eed answer quick and,
Q: 2. What is embedded SQL? What are its advantages?
A: SQL stands for Structured Query Language.
Q: 2. What is a data model? List the types of data model used.
A: An integrated set of concepts that may be used to describe and manipulate data, as well as…
Q: addresses references (provided as decimal numbers). Show all calculations steps.
A: The answer is
Q: Problem 5. Remove the node with key '12' from the following red-black tree 3 4 5 7 6 8 10 11 12…
A: Red- Black Tree:- A type of self-balancing binary search tree known as a "red-black tree" has one…
Q: Why is the implementation of a Software-Defined Network (SDN) crucial for schools? You must do it…
A: The solution to the given question is: SDN is a software defined network. As the name suggests , it…
Q: 2. What is a data model? List the types of data nodel used.
A: Introduction: Data Model: The term "data model" refers to the notion used when modeling the data…
Q: to you is 192.168.10.0/25. Network A has 50 pcs and network B has 20 pcs
A: The answer is
Q: Please use just your own words to describe Linux and some of its features. Please provide additional…
A: Definition: Here, it is important to ascertain this. Ubuntu outperforms other well-known Linux…
Q: Could you name a Linux package management system that you now use or would consider using in the…
A: Introduction: Software updates from specified Linux repositories (repos) may be installed, updated,…
Q: How does an application resume after the completion of an interrupt service procedure?
A: Method through which the execution of an application programme is resumed: IRET, which stands for…
Q: Question: You are given an integer array coins representing coins of different denominations and an…
A: C Programming which refers to the object oriented programming languages and it is used to create the…
Q: What precisely is Booth's algorithm's goal?
A: the objectives of Booth's algorithm The number of calculations required to multiply signed two's…
Q: Given two hex values 07H and 05H, write an 8085 program to multiply the given hex numbers and store…
A: Given two hex values 07H and 05H, write an 8085 program to multiply the given hex numbers and store…
Q: What about the von Neumann architecture, in your view, distinguished it from the competition?
A: Von Neumann Architecture is among one of the digital computer architectures.
Q: Who has the power to choose when and how data should be used inside an organization?
A: Answer:
Q: ✓ Allowed languages с Problem Statement Write a C Program that determine the number of upper case…
A: ALGORITHM:- 1. Take input for the number of test cases and then each time take input for the string.…
Q: Why is Switch more intelligent than Hub? Separate the services that need a connection from those…
A: Switch and hub link networks. Both devices use the OSI model. Switch works at data connection layer,…
Q: What is the difference between global policy and local rules when it comes to the protection of…
A: Here is the answer below:-
Q: Using Python language implement Greedy Algorithm for the following graph to find the shortest path…
A: To resolve this issue:
Q: Write a program, which uses a selection structure (if/else) to calculate and print the student…
A: Required language is C#:
Q: What role does the remote interface play in the RMI implementation process? Which conditions must be…
A: A remote interface is required for RMI implementation, which consists of: When dealing with RMI, a…
Q: Write a function that does the following for the given values: add, subtract, divide and multiply.…
A: Write a function that does the following for the given values: add, subtract, divide and multiply.…
Q: 2. What is a data model? List the types of data model used.
A: A data model is a conceptual representation of data objects and the relationships between them. Data…
Q: What distinguishes cloud computing from grid computing, and how can you decide which to use?
A: Introduction; The term "cloud computing" refers to a kind of computing where data is kept on a…
Q: Model-View-Controller aid in the organization of web applications? What advantages do…
A:
Q: What signs point to a software project's impending failure? Why do I have to elaborate?
A: What signs point to a software projects impending failure Warning Sign 1: Unclear or Unrealistic…
Q: Give examples of how the four Ps of effective software project management are used.
A: The four P's are what make good project management for software rely on: People Product Process…
Q: 2. What is a data model? List the types of data model used.
A: A simple abstract representation in the shape of a data model is typically graphical and contains…
Q: Give the names of three IGPs (internal gateway protocols).
A: IGPs, or interior gateway protocols The protocols used inside independent systems are known as IGPs.…
Q: re the ACID proper
A: Solution - In the given question, we have to specify what are the ACID properties.
Q: What connection does a microkernel design have between system services and user applications? Would…
A: Kernel : A kernel is an important segment of an operating system that is handle system…
Q: (d) sum = 0; for (i = 0; i < n; for(j = ++i) 0; j < i; ++j ) ++sum; (e) sum = 0; for(i= = 0; i < n;…
A: d) Ans:- sum=0 for(i=0; i<n; ++i) for(j=0; j<i; ++j) ++sum; Describe the…
Q: ding an e
A: Supervised machine learning - The use of labelled datasets distinguishes the machine learning…
Q: Give examples of peer-to-peer architectural features.
A: A peer-to-peer network is designed around the notion of equal peer nodes simultaneously functioning…
Q: Write a function that does the following for the given values: add, subtract, divide and multiply.…
A: Algorithm - This problem will be solved by switch case in java programming Logic - switch (op) {…
Q: Can you explain the lines: out_str += chr((ord(c) + key-97) + 97) else:…
A: There is one python program given, out_str += chr((ord(c) + key-97) + 97) else:…
Q: What modifications to a computer network system are possible to prevent virus infection?
A:
Q: Problem Statement Write a C Program that will compute for the product of two complex numbers.
A:
Q: Write a function that does the following for the given values: add, subtract, divide and multiply.…
A: In this question we need to write a program to perform arithmetic operation on two integers…
Q: Regarding cloud computing What elements are necessary for SLA management?
A: SLA: (Service Level Agreement): A service level agreement is a settlement among service providers or…
Q: Describe the purpose and operation of social networking, online discussion groups, chat rooms,…
A: Social networking : With the help of social networking, people may interact with their friends,…
Q: What is meant by "overflow" when referring to unsigned integers.
