Design a contact form using HTML CSS and javascript that resembles the one shown and perform validate both forms using JavaScript (internal or external)
Q: Use the hardware description language (HDL) to document the following logic circuit: X Z > F
A: Below I have provided hand written solution of the given question
Q: Explain following in IEEE 802.11 WLANs with timing diagram. i) DFWMAC-DC ii) DFWMAC-DCF with…
A:
Q: In Python IDLE Write a program that reads the file’s contents and determines the following:…
A: As I have read the guidelines I can provide answers to only 1 part of the questions in case of…
Q: needs to allocate addresses for two organization ea with 500 addresses, two organizations each with…
A: The answer is
Q: the installation steps of installing Windows Active Directory for a domain called afribank.co.za.…
A: It is defined as a directory service that runs on Microsoft Windows Server. The main function of…
Q: Briefly outline what is the outcomes from the Linux command "echo $PATH"
A: Let's first understand what is echo command . The echo is like printing something on the terminal .…
Q: Alice and Bob use the ElGamal scheme with a common prime q= 131 and a primitive root a = 6. Let…
A: The answer is
Q: Explore what a hacker can do to make use of the coding problem of buffer overflow.
A: Given: We have to discuss Explore what a hacker can do to make use of the coding problem of buffer…
Q: Find the maximum flow of graph K₁. a 5 b 8 8 a C Od c 10 10 14 15 12 16 d K₁ 12 t
A: Given graph contains, Set of vertices= {s, a, b, c, d, t} Source node is s and sink node is t. It…
Q: What are the difficulties in troubleshooting DNS errors?
A: What is DNS? DNS, or domain name system, is the mechanism that links website domain names (like…
Q: Question 02: Identify the types of addressing modes used in following instructions: No Instruction .…
A: The solution of the question is given below in step 2.
Q: Write a note on Computer virus
A:
Q: if we segregate the binary with 4 bits each we will get to know how many bits are there " 4 bits…
A: In this question we will answer the correct form of bits and bytes for the 2018 decimal number in…
Q: c++ work in visual studios. Please read everything and answer. I am making a 2D shooter game. My…
A: It is defined as an IDE made by Microsoft and used for different types of software development such…
Q: What is the role of ergonomics in the computing field? Describe the ergonomic safety precautions as…
A: Introduction: Without giving it much thought, people spend the majority of their days in front of…
Q: make me a script of explanation on how this function and the code itself.
A: Line 1-2 : contain necessary header files of c++ . Line 3-12 : contain a structure having name…
Q: In artificial intelligence, what is rationality and logical reasoninga ?
A: Introduction: There are two terminologies used to describe artificial intelligence: Rationality…
Q: Write the equivalent assembly code if you were to translate from C to Assembly: for (i=0; i<10; i++)…
A: The given question instructs to convert the given c code to its equivalent assembly code: The given…
Q: Write TRUE if the truth value of the statement is incorrect, otherwise write FALSE. Sky is blue…
A: The answer is given below.
Q: Distinguish between system analysis and system design, and discuss the importance of the two in…
A: System analysis is a process which is used to study a system including an information system that…
Q: Write a note on Computer virus
A: Introduction • A virus is a piece of terrible programming that runs without the client's assent. •…
Q: what is the introduction of mobile security and mobile infrastructure? what are the examples of…
A: Introduction: The term "mobile device security" describes the safeguards put in place to guard…
Q: Write a C++ function named is Prime that takes a positive integer argument and returns true if the…
A: Here I have defined the function named isPrime(). Inside the function, I have used a loop to…
Q: Given the following grammar in BNF:→=→X | Y | Z →%→? → () a) Change the grammer rules so that! and…
A: New Grammar Rules → < var > = → X | Y | Z → % → ? → ( ) → ! → ~ < var
Q: You can choose to use PAP or CHAP while configuring PPP authentication. Which one is the safest…
A: CHAP IS more secure Explanation:- Secure protocol The authentication protocols go by the acronyms…
Q: Provide a Big Data Architecture for a business that offers its clients a flight information service.
