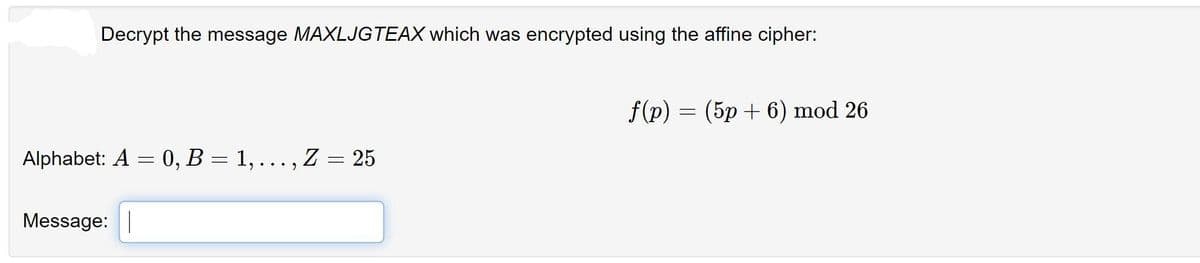
Decrypt the message MAXLJGTEAX which was encrypted using the affine cipher: Alphabet: A = 0, B = 1, ... , Z = 25 Message: | f(p) = (5p+6) mod 26
Q: What are the benefits of internet usage for people with special needs? If you think about the…
A: Introduction The internet improves the lives of those who are blind. The following alternatives are…
Q: How exactly might cloud computing help an enterprise, and what are its highest priorities?
A: Given: "Cloud integration" refers to tools and technologies that connect different applications,…
Q: ake a look at these five significant ethical concerns that relate to computer nd see what you think.
A: Ethical concerns refers to the moral principles and values that guide decision-making in regards to…
Q: Is it correct to say that ScoutSuite, Pacu, and Powler are all online protection tools? Cloud…
A: Introduction: As cloud computing technology advances, it is very rare for IT teams to find gaps in…
Q: Could you describe the four most significant benefits of continuous event simulation?
A: Integrating Continuously: Continuous integration (CI) helps developers produce software more…
Q: Could you describe the four most significant benefits of continuous event simulation?
A: Integrating in a Constant Manner: Continuous integration (CI) improves the process of developing…
Q: In the event that an unlawful conduct is committed online, what assumptions are often made about the…
A: Given: We have to discuss In the event that an unlawful conduct is committed online, what…
Q: When comparing logical and physical data flows, what should you look for? The metadata of a data…
A: When comparing logical and physical data flows, you should look for differences in the way the data…
Q: Please written by computer source Where do i create an IPO? like on word or python or something…
A: The stock market is where publicly traded companies' stocks are traded. An initial public offering…
Q: Could you provide me an actual SQL database and explain how it functions?
A: Using electronic storage technologies, a database is created to keep and retrieve information about…
Q: Create introduction about the use of artificial intelligence, machine learning, and deep learning,…
A: Artificial intelligence (AI), machine learning (ML), and deep learning (DL) are technologies that…
Q: rating sys
A: Introduction: A programme, or group of applications, known as a user interface, enables a user to…
Q: //go method to be used to process a two-dimensional array public static int go (int[] [] Mat) { int…
A: EXPLANATION: In the given go function, their are two for loop out of which one is outer loop and…
Q: Individuals often express the following concerns about the incidence of crimes committed online:
A: Identity theft: People are concerned that their personal information, such as their Social Security…
Q: In order for mobile technology to become widespread, we must first overcome a number of challenges.…
A: The user's mobile device follows them everywhere they go: It consists of computer hardware, portable…
Q: Could a data breach really damage cloud data storage? Is there anything you can do to counter this,…
A: Data breaching in Cloud Computing is described as the accessing private information that is stored…
Q: Do you think the Symbian, Android, or iOS devices slowed down because of the algorithm employed to…
A: The solution is given in the below step
Q: Provide a succinct explanation of a few of the difficulties that are now being experienced by global…
A: Global information systems are the systems used by many governments throughout the world.Global…
Q: Why is it very crucial to conduct a successful criminal investigation with proper documentation?…
A: Documentation can help to protect the rights of the accused and ensure that the investigation is…
Q: Differentiating between a low-level programming language and a high-level programming language…
A: Disparaging Expressions: Languages that provide little to no feedback from the PC's guide set design…
Q: What kinds of support are available to an employee who isn't living up to their full potential as a…
A: There are several types of support that may be available to an employee who is not living up to…
Q: In terms of cloud safety, what does the "shared responsibility paradigm" entail?
A: Please refer to the following step for the complete solution to the problem above.
Q: How dissimilar are cloud security solutions like ScoutSuite, Pacu, and Powler? What are some ways…
A: Scoutsuite is a programme that may be used to identify cloud security vulnerabilities. It employs…
Q: Include a summary of the requirements for training and certification, as well as some examples taken…
A: Training and certification are necessary(provide): If a person, thing, or organisation has…
Q: An example of a recent security violation involving access control or authentication might be…
A: Given: Describe a recent security breach that included access control or authentication that was…
Q: What are the benefits of internet usage for people with special needs? If you think about the…
A: The Internet provides many benefits for people with special needs, including access to information,…
Q: In the company's privacy policy, you must provide information about how Personal Operating Solutions…
A: Personal Operating Solutions has the following privacy policies: Personal Operating Solutions…
Q: Give an overview of how a NoSQL database differs from a relational database. Name the four distinct…
A: RDBMS (Relational Database Management Systems): RDBMS stands for Relational Database Management…
Q: When individuals are purchasing a computer, they sometimes might get the most expensive computer…
A: A computer is a digital electronic machine that can be programmed to automatically perform a series…
Q: Give an example of a large-scale application and elaborate on whether or not explicit declaration is…
A: Explicit declaration: ## It is the existence of an identifier inside a DECLARE statement, label…
Q: What features and efficiencies are must-haves for data center uptime?
