Alphabet: A = 0, B = 1,..., Z = 25
Q: Explain phases of thread lifecycle, in java
A: Introduction Explain phases of thread lifecycle, in java
Q: Create a Binary Search Tree Class with the following Operations: Operations: Insert(int n): Add a…
A: C++ program binary search tree perform following operation:- Insert Find Delete Display
Q: A student is doing research for an assignment on her computer. Is she primarily a network edge or…
A: let us see the answer:- Introduction:- She is primarily working at a network edge so further I will…
Q: Explain why bridged Ethernet cannot be scaled to a network the size of the Internet.
A: Introduction Ethernet is the technology for connecting devices in a wired local area network (LAN)…
Q: What does the term "web server" mean?
A: A web server is a computer that stores web server software and a website's component files. It…
Q: Differenciate entre Sistema and Sistemas Embedidos Let's see them. Can Embeded software be utilized…
A: Definition: System software is used to control, operate, and expand a computer system's processing…
Q: What exactly is a dynamic web page?
A: Dynamic web page : A dynamic web page changes its content every time it is viewed. It's a web page…
Q: What is the definition of digital privacy in the context of evolving technology? Can you provide…
A: Introduction: The terms "security" and "privacy" pertain to the protection of data, whereas the…
Q: What are the benefits of ICT in Education? What are ICT's bad effects on education? Why has ICT…
A: What are the benefits of ICT in education? Information and communication technologies ICT has a…
Q: What is the most successful data extraction approach to utilise in a small firm that relies solely…
A: Introduction: The process of converting unstructured or semi-structured data into structured data is…
Q: What exactly is a virtual switch?
A: let us see the answer:- Introduction:- A virtual switch is a piece of software that enables one…
Q: Define a real-time operating system. Describe how it differs from a regular OS. What do real-time…
A: answer is
Q: What are some effective strategies for preventing data loss?
A: Given: We have to discuss What are some effective strategies for preventing data loss.
Q: List any five aspects of the Human Eye that allow it to collect pictures in the actual world.
A: Human Eye : The Human Eye has five parts to acquire images in the real world. The cornea, iris,…
Q: Do the routing protocols used inside a network and those used outside of a network have different…
A: According to the question the routing protocol always helps to the our network to manage the data…
Q: Distinguish hash from MAC. Show how they may be used to authenticate communications. What…
A: Answer: Hash Vs MAC: The principal distinction is applied: while hashes are utilized to ensure the…
Q: How would you respond to the following question: Spawning of processes and context switching
A: Spawning Procedure: Process spawning is a method/technique in OS that creates a child process by…
Q: What distinguishes the software development process from software modeling? Describe how one aids…
A: Software Development Process: A software development process is a method of separating software…
Q: What happens if a process attempts to visit a page that hasn't been cached? What are the phases in…
A: Introduction \given: We are given the opportunity to discuss the notion of demand paging, in which…
Q: What is the definition of a property?
A: Introduction: Each item has a unique set of properties that influence both its appearance and its…
Q: Compare and contrast cache and virtual memory, as well as provide an example scenario in which both…
A: Introduction: It is a component or system in computing that stores data for immediate use in a…
Q: What distinguishes the software development process from software modeling? Describe how one aids…
A: Process of Software Development: In software engineering, a software development process is a method…
Q: Do you believe that the graph isomerphism problem belongs in the P class? Why, if this is the case?…
A: Isomorphism between two graphs It is said that two graphs are isomorphic when they contain the same…
Q: How is an embedded computer different from a general purpose computer?
A: General Purpose computer : A general purpose computer system is what you think of when someone says…
Q: In the context of a block chain Internet of Things application, describe the overall notion of…
A: Introduction: A unique sensor data storage, visualisation, and remote administration platform,…
Q: Interpolation is commonly used in computer graphics. If interpolation is used, choose one that does…
A: Foundation: Interpolation is a statistical strategy for estimating an unknown security's price or…
Q: Computer science Explain how cryptographic mechanisms can be used to guarantee the following basic…
A: Introduction: Computer science Explain how cryptographic mechanisms can be used to guarantee the…
Q: Determine how piracy has evolved over time. Computer science
A: Introduction: We will learn what piracy is and how it has evolved over time.
Q: Interpolation If interpolation is commonly used in computer graphics. is used, choose one that does…
A: Interpolation is a statistical technique that uses related known variables to predict an unknown…
Q: What exactly is DMA? Briefly explain.
A: Introduction: DMA is an abbreviation for Direct Memory Access. DMA essentially halts the processor's…
Q: Consider the following scenario: a large project with a strong architecture, partially specified…
A: Software Development Model: An IT software development process is a grouping of software development…
Q: PAP or CHAP may be used to establish PPP authentication. Is one more secure than the other in this…
A: IntroYou may choose between PAP and CHAP authentication when setting PPP authentication. Which of…
Q: What are some effective strategies for preventing data loss?
A: answer is
Q: What are the downsides of symmetric encryption's key management?
A: Symmetric Encryption's: Symmetric key encryption encrypts and decrypts data using the same key.…
Q: What happens if a process attempts to visit a page that hasn't been cached? What are the phases in…
A: Memory Demand: Memory Demand is calculated using performance counters and represents the amount of…
Q: Computer science Short answer What is a local variable’s scope?
