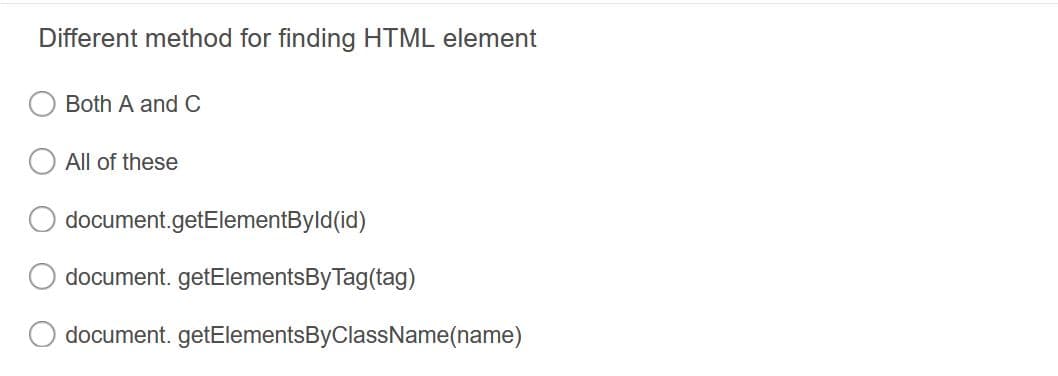
Different method for finding HTML element
Q: ulti-purpose mi
A: A microcontroller (MCU for microcontroller unit) is a little PC on a solitary…
Q: Cloud computing is becoming increasingly common, and many businesses have embraced it. (a) Give two…
A: What is meant by cloud computing :-Cloud computing is a computer model in which servers, networks,…
Q: A binary search tree with the height ‘h’ can have a maximum of 2 (h + 1) - 1 nodes. B. The height…
A:
Q: important components of the operating system? in conclusion,
A: An operating system (OS) is system software that oversees PC equipment, software assets, and offers…
Q: Distinguish between online transaction processing (OLTP) and data warehousing solutions. Also,…
A: Data warehousing systems vs OLTP systems: A data warehouse is a strategy that gathers or collects…
Q: Sketch the block diagram for a memory system bank that will have 4M addresses and a 2byte word size…
A: Given, Using multiple 4M × 2-byte chips (see below) plus a decoder, construct theblock diagram of a…
Q: QI/By Using the following schema, answer the following SQL queries and commands…
A: here we have given the queries for the first three subparts as per the guidelines. you can find…
Q: Assume you're designing an embedded system that uses timer 0 to create a 70% duty cycle and timer 1…
A: We may conduct several operations concurrently in embedded designs by using a real-time operating…
Q: In software engineering, what fundamental principles are being overlooked? explain?
A: Software fundamental ideas Software is a collection of computer instructions that are executed in…
Q: Identify the databases that contain information about you. Can you get a printout of your data…
A: Database applications in daily life: Named entity recognition primarily identifies and categorizes…
Q: What are some of the methods used in the creation of software?
A: Software is created by computer programming, which a software developer completes. A software…
Q: Is it possible for you to explain the metrics used in the software development process? All aspects…
A: software development process, there are many metrics: These are the metrics used to evaluate the…
Q: Explain the notion of Instruction Set Architecture (ISA) in detail.
A: Answer :
Q: Exactly what were the purposes of the Atlas Computer were you wondering?
A: The following code demonstrates the functions: Fixed store An address in the Fixed Store referring…
Q: With the help of suitable examples, describe the ways (at least 6 reasonable ways) in which internet…
A: MIS stands for Management information system.
Q: Is it possible to explain in full the four main benefits of continuous event simulation?
A: Is it possible to explain in full the four main benefits of continuous event simulation below Step
Q: What actions must you do in order to modify the Text attribute of a form?
A: The text attribute specifies the text that is shown or shown on the form.
Q: What are the benefits of utilizing complex word processing software such as Word 2016 over a simple…
A: While Notepad is a straightforward text editor, Word incorporates numerous components (graphics,…
Q: erface lay
A: Solution - In the given question, we have to define the network interface layer.
Q: Computer science Explain the difference between connectionless and connection-oriented services.
A: Introduction: Because of corporate policy, we can only respond to one question at a time, so please…
Q: Assume that there are two IEEE-754 single precision floating point numbers stored in my_data. ;…
A: extract_sign:;Extract the sign bit from the IEEE-754 single precision floating point number ;Input:…
Q: Four arguments for the importance of continuous event simulation?
A: Four arguments for the importance of continuous event simulation?
Q: Explain the garbage collection system and its benefits in Java.
A: Introduction: Garbage collection in Java is a fully automated procedure.Objects that are to be…
Q: Locate two GSS software options that can be utilized to aid group decision-making over the internet.
