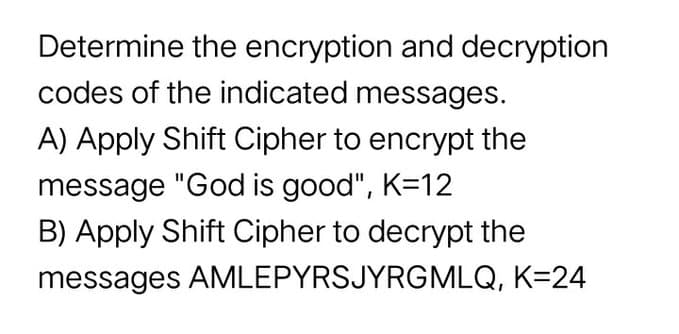
Determine the encryption and decryption codes of the indicated messages. A) Apply Shift Cipher to encrypt the message "God is good", K=12 B) Apply Shift Cipher to decrypt the messages AMLEPYRSJYRGMLQ, K=24
Q: Assume that product codes are formed from the letters V, S, and Q, and consist of 4 not necessarily…
A: 1). For 4 letter product code to be arranged with the letters V, S and Q, the first position is…
Q: (i) How many bit strings of length 8 start with 0 and end with 0? (ii) How many bit strings of…
A: NOTE: According to guideline answer of first three subpart can be given, for other please ask in a…
Q: Suppose that a password for a computer system must have at least 6, but no more than 9 characters,…
A: Given, a password for a computer system must have at least 6, but no more than 9 characters, where…
Q: 2) Each type of machine part made in a factory is stamped with a code of the form…
A: We can use :- 26 letters, 10 digits, 10 digits (as digits can be repeated) Total number of…
Q: At a certain company, passwords must be from 4-6 symbols long and composed from the 26 uppercase…
A: Let us consider there n number of objects, and r to be chosen such that repetition is allowed; then,…
Q: each character in a password is either a digit(0-9) or lowercase letter (a-z). how many valid…
A: There is total 10 digits, such that 0, 1, 3, …., 9 and there is total 26 lowercase letters, such…
Q: Each character in a password is either a digit [0-9] or lowercase letter [a-z]. How many valid…
A: We need to find the total number of valid passwords with given restrictions. The solution is given…
Q: b.Given Bob's public key of (85, 7) and private key of (85, 55), show how Alice can encrypt m=5 to…
A: Given: b) Given Bob's public key of (85, 7) and private key of (85, 55), To show how Alice can…
Q: A nine character password has been randomly assigned by using capital and lower case letters. In how…
A: Given : A nine character password has been randomly assigned by using capital and lower case letters
Q: 1. What is the largest 16-bit binary number that can be represented with (a) unsigned numbers? (b)…
A:
Q: How many five-letter passwords can be formed from the letters {A, B, J, K, X, Z} under the following…
A: From the provided information, The letters are {A, B, J, K, X, Z} Total letters = 6
Q: A passcode is to be created from 2 letters, 2 digits, and 2 special characters (consisting of ?,!,…
A: Combination only includes number of ways of selection whereas, permutation includes number of ways…
Q: A pass code for an account consists of 2 letters followed by 3 symbols. If letters may be chosen…
A:
Q: RSA Encryption, Let p = 13 and q = 11 a) Calculate an appropriate public code, and private code for…
A:
Q: Use the cyclical alphabetic encrypting code that shifts each letter 12 positions to code the…
A: Given code = Vincit Omnia Veritas The cyclical alphabetic encrypting code that shifts each letter…
Q: 1. A 10-bit string is sent over a network. The valid set of strings recognized by the receiver must…
A:
Q: Given the characters A,B,C,H,I,T,U,V,1,2,3,and 4, how many seven character passwords can be made? (…
A:
Q: Let's suppose that a password must contain 4 characters, where a character can be any of the digits…
A: Total number of digits = 5 Total number of letters = 26 Total options are 5 numbers + 26 letters =…
Q: A computer password must be 3 letters followed by 5 digits (0 through 9). How many different…
A: Note: Hey, since there are multiple questions posted, we will answer first question. If you want any…
Q: How many 3-letter passwords can be made using the letters A through Z if... a) Repetition of…
A: We have to find the number of 3-letter passwords that can be made using the letters A through Z if…
Q: 1. Frankie has to create a new Virginia Tech password. Suppose Frankie wants his password to be 7-9…
A: The given data is:
Q: A seven-character computer password can be any three letters of the alphabet, followed by two…
A: Given, A seven-character computer password can be any three letters of the alphabet, followed by two…
Q: Each character in a password of length six can be any uppercase letter from A-Z or any symbol from…
A:
Q: How many 4-letter passwords can be formed using the letters in the word "HONESTY" if the 4-letter…
A: Given: n(total) = 7 n(vowels) = 2 (O,E) n(constants) = 5 (H,N,S,T,Y) n(chosen) = 4 Assuming that…
Q: y needs temporary passwords for the trial of a new payroll software. Each password will E igits 3…
A:
Q: Suppose each license plate in a certain state has four letters followed by two digits. The letters…
A: When the repetition is allowed in formation the general formula for calculating the possibility is…
Q: 22. Each symbol in the Braille code is represented by a rectangular arrangement of six dots, each of…
A: Given: We must find the entire number of symbols represented in braille code by raising at least one…
Q: The name of a file in a computer directory consists of two uppercase letters followed by a digit,…
A: we have to name of a file in a computer directory consists of two uppercase letters followed by a…
Q: Assume that product codes are formed from the letters T, Z, Q, V, Y, U, and X, and consist of 6 not…
A: To determine the total number of product codes satisfying different specified conditions
Q: In a public key cryptosystem using the RSA algorithm, a user uses two prime numbers 11 and 17. He…
A:
Q: 2) A school district assigns each of their students a password that consists of three unique letters…
A: Solution
Q: Each symbol in the Braille code is represented by a rectangular arrangement of six dots, each of…
A: We have to find the total symbols represented in braille code with at least one of the six dots must…
Q: If the given encrypted text is " PDWULA" then the decrypted text using Caesar cipher will be,
A: According to historical records, Caesar always used a shift of 3. As long as message recipient knew…
Q: A certain website wants you to build a 6-character password from the letters a through i, the…
A: Given: The letters will be selected from a through i. Thus, there are a total of 9 letters from a…
Q: 2. At a certain company, access codes nust pe 4 composed of the 26 lower case letters of the…
A: Let A=Access codes 4 to 6 symbolsA1=Access codes with 4 symbolsA2=Access codes with 5…
Q: A five character computer password can be formed from three digits, followed by two lower case…
A: There are totally 26 lower case letters of the alphabets(a-z) and 10 digits (0-9). A five character…
Q: If the given plain text is "METHOD " then the encrypted text using Caesar cipher will be, O PHWIRG O…
A:
Q: How many possible passwords can be formed from the letters: ASSISTANT_TITAN ?
