Draw the graph in matlab Show the running code and output
Q: Share TWO best IT applications that support your daily routine.
A: There are many IT applications that I use in day-in-day-out. Some of the them which are really good ...
Q: B) Write a PYTHON script to enter a value of S (between 1 and 3) for (50) entered values of X then f...
A: Use if-elif to check for the value of S and then use a for loop to accept input for 50 times
Q: Explain the purpose of everyline of this program. Source Code: import java.util.Scanner; public c...
A: Here, I have to explain the above code with an explanation.
Q: What is database security, exactly? What are two approaches to database security?
A: Database security defines the range of tools, controls, and measures designed to establish and prese...
Q: What is the difference between implicit intent and explicit intent? Write code for sending User Name...
A: Intent can be defined as it is a type of messaging object which shows of action is going to get perf...
Q: nformatio
A: To start building a complete, professional job listing for your company, add your information securi...
Q: Database administrators are in charge of backing up the database, while users are in charge of backi...
A: Introduction: As we all know, backup is a vital activity that must be performed regularly to avoid d...
Q: What are all of the interview questions (at least six) that the requirement analyst asks when buildi...
A: Introduction: Student life cycle management system is a comprehensive data-driven approach that help...
Q: To swap between two numbers (a and b) * t=a;b=a;b=Dt O t=a;a=b;b=t O a=t;t=b;b=t a=b
A: The swap() function is used to swap two numbers.
Q: What is the output of this code segment when the input value of X equal 100.
A: Out of range
Q: Write three advantages and disadvantages, of the major traffic components. Provide table
A: The distinction between disadvantage and advantage as nouns is that disadvantage is a flaw or unwant...
Q: What are the drawbacks of using OOPs?
A: INTRODUCTION: Object-oriented programming (OOP) is a programming paradigm based on the notion of ob...
Q: Sort DNS records by the kind of record they include. Describe each with examples and a brief explana...
A: Introduction: A typical method of deploying Content Delivery Networks is to add the CDN's address as...
Q: Consider the following ERD; consider additional attributes if needed Write relational algebra expres...
A: Here i write relational algebra query for all : ====================================================...
Q: Determine the various network layers, such as the edge, core, and access.
A: Introduction: A network is a collection of computers, servers, mainframes, network devices, peripher...
Q: What are the risks connected with using the MD5 algorithm to sign certificates?
A: Given: What are the vulnerabilities associated with signing certificates using the MD5 algorithm?
Q: #include using namespace std; main() { int a=3, b=2,c=a*b; b++; a=b++; b++;
A: INTRODUCTION: We need to tell the output of the code
Q: What Is A Management Information Systems Degree?
A: Introduction: Management Information Systems (MIS) is a difficult topic of study that focuses on com...
Q: Let's pretend we have a fully developed m-ary tree. The tree has internal vertices if the value of m...
A: Given: Let's pretend we have a fully developed m-ary tree. The tree has internal vertices if the val...
Q: What are the two most common types of UPSs?
A: Introduction: Usually there are three types of UPSs. Two primary types of UPSs would be:- Online ...
Q: 2.15 2.2, 2.5> Provide the type and hexadecimal representation of the following instruction: sw St3,...
A: Below is the answer to above question. I hope this will be helpful for you...
Q: . In this java program, explain everyline of this code. Source Code: import java.util.*; public c...
A: Algorithm: 1)This program randomly generates two number between 0 to 4 and assign it to array arr at...
Q: Complete the Truth Tables. STATEMENT: (? ∧ ?) ∨ ~? p q p ∧ q ∼p (p ∧ q)∨∼p T T T ...
A: As given, we need to complete the truth tables for the given statements. i) (p ∧ q) ∨∼p ii) ~q → (~...
Q: What are the most essential considerations in physical database architecture?
A: Physical database architecture can be defined as the way in which the database and the files get st...
Q: B. Make a functional simulation of the equation by drawing the circuit diagram as it is. All possibl...
A:
Q: In this short introduction, consider the advantages and disadvantages of connectionless protocols as...
A: Introduction: When two network endpoints interact using a connectionless protocol, they do so withou...
Q: What is the difference between ASCII and Unicode? What are some of the difference between string and...
A: Introduction: What is the difference between ASCII and Unicode? What are some of the difference betw...
Q: What steps are involved in modelling fully distributed systems from beginning to end?
A: Introduction: A distributed system is a computing environment in which different components are disp...
Q: A star configuration of a network represents its structure as a graph with an edge from a single, ce...
A: Here, I have to provide a solution to the above question.
Q: SALESMAN Colunns Data Constrants lerants istatstes ITrogers IFiashback lDeperdendes IDetals İPartons...
A: Use update command to change the commission of salesman. Option b is correct
Q: Make a program that input position number and day of work and compute the total salary earn... Sampl...
A: import java.util.*;public class Main { public static void main(String[] args) { Scanner scan...
Q: Justify why deep access is better than shallow access from the standpoint of a coder; avoid making a...
A: Introduction: Deep and shallow binding are two variable access strategies used in computer languages...
Q: Write the following function/procedure in MIPS. **only $s1, $s2, $a0, $v0 registers can be used. ...
A: MIPS assembly language code for the given question : func: addiu $sp,$sp,-24 sw $fp,20($sp) move $fp...
Q: Give an example of an application that requires algorithmic content at the application level and dis...
A: Given: Give an example of an application that requires algorithmic content at the application level...
Q: Explain how a function works with a relevant example.
A: Introduction Using a relevant example, explain how a function works.
Q: If the opcode field of instructions in a microprocessor's architecture is 16 bits wide, what is the ...
A: total possible instruction would be 2n where n is the number of bits in the opcode.
Q: 2. For a n-vector x, and X1 +x2 X2 + x3 y = Ax = Xn-1 + Xn a) Find A b) Are the columns of A linearl...
A: Hi Dear!! Please positive feedback!!! a)
Q: What exactly are cloud-based backup systems, and what are some of their advantages?
A: Cloud based backup can be defined as it is a service which contains data stored on remote server so...
Q: Multiple Choice Question A database management system needs _________ to prepare the data for prese...
A: Data in database is single item that are stored in a database, either individually or as a set. Data...
Q: 3. You have an open map document that has ten layers including one named SEWERS that has a line geo...
A: The raster data model is widely used in applications ranging far beyond geographic information syste...
Q: #include using namespace std; int main() { int x,y; or (x=0 ;x 3) break ; cout << y << endl; }}} O ...
A: Given code is in c++ Using for loop print the loop.
Q: Denial of Service (DoS) is one type of attack, which of the following action-can perform when it acc...
A: Here in this question we have asked about denial of service attack..and among four option we have to...
Q: Explain how HDFS and MapReduce are mutually beneficial.
A: Introduction: Hadoop spreads data processing over a cluster of commodity computers and runs on sev...
Q: 1. Under the user location. scenario, all record- and file-locking activities are performed at the e...
A: Choose the correct answer for the given question.
Q: What is the output of the following code when x is equal 5. x CInt(Text1.Text) If x = 1 Then MsgBox ...
A: Solution: The correct answer is 'Wednesday' Explanation: In this visual basic program assign the val...
Q: What are the most important features of a computer processor?
A: Introduction: The logic circuitry that listens to and executes the fundamental instructions that ope...
Q: What exactly is computer scalability?
A: Introduction: Scalability is tied to both computer systems and business transformation. It refers to...
Q: Assume we have a cache memory consisting of eight one-word blocks and the following sequence of bloc...
A: I'm providing the answer of above question. I hope this will be helpful for you....
Q: A CPU has a clock speed of one gigahertz (GHz). The processor's CPI was determined to be 6 cycles pe...
A: Introduction A CPU has a clock speed of one gigahertz (GHz). The processor's CPI was determined to b...
Q: Sort DNS records by the kind of record they include. Describe each with examples and a brief explana...
A: Introduction: A DNS record is a database entry that maps a web address to an IP address. DNS records...
Draw the graph in matlab
Show the running code and output
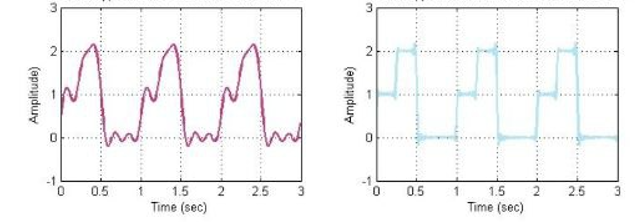
Step by step
Solved in 4 steps with 4 images