A: Big data architecture is used to handle ingestion, analysis and processes of data which is too big…
Q: A) fcx) = (x + log (log (3² + x²)) ; fcx³E 0(³√x) B) f(x) = 1g (2x.x²); f(x)= (x) (H)
A: (A) f(x) =under root x+ log(log(3^x+x^2)); f(x) <-O(xcuberoot) (B) f(x) =log(2^x.x^2); f(x)…
Q: List the different types of malicious code and compare the virus protection tools.
A:
Q: An ISP is granted a block of addresses starting with 180.100.0.0/16. The ISP needs to distribute…
A:
Q: Write TRUE if the truth value of the statement is incorrect, otherwise write FALSE. Arctic Ocean is…
A: answer starts from step 2
Q: Write the pseudocode for an application that will implement the requirements below. Declare a…
A: Pseudocode is a made-up, informal language that aids in the creation of algorithms by programmers. A…
Q: What is the ouput of the following CO char ch='c'; ch -=2; System.out.println(ch);
A: SUMMARY Question 1Answer : option ( C) Question 2Answer : option ( A) CharactersMost of the time,…
Q: Write a function called translate_to_italian () that takes a string as a parameter (a colour).…
A: We chose C++ to execute this logic but this can be applied in any programming language.
Q: Computer science: A work breakdown structure is what? What resources and equipment are utilised to…
A: Work breakdown structure:- A WBS in the fields of project management and systems engineering is an…
Q: A dope vector is what? What function does it fulfil? Computer science
A: Compilers utilize a data structure called a "Dope Vector" to record precise metadata about the same…
Q: (Q11.6, a2, The OS organizes the directory of files based on various methods such as Single-Level…
A: The directory is the name of the container that is used to store folders and files. The files and…
Q: As a result of technical improvements, the majority of appliances are now wirelessly enabled. Is it…
A: Introduction: There is a growing trend in the residential, commercial, and industrial sectors to…
Q: Explain various multiplexing techniques used for wireless data network.
A: Multiplexing is a technique in which we use different wireless data network techniques such as:…
Q: You will write a program that allows the user to enter 10 songs and their artists into a playlist…
A: C++ program: #include <iostream>#include<string>#include<cstdio>using namespace…
Q: What are some instances of good website design and examples of terrible website design?
A: Introduction: Website designs: => Web design encompasses several abilities and disciplines…
Q: Write a program that uses an array (of size 10) to demonstrate how to use the linear search…
A: Java: Java is a high level, class based, object oriented programming language. It was developed by…
Q: Why is ASCII storage slower than binary storage?
A: Comparing a binary file to a text file with the same amount of data shows that a binary file is…
Q: 2. Explain Simple classification Techniques ? (discuss all 4)
A: Simple Classification Techniques: In this section, we will discuss different classification…
Q: Question 2 P2.2 Using the key matrix A = [22]. decode the message: 36 50 53 76 29 34 15 22 37 64…
A: Following is the process to decode a message Compute the inverse of the matrix that was utilized to…
Q: Question 5 The description of _______ can be given by a lexical specification, which is usually…
A: In this question we have to fill the blanks in the description given. Let's answer
Q: How and where should I utilize octal cable?
A: Octal cable This cable is required to connect the console ports of a Cisco 2509 or 2511 router to…
Q: The project team will embark on a data take-on exercise because an operational system requires a…
A: Before going on how DBMS interface or in other words Database Interface works let us first know what…
Q: Explain the following terms and describe what they are used for: HTML, URL, XML, Java, JSP, XSL,…
A: HTML is a hypertext markup language designed for the formatting system for displaying material…
Q: Apply the knowledge learnt in this module and create a Java program using NetBeans that takes in two…
A: Program - import java.util.Scanner;public class DivisionCalc{public static void main(String…
Q: Why are Software engineering Standards regarded as Process Standards rather than Product Standards?
