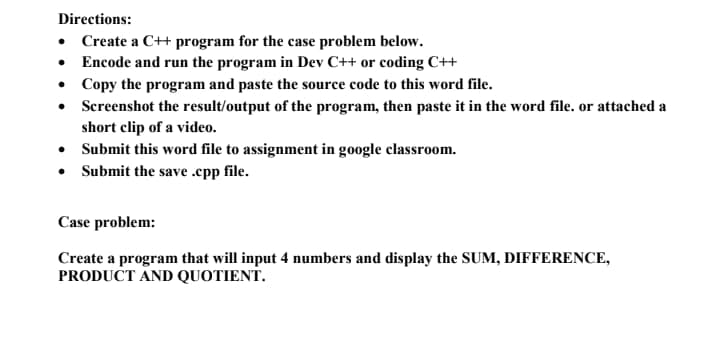
Directions: • Create a C++ program for the case problem below. • Encode and run the program in Dev C++ or coding C++ • Copy the program and paste the source code to this word file. • Screenshot the result/output of the program, then paste it in the word file. or attached a short clip of a video. • Submit this word file to assignment in google classroom. • Submit the save .epp file. Case problem: Create a program that will input 4 numbers and display the SUM, DIFFERENCE, PRODUCT AND QUOTIENT.
Q: java create program to that defines a method "minimum" that receives one parameter which is an…
A: Please upvote. I am providing you the correct answer below. Please please please.
Q: To balance performance across the CPU, memory, buses, and peripheral devices is almost impossible…
A: Start: Look at how each of these things affects the gadgets' ability to stay in the air. In any…
Q: Match the columns: 1. information crisis 2. strategic information 3. operational systems 4.…
A: A data warehouse is a type of data management system that is designed to enable and support business…
Q: i Another word for a software application is a program? True /False ii. When there is more than one…
A: The answer is given in the below step
Q: When it comes to the Internet of Things, what is it and how does it work?
A: Internet of Things (IoT) is an expression that refers to the network of physical items that are…
Q: It is unnecessary to do integration testing if the individual applications have been extensively…
A: In the context of testing, the term "integration testing" refers to a type of testing in which…
Q: ou are given the following game tree. The top level is a maximizing level. Give the values…
A:
Q: Detail the components of the spheres of security paradigm. The document must have a sufficient…
A: Introduction: Information security is primarily concerned with preventing unauthorized access to…
Q: Describe the stages of the Waterfall Systems Development paradigm. How does this compare to Agile…
A: Provided: A concise explanation of the Waterfall Systems Development paradigm's steps.What are the…
Q: A symmetric block cipher's hardware components may be summarized as follows: In what ways does it…
A: Below are the typical hardware components of a symmetric block cypher, as well as its two families…
Q: Write a C++ program to calculate a rectangle's area. The program consists of the following function:…
A: ALGORITHM:- 1. Declare and define all the methods as required. 2. Call them from the main()…
Q: What is the fundamental cause of scope creep in information systems design?
A: Introduction: The project will be completed with the help of Information System Design. A project is…
Q: What does Shell imply and how does it vary from the Kernel in the context of Unix?
A: Shell The shell is the user's interface to the kernel. User-to-kernel interface and command-line…
Q: DESCRIBE HOW A FIREWALL RESEMBLES A DATA STREAM THAT HAS BEEN DIVIDED INTO PACKETS.
A: The packet's path address is provided by the source Routing Feature, which helps the firewall in…
Q: In order to use wireless LANS, you must meet the following five conditions:
A: Requirements for Wireless LAN: A wireless LAN must fulfil the same characteristics as any other LAN,…
Q: A DBA's workload may be affected by the use of various heuristic rules for each of the eight cost…
A: Given: A database management system (DBMS) is software that stores and retrieves user data while…
Q: A cybersecurity expert discovers several users with administrative rights during a security review.…
A: Ans: Least Privilege
Q: When the CMP instruction sequence is executed, what is the final value for AL register ? MOV AL, 25h…
A: CMP Destination,source: It compare the two operands by subtracting source from the destination. Here…
Q: VPN technology for extranets like online hardware stores.
