Does AG(req -> AF busy) hold in all initial states for the following model (Fig.1)? Why or why not? Clearly state the reason that backs up your conclusion.
Q: The ideas of virtual memory and virtual machines may be contrasted with one another and are in…
A: Comparison according to definitions: Consequently, every software may see the whole address space of…
Q: When redistributing a route into EIGRP, what is the necessary parameter? Administrative distance is…
A: EIGRP EIGRP stands for Enhanced Interior Gateway Routing Protocol. It is a network layer protocol…
Q: What is the strength of a network structure?
A: Introduction: What is the strength of a network structure?
Q: Write a c program to swap the value of two variables.
A: Introduction: Here we are required to create a program in C that will swap the values of two…
Q: Q. If a host on a network has the address 172.16.45.14/30, what is the subnetwork this host belongs…
A: The Answer is in step2
Q: Read and analyze the problem below carefully. Create a program using the if and if-else statements.…
A: I give the code in Python along with output and code screenshot
Q: Explain the current phenomenon of the convergence of digital gadgets and the connection it has with…
A: Introduction: The following is the current digital device convergence trend: The presentation of…
Q: How does one go about converting a data model into a database design? What steps are involved in…
A: INITIATION: Using Access, it is possible to create Internet-accessible database applications.…
Q: The concept of dynamic memory allocation is explained in simple terms.
A: Resources are always in short supply. We have worked to improve resource utilization; this is the…
Q: euse patterns. Why not
A: Patterns of frequency reuse: Frequency reuse alludes to allocating and reusing channels across an…
Q: Compare and contrast five distinct techniques to memory management.
A: The advantages and disadvantages of five distinct memory management strategies are listed below.
Q: Describe a few different methods that may be used to hijack a session. How would one defend…
A: The solution to the given question is: INTRODUCTION Session hijacking is a form of attack in which…
Q: Mobile devices and impromptu collaboration are topics that will be briefly covered in this…
A: Given: The use of mobile devices and collaborative tools to enable geographically scattered…
Q: Haskell: Based on the data declaration, data Nat = Zero | Succ Nat. Define a function exp :: Nat ->…
A: exponential function which takes natural number as input and gives natural number as output is given…
Q: Spindle disk photodetector lens sledge laser sledge motor photodetector photodetector lens IMAGINE…
A: CD - ROM The abbreviation for "compact disc read-only memory" is "CD-ROM." A reflective aluminum…
Q: The Study of Computers How can I determine the point at which rapid sort transitions into insertion…
A: A Hybrid Procedure mixes two or more algorithms that solve the same issue, picking one (depending on…
Q: Paging as a memory management strategy has many benefits and cons.
A: Given:Explain in further depth three benefits and three drawbacks associated with the use of paging…
Q: What's an associative cache?
A: The main memory is seen as two fields in an associative cache. These fields are Tag and Word. The…
Q: When you talk about the partitioning of operating systems, what exactly do you mean by that? Please…
A: Memory partitioning: Memory partitioning divides a computer's memory for resident programmes.…
Q: What distinguishes a physically structured data flow diagram from its logical counterpart, the data…
A: Given: A logical DFD is concerned with a company's activities, while a physical DFD is concerned…
Q: Which is safer for frequent reuse patterns: a low reuse factor or a high reuse factor? Provide an…
A: When channels are allocated and reused over a certain coverage area, the term Frequency Reuse is…
Q: What kind of problems does a simultaneous multithreading architecture need an operating system to…
A: Simultaneous multithreading is a processor design that combines hardware multithreading with…
Q: Why is multitasking, also known as multithreading, more common than having many processes running…
A: Multithreading: It is possible for a single process to include many threads, each of which may…
Q: The contact form page must contain a form that contains the following fields: • Name • Email • The…
A: 1-> In this problem I have used javascript DOM manipulation concept 2-> Uploaded all the…
Q: Detailed information on the Domain Name System (DNS), including iterated and non-iterated searches,…
A: Introduction: The goal of DNS is to translate a domain name into an IP address. This is done by…
Q: Multithreading is more prevalent than a multitude of unconnected background processes. Explain.
A: Threads originate inside a process.
Q: Please provide five examples of how fuzzy logic is used in engineering (especially in computer…
A: Calculations in Boolean logic yield direct outputs of 1 or 0. However, fuzzy logic is utilised when…
Q: What were some notable benefits that DDR offered over the more traditional SDRAM?
A: SDRAM (synchronous DRAM) is a general term for dynamic random access memory (DRAM) synchronized with…
Q: What is dynamic memory allocation and how is it implemented? When it comes to the user, what are the…
A: Dynamic Memory Allocation: When a running application requests a block of main memory from the OS,…
Q: Write an algorithm to identify keyframes from a video with the file names being the timestamp as…
A: YOLOv3 YOLOv3 stands for You Only Look Once-Version 3. It is use to detect real-time object in…
Q: Shared structures might instead be stored locally inside one process and accessed through…
A: To be determined: A possible alternative architecture may involve storing shared structures in the…
Q: What are the three kinds of embedded processors that may be found? They're different.
