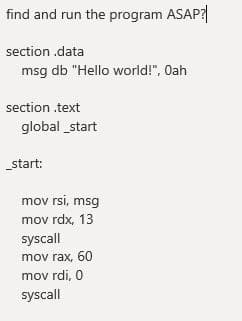
ection .data msg db "Hello wa ection .text global _start start: mov rsi, msg mov rdx, 13
Q: Which risk management techniques are the most effective for cloud migration?
A: Risk management techniques are most effective for cloud migration Administrative consistence…
Q: Describe a cloud storage application and explain how it varies from a traditional client storage…
A: Introduction: It is safe to say I believe in the ease and value that cloud storage provides because…
Q: What might a hypothetical business case for cloud migration look like?
A: Introduction When we develop a business case, we are ultimately driving a representation of return…
Q: So, what precisely is simulation? Why is MATLAB considered one of the best simulation software…
A: Justification: MATLAB is a high-performance programming language that was developed for use in…
Q: What are the benefits and drawbacks of using the cloud for data storage? A list of cloud-based…
A: Introduction: Basic cloud storage is a cloud computing approach in which data is stored on the…
Q: Assess the risks and benefits of cloud security from a security standpoint. The are a variety of…
A: Benefits Proficient recuperation - Distributed computing conveys faster and more careful…
Q: When RAM (Random Access Memory) is volatile, why do we need cache memory? Is it feasible to use a…
A: Introduction: The information temporarily saved in RAM is deleted when you restart or shut down your…
Q: What kind of storage medium would you recommend for archiving reasons to a classmate?
A: Introduction: A solid state drive and a flash drive (also known as a thumb drive or a USB…
Q: Program Input: Two values one for the age and the other for the number of monthly subscriptions.…
A: The code is given below.
Q: Provide a high-level description of how the gradient mesh tool works and how it is used. The…
A: Gradient mesh tool - it is a tool implemented in vector graphics software and the main function of…
Q: What are the disadvantages of utilizing a cloud storage service rather than a traditional client…
A: Introduction: Cloud computing is a means of storing and managing data on distant servers via the…
Q: Describe the memory structure of the programme memory on the 8051 microcontroller.
A: Introduction: The 8051's internal data memory is separated into two categories. This is a set of…
Q: The ramifications of a data breach on cloud security are not well understood. In what ways may you…
A: Justification: When critical company data housed in a private cloud instance is mistakenly exposed…
Q: Explain the term "operating system." Provide a list of the functions that an operating system…
A: Operating system: The operating system is the software that allows application programmed and…
Q: Is it feasible for organisations to operate in a safe and secure way while using cloud computing…
A: yes, It is possible for organisations to operate in a safe and secure way while using cloud…
Q: In network security and cybersecurity, what role does intrusion detection and prevention play?
A: Introduction: In order to keep a network safe, a network intrusion detection system (NIDS) is…
Q: The ramifications of a data breach on cloud security are not well understood. In what ways may you…
A: Breach of cloud data A data breach occurs when secure/confidential information is intentionally or…
Q: Use the Inverse Matrix method to solve the following system of linear equations. 3X + Z = 31 2X –…
A: This question comes from Matlab Programming Language which is a paper of Computer Science. Let's…
Q: Write a program to roll dice (use the “rand” function) for 36,000 times and then calculate the…
A:
Q: What is the purpose of UDP? Wouldn't it have sufficed to simply allow user processes to send raw IP…
A: UDP: UDP stands for User Datagram Protocol. It is a communication protocol used for establishing…
Q: Specifically explain tehnically how dow 5G improve on previous cellular networks to provide low…
A: In this question, we have to understand the improvement of 5G technology on previous cellular…
Q: A cassette drive is a term that refers to a classic cassette recorder that is used to store or load…
A: Introduction: Cassette drive refers to a conventional cassette recorder that is used to store or…
Q: 1) Structuring elements are aligned with the image where the the image origin. of the kernel is…
A: Note: Since the given question is multipart we are advised to do only first three parts. Kindly post…
Q: s and line them up on the desk (it’s a very long desk). The colour of the ith crayon is a string…
A: code : #include<bits/stdc++.h>using namespace std;struct theWrd {string word;int…
Q: What is the relevance of intrusion detection and prevention as a basic network defence and…
A: With hundreds of thousands of government employees doing telework, protecting federal systems is…
Q: How might endpoint devices and infrastructure devices be connected in a local area network? To…
A: According to the information give:- We have to define the endpoint devices and infrastructure…
Q: The user interface for your application is created in the IDE's window.
A: Overview: An integrated development environment is software that integrates common developer tools…
Q: Is cloud computing having a detrimental impact on e-commerce?
A: Introduction: Cloud computing has several advantages in the e-commerce business, including security…
Q: Define a function drawCircle. This function should expect a Turtle object, the coordinates of the…
A: The program is written in Python Language:
Q: What exactly is a system selection report?
A: System Selection Report System selection report is being written to explain the reasons behind the…
Q: Here please Write a function in Computer Graphics using any Graphic Function. See the pic for the…
A: Here we can write the C++ coding for the given image , and run the code and attach the output , so…
Q: As a network administrator, what transport layer protocol do you employ to convey video streaming…
A: Overview of video streaming data: Both streaming and HTTP-based methods are used to offer online…
Q: A data warehousing information system architecture may include a range of components. To be exact,…
A: Justification: A data warehouse architecture is a technique for establishing the entire architecture…
Q: With a simple illustration, explain the many types of firewalls.
