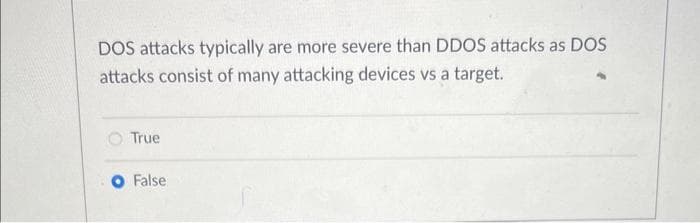
DOS attacks typically are more severe than DDOS attacks as DOS attacks consist of many attacking devices vs a target. True False
Q: Create an SVM to calculate the XOR function. Use the values +1 / -1 for inputs and outputs. Map the…
A: The XOR function is a logical operation that returns true if the inputs are different, and false if…
Q: How does virtualization affect time allocation for hosts and visitors?
A: In this question, it is asked how the concept of visualization affects the allocation of time for…
Q: Talk about the specific ways in which GM used IT to promote global coordination. To what extent did…
A: The information system is essentially the combined collection of several components that are used to…
Q: Question 2 How do you set a breakpoint in Eclipse? Saved double click on the margin on the left side…
A: There are multiple ways to set a breakpoint in Eclipse: Double click on the margins on the left…
Q: Is authentication helpful in any way towards our goals? We'll examine and contrast the different…
A: Authentication verifies a user’s identity to ensure they have permission to use a particular network…
Q: Which SQL statement returns only records that have matching values in both tables A and B?
A: Write an SQL statement that returns only records that have matching values in both tables A and B.
Q: It's important to know the four primary categories of information.
A: A firm may benefit from using an information system in its process of decision-making. Better…
Q: Can you explain what exactly an object program is?
A: Introduction: Object program: Compiler/assembler output Machine executable form/code Obtained after…
Q: What are your opinions on the potential benefits of interruptions for increasing productivity and…
A: Interruptions can be beneficial for increasing productivity by providing a break from monotonous…
Q: e shift to cloud computing have? Do you know how to work well with others?
A: Given : What kind of commercial effects does the shift to cloud computing have?
Q: Which program transfers instructions from main memory to the central processing unit (CPU) so that…
A: The code that may be executed is being loaded by the programme. The process of loading programmes…
Q: Explore the online presences of the aforementioned major giants, plus Microsoft, Oracle, and Cisco,…
A: With the advent of software, security has become the primary worry for the increasing number of…
Q: Locating and fixing healthcare network issues
A: I've discussed troubleshooting a healthcare network here. Answer: In the foreseeable future,…
Q: What are the three goals that a network must meet in order to operate effectively? Try to come up…
A: A computer network, sometimes called a data network, is a series of linked hubs that may exchange…
Q: Better performance may be achieved using either a synchronous or asynchronous bus between the…
A: One can favour the usage of a synchronous bus between the central processing unit and memory over…
Q: Write a Python program that reads a text file called student.txt. The input text file contains…
A: Answer:
Q: There are six main parts to every successful computer communication system. Break down the…
A: Computer communication is a procedure that allows two or more devices to exchange data, knowledge,…
Q: I was wondering if you could forecast any significant hardware developments in the computer industry…
A: Over the last several decades, computer technology has seen significant advancements. In the last 50…
Q: In a dual core processor, consider first four letters of your name coming as processes each having…
A: If the first four letters of a name are used as processes with size equal to their ASCII code in…
Q: How much of the operating system's launch should be devoted to operations that may be eliminated in…
A: Introduction : A system's kernel is its beating center. It serves as a link between programs and the…
Q: I need to know the distinction between a casual analysis, a statistical analysis, and a Pareto…
A: The answer is given below step.
Q: What kinds of choices may management make after the systems analysis phase is through, and what…
A: After the systems analysis phase is complete, management may make several choices, including:…
Q: What precisely are the many forms that malicious software might take? What distinguishes worms from…
A: Basics Malware is evil software that permits unauthorised access to networks for purposes of theft,…
Q: If we use direct encoding of RGB values for each primary color, how many color combinations are…
A: RGB colour space: One of the most used colour coding systems in computers and other digital devices…
Q: In what ways are optimized compilers useful? As a developer, how would you put it to use? When…
A: Compiler optimization may be described as a crucial component of contemporary software: enabling an…
Q: The operating systems on a mainframe and a laptop couldn't be more different from one another. How…
A: Introduction : A computer's operating system (OS) is a piece of software that enables the hardware…
Q: Please enumerate the top eight guidelines for creating user interfaces. If pressed, how would you…
A: The design of user interfaces should adhere to these eight essential guidelines, which are listed in…
Q: Exactly how is TLS different from SSL in terms of significance? To guarantee the safety of data…
A: Since you asked many inquiries, we will address the first one first. A secure socket layer, or SSL,…
Q: Cybercrime comes in many forms, each with its own set of repercussions. Knowing them might help you…
A: Cybercrime may be divided into two basic categories. Type I: Advance Cyber Crime: Commonly referred…
Q: To what extent is it important to be technologically literate, and how can one acquire such skills?
