database system
Database Systems: Design, Implementation, & Management
11th Edition
ISBN:9781285196145
Author:Steven, Steven Morris, Carlos Coronel, Carlos, Coronel, Carlos; Morris, Carlos Coronel and Steven Morris, Carlos Coronel; Steven Morris, Steven Morris; Carlos Coronel
Publisher:Steven, Steven Morris, Carlos Coronel, Carlos, Coronel, Carlos; Morris, Carlos Coronel and Steven Morris, Carlos Coronel; Steven Morris, Steven Morris; Carlos Coronel
Chapter10: Transaction Management And Concurrency Control
Section: Chapter Questions
Problem 1P
Related questions
Question
3
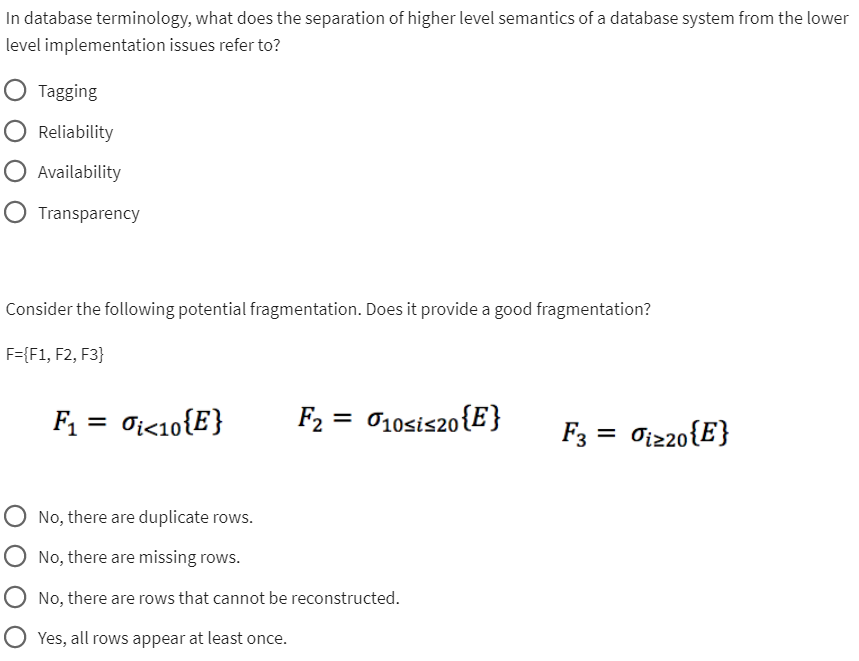
Transcribed Image Text:In database terminology, what does the separation of higher level semantics of a database system from the lower
level implementation issues refer to?
O Tagging
Reliability
Availability
Transparency
Consider the following potential fragmentation. Does it provide a good fragmentation?
F={F1, F2, F3}
F₁ = Oi<10{E}
F₂ = 10sis20 {E}
No, there are duplicate rows.
No, there are missing rows.
No, there are rows that cannot be reconstructed.
Yes, all rows appear at least once.
F3 = Oiz20{E}
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781285196145
Author:
Steven, Steven Morris, Carlos Coronel, Carlos, Coronel, Carlos; Morris, Carlos Coronel and Steven Morris, Carlos Coronel; Steven Morris, Steven Morris; Carlos Coronel
Publisher:
Cengage Learning

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781285196145
Author:
Steven, Steven Morris, Carlos Coronel, Carlos, Coronel, Carlos; Morris, Carlos Coronel and Steven Morris, Carlos Coronel; Steven Morris, Steven Morris; Carlos Coronel
Publisher:
Cengage Learning