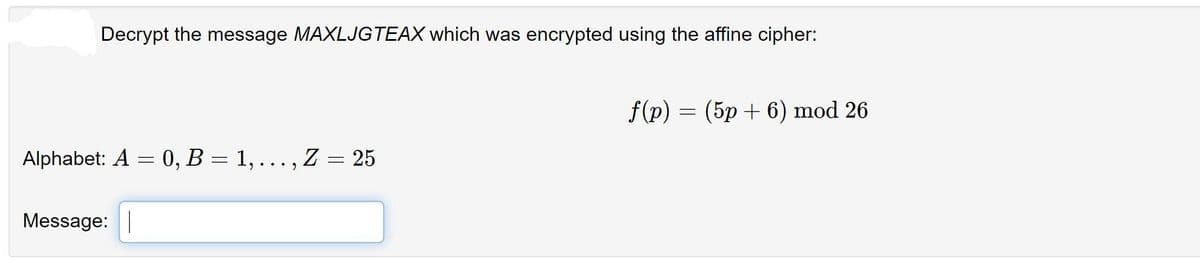
Decrypt the message MAXLJGTEAX which was encrypted using the affine cipher: f(p) = (5p+6) mod 26
Q: Magnetic storage, what are they?
A: Magnetic storage is the trick of magnetic fields in place to record audio, video or other data. In…
Q: Computer science Firewalls use Access Control Lists (ACL).
A: Introduction: ACLs are used to filter traffic based on a set of rules for incoming and outgoing…
Q: chnical term. Make two lists, one for each list. What function does it play in the storing of…
A: Below it play in the storing of software in embedded computers
Q: What are some of the most often used CLI troubleshooting commands for diagnosing and resolving…
A: At times, time outs, lengthy buffering, and poor quality online calls are all typical in any user's…
Q: 1) Update your SQL server to allow mixed authentication mode. You can do it in SSMS or by running…
A: Here is the sql code:
Q: innovations in assistive technology do you see for p sistive technology is accessible to the general…
A: In the course of our life, science has advanced a long ways past the constraints of our creative…
Q: Web servers utilise a variety of technologies to create personalised web pages that are tailored to…
A: Web servers employ the following technologies to respond to client requests: JavaScript: Client-side…
Q: Divide IP addresses for network ID 172.168.89.0
A: The answer is
Q: ns and prosecutions ha lear what you're saying
A: The dark web is the World Wide Web content that exists on darknets: overlay networks that…
Q: What does it mean to be a host on the internet?
A: A computer or other device that communicates with other hosts on a network is known as a host (also…
Q: What is the definition of baseband?
A: Introduction: The definition of baseband :
Q: List and describe all the words related to the quantification of data, such as bit, byte, and…
A: There are many units of information. We will list down some of them units(step2) with It's binary…
Q: In your own words, describe what happened as a consequence of the data breach that was previously…
A: Introduction: A data violation is a cyber assault that has access to and discloses sensitive,…
Q: What are some effective strategies for preventing data loss?
A: Given: We have to discuss What are some effective strategies for preventing data loss.
Q: Explain how the ACID paradigm of database architecture may be applied to two non-financial examples.
A: The term ACID refers to the four important qualities of a transaction in transaction processing:…
Q: Explain ISA (Instruction Set Architecture) and the several types of ISA (Instruction Set…
A: An instruction set architecture is also called computer architecture is an abstract model of a…
Q: It's important to know what makes up an information system's core components. What is the difference…
A: Introduction: When it comes to information systems, they are a collection of interconnected…
Q: Using a database, it is feasible to do both forward and backward recovery.
A: Introduction: Database recovery is required when a database instance fails (and is restarted) or…
Q: What happens if a process attempts to visit a page that hasn't been cached? What are the phases in…
A: Introduction Given: We are given to discuss the concept of demand paging where the page is not in…
Q: Computer science Explain how cryptographic mechanisms can be used to guarantee the following basic…
A: Introduction: Computer science Explain how cryptographic mechanisms can be used to guarantee the…
Q: Do you believe that the graph isomerphism problem belongs in the P class? Why, if this is the case?…
A: Isomorphism between two graphs It is said that two graphs are isomorphic when they contain the same…
Q: What is the simplest approach for me to fix a Node Constructor in my Java program? The current issue…
A: Summary There must be some problem with the constructor or class
Q: How can ICT and technology tools assist teaching and learning? Why is it vital?
A: ICT promotes student engagement and information retention in the classroom: Students become more…
Q: List any five aspects of the Human Eye that allow it to collect pictures in the actual world.
A:
Q: ich network topology would you propose as a starting point?
A: Lets see the solution.
Q: Is the internet beneficial for those with physical or mental disabilities? What new technology do…
A: The internet improves the lives of visually impaired individuals. They have the following…
Q: in the BFS alg
A: A graph traversal algorithm begins crossing from root node and investigate every one of the…
Q: t, and the Stack Segment should all be distinguished. Determine the combination of registers that…
A: Code segment (CS): code segment is utilized for tending to memory area in the code segment of the…
Q: When it comes to people with impairments, what function does the internet play in their lives? What…
A: Introduction: In our lifetime, science has progressed far beyond the limits of our imagination. We…
Q: Five typical network topologies should be able to be identified. Which one do you see as the most…
A: Introduction Five typical network topologies should be able to be identified. Which one do you see…
Q: What exactly is the content switch?