A: Embedded systems: Microprocessor-based computer hardware systems with software designed to execute a…
Q: The purpose and nature of telecommunications network protocols are described
A: A network protocol for telecommunications is a collection of rules for structuring and processing…
Q: How, as a database designer, are you able to alter the performance of the database in different…
A: Foundation: The database designer is responsible for defining all of the specific database…
Q: Scenario: You are maintaining a List of millions of sorted video game scores. Someone just finished…
A: An algorithm is consider as best sorting algorithm when it perform fastest in best and worst case.…
Q: 5. Round Robin(RR) Scheduling (Quantum = 3, Context Switch = 1) according to the below table: Note:…
A: Here is the solution
Q: What's the difference between embedded system software and system software in general? What are some…
A: System Software: System software is software that is used to operate and control a computer system,…
Q: Q12/ The odd parts of the signal x (t) in MATLAB is
A: As per the question statement, We need to find the odd part of the signal x(t).
Q: It is not always the case, despite the fact that the majority of computer systems employ fewer…
A: Repetitive frequency patterns: Frequency reuse refers to the allocation and reuse of channels across…
Q: Explain in detail three benefits and drawbacks of paging as a memory management approach.
A: Introduction: Explain three pros and downsides of using paging as a memory aid in detail.
Q: In a few words, explain dynamic memory allocation.
A: Introduction: The technique of controlling system memory while it is operating is known as "dynamic…
Q: How do I implement a file with sets of numbers, such as 0 4 2 6 0 9 1 5 to an adjacency matrix
A: An adjacency matrix is a V x V binary matrix A (a binary matrix is a matrix in which the…
Q: In a nutshell, this is how dynamic memory allocation is explained.
A: Introduction: Dynamic memory allocation is the process of allocating memory space during execution…
Q: Algorithmic cost model What disadvantages does it have compared to other methods?
A: The constructive cost model is the algorithmic software cost model that is employed. What is the…
Q: Q1\Write a program that sums the numbers between 1 and 9 and finds the sum total
A: As no programming language is mentioned, I am using C++ There are two ways of doing this: Run loop…
Q: A comprehensive and in-depth explanation of how the Domain Name System (DNS) works, including topics…
A: Domain Name System (DNS): The principal function of the DNS, which is also known as the domain name…
Q: What is the maximum number of IP addresses that can be assigned to hosts on a local subnet that uses…
A: Given that a subnet mask is 255.255.255.224 and we have to calculate maximum number of IPs that can…
Q: What are some ways that context pointers may be used to provide product recommendations? Provide an…
A: How may context pointers be used for a product recommendation? Explain with a specific example of an…
Q: 1. If a- rand(3, 5), then a(2.3) is
A: There are multiple unrelated questions are there. So as per policy, I will be answering only first…
Q: What are scanf(restrictions )'s and how may they be circumvented?
A: Despite the fact that it is also about overflow, the real problem with scanf is something else…
Does AG(req -> AF busy) hold in all initial states for the following model
(Fig.1)? Why or why not? Clearly state the reason that backs up your conclusion.
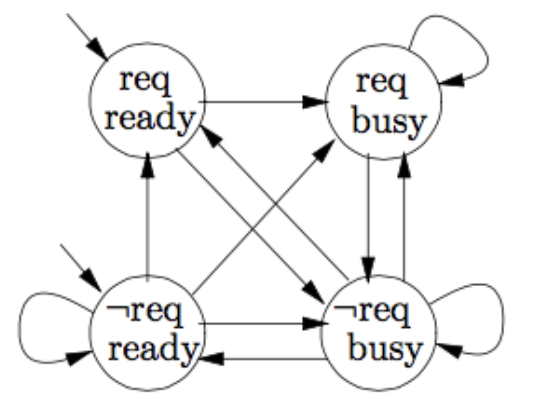
Step by step
Solved in 2 steps with 1 images

- Question#05 b part Please provide detailed solution with explanation and justification asap to get a upvote for B partPrincipal of information systems (Access) Q3.Insert atlest 3 rows with valid data.INSTRUCTIONS Using spreadsheet software enter the following table below that shows thenumber of tourists visiting the following countries over a five-year period. UseTimes New Roman and Font size 12. Name the worksheet Table. COUNTRIEsS 2014 2015 2016 2017 2018‘000 ‘000 ‘000 ‘000 ‘000Grenada 350 465 375 250 485Antigua andBarbuda 153 160 155 149 256Barbados 573 625 725 680 740St. Kitts 347 515 538 178 384St. Lucia 600 436 368 535 858Trinidad andTobago 379 563 475 415 563Jamaica 416 200 500 300 475Bahamas 300 450 550 460 470Aruba 208 367 415 500 684Dominica 135 317 279 350 465 Insert a column to the right of the table with the heading “Total Visitors”. Inthat same column compute the total number of tourists that visited eachcountry over the years. Insert a row heading Maximum to show the maximum number of visitors foreach given year. Sort the data in ascending order based on the Countries. Insert a row heading Minimum to show the minimum number of visitors foreach given year. …
- A Web service is a software system designed to support interoperable machine-to-machine interaction over a network. It has an interface described in a machine-processable format. Select a current healthcare database software and describe its application in healthcare databases. Include references.university er digram for database. 15 entities. yes at least 10.How are horizontal and vertical divisions different?

