e access tim ess time of c -1 is thrice th ty from the L ock cycles. T of the system
Q: Which one of the following is a real time operating system? a) Windows CE b) RTLinux c) VxWorks d)…
A: let's see the correct answer of the question
Q: Describe the DNS in its entirety, including iterated and non-iterated queries, authoritative and…
A: Given: The goal of DNS is to translate a domain name into an IP address. This is done by getting the…
Q: Choose the correct MATLAB nmand to rotate matrix A 180 nter clockwise:
A: "rot90" is command used to rotate the array by 90 degrees. We will see it with the help of code…
Q: Explain each part of the Pseudocode below: START Public Class BankingSystem Declarations…
A: As per the question statement, It is asked to explain the given pseudo code.
Q: 1. (Store numbers in a linked list) Write a program that lets the user enter numbers and displays…
A: As the programming language is not mentioned here, we are using JAVA The code and output screenshot…
Q: Do you have any comments on the metrics of user interface design?
A: Comments on the metrics of user interface design are given below:
Q: In the field of computer science, what does the abbreviation for "Transaction Protocol Data Unit"…
A: In the field of computer science, what does the abbreviation for "Transaction Protocol Data Unit"…
Q: Statement A type of optical storage Has the largest storage capacity Can be dual-layer Blu-ray (✓)…
A: Please refer below for your reference: According to company guidelines we are restricted to answer…
Q: Find the problem location for the following case to make the program able to run?
A: None of the given
Q: Application software and system software will both be compared.
A: The answer is given below...
Q: Here are file entry points. I'm curious about their pros and cons.
A: File organization is nothing more than arranging all of an employee's records alphabetically by name…
Q: Which method is used to make certain that legacy systems will continue to evolve in the future?
A: Required: Which method is used to ensure that legacy systems keep getting better? Reverse…
Q: Because threads are little, they are referred to as "lightweight." Are system resources distributed…
A: Given: It is dubbed a lightweight process to emphasize how a thread is similar to a process but is…
Q: Typical web-based applications are made up of a number of different components, which are listed…
A: Web-based application: A web-based application is any programme that is available through HTTP via a…
Q: Q9: If you have 7.3 version of MATLAB how you can open a script file :
A: Matlab compiler has different icons to full fill the different needs of the programer. The icons in…
Q: What exactly is meant by the term "wear leveling," and why is it important for solid-state drives…
A: What is wear levelling, and why is it essential to identify SSDs? Equalizers are worn. Wear…
Q: What does it mean precisely when memory is lost?
A: Given: Forgetting things, being confused, having trouble focusing, and other issues may all be…
Q: A programmer's perspective is critical, and you should avoid relying just on speed when making your…
A: Introduction: Deep binding and shallow binding are two approaches to accessing variables that may be…
Q: Which of the following is not the application of stack? a) A parentheses balancing program b)…
A: Given question are multiple choice selected question.
Q: I'd want to know which eight user-interface design ideas are most important. Is there a way to rank…
A: User-interface design: The user interface must be designed in such a way that it speeds the user's…
Q: Is there a reason why U3D is often referred to as "3D PDF"?
A: U3D is a 3D data structure and file format. It has .u3d extension. It is used in 3D PDF documents.…
Q: The use of cloud computing is associated with a variety of security flaws that are unique to this…
A: GIVEN: Cloud security is a problem that should be discussed at all organizational levels, from the…
Q: Which strategy is used to ensure that legacy computer systems continue to develop over time?
A: Reverse Engineering and Re-engineering ensure that legacy systems continue to develop in their…
Q: What is the role of the anchor MSC in GSM networks?
A: The anchor MSC is the MSC that handled the first call procedure.
Q: PYTHON: In this assignment, you will use all of the graphics commands you have learned to create…
A: Answer in step 2
Q: Q1) Write and design a project to find the value of y 14 Solution by visual basic y = ix! i=4
A: As per the question statement, We need to write VB code.