A: answer is
Q: Which two protocols manage neighbor discovery processes on IPv4 networks?
A: Answer is in step2
Q: Create an algorithm that will list all prime numbers from 10 to 50.
A: An algorithm is a step-by-step process to solve a given problem. prime numbers between 10 and 50…
Q: Why is a secret communication from Alice to Bob encrypted using the shared symmetric key rather than…
A: Institution: Asymmetric encryption is also known as public-key encryption, except it uses a key pair…
Q: What are the implementation challenges with Dates and Times?
A: Dates and Times data types in SQL can create implementation issues while the implementation process…
Q: When a client calls a method on a remote object, it is activated.
A: Remote Object Activation: 1.The capacity to naturally make remote objects, set off by demands for…
Q: Explain the two basic functions of an operating system.
A: answer is
Q: What happens if a process attempts to visit a page that hasn't been cached? What are the phases in…
A: Introduction \given: We are given the opportunity to discuss the notion of demand paging, in which…
Q: What are some effective strategies for preventing data loss?
A: Given: We have to discuss what are some effective strategies for preventing data loss.
Q: In what industries does Web Engineering play a role? What are some of the challenges involved in…
A: Industries that pay top salaries for software : Web engineering is the practice of applying…
Q: How has the convergence of computers, telecommunications, and media led in the creation and…
A: Extend your discussion of how the convergence of computers, telecommunications, and media has led to…
Q: Which network topology would you propose as a starting point? Why?
A: Introduction
Q: Is there any other way for Peter to prevent losing his password except using key recovery?
A: Combination of uppercase and lowercase letters: Symmetric and asymmetric encryption are the two…
Q: The Simple Object Access Protocol is located in which of the following OSI layers? A. Data link; B.…
A: According to the question The SOAP relative complexity has led to developers and prefer simpler…
Q: Are there advantages and disadvantages of doing internal static analysis in software development?
A: Development: Static analysis, often known as static code analysis, is a technique of troubleshooting…
Q: Use R only! Screen shot code and output •Rewrite the perceptron() function so that it will use…
A: Perceptron You can just go through my previous post on the perceptron model (linked above) but I…
Q: In the context of a block chain Internet of Things application, describe the overall notion of…
A: Introduction: A unique sensor data storage, visualisation, and remote administration platform,…
Q: When it comes to VES modelling, what's the difference between a smooth model and a layered model?
A: Modelling: The setup and usage of several model types for the inversion of a final smooth model,…
Q: You may produce several copies of a video with different quality levels using compression…
A: The two key video compression techniques used in video: We must discuss the usage of video…
Q: In order to establish whether or not a new information system project is a success, consider the…
A: Introduction: List FOUR elements that are considered when determining whether or not a new…
dont dont dont post copied content strict warning dislike for sure answer only 100% known
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- The affine cipher (transformation) C≡3P+24 (mod26) was used to encrypt a message. The resulting ciphertext is RTOLKTOIK. Decrypt this message. A=0,B=1,C=2,...,Y=24,Z=25Decrypt "FYDQAIRR" if it is known to have been encrypted with the affine cipher and c→M and k→C are knownPerform the Encryption and then the Decryption for the Hill Cipher where the Plain text: "POH" and the key is: "GYBNQKURP".
- Perform the Encryption using the Hill Cipher where the Plain text: "POH" and the key is: "GYBNQKURP".The affine cipher f(p) = (9p + 10) mod 26 is used to obtain the encrypted message F EMV Z,where p is the two digit representation (00-25) of each character in the original message. What is the original message?Decrypt "RXJFKZYH" if it is known to have been encrypted with the affine cipher and c→J and k→N are known
- Find the decryption key for the affine cipher with n=26, a=5 and b=8. Encrypt the messagewith the code 15 and 19Q17. Use the values below to decrypt the numerical ciphertext c = 133 , using the cryptoscheme: Encryption (m + k) mod N = c Decryption (c - k) mod N = m N = 50 k = 42The ciphertext text “GEZXDS” was encrypted by a Hill cipher with a 2 × 2 matrix. The plaintext is “solved”. Find the encryption matrix M.
- What is the formula used for encryption of data using affine cipher(a,b are constants and x is the numerical equivalent of a letter to be encrypted)? 1. ax+b 2. (ax+b)%26 3. a(x^2) +bx 4. (a(x^2) +bx)%26Encrypt the plaintext “CAT” using the following RSA model if A uses P = 11 and Q = 19 whereas B uses P = 13 and Q = 17. Then Decrypt the cipher to get back the plaintext.Decrypt the word RWLSR if it was encrypted using an alphabetic Caesar shift cipher that starts with shift 9 (mapping A to J), and shifts one additional space after each character is encrypted.

