e code in assembly language
Q: What measures may be taken to prevent DNS tunneling? How can you recognize port scanning attempts…
A: If a question has many parts, we need to respond to the first part. DNS tunneling is a kind of cyber…
Q: Can we expect any benefits from using the Vector Space Model (VSM) as opposed to the Latent Semantic…
A: Vector Space Model (VSM)- Vector space models are also called term space models. This model is an…
Q: a) let p, q and r be propositions. Simplify the following o proposition: ((r) ^ p ^ q) v ((-r) ^…
A: HERE IS COMPLETE SOLUTION REGARDING YOUR PROBLEM
Q: The difference between deterministic and non-deterministic computers according to their purpose and…
A: INTRODUCTION: When it comes to a determining whether or not machines are deterministic, it is…
Q: Global positioning system is shortened to "GSM." Why do you need a SIM card for your cell phone?
A: Introduction:The Global System for Mobile Communications, often known as GSM, was developed in the…
Q: Please enter an integer value: 0 Please enter an integer value: 45 Please enter an integer value: 65…
A: The program ask user to enter 5 unique integer values. It then prints those integers, find minimum…
Q: What distinguishes Ubuntu from other server operating systems, and what features does it share with…
A: Ubuntu is a free and open-source computer operating system (OS) that is derived from the Debian…
Q: What are blocks? what are they used for? can we pass them as arguments?
A: Note: As per companys rules we are suppose to answer only one question at a time. Kindly post other…
Q: he two primary roles of an OS should be briefly explained here.
A: Operating System "OS" is the interface between the computer user and the computer hardware. An…
Q: Explain why it matters more that object function takes precedence over constraints in linear…
A: Linear programming is used to determine the optimal solution to a problem with specified…
Q: In this session, we'll examine the significance of software architecture at every stage of the…
A: Here in this question we have asked to examine the significance of software architecture at every…
Q: Write a for loop in Java that will display (each on a separate line) a series of numbers based on…
A: Below I have provided java program
Q: World computer language allows logic to be run in a browser? Java JavaScript HTML SQL
A: Java : It is a compiler language so you can not run it on the browser because it required compiler…
Q: Discuss how data mining may be used to achieve various goals.
A: The mining of data has a wide variety of uses in the commercial world. For instance, the…
Q: This article will provide an in-depth overview of Windows Service Control Manager.
A: let us see the answer:- Introduction:- Service Manager is a folder in Windows that allows users to…
Q: In order for an IT project to achieve its required objectives and meet quality expectations, what…
A: Answer : For Any IT project the three boundaries Budget , time , and policy
Q: How do you distinguish between cohesion and coupling while creating software?
A: Cohesion: Cohesion is the sign of the relationship inside the module. It is the idea of…
Q: 2Wireless networking technologies, topologies, and future developments will be extensively…
A: Inexpensive to set up and ideal for mobile teams and users, wireless LANs are quickly becoming the…
Q: What does it mean to put the user first when designing software?
A: What is Software Development? Software development is a procedure used to generate standalone or…
Q: The nature of wireless networks causes a variety of complications. List three of these problems and…
A: The subfield of computer science that is simply referred to as computing networks is the focus of…
Q: What does Windows Service Control Manager accomplish, and what is its function?
A: Windows Service Control Manager: Windows Service Control Manager (SCM) is an extraordinary cycle…
Q: Because of its distinctive features and capabilities, the Ubuntu Server Operating System stands out…
A: Operating system: In fact, an operating system (OS) is a type of system software that is responsible…
Q: Help code.
A: PROGRAM INTRODUCTION: Include the required header files. Start definition of the method to…
Q: write code for Convert PDF to docx using Python
A: Code for Convert PDF to docx using Python is:-
Q: It is beyond the scope of this article to go into how processes are really implemented in operating…
A: A special entity that represents the work that would be implemented by the system is known as a…
Q: Which of the following is a commonly used Agile methodology for IT projects? a. Six Sigma b. Scrum…
A: The Agile technique divides a project into many parts and uses these phases to manage the project.…
Q: Talk about the increasing risks coming from inside an organization, as well as the precautions you…
A: Introduction Insider risks are dangers that might originate among a company's employees. Threats…
Q: Give some concrete examples of the differences between the operationalization of objective and…
A: Variables are crucial in any programming language for storing specified values during programmed…
Q: ting systems that aren't interrupted fu pt-driven most of the time.
A: An operating system (OS) is system software that manages computer equipment, software resources, and…
Q: For a number N, a goodArray is the smallest possible array that consists of only powers of two (20,…
A: As language is not provided doing it in python Programming Language below:
Q: In-depth discussion of architectural design's significance in software development.