Q: 26. Which of the following package allows individuals to use personal computers for storing and…
A: The Personal Assistance package allows users to store and retrieve their personal information.…
Q: What exactly do you mean when you talk about "network security"? Describe how the data encryption…
A: Given: In general, network security refers to any firm's or organization's efforts to safeguard its…
Q: 2: write code to draw the following picture. 9 first 8 second 7 7 6 6 55 5 4 3 2 1 0 6 5 Mon 33 Tue…
A: In this question we have to construct the given chart which is bar chart. Here, we will use python…
Q: It is important to convey how tough it is to create user interfaces on a smart phone to a software…
A: Software Development: When a group begins work on a software project, there are five activities…
Q: Q3: A MATLAB function used to clear a selected variable value from workspace :
A: A matlab function used to clear a selected variable value from workspace
Q: What's the difference between on-premises and cloud-based IT security solutions?
A: correct answer is given below
Q: Process of removing an element from stack is called __________ a) Create b) Push c) Evaluation d)…
A: In this question we have to explain terms related to stack and give a answer to a provided…
Q: Pushing an element into stack already having five elements and stack s
A: Pushing an element into stack already having five elements and stack size of 5, then stack becomes
Q: Insert the correct forms of verbs in the brackets. (17.5 Marks) 1- In most countries of the world,…
A: 1. Belongs, Includes 2. designed, Developed ,extracts 3.Being 4.Travels 5.Done
Q: What are the characteristics of stack based IDS? a) It is programmed to interpret a certain series…
A: An intrusion detection system(IDS) is a system that monitors network traffic for suspicious activity…
Q: Q13: In the given MATLAB code identify the problem? x=1; while x<=10 y=x^2 end while command must…
A: Answer in step 2
Q: What's OS Partitioning? Advantages and disadvantages
A: OS Partitioning: This is the easiest way to store several processes in main memory. This…
Q: rns about the safety of cloud comp
A: Introduction: Below the describe concerns about the safety of cloud computing have been brought to…
Q: 1. Let M be the Turing machine defined by Table 1 where the start and final states are 90 and 92,…
A: Hi there, Please find your solution below, I hope you would find my solution useful and helpful.…
Q: . Sort It Yourself by CodeChum Admin A descending order means values arranged from largest to…
A: #include <iostream>using namespace std; int main() { // your code goes here int a,b,c;…
Q: Share your knowledge about the ARP protocol with a buddy. Please specify the operating layer at…
A: Introduction:- APR protocol and specify the operating layer at which it works as well as the kind of…
Q: The wind chill temperature, Twe, is the air temperature felt on exposed skin due to the wind. In…
A: As per the question statement, We need to write MATLAB code.
Q: Let G be a graph with n vertices and m edges. • True or false: All its DFS forests (for traversals…
A: Let G be a graph with n vertices and m edges.a. True or false: All its DFS forests (for traversals…
Q: What is the main difference between having "many threads" and having "many processes"? Would it be…
A: here in the given question ask for what is the main difference between having many threads and…
Q: On systems where there are multiple operating system, the decision to load a particular one is done…
A: On systems where there are multiple operating system, the decision to load a particular one is done…
Q: What advantages does it have over using an operating system that is specific to a given kind of…
A: An operating system (OS) is system software that manages computer hardware and software resources…
Q: How can one make sure that legacy systems keep evolving even after they have been implemented
A: GIVEN: HOW CAN ONE ENSURE THAT ANCIENT SYSTEMS CONTINUE TO EVOLVE?
