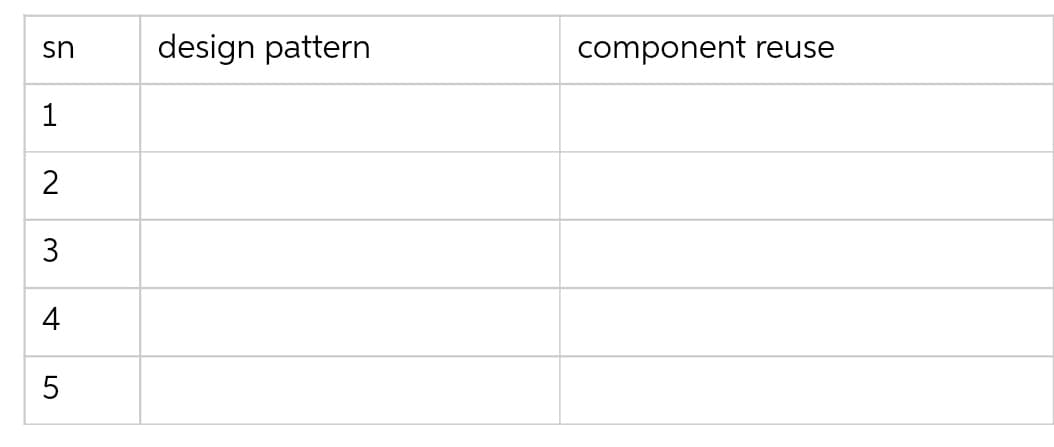
difference between design pattern vs component reuse in OOAD.
Q: Describe the strategy for saving reprogramming time for views
A: Introduction: View controllers are significantly used in the state preservation and restoration o...
Q: When using public key cryptography, what is the minimal number of keys required?
A: Introduction: In the case of public-key encryption, a pair of keys is employed.
Q: Is a self-transition required in every State Diagram? What gives you the impression that this is the...
A: Introduction: The transition between states is defined by a state diagram, which is dependent on the...
Q: ICT and BRI. How is one related to the other? please cite references
A: The use of technology in banking has resulted in a number of synergies with BRI, in addition to prov...
Q: A Triangle will have 3 sides. The class will be able to keep track of the number of Triangle object...
A: Given The answer is given below.
Q: Describe LDS BX, LOC instruction operator.
A: According to the question we need to describe LDS BX, LOC instruction operator.
Q: #include int main(void) { int sum = 0; int number = 0; while (number < 50) { ...
A: In this question, we are asked to modify the program so that it sums up-to 100 except 49, 50 and 51 ...
Q: Describe the evolution of the information system, as well as the significant individuals and events ...
A: Introduction: An information system is a formal, sociotechnical, organisational structure meant to c...
Q: How do you construct a handler for the Load event?
A: Introduction Creating Load event handler: There are two ways to create a Load event handler for a ...
Q: Using MySQL workbench to create a database with six tables. You need to set up primary key and forei...
A: Select this option to generate a statement to drop each object before the statement that creates it....
Q: Explain dynamic RAM briefly.
A: Intro Types of RAM: There are two types of RAM Dynamic RAM (DRAM) and Static RAM (SRAM).
Q: Explain the meaning of the phrase "Verification model satisfies the specification" in the context of...
A: Introduction: The question requires you to define the phrase "Verification model fulfils the specifi...
Q: Given the recorded temperatures for a week: Mon Tue Wed Thu Fri Sat Sun 42 39 52 49 75 83 41 Find th...
A: For this program, the following steps need to be taken: Assigning given temp data into a vector Cal...
Q: Computer Science Investing in stocks is a way to create assets that are supposed to provide financi...
A: Stock.java public class Stock{ //Design a class, Stock, with instance variable cost. private d...
Q: The Turing Machine below starts with the input 0101 with the head on the left most 0. What will be i...