A: Firewall: Firewalls secure a computer network from being hacked, Denial of Service, and other…
Q: Explain the four major elements of a computerized information
A: Hardware Hardware represents the physical components of an information system. Some can be seen or…
Q: ss and security breaches become more likely as a result of troubleshooting?
A: Inadequate endpoint protection: Most businesses have endpoint security, usually in the form of…
Q: Nowadays, the great majority of appliances are integrated with wireless technology as a result of…
A: Introduction: The internet is a vast network of interconnected computers. The worldwide web…
Q: Identify and outline the primary security problems specific to cloud computing, as well as potential…
A: The primary security problems specific to cloud computing as well as potential solutions. Absence…
Q: In this part, discuss the primary properties of the Go-Bank-N and Selective Repeat algorithms.
A: Introduction: Selective Repeat Protocol and Go-Back-N Protocol are both sliding window protocols.…
Q: Your firm's finance director has requested you to describe the various types of network equipment…
A: justification: Your company's finance director has asked you to describe the various sorts of…
Q: In fiber-optic cabling, which fibre is used to shield the inner core and keep the cable from…
A: Introduction: The light-carrying part of the fiber is called the core. The core is surrounded by…
Q: Which of the following is not a classification task? * a) Determining whether a patient has a…
A: d) Predicting house prices in a given area
Q: Separate the functional and non-functional needs of an information system of your choosing, and…
A: information system: The generation, exchange, and dissemination of information created by computers…
Q: What is feature engineering
A: c) The process of transforming raw variables to create new variables
Q: Which of the following is an identity element of the binary operation (*)?
A: parameter 'e' called identity element of binary operation. In multiplication rule e = 1
Q: Why aren't secondary storage devices based on semiconductor memory used?
A: Introduction: Semiconductor memory is not used for secondary storage.
Q: Response time, transaction success rate, and system availability are just a few of the key…
A: Answer True
Q: Implement the function of modulus operator. Don't use the inbuilt function. Programming language:…
A: Required: Implement the function of the modulus operator.Don't use the inbuilt function.Programming…
Q: Using a diagram, describe the OSI Network management in detail.
A: OSI Network Management Model: There are four main models in the OSI Network Management model and…
Q: What is a command-line interpreter (CLI) and how does it work? What is the primary function of a…
A: Dear learner, hope you are doing well , I will try my best to answer this question. Thank You!!
Step by step
Solved in 2 steps with 1 images

- <?php include('../connect.php'); $result = $db->prepare("SELECT * FROM supliers"); $result->bindParam(':userid', $res); $result->execute(); for($i=0; $row = $result->fetch(); $i++){ ?> <option><?php echo $row['suplier_name']; ?></option> <?php } ?> Code not runningI'm building a TPS in Android Studio (TPS). The SQLite Database browser shows my records but not my list view activities.Just the correct answers Please. Thank You! PHP is a server-side program. True False Which is an SQL word but not a Data Definition Language key word? INSERT CREATE ALTER DROP What PHP function will validate if a hashed password is correct? hashedpw() password_hash() hex() password_verify()
- DO NOT COPY FROM OTHER WEBSITES Q. How to create dynamic circular list from this txt file data? txt file: Alyce,Female,33 Autumn,Female,26 Brad,Male,45 Jon,Male,60 Zach,Male,22Given the following PHP command statements (assume correct $dbname, $username, $passowrd vaules). $dbCon = new PDO("mysql:host=localhost;dbname=".$dbName, $username, $password);$sql = 'SELECT productCode, productName, listPrice FROM products';$stmt = $dbCon->prepare($sql);$stmt->execute();while ($row = $stmt->fetch()){ echo $row[0] . " | " . $row[1] . " | " . $row[2] . "<br/>";} What value is in $row[1]?https://www.w3schools.com/sql/trysql.asp?filename=trysql_select_all
- . Change to your home directory. Use the rmdir command to delete the spreadsheets directory. What happens? cd go to home directoryAPI1(candidate, timestamp, precinct) - Given a candidate C, timestamp T andprecinct P, return how many votes did the candidate C have at T or largest timestampT’ smaller than T, in case T does not appear in Penna. Penna table has columns such as: ID, Timestamp, State, Locality, Precinct, Geo, totalvotes, Trump(the number of votes for Trump), Biden(The number of votes for Biden), filestampFork the data sharing repository here: https://github.com/jtleek/datasharing Copy and paste the link to the forked repository on your Github account.
- 190. Which of the following is written for getting help in GDB? a. he b. h c. assist d. assistantLearn how to restore lost data from this article.1.Create a script file (mysqlbackup.sh)that when executed will conduct a mysql backup 1.Save the script file in Ubuntu’s Home Directory 2.Database name mysql 3.backup_mysql.sql (name of mysql backup) 2.Schedule a job that will run at 11:00pm every Sunday and execute the mysql backup 3.Schedule a job that will run Monthly and execute the following commands: 1.apt-get update –y 2.service apache2 restart 4.At 7:45pm schedule a job to run that will conduct the following: 1.Create a new directory called ‘Backup’ in azureuser’s home directory 2.Move the mysql backup script file inside the ‘Backup’ folder 5.Verify that all jobs will run correctly