A: Introduction: Product: Any software generated in response to a customer's request is referred to as…
Design a contact form using HTML CSS and javascript that resembles the one shown and perform validate both
forms using JavaScript (internal or external)
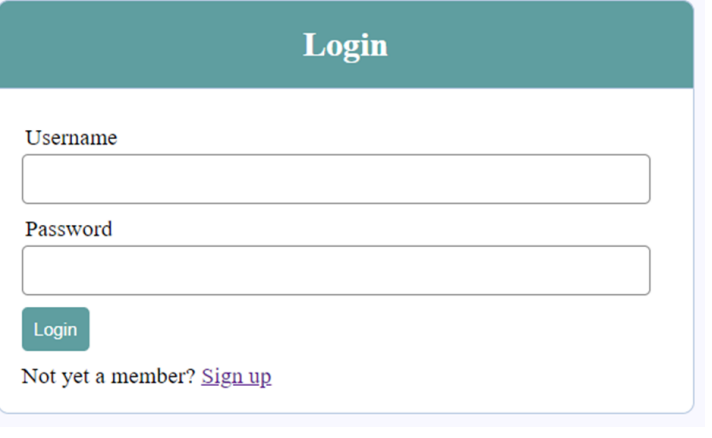
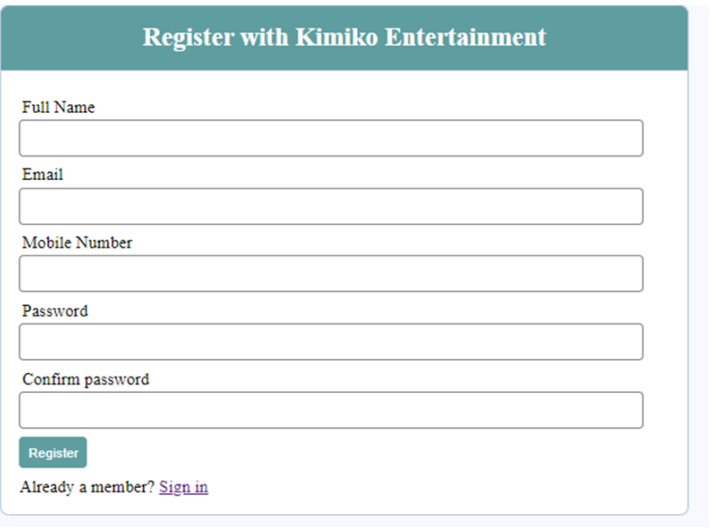
Step by step
Solved in 3 steps with 6 images

- In Form1: Create a List of Employees Define a method preloadEmployeeList with at least 2 employees of each type Define a method displayEmployeeList (name, empid, bimonthsalary,vacation accrued) to a JTable Define a method DisplayEmployeeList2. To display to a JTextArea the data returned by ToString() method.This is what I did since mine is in Java:private String generateId(String ipAddress){ if(ipAddress != null){ String [] to4thOctet = ipAddress.split("."); String toParse = to4thOctet[3]; return BuildConfig.USER_ID + toParse; } else{ return username; } }Create the Singly Linked List after having executed the following methods. Each item must have a headand tailreference. Whenever a method is not expected or invalid, write Exception. Only the process not the code •addHead("Dancing") •addHead("Backup") •addHead("Backup") •addTail("Backup") •addTail("Backup") •removeHead()
- Please answer this question properly must attach output screenshot IN PYTHON create a User class with with 2 attributes : first_name, last_name, hireDate, age, job_title . create a method named describe_user() that prints all the info for the user create a 'great_user() method that prints a personalized greeting to the user add an attribute named login_attempts to the user class from 1 above write a method called increment_login_attempts() that increments the login_attempts value by 1 write another method called reset_login_attempts () that resets the value of login_attempts to 0 Make an instance of the User class and call increment_login_attempts() several times. Print the value of login_attempts to make sure it was incremented properly. Make an instance of the User class and call reset_login_attempts(). Print the value of login_attempts to make sure it was reset to 0. Write a class called Admin that inherits from from User class you wrote above Add an attribute, privileges, that…User: Make a class called User. Create two attributes called first_name and last_name,and then create several other attributes that are typically stored in a user profile. Makea method called desctibe_user() that prints a summary of the user's information. Makeanother method called greet_user() that prints a personalized greeting to the user.Then - Create several instances representing different users, and call both methods for each user. Admin: Write a class called Admin that inherits from the User class. Add an attribute,privileges, that stores a list of strings like "can add post”, "can delete post”, "can banuser”, and so on. Write a method called show_privileges() that lists the administrator'sset of privileges. Then - Create an instance of Admin, and call your method.Please fill in all the code gaps if possible: (java) public class LinkedListNode { private Object date; private LinkedListNode next; // Constructor: public LinkedListNode (Object data) // You also need to define the getter and setter: public LinkedListNode getNext() public void setNext (LinkedListNode next) public Object getData() public void setData(Object data) }