A: The significance of architectural design in the process of developing softwareThe process of…
Q: Unfortunately, we cannot examine the inner workings of operating systems and how they accomplish…
A: An operating system (OS) connects the user of a computer to its hardware. An operating system…
Q: Network/OS systems have a distinct perspective on what is meant by "risk." Do you have any examples…
A: Answer: We will see here what do you mean by risk in the Network or OS and also we will see examples…
Q: A virtual private network (VPN) is the best option for protecting the perimeter of a network. Can…
A: In terms of network security, virtual private networks, or VPNs, are very crucial. Below are a few…
Q: End-to-end encryption could be a problem for application-level proxies. Please offer a method for…
A: End-to-end encryption: End-to-end encryption can affect application-layer proxies. Proxy-based…
Q: Which statement below displays the value of the class variable numRectangles of the Rectangle class?…
A: All the answers are marked below:
Q: Many commonly used programs and tools may be used to identify the main source of network problems.…
A: The first step is to comprehend how a router works. A router serves four main purposes: it routes…
Q: Windows Service
A: Windows Service Control Manager (SCM) is a built-in program that comes with Windows. You can control…
Q: What is a violation of the DRY principle? Where may they typically be found?
A: DRY Principle DRY can be defined as follows: Every item of knowledge must be represented in a system…
Q: 2Wireless networking technologies, topologies, and future developments will be extensively…
A: Wireless networking: Wireless local networks are reasonably affordable to set up and are ideal for…
Q: Is there any evidence to suggest that interrupt-driven operating systems outperform non-interrupted…
A: A non-interrupt driven OS relies on each task or driver processing a small amount before handing…
Q: Define each layer of the OSI model and explain its function.
A: The Open Systems Interconnection (OSI) model defines seven levels through which computer systems…
Q: Write a program that outputs inflation rates for two successive years and whether the inflation is…
A:
Q: Question 1: Draw the Venn Digrams for the following combincations of the sets X, Y and Z: (c)…
A:
Q: Where can I find out more about optimizing database performance? Why and how is focusing on just one…
A: According to Bartleby's criteria, I can only answer the first three subparts if they are connected…
Q: In this session, we'll examine the significance of software architecture at every stage of the…
A: Here, we will discuss the significance of architectural design in the software development process.…
Q: Give a little history of how wireless LAN standards came to be.
A: A local area network (LAN) consists of a series of computers linked together to form a network in a…
Q: How about we have a more in-depth look and study of your experiences with wireless security?
A: Wireless Security Wireless security, which includes Wi-Fi networks, is the defence against unwanted…
Q: How about we have a more in-depth look and study of your experiences with wireless security?
A: The term "wireless security" refers to the safeguarding of computers and data from harm when…
Q: What are the benefits of utilizing Design Patterns, and how do they work, in software development?…
A: Introduction to Design Patterns Some of the finest practices utilized by skilled developers of…
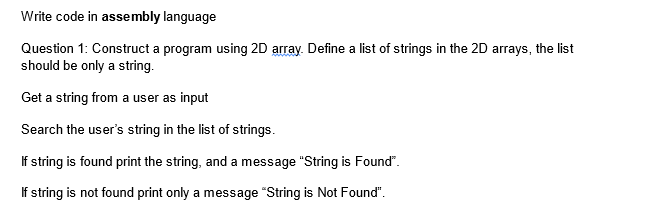
Step by step
Solved in 2 steps with 1 images

- Implement in C Program 5.20 LAB: Word frequencies Write a program that reads a list of words. Then, the program outputs those words and their frequencies. The input begins with an integer indicating the number of words that follow. Assume that the list will always contain fewer than 20 words, and each word contains fewer than 10 characters. Ex: If the input is: 5 hey hi Mark hi mark the output is: hey - 1 hi - 2 Mark - 1 hi - 2 mark - 1 Hint: Use two arrays, one array for the strings and one array for the frequencies. #include <stdio.h>#include <string.h> int main(void) { /* Type your code here. */ return 0;}Write a Java program to implement sequential search. Create a String array in main method and initialize it with 5 different names. Now take any name from the user, find whether that name is present in that array or not, and print the position of that name in the array if found. Write a search method to sequentially search the name from the array. Invoke the search method from the main method. The array and the name to be searched should be passed into the search method as parameters. Sample input & output:[Let’s assume that the 5 names are Diana, Becker, Ann, Eve, and Cory]Enter the name: CoryThe name is found at 5th position.Enter the name: Donald The name is not found.Now write a Java program to implement binary search for the above problem. [Hint: You can use equals() and compareTo() methods of String class.]Write a c program and fill a queue with random numbers between 0 and 100. The size of thequeue is assumed to be 15. After filling the array with random numbers, display the elementsin the queue and remove the elements of the queue and store these numbers according to thefollowing criteria.If the number in the queue is less than 50, remove it from the queue and store it insidequeue 2.Else, remove the number and store these values inside queue 3.Display all three queues on the screen.