A: VPN Technology: An extranet is a private intranet that is built on the Internet and adheres to…
Q: Determine the difference between virtual memory and virtual machines. What are the distinctions…
A: Identify the differences between virtual memory and virtual computers. Virtual memory: Virtual…
Q: oking to start a new online business. As part of registering your new venture and applying for small…
A: In its most straightforward terms, the risk appraisal poses the inquiry: in the event that we don't…
Q: In order to access 1024K words of memory, how many address bits are required?
A: A database management system - (DBMS) is software that stores and retrieves user data while taking…
Q: Specify the architecture of a computed unified device.
A: Introduction: Compute Unified Device Architecture (CUDA) is an acronym for Compute Unified Device…
Q: Iraqi airways has website that provides customers with: searching flights, book a flight and…
A: 1. The best SDLC method for this project is the Predictive SDLC method. As its name suggests, the…
Q: What level of confidence do you have in the safety of your data?
A: Information of safe Data: To guarantee that your information is safe and secure for the rest of…
Q: stem manager customer Register Account view available date Check in Check out
A: A communication diagram is one type of object diagram that shows the objects along with the messages…
Q: Write a row-level trigger that executes before updating a project's location in the project table.…
A: The question is to write the SQL query for the given problem.
Q: s(1 Consider a serial bus (1 bit wide) that runs at 2GHZ, using alternate cycles for control signals…
A: The Answer is in step-2.
Q: (c) State FIVE (5) elements of an activity bar chart.
A: Please upvote. I am providing you the correct answer below. Please please please.
Q: Draw a flowchart and write a C Program that will input a radius and will compute for the area,…
A: let us see the answer:- Code:- #include<stdio.h> #define PI 3.14 int main(){ float radius,…
Q: What is a firewall's principal purpose? What are the general guidelines for using packet filtering?
A: The answer is as follows.
Q: What are the seven levels of the OSI?
A: Open Systems Interconnection (OSI): Identify the seven levels of the OSI model. The seven layers…
Q: Assume a computer has two network interface cards, NIC1, a Wifi USB, and NIC2, an on-board Ethernet.…
A: The network interface card (NIC) enables computers to interact across a computer network via wired…
Q: What difficulties does a multithreaded architecture provide for an operating system?
A: Given the information provided, we need to understand more about the challenges involved in…
Q: What distinguishes software engineering from other types of engineering and why is it considered an…
A: Aspects of the software engineering field: As with software architecture, software engineering is…
Q: When feasible, operating systems stack blocks of a file on top of one another in order to save space…
A: Using hard discs or magnetic discs, the operating system strives to guarantee that, when a file is…
Q: Two tiers of addresses are required before a packet may be sent to a host or router. Name each one.
A: Explanation: Packet switching is a way of organising data that is transferred across a digital…
Q: Explain or draw a diagram on how to implement a database using PHP as the interface to a website.
A: Best Way is by using 3 tier Architecture: 1. Client Layer 2. Communication(Middle) Layer 3. Database…
Q: Is there a distinction between the two modes of an operating system? What is the major function of…
A: Start: An operating a system (OS) is a piece of the software that connects a computer user to the…
Q: When comparing 7CH and 7CH, what is the difference between 7CH and 7CH? Where exactly in the…
A: Given: What is the difference between 7CH bit address and 7CH byte address? What memory location…
Q: If you're going to use distributed data processing, what are the advantages and disadvantages?
A: Introduction: What are the benefits and drawbacks of distributed data processing that should be…
Q: There are a lot of principles in software engineering, but are there any missing? explain?
