Describe how you would react to the following scenarios: ■ A senior marketing manager informs you that one of her employees is looking for another job and she wants you to give her access to look through her email. A vice president of sales informs you that he has made a deal to provide customer information to a strategic partner and he wants you to burn all of the customer informa- tion onto a CD. You start monitoring one of your employees' email and discover that he is having an affair with one of the other employees in the office. ■ You install a video surveillance system in your office and discover that employees are taking office supplies home with them.
Describe how you would react to the following scenarios: ■ A senior marketing manager informs you that one of her employees is looking for another job and she wants you to give her access to look through her email. A vice president of sales informs you that he has made a deal to provide customer information to a strategic partner and he wants you to burn all of the customer informa- tion onto a CD. You start monitoring one of your employees' email and discover that he is having an affair with one of the other employees in the office. ■ You install a video surveillance system in your office and discover that employees are taking office supplies home with them.
Principles of Information Systems (MindTap Course List)
13th Edition
ISBN:9781305971776
Author:Ralph Stair, George Reynolds
Publisher:Ralph Stair, George Reynolds
Chapter14: Ethical, Legal, And Social Issues Of Information Systems
Section: Chapter Questions
Problem 1CE
Related questions
Question
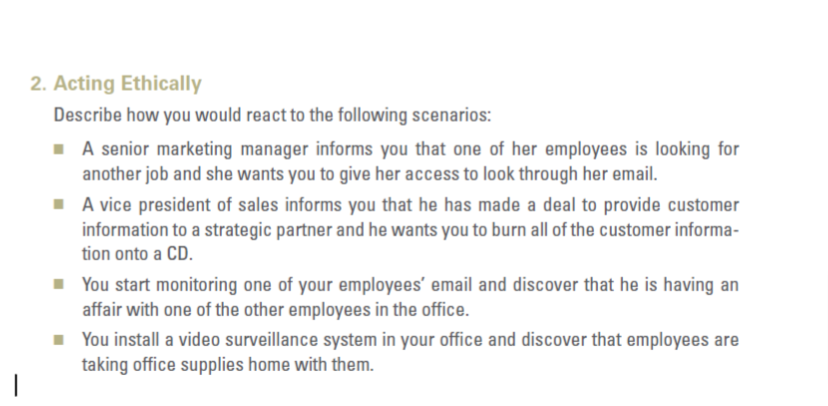
Transcribed Image Text:2. Acting Ethically
Describe how you would react to the following scenarios:
■ A senior marketing manager informs you that one of her employees is looking for
another job and she wants you to give her access to look through her email.
■ A vice president of sales informs you that he has made a deal to provide customer
information to a strategic partner and he wants you to burn all of the customer informa-
tion onto a CD.
■You start monitoring one of your employees' email and discover that he is having an
affair with one of the other employees in the office.
■ You install a video surveillance system in your office and discover that employees are
taking office supplies home with them.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781305971776
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Fundamentals of Information Systems
Computer Science
ISBN:
9781337097536
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Fundamentals of Information Systems
Computer Science
ISBN:
9781305082168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781305971776
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Fundamentals of Information Systems
Computer Science
ISBN:
9781337097536
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Fundamentals of Information Systems
Computer Science
ISBN:
9781305082168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning
