Ee in tegem
Q: Make a program in c++ that will input the 10 numbers and determine the average, and display all…
A: I have provided C++ CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOT----------------
Q: Describe the six most important aspects that should be included in a tool to aid in the management…
A: Change Management Change Management is an IT Services Management (ITSM) technique that assures the…
Q: urses / To control television, which of the following wireless connections is used? Bluetooth
A: Option a Infrared
Q: Convert the following numbers to decimal: a) 623(16) b) 525(8)
A: Steps: Hexadecimal to decimal: Sum up each digit multiplied by 16 raise to the power number from 0…
Q: How can mobile Mapping and DaaS (Data as a Service) implemented in Database system (HR)?
A: Both Mobile mapping and DaaS can be implemented in Database system.
Q: What is the difference between the OSI and TCP/IP models of networking? Use facts and evidence to…
A: The TCP/IP paradigm has four layers: Network access, internet, transport, and application. These…
Q: In Excel, what is the difference between creating a workbook and creating a template for something?
A: MICROSOFT EXCEL: It's a spreadsheet with graphing capabilities, pivot tables, and a macro…
Q: Writes the contents of a file one page at a time, using the command write-page. O a. Less O b. More…
A: Option (a) LESS is the correct option.
Q: What are the responsibilities of the HLR and VLR in GSM networks? What characteristics of mobile IP…
A: Introduction: The GSM network's home location registration (HLR) is a permanent and crucial record.
Q: Inquire about supply chain measures for the core processes?
A: Core Processes: The processes of a company whose goal is to produce things or provide services to…
Q: Identity and access management play what function in today's world?
A: We must explain what identity and access management is and why it is important: Explanation of the…
Q: tures capa
A: Signatures Guarantee: A signature ensure is a sort of approval offered by a bank or other monetary…
Q: What is the dominant operation in this algorithm? 1. Input a positive integer n 2. answer n 3. While…
A: The correct answer is given in the below step with a proper explanation. Explanation for wrong…
Q: Almost all current appliances can now interact wirelessly thanks to technological breakthroughs.…
A: Introduction: Wireless data transfers are used to connect network nodes in Wi-Fi networks. Wireless…
Q: A supernet has first address of 205.16.32.0 and a supernet mask of 255.255.248.0. Prove that…
A: The answer is
Q: Remove all errors from the C++ program given below asap.
A: Thank you _____________ Like ________ __________ #include <bits/stdc++.h> using namespace…
Q: Describe the second chance approach for page replacement within the framework of an LRU…
A: Introduction Algorithm: All piece reference values are set to False (Let it be the size of the…
Q: The following line relates to one of the Program Organization Principles: 99 The use agreement for a…
A: Introduction: This article is intended to serve as a glossary of terms for software development and…
Q: Is it possible to call information security both an art and a science? How does treating security as…
A: The answer is given below.
Q: See whether any penetration testing is going on on the network before proceeding. Is there a worry…
A: Penetration: A penetration test, often called a pen test, is a legitimate simulated cyber attack on…
Q: be adding all the cards
A: public class Card { private String mySuit; private int myValue; public Card(…
Q: What is the name of the port in a modern PC (or server) that connects it to a LAN network? NIC O DAC…
A: The port in a modern PC or server that connects it to a LAN network is:
Q: Problem 1: Using KMaps, find the simplest SOP expression of F= Ew,x,Y,z(0, 1, 6, 7, 8, 9, 14, 15).
A: I have provided answer with brief explanation------------ I have provided hand-written…
Q: Is it more difficult to create Graphical User Interfaces (GUI) using pixel-based coordinates?
A: Graphical User Interfaces (GUI) A graphical user interface (GUI) is a user interface that uses…
Q: In particular, how is the key for encryption sent across the internet?
A: Internet: The Internet is a network of billions of computers and other electronic devices that spans…
Q: In today's emerging nations, wireless networks are critical. In certain regions, wireless technology…
A: Users can talk to each other even when they are moving: because wireless networks don't need wires…
Q: Explain how the DHCP server goes about assigning IP addresses to hosts. Make a list of its…
A: IP Addresses: "Internet Protocol address" is what IP stands for. The Internet Protocol (IP) is a…
Q: Which switch command will turn off the Dynamic Trunking Protocol (DTP)? a. switchport dtp b. data…
A: Option d
Q: Given the below graph, show the minimum spanning tree (starting with node A). A B 1 5 E F D 6. 4 G
A:
Q: h implementing mineswpeer such that the user may uncover squares with mouse clicks and choose the…
A: We play on a square board and we need to tap on the board on the cells which don't have a mine. And…
Q: In particular, how is the key for encryption sent across the internet?
A: Given: In particular, how is the encryption key supplied over the internet? The key for encryption…
Q: #include #include #include #include int count = 0; void *threadfunc(void *arg){ cout<<"Thread…
A: The correct solution is given below with explanation
Q: In what way does it affect you if your data is stolen? What actually occurred, and how did it…
A: Information Secure: Techniques such as passwords, encryption, authentication, and security against…
Q: A Computer o11 the 4 Mbps network is regulated by a token bucket. The bucker is filled at a rate of…
A: Please refer below for your reference: Given: Rate r = 1Mbps Capacity c= 8Mb full rate m= 6Mbps
Q: What role do detection and prevention of intrusions play in network security and cybersecurity?
A: NOTE :- Below i explain the answer in my own words by which you understand it well. Intrusion…
Q: In Excel, what is the difference between creating a workbook and creating a template for something?
A: Introduction: In Excel, what is the difference between creating a workbook and creating a template…
Q: Which kind of organizations stand to benefit the most from cloud computing?
A: Intro Cloud computing is used in health care and financial organizations. Cloud computing simplifies…
Q: When developing a programme, each language has a set of rules that must be properly observed. What…
A: Programming Languages: Despite the fact that there are several programming languages for software…
Q: A network's topology must be specified in five separate ways. Which of the two do you think is the…
A: Introduction: The physical or logical arrangement of a network is referred to as network topology.…
Q: From the perspective of application developers and consumers, compare the three cloud computing…
A: Cloud computing is a newer trend in information technology that utilizes internet-based servers to…
Q: In the IPV4 header, what is the size of the source and destination address fields? O 128 bits O 32…
A: Introduction: Here we are required to explain what is the size of the source and the destination…
Q: en how a primitive data is kept in memory and how a reference data is stored in memory in terms of…
A: In software engineering, primitive data types are a bunch of essential data types from which any…
Q: High Performance Computing Questions/CUDA Programming Given a __global__ function add and a…
A: The two statements given: A _global_ function and a positive integer N, and call is add<<<…
Q: Provide an explanation of what has happened as a consequence of the data breach that was previously…
A: Introduction: A data breach occurs when a hacker gains unauthorized access to and reveals sensitive,…
Q: Why isn't software being developed to replace human translation?
A: Intro For faster results and lower costs, consider machine translation. Run a document via software…
Q: For example, explain how a file-management system may allow several users to modify or create new…
A: Introduction: Explain how a file management system may allow several users to modify or create files…
Q: y officer in pla
A: As we've learned, security should presently not be a secondary issue while executing it," Al…
Q: a of v ne use c
A: PC failure and loss are central questions bringing about pointlessly significant expenses and cost…
Q: Why are health-care websites important? What are the differences between telesurgery and…
A: World Wide Web: The World Wide Web is abbreviated as the Web. The word is widely used on the…
Q: lain what an intrusion dete
A: Introduction: Below an intrusion detection system
6
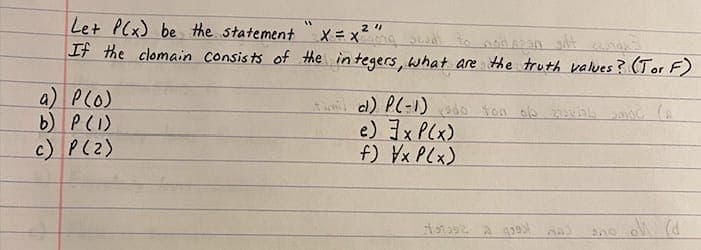
Step by step
Solved in 2 steps with 1 images

- Given f(x)=x2+6x and g(x)=1−x2, find f+g, f−g, fg, and fg. Enclose numerators and denominators in parentheses. For example, (a−b)/(1+n).Consider the following statement: Statement A: ∀ integers m and n, if 2m + n is odd then m and n are both odd. Disprove Statement A. That is, show that Statement A is falseLet :P: Birds can fly.Q: 2+1=4.R: x is an integer.S: π is a rational number. CONSTRUCT THE SENTENCE OF THE FOLLOWING LOGICAL PROPOSITIONS. 1. ~ ((p ⊕ q) ↔ (~r)) →s
- 4. Let N(x) be the statement “x has visited North Dakota,” where the domain consists of the students in your school. Express each of these quantifications in English. a) ∃x N(x) b) ∀x N(x) c) ˺∃x N(x) d) ∃x ˺N(x) e) ˺∀x N(x) f ) ∀x ˺N(x)Let :P: Birds can fly.Q: 2+1=4.R: x is an integer.S: π is a rational number. CONSTRUCT THE SENTENCE OF THE FOLLOWING LOGICAL PROPOSITIONS. 1. ((p→q) ⊕ ~s) → qGiven the universal set of nonzero INTEGERS, determine the truth value of the following statement.
- A prime number is a natural number greater than 1 which is not a product of two smaller natural numbers. Prove or disprove: For every integer q, if q > 7, then q can be written as q = (a + b * c) such that the following properties hold a and b are prime numbers, c is an integer greater than 1.Assume double[][] x = new double[2][5], what are x.length, and x[1].length?Construct a truth table for the given statement. ~q→~p Fill in the truth table. q p ~q ~p ~q→~p T T ▼ Upper TT Upper FF ▼ Upper TT Upper FF ▼ Upper TT Upper FF T F ▼ Upper FF Upper TT ▼ Upper FF Upper TT ▼ Upper TT Upper FF F T ▼ Upper TT Upper FF ▼ Upper TT Upper FF ▼ Upper FF Upper TT F F ▼ Upper TT Upper FF ▼ Upper TT Upper FF ▼ Upper FF Upper TT
- 1. Which of the following statements are true? (a) |N|=|Z| (b) |N|<|Z| (c) |Z|=א0 (d) |R|>|Z| 2. Which of the following statements are tautologies? (a) P → Q (b) P ∧ ¬P (c) P ∨ ¬P (d) P → P 3. The contrapositive equivalency of ¬Q → P is given by: (a) P → Q (b) Q → P (c) ¬P → Q (d) ¬Q→PLet Σ = {a, b}. Indicate whether or not L is regular and prove your answer. (i) L={w ∈ {a, b}* : w contains at least two a’s and at most three b’s}. (ii) L={a^ib^j : i, j ≥ 0 and i < j.}.Let S = {x | x = 3n, n ∈ Z+}. Which of the following expression(s) is/are true?a. 3 ∈ S b. 3 + 6 ∈ S c. ∅ ⊂ S d. S ⊆ S e. 1 ∈ S