A: According to the question we need to answer:
Q: De 8ign a DFA for the following langag L={ w|we {c, b}" and #a (W) iseven W E %3D
A:
Q: earch Status Page searchstatusform.html This web page contains a form that accepts a status search i...
A: Explanation: In the first step mark the basic HTML tags. In the next step in the H1 tag write the m...
Q: Assume you were hired to design a Public Bus Transport System. The system will keep track of busses,...
A: 2.5 The system will initially have 50 buses.which would travel from bus stop A to bus stop B.Buses w...
Q: 4 The Turing Machine Below starts with the input 1010 with the head on the left most 1. What will be...
A: Given Data : Input: 1010 Position of head: Leftmost 1
Q: How many bytes are in a zettabyte?
A: 1 zettabyte = 1021 bytes
Q: What is the point of having strings variables, in your perspective as a Telecom Engineer, since we a...
A: Introduction: A variable is a container that may contain values. The user may control the output of...
Q: What Is Cloud Computing and How Does It Work?
A: Introduction: Simply described, cloud computing is the distribution of computer services—such as ser...
Q: In a void function, how would you utilise a return statement?
A: Introduction: In a void function, how would you utilise a return statement?
Q: Do routers route packets to MAC addresses?
A: Introduction: Do routers route packets to MAC addresses?
Q: Describe the notion of completeness of R in layman's term
A: Describe the notion of completeness of R in layman's term
Q: Write a program that displays the numbers from 20 to 10 on a single line.
A: In programming, loops are utilized to rehash a block of code until a predetermined condition is me...
Q: Write a Java program to take an array of ints, print the number of 9's in that array.
A: Enter size of array and then enter all the elements of that array. Now enter the element of which yo...
Q: ay Explain Informed (Heuristic) search.
A: According to answering policy we can answer only first question. You can repost remaining questions
Q: # stack the following list vertically with ones matrix and transpose it mat = [1, 5, 3, 7, 8] [[1. 1...
A: - We have to create the list shown with 1's appended and them we have to transpose it. - We are usin...
Q: Why is it vital to consider accessibility when designing your web pages?
A: Introduction: Web pages are documents that deliver material to people on the internet. Accessibility...
Q: Suppose that 50% of a program requires serial execution. With a computer equipped with a quad-core (...
A: A ton of elements can change the response here. Situation 1 :- Assuming that 1 center is saved...
Q: What are your obligations as a Systems Analyst?
A: Introduction: An information technology system analyst's role is to analyse and create solutions to ...
Q: What is DHCP and why do we need it?
A: let us see the answer:- Introduction:- Dynamic Host Configuration Protocol (DHCP) is a network manag...
Q: Write a Java program to take an array of ints, print the number of 9's in that array
A: Take the input from user and while iterating compare each and every element and increment if the ele...
Q: Include the four properties of a computer in today's educational system, based on "Why computers are...
A: Introduction: In today's educational system, there are four qualities of a computer: This question i...
Q: Why would we pick a non-BCNF architecture for a relational database?
A: Intro Why would we pick a non-BCNF architecture for a relational database?
Q: What are the most important factors to consider while creating a physical database?
A: Introduction: In a framework, a reasonable data set plan models all of the data. The end result is a...
Q: PUSH and POP instruction always transfer one byte of data : TRUE or FALSE?
A: answer is
Q: 4 m 12 m Express the hydrostatic force (in N) Enter a number. de of the plate as an integral (let th...
A:
Q: Problem A Write a class FinancialAidApplicant which describes an applicant for financial aid and wil...
A: If-else if-ladder conditional statement in java program: The multiple if conditions are checked in t...
Q: For what kinds of systems are agile development approaches most likely to be an effective strategy t...
A: Agile methods: Agile project management is a sort of procedure. Demands and solutions arise via coll...
Q: 1. Implement and plot a simple linear regression for the above data, where the temperature is “x", a...
A: Linear regression is used to predict analysis between the components. Explanation: In the main func...
