electoral office Booth details PC VOTER Register electoral details letter Mail ID, password electoral details REGISTER DB ID, password, DOB, vote out Generate password start PC VOTING AGENCY winner Count election counts valid votes Validate ELECTION DB vote Which of the following guidelines would apply when drawing in the trust boundaries on this DFD? Select all ti If your system reads data from a database, place a trust boundary between the system and the database
electoral office Booth details PC VOTER Register electoral details letter Mail ID, password electoral details REGISTER DB ID, password, DOB, vote out Generate password start PC VOTING AGENCY winner Count election counts valid votes Validate ELECTION DB vote Which of the following guidelines would apply when drawing in the trust boundaries on this DFD? Select all ti If your system reads data from a database, place a trust boundary between the system and the database
Computer Networking: A Top-Down Approach (7th Edition)
7th Edition
ISBN:9780133594140
Author:James Kurose, Keith Ross
Publisher:James Kurose, Keith Ross
Chapter1: Computer Networks And The Internet
Section: Chapter Questions
Problem R1RQ: What is the difference between a host and an end system? List several different types of end...
Related questions
Question
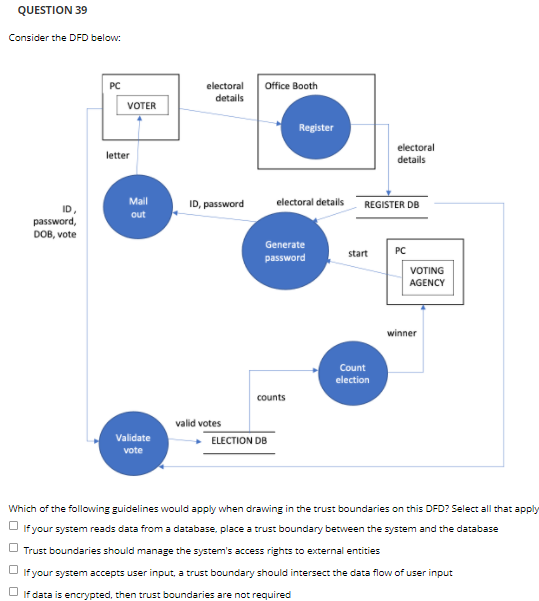
Transcribed Image Text:QUESTION 39
Consider the DFD below:
electoral
details
PC
Office Booth
VOTER
Register
electoral
letter
details
Mail
ID, password
electoral details
REGISTER DB
ID,
password,
DOB, vote
out
Generate
start
PC
password
VOTING
AGENCY
winner
Count
election
counts
valid votes
Validate
ELECTION DB
vote
Which of the following guidelines would apply when drawing in the trust boundaries on this DFD? Select all that apply
If your system reads data from a database, place a trust boundary between the system and the database
Trust boundaries should manage the system's access rights to external entities
If your system accepts user input, a trust boundary should intersect the data flow of user input
O If data is encrypted, then trust boundaries are not required
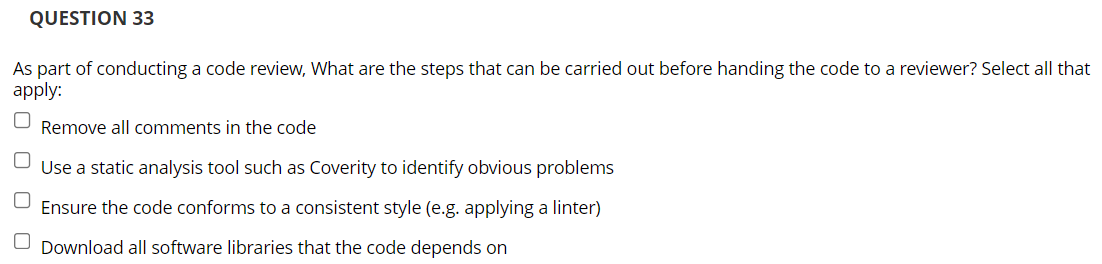
Transcribed Image Text:QUESTION 33
As part of conducting a code review, What are the steps that can be carried out before handing the code to a reviewer? Select all that
apply:
Remove all comments in the code
Use a static analysis tool such as Coverity to identify obvious problems
Ensure the code conforms to a consistent style (e.g. applying a linter)
O Download all software libraries that the code depends on
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Recommended textbooks for you

Computer Networking: A Top-Down Approach (7th Edi…
Computer Engineering
ISBN:
9780133594140
Author:
James Kurose, Keith Ross
Publisher:
PEARSON

Computer Organization and Design MIPS Edition, Fi…
Computer Engineering
ISBN:
9780124077263
Author:
David A. Patterson, John L. Hennessy
Publisher:
Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:
9781337569330
Author:
Jill West, Tamara Dean, Jean Andrews
Publisher:
Cengage Learning

Computer Networking: A Top-Down Approach (7th Edi…
Computer Engineering
ISBN:
9780133594140
Author:
James Kurose, Keith Ross
Publisher:
PEARSON

Computer Organization and Design MIPS Edition, Fi…
Computer Engineering
ISBN:
9780124077263
Author:
David A. Patterson, John L. Hennessy
Publisher:
Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:
9781337569330
Author:
Jill West, Tamara Dean, Jean Andrews
Publisher:
Cengage Learning

Concepts of Database Management
Computer Engineering
ISBN:
9781337093422
Author:
Joy L. Starks, Philip J. Pratt, Mary Z. Last
Publisher:
Cengage Learning

Prelude to Programming
Computer Engineering
ISBN:
9780133750423
Author:
VENIT, Stewart
Publisher:
Pearson Education

Sc Business Data Communications and Networking, T…
Computer Engineering
ISBN:
9781119368830
Author:
FITZGERALD
Publisher:
WILEY