A: Unsigned Integers are integers or whole numbers. These are the integers which doesn't have…
Q: Step 2 Below the tablet media query, add a new comment with the text, Media Query for Desktop…
A: Here we have given solution for the 6 given tasks. you can find the solution in step 2.
Q: Mr. SK is a new salesforce employee who is now taking LWC classes to improve his abilities as a…
A: Definition: Lightning web components employ a reactive wire service to access Salesforce data. To…
Q: The precise expectations for the software development project must be understood.
A: Introduction: Project deliverables are any physical or intangible outputs that are submitted as part…
Q: Watson stands apart from other computers thanks to its capacity for learning.
A: Capacity for learning: I refer to your brain's physical makeup, which includes all of the neural…
Q: Provide examples of Interrupt and Trap, as well as their distinctions.
A: Traps:- They are raised by the user program to invoke a functionality of the operating system.…
Q: How does the protocol go from one layer of the OSI model to another?
A: INTRODUCTION: Protocol: The most popular definition of the protocol is "a set of rules that describe…
Q: What elements may cause a virus to propagate over the computer network of a company?
A: Virus stands for Vital Information Resources Under Siege. Virus is a software program, it causes…
Q: A small company needs an interactive program to compute an employee’s paycheck. The payroll clerk…
A: pseudo code The term "pseudo code" is frequently utilized in algorithm-based professions like as…
I need answer quick and,
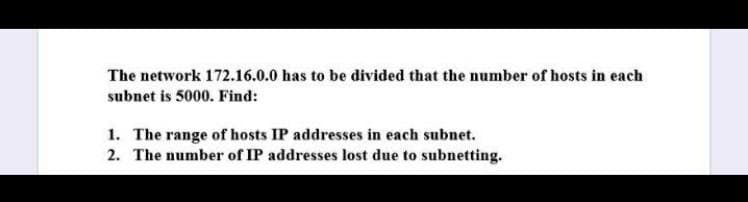
Step by step
Solved in 3 steps with 3 images

- In a class A subnet, we know the IP address of one of the hosts and the subnet mask as given below: IP Address: 25.34.12.56 Subnet mask: 255.255.0.0 What is the first address (subnet address)? What is the last address?Q7. Suppose we have the following IP addresses for two different organizations, we have to create 5 networks having 30 hosts in it. Find first sub network ID, Fist address, Last address and Braodcast for each of the following given addresses.a. 17.23.120.8b. 252.5.15.111Suppose you have been given this classful IP address 130.1.1.8. You want to create a network of 1024 (assignable) IP addresses, what will be the length of network and host part?
- Let’s consider you have a Class C IP address 204.15.5.0/24. You have to determine whether it is possible to createfollowing network with the given IP address? If yes, what could be the possible ranges of IP addresses for thesubnetworks? Let’s consider the above network. If you are using VLSM /CIDR, determine what subnet mask numbers allow therequired number of hosts.Suppose a user has a webserver running at a machine with the name nadir.edu.net.pk and IP address 10.10.10.10. The authoritative DNS address for this web server is with the name dns.nadir.edu.net.pk and with IP address 11.11.11.11. Write all the steps involved in retrieving the IP address of nadir.edu.net.pkQ2 Using this IP address 150.150.55.20 solve the following questions- Which Class this IP related to?- Suppose you use the following subnet mask 255.255.252.0 ,What is the number of hosts exist within a subnet?- What should you do to make each subnet have at least 200 hosts?
- Take the Class A address 10.0.0.0 and answer the following questions by typing those answers at the end of each question: What is the default subnet mask of a Class A IPv4 address? What is the first usable IP address of this “not-subnetted” network? What is the last usable IP address of this “not-subnetted” network? What is the broadcast address of this “not-subnetted” network? How many total hosts are allowed on this “not-subnetted” network? Let’s split this network into 4 subnets What is the new subnet mask? What is the first subnet address of your newly subnetted address? What is the first usable IP address of your newly subnetted address? What is the last usable IP address of your newly subnetted address? What is the broadcast address of your newly subnetted address? How many usable hosts on this subnet? Fill in the following information for the second, third, and fourth new subnets: Network (subnet) address Usable host range BroadcastSuppose a user has a webserver running at a machine with the name www.nadir.edu.net.pk and IP address 10.10.10.10. The authoritative dns address for this web server is with the name dns.nadir.edu.net.pk and with IP address 11.11.11.11. a. Write all the steps involved in inserting this webserver name in the DNS hierarchy. b. Write all the steps involved in retrieving the IP address of www.nadir.edu.net.pkWhat is the purpose of an IP address mask? Suppose an IP address is identified as 200.60.40.88/24. What is the network address in this case? What is the host address? How many hosts can this network address support? Repeat this exercise for the IP address 222.66.44.80/26.
- Assume that Computer A, which is connected through an Ethernet cable to the Switch S1, is just powered on. The user opens a browser and then types a website address to receive the website from the Server (as shown in Figure 1). Write down all the important protocols that come into play by the time the first frame containing HTTP request reaches R1. (Note: Before HTTP frame, other frames have already been sent by other protocol(s).) Write down all the protocols with reference to the TCP Model as follows? Application Layer: Transport Layer: Internet Layer: Link Layer:Let’s consider you have a Class C IP address 204.15.5.0/24. You have to determine whether it is possible to createfollowing network with the given IP address? If yes, what could be the possible ranges of IP addresses for thesubnetworks?Find the class of the following two IP addresses (both are classful addresses),as well as their netid and hostid: a. 104.37.3.6 b. 208.34.54.12