A: Uptime is the single most essential aspect of a data center. In addition to using software and…
Q: How would you, as a data center systems administrator, go about planning, building, and maintaining…
A: As a data center systems administrator, I would approach planning, building, and maintaining an…
Q: Take a look at these five significant ethical concerns that relate to computer systems and see what…
A: The five moral aspects of information systems are as follows: 1. Your rights and duties when it…
Q: Is (p ↔ q) the negation of ((p^ā) V (q^p)) ? Prove your answer.
A: Simply said, a proposition is a statement. The relationship between assertions is examined in…
Q: In Cisco Packet Tracer, how can I restrict a Gigabit link's throughput to a subset of the available…
A: Information in this section is recommended by Cisco. VLANs are a key component that enables network…
Q: Organizations often encounter several challenges when attempting to migrate their operations to a…
A: Introduction: Regular backups, dependable power sources, paths for connecting data, security…
Q: What are the pluses and minuses of a cloud-based, global network?
A: Cloud computing is a technology that allows organisations to give compute services to their…
Q: regions REGION_ID NUMBER REGION_NAME VARCHAR2(25) departments DEPARTMENT_ID NUMBER DEPARTMENT NAME…
A: Please find the respective SQL statements for the queries: We use aggregate functions like count and…
Q: internet criminal activity and the repercussions these acts have on society 2) Identify the measures…
A: The answers are given in the below steps
Q: How do you think computers and social media influence your friendships and those of your peers? In…
A: In addition to problems such as cyberbullying, oversharing, and sexting, social media can also…
Q: An observation indicates that the initial population of grey seals P(t) nearby a harbor is 25 and…
A: Euler's method is a simple numerical technique for approximating solutions to ordinary differential…
Q: actions that will cut down on the number of temptations and diversions that will slow down the…
A: How to Deal with Distractions and Interruptions at Work Reduce or stop self-distractions. Start with…
Q: Is it a smart move to deploy anything that even remotely resembles this "Employee Management System"…
A: Introduction: An employee management system is software that allows your employees to give their…
Q: There are several models used in software development, and each one has its own strengths and…
A: Given: Many different models are used in software development. They are comparable to: RAD Model…
Q: hich is better for a small, rapidly developing business: an on-premise CRM system, an on-demand CRM…
A: Answer is
Q: What does it mean for us to have everything connected to the internet all the time? Think of…
A: Introduction: IoT is a network of internet-connected, networked devices that may automatically…
Q: What kinds of training should be offered to workers so that there is a lower chance that "rules of…
A: Rules of Behavior are security controls about user responsibilities and particular behaviour…
Q: Regarding the offense of committing crimes online, what conclusions or suggestions may be made?
A: The answer for the above question is given in the below step for your reference
Q: ial interaction, and governance are just a few of the many themes covered by computer ethics. To…
A: Introduction: System boundaries must include distinct individuals and their workstations because…
Q: precise meaning of the term "computer network" What are all the components that go into making up…
A: A computer network is a collection of interconnected devices, such as computers, servers, and…
Step by step
Solved in 2 steps

- The affine cipher (transformation) C≡3P+24 (mod26) was used to encrypt a message. The resulting ciphertext is RTOLKTOIK. Decrypt this message. A=0,B=1,C=2,...,Y=24,Z=25Perform the Encryption and then the Decryption for the Hill Cipher where the Plain text: "POH" and the key is: "GYBNQKURP".Perform the Encryption using the Hill Cipher where the Plain text: "POH" and the key is: "GYBNQKURP".
- Decrypt the word RWLSR if it was encrypted using an alphabetic Caesar shift cipher that starts with shift 9 (mapping A to J), and shifts one additional space after each character is encrypted.The affine cipher f(p) = (9p + 10) mod 26 is used to obtain the encrypted message F EMV Z,where p is the two digit representation (00-25) of each character in the original message. What is the original message?Decrypt "FYDQAIRR" if it is known to have been encrypted with the affine cipher and c→M and k→C are known
- Encrypt the plaintext “CAT” using the following RSA model if A uses P = 11 and Q = 19 whereas B uses P = 13 and Q = 17. Then Decrypt the cipher to get back the plaintext.What is the formula used for encryption of data using affine cipher(a,b are constants and x is the numerical equivalent of a letter to be encrypted)? 1. ax+b 2. (ax+b)%26 3. a(x^2) +bx 4. (a(x^2) +bx)%26Q17. Use the values below to decrypt the numerical ciphertext c = 133 , using the cryptoscheme: Encryption (m + k) mod N = c Decryption (c - k) mod N = m N = 50 k = 42
- Encrypt the message “meet me at the usual place at ten rather than eight o clock”using the Hill cipher with the key = 9 4 5 7 a. Show your calculations and the result.b. Show the calculations for the corresponding decryption of the ciphertext torecover the original plaintext.The ciphertext text “GEZXDS” was encrypted by a Hill cipher with a 2 × 2 matrix. The plaintext is “solved”. Find the encryption matrix M.Use a Caesar Cipher with digraph coding to encrypt the following plaintext: ‘buffer’ with a key ofK=100