- Write a program to input a list of numbers in an array and then rearrange this array in such a waythat all the odd numbers appear in the beginning of the array and all the even numbers appear in theend of the array. E.g., if the input list is 1,4,2,7,6,5,9, then after rearrangement the list should be:1,7,5,9,4,2,6. program should be in c language.Write a Java program to implement the following: Ask the user to enter the names of 3 Books and store them in an ArrayList called Book Remove the second book from the list Add the user to enter a new book name and store to be the first book of the list Ask the user to enter a book name, search for it in list, and print “exist” or “not exist” Print the book name at index 2 Print all list items using loop Print the size of the listWrite a program that reads a list of integers from input and identifies the mode (the value that appears most often). The input is a sequence of integers that ends with -1. Total number of integers in the list is unknown. Output the mode and end with a newline. Assume that the list is not empty and only one mode exists. Ex: If the input is: 5 9 2 -3 -5 -3 2 1 4 5 5 -1 the output is: 5 import java.util.Scanner; import java.util.ArrayList; public class LabProgram { public static void main(String[] args) { Scanner scnr = new Scanner(System.in); /* Type your code here. */ }}
- Write a Java program to create a new array list, add the following data {PHP, Java, C++, Python} and print out the collection.a) Print out all elements using foreach.b) Insert an element (JavaScript) into the array list at the first position.c) Remove the third element from the array list.d) Search an element (C++) in the array list.e) Remove all elements from the ArrayList.Implement in C Program 5.18 LAB: Output values below an amount Write a program that first gets a list of integers from input. The input begins with an integer indicating the number of integers that follow. Then, get the last value from the input, which indicates a threshold. Output all integers less than or equal to that last threshold value. Assume that the list will always contain less than 20 integers. Ex: If the input is: 5 50 60 140 200 75 100 the output is: 50,60,75, The 5 indicates that there are five integers in the list, namely 50, 60, 140, 200, and 75. The 100 indicates that the program should output all integers less than or equal to 100, so the program outputs 50, 60, and 75. For coding simplicity, follow every output value by a comma, including the last one. Such functionality is common on sites like Amazon, where a user can filter results. include <stdio.h> int main(void) { const int NUM_ELEMENTS = 20; int userValues[NUM_ELEMENTS]; // Set of data…Write a Java program using a one-dimensional array that accepts as input an integervalue asking for the number of elements for each list. This will be used to generate randomnumbers (5 to 69) for the one-dimensional arrays (List A and List B). The program willcompute for the product and store it in another array (List C).
- Write a C/C++ program that takes an input (array) from 1 to n (say n = 50) and displays the string representations of those numbers with following conditions If the current number is divisible by 2, then print CSU If the current number is divisible by 5, then print LB If the current number is divisible by both 2 and 5, then print CSULB If the number is neither divisible by 2 nor 5, then print the number Example: 1 CSU 3 CSU LB CSU 7 CSU 9 CSULB 11 CSU 13 CSU LB CSU 17 CSU 19 CSULB … Tasks to do: (4%) Implement the solution using a single thread (i.e., without using threads and only a main function with any other possible helper function for ease) with all the above conditions implemented in the correct order so that the results are correct. Reason about what can cause the algorithm to print unwanted results (think about the order in which you will write the above…Write a C/C++ program that takes an input (array) from 1 to n (say n = 50) and displays the string representations of those numbers with following conditions If the current number is divisible by 2, then print CSU If the current number is divisible by 5, then print LB If the current number is divisible by both 2 and 5, then print CSULB If the number is neither divisible by 2 nor 5, then print the number Example: 1 CSU 3 CSU LB CSU 7 CSU 9 CSULB 11 CSU 13 CSU LB CSU 17 CSU 19 CSULB … Tasks to do: (4%) Implement the solution using a single thread (i.e., without using threads and only a main function with any other possible helper function for ease) with all the above conditions implemented in the correct order so that the results are correct. Reason about what can cause the algorithm to print unwanted results (think about the order in which you will write the above…Write a program that reads a list of integers from input into an array and outputs "yes" if the list is sorted in ascending order between two provided positions. Otherwise, output "no". The first input specifies the number of items in the list. The next set of inputs is the list. The last two inputs are the start and end positions (inclusive). Assume the list contains less than 20 integers and position 1 is the first element. Ex: If the input is: 8 5 6 7 4 3 2 1 0 1 3 the output is: yes Ex: If the input is: 6 1 2 3 4 5 2 4 6 the output is: no

