Information Technology Project Management
9th Edition
ISBN:9781337101356
Author:Kathy Schwalbe
Publisher:Kathy Schwalbe
Chapter11: Project Risk Management
Section: Chapter Questions
Problem 5E
Related questions
Question
Answer in c
dairy.txt
DAY Milk Cheese Butter Cream Yogurt
Monday 50 25 32 16 512
Tuesday 64 12 34 62 97
Wednesday 23 54 67 13 62
Thursday 34 54 25 35 127
Friday 76 23 54 24 120
fruits.txt
DAY Banana Apple Orange Mango Watermelon
Monday 60 35 32 16 30
Tuesday 44 22 34 62 54
Wednesday 33 14 67 13 22
Thursday 24 44 35 15 42
Friday 36 43 24 34 29
Transcribed Image Text:+ Automatic Zoom
wwwwv p
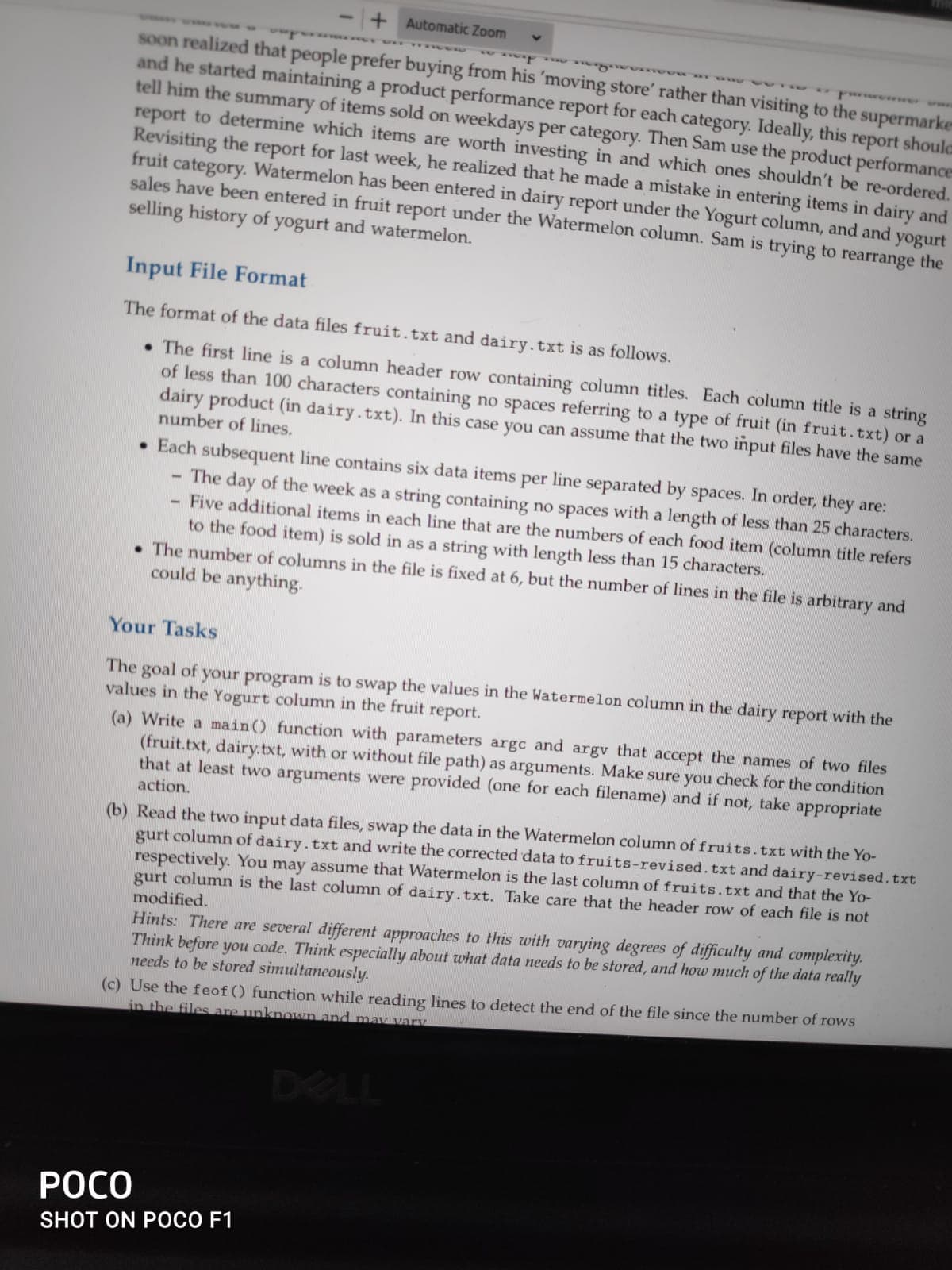
soon realized that people prefer buying from his 'moving store' rather than visiting to the supermarke
and he started maintaining a product performance report for each category. Ideally, this report shoula
tell him the summary of items sold on weekdays per category. Then Sam use the product performance
report to determine which items are worth investing in and which ones shouldn't be re-ordered.
Revisiting the report for last week, he realized that he made a mistake in entering items in dairy and
fruit category. Watermelon has been entered in dairy report under the Yogurt column, and and
sales have been entered in fruit report under the Watermelon column. Sam is trying to rearrange the
selling history of yogurt and watermelon.
yogurt
Input File Format
The format of the data files fruit.txt and dairy.txt is as follows.
• The first line is a column header row containing column titles. Each column title is a string
of less than 100 characters containing no spaces referring to a type of fruit (in fruit.txt) or a
dairy product (in dairy.txt). In this case you can assume that the two input files have the same
number of lines.
• Each subsequent line contains six data items per line separated by spaces. In order, they are:
The day of the week as a string containing no spaces with a length of less than 25 characters.
Five additional items in each line that are the numbers of each food item (column title refers
to the food item) is sold in as a string with length less than 15 characters.
• The number of columns in the file is fixed at 6, but the number of lines in the file is arbitrary and
could be anything.
Your Tasks
The goal of your program is to swap the values in the Watermelon column in the dairy report with the
values in the Yogurt column in the fruit report.
(a) Write a main() function with parameters argc and argv that accept the names of two files
(fruit.txt, dairy.txt, with or without file path) as arguments. Make sure you check for the condition
that at least two arguments were provided (one for each filename) and if not, take appropriate
action.
(b) Read the two input data files, swap the data in the Watermelon column of fruits.txt with the Yo-
gurt column of dairy.txt and write the corrected data to fruits-revised.txt and dairy-revised.txt
respectively. You may assume that Watermelon is the last column of fruits.txt and that the Yo-
gurt column is the last column of dairy.txt. Take care that the header row of each file is not
modified.
Hints: There are several different approaches to this with varying degrees of difficulty and complexity.
Think before you code. Think especially about what data needs to be stored, and how much of the data really
needs to be stored simultaneously.
(c) Use the feof () function while reading lines to detect the end of the file since the number of rows
in the files are unknown and mav vary
DELL
РОСО
SHOT ON POCO F1
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 5 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Information Technology Project Management
Computer Science
ISBN:
9781337101356
Author:
Kathy Schwalbe
Publisher:
Cengage Learning

Fundamentals of Information Systems
Computer Science
ISBN:
9781305082168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781285867168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Information Technology Project Management
Computer Science
ISBN:
9781337101356
Author:
Kathy Schwalbe
Publisher:
Cengage Learning

Fundamentals of Information Systems
Computer Science
ISBN:
9781305082168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781285867168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning