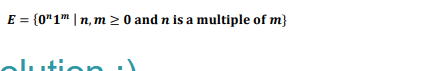
E = {0"1" |n, m≥ 0 and n is a multiple of m}
Q: What characteristics must computer graphics possess for optimal operation?
A: Introduction: When a collection of photographs has to be edited or when an image needs to be created…
Q: What advantages and benefits do information systems have?
A: Let's first discuss about the information system before knowing the benefits of it. In the digital…
Q: What are the functions and operation of an operating system in a computer system?
A: Operating system is a system software which manages the computer software and hardware resources by…
Q: It is necessary to provide a brief summary of nonvolatile solid-state memory technology.
A: Mounting refers to the grouping of files in a file system structure accessible to the user of the…
Q: Write a program in C++ that finds the count of a number in a list of integers from a text file named…
A: Here is the c++ code: See below step for code.
Q: What are the disadvantages of using a Data Modeling strategy?
A: Data Modeling strategy: Analyzing data items and their connections to other things is the process of…
Q: What advantages and benefits do information systems have
A: Answer:
Q: Create a JFlap Turing machine that has the alphabet of a, b, c, and null. The tape initially has…
A: The required JFLAP Turing Machine is below:
Q: The speed, memory, and array size of contemporary digital computers are quite remarkable.
A:
Q: What distinguishes a conceptual data flow diagram from an actual data flow diagram?
A: Definition: A conceptual data flow diagram and an actual data flow diagram are two different things.…
Q: Solving First Order Differential Equations dsolve Symbolic solution of ordinary differential…
A: Answer: % Program script file clc,clear allsyms…
Q: Assume the Circularly Linked List as follows, please write a code to insert the new data node into…
A: In this question we need to write a program to insert an element in a circular linked list.
Q: Please describe briefly the strategies for nonvolatile solid-state memory that are gaining in…
A: Introduction: Assumed: nonvolatile memory found in solid-state electronicsA memory system that is…
Q: What are your thoughts on the need for many addressing modes in a computer system?
A: Intro Modes of address Addressing modes can be thought of as the method used to specify the operand…
Q: What's the difference between the models of Multithreading?
A: The system must manage both kernel and user threads. The seed of the operating system supports…
Q: Should system users be involved in system development activities, or should systems professionals…
A: System Development: System development is the process by which IT professionals design, program,…
Q: In this architecture, the message M is not divided into smaller packets at any layer.
A: The answer is
Q: When a control hazard occurs, what usually happens is to simply insert 3 bubbles. But, why does the…
A: Dependencies in a pipelined processor There are mainly three types of dependencies possible in a…
Q: Write a program that sorts the values inside the array in ascending order using the selection sort…
A: The selection sort technique the list is divided into two parts, in one part all elements are sorted…
Q: Give some instances of how information system principles operate.
A: Information System principles: User involvement, user control, interface design, information…
Q: In this project, you will complete a C-class by writing a copy constructor, destructor, and…
A: Constructor and destructor:General Contractors are the only class functions that do the construction…
Q: Explain the differences between system software and application software. Among other things,…
A: The difference between system software and application software is 1) The application software is…
Q: We have gotten used to using a variety of computers throughout time. Can you describe them in broad…
A: introduction: Computers have undergone many eras of development. Computers have evolved to meet…
Q: What are the two primary operating system functions?
A: Operating system is a special software program which acts as a user interface between the user and…
Q: Both coherent and noncoherent psk demodulators demodulate signals differently.
A: In coherent demodulation the receiver needs to be in synchronization with the transmitter in terms…
Q: Which of the following is/are a difference between STL arrays (e.g. std:: array) and C-style arrays…
A: Hello stududent
Q: The income tax that employees need to pay are as below: For salary greater than or equal to 10000…
A: Here is the python code: See below steps.
Q: How improvements in information and communication technology have helped society from a computer…
A: Introduction: The infrastructure and parts that make up modern computers are known as ICT, or…
Q: What design pattern should Shira use to implement her desired API? ick ONE option RAII ("Resource…
A: Hello student I am giving this solution as per my best of knowldge
Q: Why do certain organizations choose a distributed computer system over a centralized one, while…
A: Advantages of using DDP: The three advantages of DDP that are most often emphasized are savings in…
Q: Which of the following is/are true of a function marked as constexpr in C++17? Select all that…
A: constexpr keyword is used to create compile-time constants. A constexpr function is a function…
Q: Is it feasible to examine how various businesses use information systems?
A: Introduction: To function effectively and raise the company's overall performance, they must plan…
Q: Describe briefly the increasingly prevalent nonvolatile solid-state memory technology.
A: The memory in question is solid-state and non-volatile. memory that is impervious to tampering.…
Q: Why is the notion of a file so simple but so potent?
A: introduction: Because it enables one to write extremely big and very tiny integers swiftly and…
Q: Two features distinguish the classroom technology program. Specify and explain each of these two…
A: Introduction: A teacher development course called Learning Technologies for the Classroom is…
Q: What distinguishes a conceptual data flow diagram from an actual data flow diagram
A: Please find the answer below
Q: Let G be a Context-Free grammar which is in the Chomsky Normal Form. To check that this grammar…
A: The complete answer is below:
Q: Topic: Censorship of the Internet Justify the proposed solution (s) for the topic from social,…
A: The censorship of the internet is very important from social, legal, and other perspectives.
Q: Dynamic memory provides a number of benefits over static memory, but it also has limitations.
A: The advantages and disadvantages of dynamic and static memory are as follows: Dynamic Allocation…
Q: Why did you choose Microsoft Excel above other alternatives?
A: Accounting page programming in Microsoft Excel has become a standard component of the majority of…
Q: 6. Write a Python program that reads a text file called student.txt. . The input text file contains…
A: Below I have provided a python program for the given question. Also, I have attached a screenshot of…
Q: In the index.htm/file, add a class attribute with the value tablet-desktop to the examples div In…
A: Let's understand first what are the html classes and the id attributes . When we create the element…
Q: In terms of descriptions, what is the difference between a file's logical and physical descriptions?
A: Physical files:- Actual documents contain the genuine information that is put away in the framework,…
Q: The influence of information technology on society as a whole and on our everyday lives Describe the…
A: Introduction: The three following business models would struggle to develop into successful…
Q: What are files? Why do we open and shut files? What if we use this approach?
A: A File : A container for the storage of information within a computer system is referred to as a…
Q: A computer employs RAM chips of 512 x 16 and ROM chips of 1024 x 8. The computer system needs 4K…
A: a) Given the following data: Size of RAM Chip (RAS) = 512 X 16 = 8192 = 213Size of ROM Chip (ROS) =…
Q: How can you distinguish between primary and secondary memory
A: Please find the answer below :
Q: What is the need and reason for an architectural view/view model?
A: Architectural Model-View-View Model (MVVM) The model is described as follows: Model (DATA):…
Q: You are give a matrix (a list of lists) of DISTINCT integers and a target number. Each row in the…
A: Program: public class Main { public static int[] searchMatrix(int[][] matrix,int target){…
Q: Does expressing a weighted graph using adjacency lists have any drawbacks
A: The following are the drawbacks of an adjacency list form of a weighted graph representation:…
draw
Step by step
Solved in 4 steps with 3 images

- /* segvhunt.cFind and eliminate all code that generates Segmentation Fault*/#include <stdio.h>int main() {char **s;char foo[] = "Hello World";*s = foo;printf("s is %s\n",s);s[0] = foo;printf("s[0] is %s\n",s[0]);return(0);}def find_root4(x, epsilon): ''' IN PYTHON Assume: x, epsilon are floating point numbers and epsilon > 0 Use bisection search to find the following root of x such that If x >=0, return y such that x - epsilon <= y ** 2 <= x + epsilon Else, return y such that x - epsilon <= y ** 7 <= x + epsilon Note: You must use bisection search to implement the function. ''' passA(n) __________ contains 8 __________.
- ce from the user t using recursion.Consider the given pmgqgh finclude(iostren} using namespace std; int main(){ //int n=2 take of y for(int i=0;ipython Q3: Repeatedly Cube Implement the following function, which cubes the given value x some number n times, based on the given skeleton. (define (repeatedly-cube n x) (if (zero? n) x (let (_________________________) (* y y y))))
- Count consecutive summers def count_consecutive_summers(n): Like a majestic wild horse waiting for the rugged hero to tame it, positive integers can be broken down as sums of consecutive positive integers in various ways. For example, the integer 42 often used as placeholder in this kind of discussions can be broken down into such a sum in four different ways: (a) 3 + 4 + 5 + 6 + 7 + 8 + 9, (b) 9 + 10 + 11 + 12, (c) 13 + 14 + 15 and (d) 42. As the last solution (d) shows, any positive integer can always be trivially expressed as a singleton sum that consists of that integer alone. Given a positive integer n, determine how many different ways it can be expressed as a sum of consecutive positive integers, and return that count. The number of ways that a positive integer n can be represented as a sum of consecutive integers is called its politeness, and can also be computed by tallying up the number of odd divisors of that number. However, note that the linked Wikipedia de0inition…Write a function that takes in an integer n and computes n!. Do this without recursion. In [ ]: deffactorial_iter(n):"""Takes in an integer n>0 and returns the product of all integers from 1 to n."""# YOUR CODE HEREraiseNotImplementedError() In [ ]: In [ ]: assert factorial_iter(6) == 720 assert factorial_iter(7) == 5040 assert factorial_iter(10) == 36288001. Let L = {w {a, b}* : w contains bba as a substring that starts in an odd numbered position in the string (where numbering starts at 1)}. For example, bbbbaaaab L, while bbbaaaab L. Show an NDFSM that accepts L
- Count consecutive summers def count_consecutive_summers(n): Like a majestic wild horse waiting for someone to come and tame it, positive integers can be broken down as sums of consecutive positive integers in various ways. For example, the integer 42 often used as placeholder in this kind of discussions can be broken down into such a sum in four different ways: (a) 3 + 4 + 5 + 6 + 7 + 8 + 9, (b) 9 + 10 + 11 + 12, (c) 13 + 14 + 15 and (d) 42. As the last solution (d) shows, any positive integer can always be trivially expressed as a singleton sum that consists of that integer alone. Given a positive integer n, determine how many different ways it can be expressed as a sum of consecutive positive integers, and return that count. The count of how many different ways a positive integer n can be represented as a sum of consecutive integers is also called its politeness, and can be alternatively computed by counting how many odd divisors that number has. However, note that the linked…Given an integer array nums, return all the triplets [nums[i], nums[j], nums[k]] such that i != j, i != k, and j != k, and nums[i] + nums[j] + nums[k] == 0. This time, your problem has additional details: Constraints: The solution set must not contain duplicate triplets. The order of the output and the order of the triplets does not matter. 3 <= nums.length <= 3000 -105 <= nums[i] <= 105 Function definition for Java: public List<List<Integer>> threeSum(int[] nums) { // Your code here } Function definition for Python: def threeSum(self, nums: List[int]) -> List[List[int]]: #Your code here Announced Test Cases: Input: nums = [0,1,1] Output: [] Explanation: The only possible triplet does not sum up to 0.Input: nums = [-5,0,5,10,-10,0] Output: [[-10,0,10],[-5,0,5]] Explanation: There are two possible combinations of triplets that satisfy: (-5,0,5) and (-10,0,10). Hint: There are 3 well-known ways to solve this problem!Edit this program so that it returns ecg data instead of heart beat in BPM. #include <ArduinoBLE.h> #define BLE_UUID_HEART_RATE_SERVICE "180D"#define BLE_UUID_HEART_RATE_MEASURMENT "2A37"#define ECG_SERV_UUID 0x2D0D#define ECG_MEAS_UUID 0x2D37#define ECG_NUM_CHANS_UUID 0x2D38#define ECG_SAMPLE_SETS_UUID 0x2D39#define ECG_COMMAND_UUID 0x2D3A #define HRM_VALUE_FORMAT_8BIT 0#define HRM_VALUE_FORMAT_16BIT 1#define HRM_SENSOR_CONTACT_NOT_DETECTED ( 2 << 1 )#define HRM_SENSOR_CONTACT_DETECTED ( 3 << 1 ) typedef struct {uint8_t flags;uint8_t heartRate;} heart_rate_measurment_t; union heart_rate_measurment_u{struct {heart_rate_measurment_t values;};uint8_t bytes[ sizeof( heart_rate_measurment_t ) ];}; union heart_rate_measurment_u heartRate = { .values = { .flags = 0, .heartRate = 0 } }; #define BLE_DEVICE_NAME "Arduino HRM"#define BLE_LOCAL_NAME "Arduino HRM" BLEService heartRateService( BLE_UUID_HEART_RATE_SERVICE );BLECharacteristic heartRateCharacteristic(…