A: Any collection of executable instructions is intended to do some kind of computation. It contains…
Q: D Create a class Sum with the following fields, constructors and methods: Fields: create two…
A: As per the requirement program is developed. Note: In the question programming language is not…
Q: Attempts are made by operating systems to store chunks of a file sequentially on disk. What's the…
A: Operating systems: Operating systems make every attempt to store successive file blocks on…
Q: Define the terms in brief. 1.Data pre processing 2.Data visualization 3. Machine learning
A: Data preprocessing: It is a data mining approach that is utilised to convert the raw data in a…
Q: This is the Waterfall Systems Development paradigm: What makes this different from Agile?
A: Given: Popular in software engineering and product development, the waterfall model is a sequential,…
Q: Modern systems employ what two types of data processing methods?
A: Data Processing Methods: Data Processing by Hand Data is manually handled in this data processing…
Q: List the Transport Layer's two most well-known data transport protocols. Briefly describe each…
A: Two well-known data transfer protocols are: Transmission Control Protocol (TCP) User Datagram…
Q: Q5: For the Binary search tree given below. 30 15 60 7 22 45 75 17 27 In-order Travetrsal Pre-Order…
A: In Inorder traversal, the root is traversed in between the left and right subtrees and the same rule…
Q: What is the process through which a virtual network interface card (VNIC) obtains a MAC address?
A:
Step by step
Solved in 2 steps with 2 images

- Both the int 1 (for write()) and the FILE *stdout (for fprintf()) refer to the terminal output. How are they different? A. They are actually different output streams, i.e., one is "standard output" and the other is "standard error" B. The FILE * is a C abstraction in stdio.h around the OS's int representation C. The int 1 is a C abstraction in stdio.h around the OS's FILE * representation D. They are the same thing; stdout is defined as (FILE *)1Directions: Typing make at the command line should create executable named bitflip. Only bitflip.c and Makefile are included in the input unless permission is given for any other files. Program should have consistent indentation. Code should be readable with good variable and function names. No use of "break or continue statements" except in a switch. Program must exit with a return code of 0 on success and an error code in other cases. The program used getopt to parse the command line. Whenever an error occurs on the command line the user is given the usage statement and an appropriate error message if needed. If the -o option is used the output will go to a file named as specified without changing the filename at all otherwise it will go to stdout. -e option works as specified using bitwise operations. -f option works as specified using bitwise operations. -a option works as specified using bitwise operations. -s option works as specified using bitwise operations. Program outputs…Directions: Typing make at the command line should create executable named bitflip. Only bitflip.c and Makefile are included in the input unless permission is given for any other files. Program should have consistent indentation. Code should be readable with good variable and function names. No use of "break or continue statements" except in a switch. Program must exit with a return code of 0 on success and an error code in other cases. The program used getopt to parse the command line. Whenever an error occurs on the command line the user is given the usage statement and an appropriate error message if needed. If the -o option is used the output will go to a file named as specified without changing the filename at all otherwise it will go to stdout. -e option works as specified using bitwise operations. -f option works as specified using bitwise operations. -a option works as specified using bitwise operations. -s option works as specified using bitwise operations. Program outputs…
- Please help me with this code. The code needs to consists of one header file and two c files . Must use the command line to run the program. Below is the input.txt file that needs to be used. Please provide output and the source code for each file in the program. A1, A2 20294 Lorenzana Dr Woodland Hills, CA 91364 B1, B2 19831 Henshaw St Culver City, CA 94023 C1, C2 5142 Dumont Pl Azusa, CA 91112 D1, D2 20636 De Forest St Woodland Hills, CA 91364 A1, A2 20294 Lorenzana Dr Woodland Hills, CA 91364 E1, E2 4851 Poe Ave Woodland Hills, CA 91364 F1, F2 20225 Lorenzana Dr Los Angeles, CA 91111 G1, G2 20253 Lorenzana Dr Los Angeles, CA 90005 H1, H2 5241 Del Moreno Dr Los Angeles, CA 91110 I1, I2 5332 Felice Pl Stevenson Ranch, CA 94135 J1, J2 5135 Quakertown Ave Thousand Oaks, CA 91362 K1, K2 720 Eucalyptus Ave 105 Inglewood, CA 89030 