x-direction after…
Q: What aspects are so different between Common Lisp and Scheme?
A: Common Lisp is much simpler than the huge and convoluted Scheme programming language. Scheme is…
Q: Explain each line of haskell code -- function to help double every other element of list…
A: SOLUTION - So, in this Haskell code, there are two functions used doubleDigitsHelper and…
Q: When is dynamic scoping helpful, and how can it be made better?
A: Overview: Dynamic planning, Any object or process that is constantly altering is said to be…
Q: How often, if ever, would you utilize a static route configuration as a network administrator?
A: To find how often would you utilize a static route configuration as a network administrator.
Q: When it comes to the world of computers, what precisely is the difference between architecture and…
A: Computer Architecture is a diagram for plan and execution of a computer framework. It alludes to the…
Q: INTERFACING SEVEN-SEGMENT DISPLAY needs an introductory section that includes
A: The answer is given in the below step
Q: How does dynamic memory allocation really function when it comes to dividing up available RAM? Can…
A: The method of assigning memory while a software is being executed is known as dynamic memory…
Q: Need help with the code for it to work. This is the code I have and the prompt of the assignment…
A: Algorithm: Prompt the user for the growth rates, initial populations, and timescale Initialize the…
Q: Is there a disadvantage to utilizing a WYSIWYG editor, and what are its advantages?
A: Dear learner, hope you are doing well, I will try my best to answer this question. Thank You!!…
Q: What exactly does "cooperative" multithreading mean in the context of a multi-threaded system?…
A: Introduction: b) What is "cooperative" multithreading? "Cooperative, only one each"—pros and cons?…
Q: A Java virtual machine (JVM) can only execute a single method pe
A: Introduction: JVM uses threads to execute multiple tasks simultaneously, which is a crucial feature…
Q: What are some of the main security risks associated with computer networks, and how do computer…
A: We have to explain some of the main security risks associated with computer networks, and how do…
Q: This example may be derived from "snapshot isolation" airline database. What if, instead of a…
A: Introduction: Take into consideration the database management system used by an airline and how it…
Q: Instead of keeping the structures in shared memory, it would be preferable to have them kept in the…
A: In computer science, interprocess communication (IPC) refers to the methods that enable processes to…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Now that you have done your research, explain your understanding of the data breach that happened at Desjardines in 2019? Explain five policies that Desjardines could implement to minimize illegal or unauthorized access to sensitive data? Explain how being ethical could have prevented the data breach. What background checks need to be done on employees and do they vary depending on the employee’s position? Explain five ways how Desjardines could you use artificial intelligence to help detect internal data breaches?hat has made it much easier for organizations and companies to keep more detailed information on individuals? A)Personally identifiable information B) cheaper data storage C)ethical risk D)hidden dataIs confidentiality of data at risk? Afterwards, we'll discuss measures to take against similar dangers.
- What is meant by the phrase "protection of personal information"? What are the best five strategies to keep your personal data safe?1. After reading the information presented in this module and other sources, write a one-page paper that outlines five recommendations for improving the privacy of e-mail in an organization. Your recommendations should also highlight ways that minimize or eliminate corporate data leakage. 2. After reading the information presented in this module and other sources, write a one-page paper that describes GDPR. Describe how businesses may benefit from this compliance. Research three companies that have been sued by the European Union. Which privacy issues were violated by each company? 3. The admissions office of Southern State University needs a simple and easy-to-follow Web policy document to send to its incoming freshmen. The document should tell students how to behave while on the Web. After reading the information presented in this module and other sources, create a document that includes a 10-item bulleted list highlighting the key issues of which incoming students should be aware.…Discover illegal access testing. Protecting critical data?
- What do you think are the most important measures to take to protect individuals' private information? Where is the weak link in the chain when it comes to the security of the data: integrity of the data or authentication of the userThink of the following information assurance principles: Integrity Availability Accuracy Authenticity Utility Possession Create one MC question for any two principle : identify the answer from the question created as well. thanks. it's a short question please help .Choose the option that most accurately describes how you feel about the following questions about data security: How do these alternatives compare in terms of protecting sensitive information and verifying the identity of users?
- 10. For each of the following assets, examine and assign a low, moderate or high impact levelfor the loss of confidentiality, integrity and availability respectively. Justify your answersa. An organization managing public information on its web server. b. A law enforcement organization managing extremely sensitive investigativeinformation.c. A financial organization managing routine administrative information (notprivacy-related information).Question 1 When selecting a Data Loss Prevention tool, which of the following factors should be considered first or of highest importance? compliance with GDPR and CCPA privacy directives and laws. ease of use for the policy engine and a large library of prewritten policies allowing granular control of the DLP tool's behaviors. Accuracy with respect to identifying and preventing incidents that could result in sensitive data being disclosed or released to unauthorized individuals. coverage for both data at rest and data in motion. Question 2 Which of the following technologies is the best choice for limiting unauthorized access to financial data stored in a central repository? Data Loss Prevention (DLP) system Content Management system Intrusion Detection and Prevention System (IDPS)…The following are some examples of potential data confidentiality breaches: Afterwards, we'll talk about the many precautions that may be done.