A: Technology literacy is the use of technology to solve problems and perform tasks effectively. It…
Q: Both relational and non-relational databases store data, but in various ways, and allow users to…
A: Relational and NoSQL databases have diverse architectures, store data in various ways, and are…
Q: Problem 8: Divide and Conquer Recurrences Consider the recurrence that naturally arises in some…
A: [a] The initial condition T(1) = 1 means that the base case of the recurrence is when n = 1, and the…
Q: To what extent is it difficult to achieve a reasonable compromise between the performance of the…
A: Achieving a reasonable compromise between the performance of the CPU, RAM, bus, and other devices…
Q: Differentiate bet network address and broadcast address
A: According to the information given:- We have to differentiate between network address and broadcast…
Q: In order for a network to operate optimally, what three things must be true? Can you give me a quick…
A: Introduction: When two or more computers are connected, resources (such printers and CDs) may be…
Q: Take into account the possibility that the cloud computing movement has an influence on the way…
A: The process of shifting any digital company's activities to the cloud is known as THE CLOUD…
Q: Is it realistic to think that cloud-based collaboration solutions will be employed in a wide variety…
A: Employees can collaborate on documents and other types of data stored off-site and outside of the…
Q: That's why it's crucial to make affordable, high-quality computers. Can an affordable, rapid, and…
A: Yes, it is possible to make an affordable, rapid, and high-quality computer. However, the specific…
Q: What you mean by "two level logic" is beyond my comprehension. Is it connected to the rest of the…
A: A logic architecture that only employs two logic gates between input and output is known as…
Q: Explain the most typical scenario in which the TCP three-way handshake is susceptible while sending…
A: Due to the vulnerability of the TCP three-way handshake, a common scenario involves two computer…
Q: Record the steps required to complete the "ADD E" command in RTN.
A: Introduction: The stages in the instruction execution cycle are as follows: fetch. decode. Execute.…
Q: What innovations in computer hardware do you think will emerge in the next decade, and why? What…
A: Introduction : Computer hardware includes the computer's central processing unit (CPU); memory such…
Q: Describe how using CSS may simplify website upkeep by reducing the number of HTML files.
A: Making use of CSS has a lot of benefits. The simplicity of website upkeep is one of the major…
Q: what is SANS' official goal? What part does it play, more specifically, in the process of certifying…
A: Introduction : SANS (SysAdmin, Audit, Network, and Security) is the world's leading information…
Q: Have you found four distinct advantages of using discrete event simulation?
A: According to the information given:- We have to define four distinct advantages of using discrete…
Q: Provide three instances of event simulations that differ from one another.
A: INTRODUCTION: Simulation approaches aid understanding and experimentation because the models used in…
Q: Problem Statement: Using a repetition, write a program that will ask the user to enter a character…
A: 1) Below is C++ Program that ask user to enter a character(L or R) and number, then generate a…
Q: When CPUs are printed and electricity can't be changed, how can we predict what would happen if we…
A: CPU clock speeds have experienced minimal increase since 2005. Why haven't they increased? Here's…
Q: Just what do you get by using cloud services? Is there a way to be safe when using cloud services?…
A: Introduction : Cloud services are a type of web-based computing service that allows businesses and…
Q: How does one quantify the trustworthiness of software, and what metrics are used in this process?
A: The dependability of the software product is measured using reliability measures. The kind of system…
Step by step
Solved in 3 steps

- This type of malware is similar to a denial of service (DOS) attack because it denies the user access to the file until a fee is paid. a) Ransomeware b) Trojan horse c) Payware d) Zero-day virusWhen a default account is granted wide permissions in an operating system, this will make it difficult for an attacker to attack the system. True FalseWhen a default account in an operating system is granted broad rights, it makes it harder for an attacker to exploit the system. True False
- When a default account in an operating system is given broad rights, it makes it harder for an attacker to exploit the system.True FalseA denial-of-service (DoS) assault against a mail server is what is known as: Attainment by interception Attainment by fabrication Attainment by modificationDoS assaults may damage a company that depends significantly on its web application servers, such as an online shop. What are some of the most well-publicized DDoS assaults in recent memory? Who was the intended victim? How many denial-of-service (DoS) assaults occur on a regular basis? What are some methods for preventing DoS attacks?
- The macro virus infects the key operating system files located in a computer’s start up sector. True False SaveComputer Science While reviewing the /etc/shadow file, a security administrator notices files with the same value. Which of the following attacks should the administrator be concerned about? A. Plaintext B. Birthday C. Brute-force D. Rainbow tableExplain DDoS (distributed denial of service) attacks in detail. DDoS attacks are not to be confused with Denial of Service (DoS) attacks.
- This type of malware uses recent or unknown vulnerabilities to attack a system before it is known a) Zero-day virus b) Single-day virus c) Spyware d) RansomewareDoS attacks may be detrimental to a business that is heavily reliant on its web application servers, such as an online retailer. Which DDoS attacks have garnered the most attention in recent memory? Who was supposed to be the targeted victim? How often do denial-of-service (DoS) attacks occur? What are some techniques for avoiding denial-of-service attacks?The macro virus attacks the critical operating system files contained in the start-up sector of a computer. True False