L1, L2 5021 Dumont Pl Woodland Hills, CA 91364 M1, M2 4819 Quedo Pl Westlake Village, CA 91362 I1, I2 5332 Felice Pl Stevenson Ranch, CA 94135 I1, I2 5332…All I need is the main.cpp file Programming Specifications: Task: Two files have been provided (wordcounter.h and wordcount.cpp). You must open a text file, read in each word until end of file, add each word to the WordCount library and print the report. Your program must request a filename of a text file that contains words to count. You must check to see if it is a valid file and issue an error message if not and request a new file name until a valid one is entered. You must have at least one function that either passes in a parameter and at least one function that returns a value. You can have a single routine that does both. You must declare the class object properly, use AddWord() to add the word to the catalog and use PrintSummary() to produce the output. Design Considerations: The file will contain only words (no punctuation or special characters) less than or equal to 13 letters. There will be no limit to the number of words. You must open the file and read each…Write a C program that, given a text file, constructs Huffman code based on the character frequencies of the file and then encodes the file accordingly. The executable must accept the following command line options:• -i filename for the input file • -o filename for the output file Use the fread function, use FILE, size, etc. Please use the following to write the code: #include <stdio.h> #include <stdlib.h> #include <string.h> #include <getopt.h>
- C++ Calculate the sum of one column from a txt file, Please do read the question carefully Below is some information in a txt file 249,V,R,5287,250,M,A,2941,251,M,R,7552,252,M,C,6723, How do I use c++ to read this text file and get the sum of the 4th column(last column) with follow #include #include <iostream>#include <iomanip>#include <string>#include <vector>#include <fstream>Write a small program that copies everything in a tet file to another file. The text file is calledin.txt and the output file is called out.txt. Two files should be exactly the same after copying(the first file shouldn’t be changed, and the second file should be the same as the first one).Your program should define a function called copyFile to copy the input file to the output filewith two arguments: a file pointer to the input file and a file pointer to the output file. You shouldnot and do not need to use an array during copying.Write a C program named toupper.c that reads the contents of a file, and writes to another file after changing all lowercase letters in the input file to uppercase. The name of the input file and the output file are to be passed as command line arguments. Assume there are only ASCII characters in the input file. The length of the input file is not known beforehand. So make sure your program keeps reading bytes until EOF is reached. Use the library function toupper to concert letters into uppercase. Example: The program is run from the command line as follows; C:\>toupper.exe infile.txt outfile.txt Suppose the contents of the input file infile.txt is: AbcdefG The contents of the output file outfile.txt should be: ABCDEFG
- Write a C program which will write user’s name and age to a sequential access filecalled ‘sequential_file.txt’. Each time the program is executed, the data already in thefile must not be overwritten. Ensure that each time text is written to the file, it is place on a new line inaddition the program should be able to read, display and count the data stored in the sequential access file called 'sequential_file.txt'. read, display and count the data stored in a sequential access file called ‘sequential_file.txt’.Question R .Python: I am trying to write a function where the program opens a directory and then lists all the files ending in .csv. Why doesn't my program work? Is there a better way to write this? import oslocation = r'C:\Users\Janelle\OneDrive\Desktop\Python_files'counter = 0 #keep a count of all files foundcsvfiles = [] #list to store all csv files found at locationotherfiles = [] #list to keep any other file that do not match the criteria for file in os.listdir(location):try:if file.endswith(".csv"):print("csv file found:\t", file)csvfiles.append(file)counter = counter+1else:otherfiles.append(file)counter = counter+1except Exception as e:raise eprint("No files found here!") print("Total files found:\t", counter)print(csvfiles) Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this lineWrite a C++ program that accepts lines of text from the keyboardand writes each line to a file named text.dat until an empty line is entered. An empty lineis a line with no text that’s created by pressing the Enter (or Return) key.b. Modify Program 9.6 to read and display the data stored in the text.dat file created inExercise 3a.