Q: With drawing
A: Answer is given below-
Q: In as few words as possible, please explain how you think the progression from the first to the…
A: Evolution of computer technology is divided into 5 generations. In evolution of each generation,…
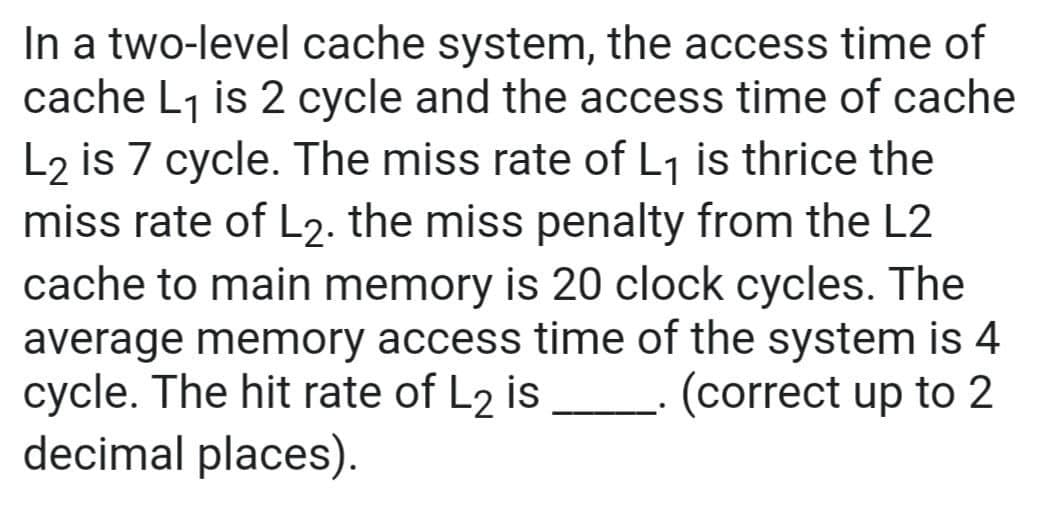
Step by step
Solved in 3 steps with 3 images

- A cache memory system with capacity of N words and block size of B words is to be designed. If it is designed as a direct mapped cache, the length of the TAG field is 14 bits. If it is designed as a 4-way set associative cache, the length of the TAG field will be ………… bits.Ifthere is a 64K cache with a block size of 7k, what is the number of bits in the indes field of block address, given the cache is (3) F Associative, (b) Direct Mapped, (¢) 2-way Sct Associative, and ) 4 - way Set Associative. bIn a microprocessor of 32 bit addresses, the tag length will change if we design a two-way set-associate cache versus a four-way set-associative cache, with the same number of cache lines in each organization, and the same number of data bytes per set. a. True b. False
- Take into consideration the difference between a fully associative cache and a directly mapped cache.For a direct-mapped cache design with a 32-bit address, the following bits of the address areused to access the cache.Tag Index Offset31–10 9–6 5–0a– What is the cache block size (in words)? b – How many entries does the cache have? c – What is the ratio between total bits required for such a cache implementation overthe data storage bits?The difference between a fully associative cache and a directly mapped cache is worth considering.
- Keep in mind the difference between a fully associative cache and a directly mapped cache.The ability to freely pair data items in an associative cache sets it apart from a directly mapped cache.Assume a cache system has been designed such that cach block contains 4 words and the cache has 1024 lines, the cache can store up 10 1024 blocks. What line of the cache is supposed 10 hold the block that contains the word from the twenty-bit address JA456:? In addition, what is the tag number that will be stored with the block?
- Distinguish between a totally associative cache and a direct mapped cache.For a direct-mapped cache design with a 32-bit address, the following bits of the address are used to access the cache.Tag Index Offset31–10 9–5 4–01. What is the cache block size (in words)?2. How many entries does the cache have?3. What is the ratio between total bits required for such a cache implementation over the data storage bits?Starting from power on, the following byte-addressed cache references are recorded. Address 0 4 16 132 232 160 1024 30 140 3100 180 2180 How many blocks are replaced? What is the hit ratio? List the fi nal state of the cache, with each valid entry represented as a record of <index, tag, data>Direct-mapped cache is a special case of set-associative cache where the set size is 1. So fully associative cache is a special case of setassociative cache where the set size is ______.

