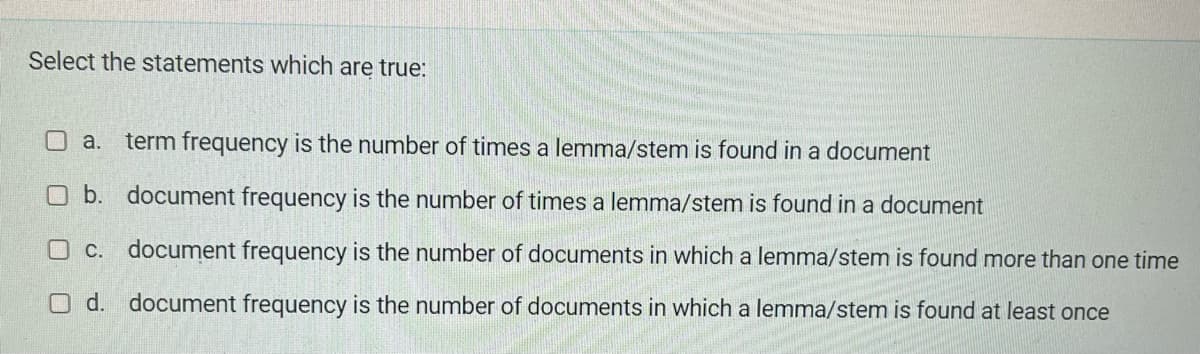
document frequency
Q: What will occur if the way individuals cooperate is altered by the introduction of cloud computing?
A: For businesses, migrating to the cloud is no longer an option but rather a must. Cloud collaboration…
Q: cloud computing offered by VMware
A: Cloud computing, in its most basic form, entails storing and accessing data and programs on remote…
Q: Improve your knowledge of cloud computing, social media blogging, and other important topics.
A: Given: Gain a deeper understanding of cloud computing, social media blogging, and other areas that…
Q: Consider the differences between a firewall and a packetized data flow
A: Given To know about the differences between a firewall and a packetized data flow.
Q: PROBLEM: Create a program that will ask to fill in two square matrices and perform matrix…
A: The program is written in C++. Check the program screenshot for the correct indentation. Please…
Q: Where exactly does the concept of user-centered design fit into the process of software development…
A: Start: Visual and diagrammatic software life cycle models (sometimes referred to as process models).…
Q: Use String methods to divide the given email into separate parts. The email will always be in this…
A: Step-1: StartStep-2: Declare variable str and take input from userStep-3: Declare a string array arr…
Q: Is it possible to tell the difference between different software programs based on the type of their…
A: Answer:
Q: What are the benefits and drawbacks of using cloud computing for your existing online company, and…
A: Cloud computing benefits the company by: The first benefit of cloud computing is that businesses may…
Q: What is artificial intelligence's ultimate goal? Give a brief overview of the main categories and…
A: The Answer is in step2
Q: In order for society, companies, and industries to gain the advantages of information systems, they…
A: Given: Any organisation can succeed with skilled data frameworks and predictable hierarchical and…
Q: What is the best method for storing user data backups? Your solution should be cost-effective,…
A: The best method for user Data backup is given below:
Q: Is it necessary to emphasize the need of data backup in organizations while emphasizing the…
A: Is it necessary to emphasize the need of data backup in organizations while emphasizing the…
Q: When it comes to technology, architecture and organization based on computers are two quite distinct…
A: Start: Architectural designThe process of putting together a computer system is known as…
Q: Consider a function defined as follows for non-negative integers n and m: A(0, m) = m+1 A(n, 0) =…
A:
Q: Write VB program to print the following figure: Form1 # # # # # # # # # # # # # #
A: The code implementation is given in the below steps. The Algorithm: The number of rows to be…
Q: It's widely accepted that the internet is at the pinnacle of information and communication…
A: Because the Internet is the great enabler of our day, it gives a great lens through which to explore…
Q: What are the main differences between the ARM architecture and the core i3 architecture, and how do…
A: Intro The ARM architecture is designed to be as functional as possible while using the least amount…
Q: In order for a network to function appropriately and efficiently, what three characteristics must it…
A: When two or more computers are connected together, resources (such as printers and CDs) may be…
Q: In order to prevent a computer network system from being infected with a virus, what kind of…
A: Answer: 1. Introduce antivirus software To try not to get an infection on your gadgets from the…
Q: If malicious traffic is diverted from one VLAN to another, there is a possibility that a network…
A: Start: VLANs are logical groups of devices on one or more LANS configured to communicate as if on…
Q: 1. Explain why certain fields are eliminated and this improves IPv6, such as check sum,…
A: One of the ideas around IPv6 was to speed up packet forwarding. To that end, several decisions were…
Q: For workers that work remotely or wirelessly, what type of network configuration would you…
A: Introduction: Computing devices that are linked together and can exchange data and resources. A…
Q: . Explain the use of the EH field
A: Answer the above question are as follows:
Q: Is it essential for the operating system to exercise a higher level of caution whenever it accesses…
A: Start: Instead of using traditional disc drives, in-memory databases store data in the computer's…
Q: Discuss the positive and negative impacts of ict on society.