A: Introduction: The local variable’s scope:
Q: You've been requested to create and make a case for employing a system architect for a new project…
A: Architectural design is a creative process: In which you create a system organization that meets all…
Q: b) Suppose the server begins to transmit the packet at time t=0. when t= transmission delay, where…
A: The answer is
Q: A descriptive model must have what characteristics and properties?
A: Development: A descriptive model depicts the connection between a system or other object and its…
Q: Compare and contrast TWO (2) advantages of adopting Internet Protocol version 6 (IPv6) against…
A: Introduction: When comparing Internet Protocol version 6 (IPv6) to version 4, there are a number of…
Q: Can an AES key be encrypted using a shared secret? Defend your response Compare hash function with…
A: Can an AES key be encrypted using a shared secret? Defend your response Compare hash function with…
Q: What kind of device are you trying to connect to? Do you have access to cloud-syncing tools and…
A: The Answer is in step2
Q: What are the various methods for resolving a stalemate once it has been identified?
A: Introduction: 1. method termination: In order to avoid a dead end, we will simply terminate one or…
Q: es, describe what telligence applicat Tii
A: intelligence architecture alludes to the guidelines and principles that administer information…
Q: Short Answers: Q. In computer science, what is the complete form of APIPA?
A: Introduction: The Networking Theory is used to answer the question.
Q: What exactly is a virtual PBX?
A: answer is
Q: Consider a two-link network where Host A is connected to the router by a 1 Mbps link with 10 ms…
A: The answer is
Q: What exactly is TCP (Transmission Control Protocol)?
A: Introduction: The Transmission Control Protocol (TCP) is a communication protocol that allows…
Q: Write the following English sentences in symbolic form- You will qualify GATE only if you work…
A: Hi there, Please find your solution below, I hope you would find my solution useful and helpful.…
Q: Give a thorough explanation of what it means to sync computers and mobile devices. How many methods…
A: Introduction: The simultaneous exchange of information is referred to as synchronisation.
Step by step
Solved in 2 steps

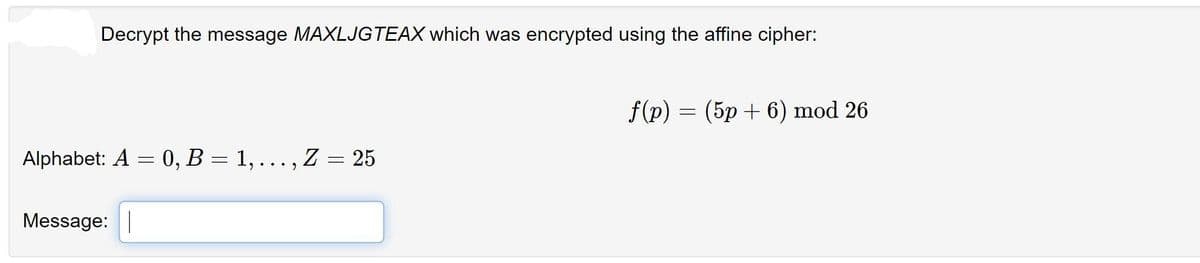
- The affine cipher (transformation) C≡3P+24 (mod26) was used to encrypt a message. The resulting ciphertext is RTOLKTOIK. Decrypt this message. A=0,B=1,C=2,...,Y=24,Z=25Decrypt "FYDQAIRR" if it is known to have been encrypted with the affine cipher and c→M and k→C are knownPerform the Encryption and then the Decryption for the Hill Cipher where the Plain text: "POH" and the key is: "GYBNQKURP".
- Perform the Encryption using the Hill Cipher where the Plain text: "POH" and the key is: "GYBNQKURP".The affine cipher f(p) = (9p + 10) mod 26 is used to obtain the encrypted message F EMV Z,where p is the two digit representation (00-25) of each character in the original message. What is the original message?Decrypt "RXJFKZYH" if it is known to have been encrypted with the affine cipher and c→J and k→N are known
- Find the decryption key for the affine cipher with n=26, a=5 and b=8. Encrypt the messagewith the code 15 and 19Q17. Use the values below to decrypt the numerical ciphertext c = 133 , using the cryptoscheme: Encryption (m + k) mod N = c Decryption (c - k) mod N = m N = 50 k = 42The ciphertext text “GEZXDS” was encrypted by a Hill cipher with a 2 × 2 matrix. The plaintext is “solved”. Find the encryption matrix M.
- What is the formula used for encryption of data using affine cipher(a,b are constants and x is the numerical equivalent of a letter to be encrypted)? 1. ax+b 2. (ax+b)%26 3. a(x^2) +bx 4. (a(x^2) +bx)%26Encrypt the plaintext “CAT” using the following RSA model if A uses P = 11 and Q = 19 whereas B uses P = 13 and Q = 17. Then Decrypt the cipher to get back the plaintext.Decrypt the word RWLSR if it was encrypted using an alphabetic Caesar shift cipher that starts with shift 9 (mapping A to J), and shifts one additional space after each character is encrypted.