Q: After executing next code: movlw 64 movwf Ox00, A movlw 32 [Ox00] = Ox [0x00] = [Ox01] = Ox_ movwf O...
A: below is the answer
Q: When the Categorized button is chosen in the Properties panel, what exactly is it supposed to do?
A: Introduction: The Properties panel show the properties of the item or objects on the canvas that hav...
Q: Use the recursion tree method to guess tight asymptotic bounds for the recurrence T(n)=4T(n/2)+n. Us...
A: Recursion Tree Method may be a picturing of an iteration method which is within the sort of a tree w...
Q: 1. How FLIP-FLOPS performed in HDL?
A: The answer is given in the below step
Q: What is the output: String str = "Hello.."; %3D str += str.substring(0, 5); System.out.printIn(str);...
A: Ans: The output of the following program is : String str = "Hello..."; str += str.substring(0,5); ...
Q: Is it possible to establish error control with the DHCP protocol?
A: DHCP stands for Dynamic Host Configuration Protocol.
Q: The lifespan of a variable declared inside the context of a Click event handler is not known at this...
A: The answer is given below :
Q: The authors claim "Poorly crafted law in this area aimed at protecting imperfect technological solut...
A: The paper "Poorly crafted law in this area aimed at protecting imperfect technological solutions res...
Step by step
Solved in 2 steps

- OpenCV using node.js. Given example how to Exercises:1. Introduction to OpenCV.js2. GUI FeaturesXcode Swift: Upload imagePython: 2048 games Board = list[list[str]]# Checks whether a given board has any# possible move left. If no more moves,# return True. Otherwise return False.def isGameOver(board: Board) -> bool:return False# Returns a tuple (changed, new_board)# where:# changed - a boolean indicating if# the board has changed.# new_board - the board after the user# presses the 'Up' key.def doKeyUp(board: Board) -> tuple[bool, Board]:return False, board# Returns a tuple (changed, new_board)# where:# changed - a boolean indicating if# the board has changed.# new_board - the board after the user# presses the 'Down' key.def doKeyDown(board: Board) -> tuple[bool, Board]:return False, board# Returns a tuple (changed, new_board)# where:# changed - a boolean indicating if# the board has changed.# new_board - the board after the user# presses the 'Left' key.def doKeyLeft(board: Board) -> tuple[bool, Board]:return False, board# Returns a tuple (changed, new_board)# where:# changed - a boolean…
- Cide_Task Programming Language and Advancements▪ C# Programming Language.▪ Visual Studio 2019. Fabricate a strategy called Scramble to get a string and return another string.The technique will be a static.Fabricate a strategy called Unscramble to return unique string.The encryption technique will be an extremely straightforward one: to scramble add 1 to eachcharacter and to unscramble take away 1 to each person.Note: we don't have to make any object of type Encrypter..Task Programming Language and Advancements▪ C# Programming Language.▪ Visual Studio 2019. Fabricate a strategy called Scramble to get a string and return another string.The technique will be a static.Fabricate a strategy called Unscramble to return unique string.The encryption technique will be an extremely straightforward one: to scramble add 1 to eachcharacter and to unscramble take away 1 to each person.Note: we don't have to make any object of type Encrypter..JAVASCRIPT 7. removeButtonListeners a. Selects all buttons nested inside the main element b. Loops through the NodeList of buttons c. Gets the postId from button.dataset.id d. Removes the click event listener from each button (reference removeEventListener) e. Refer to the addButtonListeners function as this should be nearly identical f. Return the button elements which were selected */ function removeButtonListeners(){ }
- getting error please helpHTML <nav> Perceivable Operable Understandable </nav> Question In the navigation section, add a nonbreaking space, then a black circle ● (●), and then another nonbreaking space after the word Perceivable. Do the same for Operable and Understandable. The below format is not working for me: <nav> Perceivable ● Operable ● Understandable ● </nav>Convert the schematic to TinkerCAD. Please don't use arduino. Thank you.

