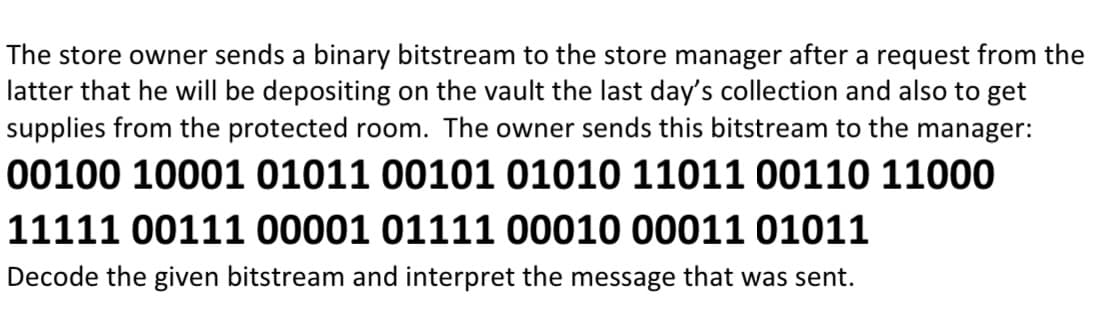
Decode the given bitstream and interpret the message that was sent.
Q: Define Subtractors
A: Please find the detailed answer in the following steps.
Q: Explain the koch curve with example.
A:
Q: plementing multi-factor authentication? What advantages would you reap if you take more care to…
A: We increase the security of your internet based accounts by utilizing two-factor authentication. To…
Q: Write A Short Note On Interpolation And Approximation.
A:
Q: In the event that a firm suffers a data breach, what potential repercussions may there be for the…
A: Data Breach: When private, sensitive information that ought to have been kept private has been…
Q: Give an in-depth explanation of how a challenge-response authentication system works. When compared…
A: In client-server systems, password-based authentication is often used. However, since the password…
Q: To what extent does the use of a siloed information system have the potential to cause problems and…
A: Introduction What is a Siloed system?: Similar to how grain and grass in a farm silo are sealed…
Q: Write A Short Note On Interpolation And Approximation.
A: The answer to the question is given below:
Q: .Write a Java Program to traverse a binary tree in postorder traversal using recursion In the main…
A: ALGORITHM:- 1. In the main method declare the tree and fill in the given values. 2. Pass the root…
Q: Explain the koch curve with example.
A: Solution : What is koch curve : A Koch curve is a fractal curve that can be made by replacing a…
Q: Discuss the role of networking in the development of IT in a research paper.
A: The question has been answered in step2
Q: If you believe you understand "Data Modeling," please elaborate.
A: Data models are created by businesses to meet their demands: In advance, rules and specifications…
Q: Discuss about the Cryptographic Primitives.
A:
Q: What are some of the main objectives of the authentication procedure? Think critically about the…
A: Required: What purposes does authentication serve? Consider the advantages and disadvantages of…
Q: Explain 802.11 Wireless LAN frame format.
A: 802.11 Wireless LAN frame is a data packet in the Data link layer which contain MAC addresses. The…
Q: Find out which passwords are flawed and how they may be fixed.
A: Cybercriminals utilize a variety of hacking techniques to attempt to access your accounts. The…
Q: When it comes to security, how can the benefits and drawbacks of the various authentication…
A: Distinguished: Differentiating oneself requires appreciating others. Outstanding people often…
Q: What is PL/SQL?
A: The answer to the question is given below:
Q: The Effects of Information Technology on Our Lives and Society Prove your point of view while also…
A: Information technology's daily and societal effects. Argue for both sides. Technology influences…
Q: How can I see all tables in SQL?
A: The answer to the question is given below:
Q: What do you mean by "objectives of authentication"? Examine the pluses and minuses of each…
A: The answer to the question is given below:
Q: If you believe you understand "Data Modeling," please elaborate.
A: Introduction: Data modelling is the process of creating a visual representation of the complete…
Q: Given a heap that contains 128 nodes, the height of the heap rooted at level 4 is TEULVIO a. 3 b.…
A: height of the heap:- Height of a node in a heap to the number of edges and the longest simple…
Q: Is it better to create a data model from scratch or use a pre-made package model?