- python: def typehelper(poke_name): """ Question 5 - API Now that you've acquired a new helper, you want to take care of them! Use the provided API to find the type(s) of the Pokemon whose name is given. Then, for each type of the Pokemon, map the name of the type to a list of all types that do double damage to that type. Note: Each type should be considered individually. Base URL: https://pokeapi.co/ Endpoint: api/v2/pokemon/{poke_name} You will also need to use a link provided in the API response. Args: Pokemon name (str) Returns: Dictionary of types Hint: You will have to run requests.get() multiple times! >>> typehelper("bulbasaur") {'grass': ['flying', 'poison', 'bug', 'fire', 'ice'], 'poison': ['ground', 'psychic']} >>> typehelper("corviknight") {'flying': ['rock', 'electric', 'ice'], 'steel': ['fighting', 'ground', 'fire']} """ # pprint(typehelper("bulbasaur"))#…User: Make a class called User. Create two attributes called first_name and last_name, and then create several other attributes that are typically stored in a user profile. Makea method called describe_user() that prints a summary of the user's information. Make another method called greet_user() that prints a personalized greeting to the user.Then - Create several instances representing different users, and call both methods for each user. Admin: write a class called Admin that inherits from the User class. Add an attribute,privileges, that stores a list of strings like "can add post”, "can delete post”, "can banuser”, and so on. Write a method called show_privileges() that lists the administrator'sset of privileges. Then - Create an instance of Admin, and call your method.1 Create a class called Citizen with the following attributes/variables:a. String citizenIDb. String citizenNamec. String citizenSurnamed. String citizenCellNumbere. int registrationDayf. int registrationMonthg. int registrationYear- Create a class called Node with the following attributes/variables:a. Citizen citizenb. Node nextNode- Create a class called CitizenRegister with the following attributes/variables:a. Node headNodeb. int totalRegisteredCitizens- Add and complete the following methods in CitizenRegister:a. head()i. Returns the first citizen object in the linked listb. tail()i. Returns the last citizen object in the linked listc. size()i. Returns the totalRegisteredCitizend. isEmpty()i. Returns the boolean of whether the linked list is empty or note. addCitizenAtHead(Node newNode)i. Adds a new node object containing the citizen object informationbefore the headNodef. addCitizenAtTail(Node newNode)i. Adds a new node object containing the citizen object information atthe end…
- Question 6 sm.True or False, BindingContext between two objects can be two-way. In that if either object's value changes, it effects the other object. An object can be a control (view) or class object. Question 6 options: True False Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this lineZybooks SDEV 255 2.1.1 Objects Define a method named orderOfAppearance() that takes the name of a role as an argument and returns that role's order of appearance. If the role is not found, the method returns 0. Ex: orderOfAppearance("Elizabeth Swann") returns 3. Hint: A method may access the object's properties using the keyword this. Ex: this.title accesses the object's title property. // Code will be tested with different roles and movieslet movie = { title: "Pirates of the Caribbean: At World's End", director: "Gore Verbinski", composer: "Hans Zimmer", roles: [ // Roles are stored in order of appearance "Jack Sparrow", "Will Turner", "Elizabeth Swann", "Hector Barbossa" ], orderOfAppearance: function(role) { }}; There is a Lord of the rings test that tests orderOfAppearance for "Saruman" but it is not shown. Heres my current code i tried if(role!==this.orderOfAppearance[role]) return "3"; else return…Create a program that uses classes, polymorphism, and enums to monitor blizzards in Europe, with class members including the blizzard name, location, and snowfall amount, with a continuous menu to update, delete, display, search and add data stored in a collection. The application should have a menu that allow users to: • Add a new item to the collection. • Display all the items in the collection. • Search for a specific item. • Exit the application by pressing 0. The application should also display any error messages if the user enters invalid input. Coding Requirements: 1. Demonstrate applied use of foreground color and change in console title 2. Classes created and apply generics, abstract, and polymorphism