A: The solution to the given question is: Information communications technology has the power to…
Q: In a setting that is suitable for forensic investigation, what steps must be taken in order to…
A: Given: SSD data must be retrieved in a forensically sound setting. The government mandates…
Q: What are the challenges of implementing mobile technology? Compared to web-based solutions, how much…
A: The answer of this question is as follows:
Q: Describe the procedure for routing data over a wide area network.
A: Intro Here, we need to figure out how to route over an extensive area network. To set up a…
Q: Why is it beneficial for your online company to make advantage of cloud computing? What are the…
A: Cloud computing for e-commerce: Businesses spend a lot on software to improve operations. Cloud…
Q: During the course of this presentation, you are going to go rather thoroughly into the topic of…
A: software development: Architectural design is a very important aspect of software development. In…
Q: What part does a trusted platform module (TPM), also known as a security key, play in the process of…
A: Given: The technique of encrypting all of the data on a disc is known as whole disc encryption. The…
Q: Is it the database administrator's or the database user's obligation to do backups? a person who is…
A: Database Administrators: Database administrators may establish backups, but it is the DBA's job to…
Q: Write a C++ program to display number of objects created using static member. Properly explain…
A: Code: #include <iostream>using namespace std; // Create class Student with attribute idclass…
Q: Is it feasible to evaluate software quality when the client continually altering what the product is…
A: Check the following statement: Is it feasible to evaluate software quality when the client…
Q: What are some of the reasons why the internet is regarded as one of the best examples of information…
A: Introduction: ICT is the abbreviation for information and communication technology. Demonstrates…
Q: The use of a surrogate key for a connection's primary key has been considered in three cases.
A: Intro In data analysis, a surrogate key is a key with no contextual relevance used to identify the…
Q: In the realm of telecommunications, the issue of precisely what it means to have 4G or 5G networks…
A: Intro Networks using either 4G or 5G: In a nutshell, the transition from the 4G network to the 5G…
Q: mechanical), class 3 should insert engineering name. Friend function should diagnose error a display…
A: // I hope my solution is helpful #include <bits/stdc++.h> using namespace std; class…
Q: When it comes to the creation of software, what are the benefits of making use of Design Patterns,…
A: The above question is solved in step 2 :-
Q: A virtual private network (VPN) is the obvious option to go with when it comes to protecting the…
A: Introduction: VPN is highly significant in terms of network security. Here are a few reasons why VPN…
Q: ibute to the spread of a virus across the com
A: Introduction: Below the factors could contribute to the propagation of a virus over the computer…
Q: What role do wireless networks play in the development of underdeveloped countries? Local area…
A: Introduction: The network's penetration in a nation is determined by elements such as the country's…
Q: Is it possible to encrypt the connection as well as the data from beginning to end? What benefit…
A: Introduction: Link encryption is a type of communication authentication in which all data at both…
Q: List and describe at least ten local or national computer science and information technology…
A: 10 CS and IT Organizations: The ACM ACM is a US-based worldwide processing learning society. It's…
Q: An in-depth conversation on wireless networking will take place, during which wireless protocols,…
A: Wireless network: Wireless local network is cheap to setup and ideal for mobile workgroups and…
Q: Explain how a firewall and a packetized data stream are comparable.