A: The following table contrasts distributed databases versus multiuser databases: In a multiuser…
Q: 1- Create a class SchoolKid that is the base class for children ar a school . It should have…
A: Inheritance:- It is the Java method by which one class is permitted to inherit the characteristics…
Q: There are several approaches to managing logins. List down everything you've done to this point to…
A: Provide an example of hypothetical login management. Choose from an assortment of authentication…
Q: There are several approaches to managing logins. List down everything you've done to this point to…
A: There are multiple authentication methods other than simple password login . This authentication…
Q: How to create a database in SQL?
A:
Q: Exercise: Using while loop structure, write C++ program that prompts the user to enter the number of…
A: As given, we need to write a C++ program, that takes the number of the students in a class and input…
Q: What does HTML5's canvas element do, exactly?
A: HTML5's Canvas Element : The HTML canvas> element is used to create images in JavaScript on the…
Q: Consider the following code snippet. 1. /* 2. * The Student class models a student with a name,…
A: Answer:
Q: When using authentication, how far can we get? Here, we'll compare and contrast the features, pros,…
A: Introduction: Authentication refers to the process of verifying that someone or something is who or…
Q: When it comes to modern networks, which routing protocols are preferred both inside and externally?
A: Modern network:- Virtual network functions (VNFs), a type of software-based modern network, are…
Q: Explain the concept of centralised system with its pros and cons.
A: Introduction: Centralized system: Master/central system that controls/coordinates with other…
Q: What effect does a data breach have on cloud safety? Which of the numerous possible preventive…
A: Definition: If cloud data security is exploited, it may lead to leaks. Sensitive data is accessible…
Q: To what end can a balanced scorecard contribute to optimizing return on investment?
A: Balanced Scorecard is a business system used to manage an organization's process. It forces…
Q: There are several subcategories to choose from when discussing the various forms of cyberattacks.…
A: Answers:- The Cyber attacks to the several negative effects. To the attack is carried out it can be…
Q: What is PL/SQL?
A: Introduction: PL/SQL : A block-structured language called PL/SQL allows programmers to use…
Q: The internet is often cited as a technological high point, but why exactly is it considered so? Does…
A: Introduction: The Internet is the most powerful instrument available in the 21st century, and it is…
Q: Is it better to create a data model from scratch or use a pre-made package model?
A: Data Model: A raskaged data model makes the metadata of a consistent, industry-verified data model…
Q: What are the company's rules governing the dissemination of information in the case of a breach in…
A: Introduction: An outline is a comprehensive plan of action or event organisation. When considering…
Q: Where is this authentication process leading? Consider the benefits and drawbacks of many different…
A: Given: must have knowledge on the objectives of the authentication procedure. to acquire the…
Q: What is PL/SQL?
A:
Q: Could you please describe the idea of a challenge-and-response authentication system to me in your…
A: Given: Password-based authentication is used in client-server systems. Since the password is…
Q: Let T(n) be a function obeying the recurrence T(n)=5T(n/5) + n°, then T(n)= a. none b. \( \theta(n³)…
A: Solution: We have to find out the time complexity of the given recurrence. Here we will apply…
Q: When a security breach occurs, what actions should businesses take?
A: Security lapses It is a risk that arises from unrecognised and unauthenticated sources that affects…
Q: What effect does a data breach have on cloud safety? Which of the numerous possible preventive…
A: Introduction : A data breach is an incident that has the potential to expose sensitive information…
Q: What Are The Three Major Classes Of Guided Media.
A: Signals are conveyed across a physical medium called Guided Transmission Media, sometimes referred…
Q: So, why exactly should one use HTML5's canvas element?