A: Technology: An application programming interface allowing applications to access security services…
Q: A phone line is connected to a communication adapter through a modem. To what end is this equipment…
A: Definition: A modem, which stands for modulator/demodulator, is a piece of hardware that enables a…
Q: Assume that each user requires 500 kbps and is only active 25% of the time. How many users can we…
A: Answer Statistical multiplexing gain is performed by switching systems in communication network that…
Q: Please enter the expected signal values in the highlighted boxes, based on the circuit's input.…
A:
Q: Since its release, it has been extensively implemented in third and fourth generation database…
A: Management Systems: An effective Business Management System is a combination of management processes…
Q: Computer science What is the Internet layer?
A: Introduction: The Internet Protocol, or IP, is the most important protocol at layer 3 (also known as…
Q: In what ways is it advantageous for a programmer who already has knowledge of a wide variety of…
A: Given: It's better to start with a basic understanding of programming ideas that are independent of…
Q: An explanation of the security measures you should take while outsourcing data to the cloud,…
A: Start: Information Security Measures: What Are They and How Do They Work? Back up your data. The…
Q: What is the difference between data abstraction and data encapsulation? How can we implement this in…
A: The Answer is in Below Steps
Q: 2.13 Consider the following three statements: S, : S2: y = x S3: x = x - y; x = x + y; Assume that x…
A:
Q: Explain smart education and smart city in a few words and provide an example.
A: In the creation of smart cities, smart education is a critical component. A smart city has strengths…
Q: Assume you're a systems analyst working on a comprehensive test plan. Describe the testing…
A: Analyst of systems: Software information is collected by a system analyst. Input from the user on…
Q: Computers and people in the same area are connected through the Local Area Network (LAN). explain?
A: Local Area Network: A local area network (LAN) is a collection of computers and peripheral devices…
Q: a) Refer to this code uploaded. The ListInterface is a repeat of the CollectionInterface.java.(true…
A: Please check below answer for asked questions.
Q: operating systems im
A: About operating systems implement processes
Q: A 2-D array is declared and we want to instantiate based on the following board = new int[5][];…
A: An array is a data structure that contains the elements of the same type. It helps to store…
Q: Suppose you insert elements 41, 38, 31, 12, 11, 50, 55 and 22 (one by one) in an original empty BST…
A: The right answer will be option(a) Tree 1 Explanation:- In the binary search tree, we pick one be…
Q: What is the proper term for a single person who is in charge of organizing a distributed denial of…
A: Intro If a single individual is in charge of organizing a distributed denial-of-service assault,…
Q: (Triangle class) Design a new Triangle class that extends the abstract Geometricobject class. Draw…
A: Solution - Programming language used: Java All necessary comments are included in program code.…
Q: This kind of assault is referred to as a "distributed denial of service attack," and it may be…
A: Distributed Denial of Service (DDoS) A DDoS attack is an attack on a computer system or on a…
Q: Which protocols are supported by SSL? Is a secure connection different from a secure session?
A: Solution: These features solve the following essential problems about web and other TCP/IP…
Q: How do you envision email in your mind? What's the best way to move an email around? Write down what…
A: Email: Email is a kind of electronic communication that is used to transport information or data…
Q: What use does a firewall serve in network design?
A: Firewalls regulate the flow of information between networks: Computers and servers dedicated to this…
Q: What command prints a long list of your current directory's filenames, along with the permissions…
A: The answer is as follows.
Q: it has to grab a txt file and reads user name and password separated with a comma and once inputted…
A: Please find the answer below :
Q: Create a C program that will ask a user for a certain number and display all prime numbers from 1 to…
A: Note:- you have written c program, iostream can’t be used in c program. Since iostream is required…
Q: Why aren't computers and cell phones considered adaptations, like other forms of technology?
A: According to the information given:- We have to define why aren't computers and cell phones…
Don't copy the answer from Bartleby do your own even if you write on papper also no problem
Step by step
Solved in 2 steps with 1 images

- Create the given items then screenshot your code and output. Upload the images to this If you are using a mobile phone, you may use this online HTML editor: https://www.w3schools.com/tryit/ A table of your class scheduleCreate the given items then screenshot your code and output. Upload the images to this If you are using a mobile phone, you may use this online HTML editor: https://www.w3schools.com/tryit/ E-mail registration form A table of your class schedulein HTML and CSS create a nav bar with buttons like in image.
- PROVIDE HTML CODE : Create a html page named as changebackground_color.html. Define a method named as random_color() which is to be called when you click on the body. This method should generate random number, which is used to set the background colorEvery HTML file is a ___________ file.You will need a <script> section in the body of an HTML file used to create a form. True False