A:
Q: Consider a binary code with 5 bits (0, 1 or 2) in each code word. An example of a code word is…
A: Hello! As you have posted 2 different questions, we are answering the first question (4-2). In case…
Q: What is the bit string corresponding to the difference of two sets?
A:
Q: Each employee at a large company is to be issued a computer ID code that consists of three letters…
A: If we have to fill n boxes with no repetition with n objects then then there are…
Q: (a) How many bit strings of length 8 are there? (b) How many bit strings of length 8 or less are…
A:
Q: How many 5-letter code words can be formed using a 27-letter alphabet? (a) if repetition is…
A:
Q: A bank password consists of SIX (6) letters of the Roman characters (small and capital letters)…
A: We need to determine the number of different passwords possible using the letters of Roman…
Q: 2. How many alphabet characters should a password be composed, making sure that there are at least 2…
A: Hello learner, we can answer first question as per the honor policy. Please resubmit other question…
Q: 1. How many 4-letter passwords can be formed using the letters in the word "HONESTY" if the 4-letter…
A: "Since you have asked multiple questions, we will solve the first question for you. If you want any…
Q: A pizza chain wants to send codes for $2 off a large pizza to the subscribers of its e-mail list.…
A: Given that there are 3 positions for letters. Each position can have 23 choices. So the total…
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 3 images

- Suppose that in a long ciphertext message the letter occurred most frequently, followed in frequency by. Using the fact that in the -letter alphabet, described in Example, "blank" occurs most frequently, followed in frequency by, read the portion of the message enciphered using an affine mapping on. Write out the affine mapping and its inverse. Example 2 Translation Cipher Associate the letters of the "alphabet" with the integers. Let and define the mapping by where is the key, the number of positions from the plaintext to the ciphertext. If our alphabet consists of through, in natural order, followed by a blank, then we have "letters" that we associate with the integers as follows:Suppose that in an RSA Public Key Cryptosystem, the public key is. Encrypt the message "pay me later” using two-digit blocks and the -letter alphabet from Example 2. What is the secret key? Example 2 Translation Cipher Associate the letters of the "alphabet" with the integers. Let and define the mapping by where is the key, the number of positions from the plaintext to the ciphertext. If our alphabet consists of through, in natural order, followed by a blank, then we have "letters" that we associate with the integers as follows:a. Excluding the identity cipher, how many different translation ciphers are there using an alphabet of n "letters"? b. Excluding the identity cipher, how many different affine ciphers are there using an alphabet of n "letters," where n is a prime?
- Once the length of the key string of a Vig`enere cipher is known, explain how to determine each of its characters. Assume that the plaintext is long enough so that the frequency of its letters is reasonably close to the frequency of letters in typical English text.Encrypt the message AT TEN HEAD NORTH TO TRENCHES using a tabular transposition cipher with rows of length 4 characters. If necessary, pad the message with A's.Suppose that the most common letter and the second most common letter in a long ciphertext produced by encrypting a plaintext using an affine cipher f (p) = (ap + b) mod 26 are Z and J, respectively. What are the most likely values of a and b?
- The ciphertext letter for T when the congruence is C =( P + 10 ) mod 26 isSuppose that a password for a computer system must have at least 6, but no more than 9 characters, where each character in the password is a lowercase English letter, or an uppercase English letter, or a digit, or one of the five special characters * , < , > ! and # (a) How many different passwords are available for this computer system? (b) How many of these passwords contain at least one occurrence of at least one of the five special characters? (c) Using your answer to part (b), determine how long it takes a hacker to try every possible password, assuming that it takes one microsecond for a hacker to check each possible password. Please solve all 3 sub questionsDetermine whether the given statements illustrate a Combination or Permutation. 1. Determining top three winners in a Math Quiz Bee. 2. Forming triangles from 5 distinct points with no three of which are collinear. 3. Selecting 5 basketball players out of 10 team members for the different positions. 4. Creating a password for your smartphone. 5. Forming a committee of 5 members from 20 people.