A: Introduction: Web designers can utilize JavaScript and HTML5 Canvas to progressively make different…
Q: Consider building a CSMA/CD network running at 1 Gbps over a 1km cable with no repeaters. The signal…
A: in CSMA / CD network we have to find minimum frame Size so below solution is given below given…
Step by step
Solved in 2 steps

- q3- With the ________ mode if there is an error in a block of the transmitted ciphertext only the corresponding plaintext block is affected a- Electronic Code book Mode (ECB) b- Cipher Feedback Mode (CFB) c- Cipher Block Chaining Mode (CBC) d- Output Feedback Mode (OFB)If you are transmitting a large file, you must utilise cypher block chaining or cypher feedback mode. How much more efficient is one?Alice encrypts a message using AES, and sends the ciphertext to Bob. Unfortunately, during the calculation of the third block, a lightning struck Alice’s house, corrupting the 2nd bit of the AES output (for the third block). Fortunately, nothing else of the calculation was affected. How much of the plaintext can Bob still recover if the mode of encryption is one of the followings: CBC, CFB, OFB, or CTR?
- Comparing CBC mode to OFB mode, only in OFB mode... A. each block is encrypted separately B. an initialization vector is utilized C. each ciphertext block depends on the previous ciphertext block D. a key stream is utilizedGive encryption or decryption of these hexadecimal messages using the one-time pad algorithm, giving the result in hexadecimal also. You may wish to convert to binary first. a. m = 0xdeadbeef, K = 0x4ea04002, c = ? b. c = 0x84848484, K = 0xffffffff, m = ? c. c = 0x104557ce, K = 0xdabbad00, m = ?a. Compute CBC-MAC for a message of 16 bits, “8642” (in Hexa). Assume a block size of 8 bits with an IV=F1 (in hexa). For simplicity, assume the encryption to be a simple XOR of the key with the plaintext. Let the encryption key be B4 (in Hexa). (Hint: Divide the message into blocks of 8 bits each; XOR each block with the previous cipher output; then encrypt this with the key. For the first block, XOR it with IV. Details in pages 325-326 Ch.12 of the textbook) b. Suppose Alice computes the Secret prefix MAC (page 322: secret prefix MAC(x) = h(key || x)) for the message ”AM” (in ASCII) with key “G” (in ASCII) that both Alice and Bob know. The hash function that is used is h(x1x2x3)= g(g(x1 XOR x2) XOR x3 ) where each xi is a character represented as 8 bits, and g(x) is a 8-bit string that is equal to the complement of bits in x. For example, g(10110011) = 01001100. The MAC is 8 bits. (8-bit ASCII representation of the characters is given below.) What is the Secret prefix MAC…
- Most IP datagram reassembly algorithms have a timer to avoid having a lost fragment tie up reassembly buffers forever. Suppose that a datagram is fragmented into four fragments. The first three fragments arrive, but the last one is delayed. Eventually, the timer goes off and the three fragments in the receiver's memory are discarded. A little later, the last fragment stumbles in. What should be done with it?N blocks of plaintext (P1 to PN) are being encrypted in CFB mode into ciphertext (C1 to CN). Assume that two bits of C3 are erroneous (their binary values have flipped). What bits of C3, C4, and C20 are erroneous?Compute CBC-MAC for a message of 16 bits, “ABCD” (in Hexa). Assume a block size of 8 bits with an IV=C9 (in hexa). For simplicity, assume the encryption to be a simple XOR of the key with the plaintext. Let the encryption key be D8 (in Hexa). (Hint: Divide the message into blocks of 8 bits each; XOR each block with the previous cipher output; then encrypt this with the key. For the first block, XOR it with IV.
- .In Go-Back-N window, when the timer of the packet times out, several packets have to be resent even some may have arrived safe. Whereas in Selective Repeat window, the sender resends ________ 1. Packet which are not lost 2. Only those packets which are lost or corrupted 3. Packet from starting 4. All the packetsThe very last block of a message encrypted with AES-256 in CBC mode is 15 bytes long and ends with the bytes: 0102030405060708090a0b0c0d0e0f When padded in accordance with PKCS #7 with 16-byte blocks, what is the complete value of the last block? *Please explain how you have solved this, thank you!!.In Go-Back-N window, when the timer of the packet times out, several packets have to be resent even some may have arrived safe. Whereas in Selective Repeat window, the sender resends ________1. Packet which are not lost2. Only those packets which are lost or corrupted3. Packet from starting4. All the packets