A: A correct answer is an option. Essential Considerations The firewall may reassemble a data stream…
Q: Why is the internet regarded as one of the best examples of modern information and communications…
A: Introduction: ICT stands for infocomm technology.
Q: What exactly is the difference between cloud storage and backup when it comes to the realm of online…
A: Cloud capacity is characterized by IBM as a: "[service] that permits you to save information and…
Q: Many businesses store all of their critical data on cloud storage providers. What makes you believe…
A: Benefits Cloud storage saves money. Sсаlе economies. Cloud vendors acquire storage and pass the…
Step by step
Solved in 2 steps

- a. In cell H4, create a formula using the IF function that tests whether the value in the Bundled column ([@[Bundled?]]) is "Yes". b. If the value in the Bundled column is Yes, subtract 10 from the amount in the Per Month column ([@[Per Month]]). c. Otherwise, the payment is the same as the value in the Per Month column. d. If necessary, fill the formula to the range H5:H48.Type the correct answer in the box. Use numerals instead of words. If necessary, use / for the fraction bar. var num2 = 32;var num1 = 12;var rem=num2 % num1;while(rem > 0) { num2 = num1; num1 = rem; rem = num2 % num1; }document.write(num1); The output of the document.write statement at the end of this block isC++ Question!!Fill in all blanks
- Indicate ALL syntax errors of each SML statement and try to correct. (1) [2-3.0, 3.0=2]; (2) if true then if false then false else true;A semaphore is a non-negative integer variable that apart from initialization can only be acted upon by two procedures. State the criticism of the semaphores usage.What is true about stored procedures and functions?(a) Procedures return value using return statement while functions don’t.(b) Procedures do not return value using return statement while functions do.(c) Both procedures and functions return value using return statement.(d) Neither procedures nor functions return value using return statement.
- Design the ER segment for each statements given below. A movie is directed by at least one director. A director may not direct a movie, but if he does, he could direct multiple movies. Each employee except for the Chairman (highest position) is supervised by exactly one employee. An employee who are considered supervisors supervises one or more employees. A project may or may not be accepted in an international conference, but can only be accepted in one. An international conference must accept one or more projects. A hospital has a database system for patients’ medical records. A patient is placed to only one ward if she is an inpatient and not an outpatient. A ward may have zero or more patients.q7- Options for both fill in the blanks are- primary key,foreign key(c) Compute the percent decline or increase in the mobile website visitors, write a formula in cell E26 and copy to cell E27. (d) In cell F26, Use the IF Function to create a formula to print "Yes" if there is cannibalization; else, the formula should print "No". Copy the formula to cell F27.Hint: If the percent increase is negative then there is cannibalization, else there is no cannibalization. Screenshot is attached below thx!!
- QUESTION ATTACHED . MATCH INPUT AND OUTPUT! AND FOLLOW THE QUESTION AS IT IS.Please follow the question and the sample. And please do not use any built in function.C++ code please. Correct and detail answer will upvoted else downvote. There are one feline, k mice, and one opening on an arrange line. The feline is situated at the point 0, the opening is situated at the point n. All mice are situated between the feline and the opening: the I-th mouse is situated at the point xi (0<xi<n). At each point, numerous mice can be found. In one second, the accompanying occurs. To begin with, precisely one mouse moves to one side by 1. On the off chance that the mouse arrives at the opening, it stows away (for example the mouse will no more move to any point and won't be eaten by the feline). Then, at that point (after that the mouse has completed its turn) the feline moves to one side by 1. In the event that at the new feline's position, a few mice are found, the feline eats them (they can not move after that). The activities are performed until any mouse hasn't been covered up or isn't eaten. At the end of the day, the primary move is made…

