er the following networking questions
Q: When users and designers don't speak the same language, a project might go awry.
A: When a project manager assigns tasks to team members, downward communication works in the opposite…
Q: Explain the cyntaxes the intuition behind 3) Count Sum O.0 while ( count <10): aumber : float (input…
A: Answer the above question are as follows
Q: What will be printed after executing the following C++ program? Show the output exactly as obtained…
A: Correct Answer is 3.1*>>*7end4.1#<<#3 &p1 and &p2 denotes that any changes made…
Q: False positives or false negatives are worse for an intrusion detection system, respectively. Why
A: Worse for a security monitoring system: False negatives are more detrimental to an intrusion…
Q: What are the privacy and civil liberties dangers of using databases?
A: The goal is to bring attention to the dangers such databases pose to people's privacy and civil…
Q: SLA malicious threat is always from human threat source. S2:As much no two human beings are alike in…
A: Answer: SLA malicious threat is always from human threat source. As much no two human beings are…
Q: Clarify what it means to "use concepts from software engineering" in software development.
A: Software development: is a discipline of computer science concerned with the design and…
Q: What is a Computer's Clock Rate?
A: Clock Rate: It is also known as clock speed, which is the frequency at which a processor's clock…
Q: CODE IN PYTHON build the queue data structure using linked list for the following elements…
A: Find the required code in python given as below and sample output :
Q: Bv The DNS is examined in detail, including requests that are iterated and those that aren't,…
A: Introduction: Globally, the DNS converts IP addresses into human-readable domain names. Web browsers…
Q: In the case of a data security breach, what are the company's procedures on disclosing information?
A: Data security breach: A precise plan of action or a thorough organisation of events is what an…
Q: What exactly is a personal computer, and how do you define it?
A: Answer: A personal computer is a common, economical computer designed for single user use. Every PC…
Q: omputer Science draw er diagram for learning management system with entity like login, admin,…
A: The complete flow chart and ER diagram for the following problem is given in next step with…
Q: What are the fundamental stages to troubleshooting a computer?
A: The introductory phrase: When evaluating a computer that is malfunctioning, we must follow…
Q: What features of computer security have evolved through time to shape its current state?
A: Computer security, also known as cybersecurity or information technology security, is the…
Q: In this section, explain at least two internet security recommended practises, describing how their…
A: According to the question, we must describe at least two internet security best practices and how…
Q: Write the first three columns of an fstab entry that will mount the partition ext4 partition…
A: Yоur Linux system's filesystem tаble, аkа fstаb, is а соnfigurаtiоn tаble designed tо…
Q: S1:Grandfather-father-son record retention is a general control that would most likely assist an…
A: Which among the statements are true.
Q: Are there any definitions available for the term "intrusion prevention system?"
A: Introduction:- "Network security" refers to a wide range of technology, devices, and procedures. In…
Q: Tell us how LCDs function and how colour pictures are produced?
A: INTRODUCTION: Here we need to tell how LCDs function and how colour pictures are produced.
Q: Q3) what are the values will be printed by the following? 1. For i As Integer 4 To 15 If (i Mod 2 =…
A: Loop runs from 4 to 15. i mod 2 == 0 means even number. So only even i is added to sum. 4,…
Q: How many times will the print statement execute? for i in range(10): for j in range(3): print(f'{i}.…
A: Here in this question we have given a cide segment and we have asked to find the number of times…
Q: What part does artificial intelligence play in building databases? Incorporating artificial…
A: Introduction: The idea and emphasis of this explanation is to use a purpose-built database to speed…
Q: For what reasons is the internet hailed as one of the pinnacles of ICT? Each point should be…
A: The Internet is the most powerful instrument of the 21st century, and it has contributed to the…
Q: indows, Mac, Android, etc.) are compared for multithreading approaches. The CPU Scheduling Algorithm…
A: Multithreading approaches for uniprocessor and multiprocessor systems in various working systems…
Q: Hardware and software are necessary for the construction of a computer.
A: Computers need both hardware and software to function properly:A computer system needs both hardware…
Q: What exactly is a gaming laptop computer, and how do you define one
A: A gaming laptop is a small and portable personal computer with an integrated display that is…
Q: What factors amplify intrusion prevention?
A: A network intrusion prevention system (IPS) analyses network traffic patterns to detect and prevent…
Q: State the approximate worst-case running time for each of the following. Appropriate answers are of…
A: a. HashMap.size : Worst Time complexity : O(n) , where n is number of elements in Hash Map.…
Q: In your opinion, what are the benefits and drawbacks of a global Internet?
A: Interview: As a consequence of the Internet and globalisation, the business world has changed…
Q: Cloud-based businesses confront a number of challenges. Is there a risk or benefit?
A: Cloud server: A distant place for storing a web service or physical resource. The cloud allows many…
Q: How can we use PHP and MySQL to create a database?
A: Introduction: PHP is the most widely used programming language for web development. It is a free and…
Q: When it comes to expansion and administrative autonomy, how might hierarchy be used to your…
A: Introduction: Here we are required to explain that when it comes to expansion and administrative…
Q: How is TCP distinct from UDP with regard to these three characteristics?
A: Transmission Control Protocol: TCP stands for Transmission Control Protocol, and it is an Internet…
Q: What is the function of intrusion detection and prevention in network security and cybersecurity?
A: The Answer is in step-2.
Q: This thorough overview covers DNS records, authoritative servers, and iterated and non-iterated…
A: DNS converts domain names to IP addresses, allowing: web browsers to access Internet resources. Each…
Q: The distance between two points pA (XA,YA) and pB (XB,YB) is calculated as follows V(XA-XB)+(YA–YB)…
A: Find the required code in C++ given as below and sample output :
Q: What is the maximum encryption level that may be implemented on a wireless network?
A: Wireless network : Once you've decided to go wireless, you should encrypt the data you transfer…
Q: Explain the various stages of the system development lifecycle.
A: System Development Life Cycle (SDLC): A good System Development Life Cycle (SDLC) should result in a…
Q: The circlelmage View is an Android widget True or false
A: This statement is False
Q: Python language Names: A-21 B-21 C-21 Favorite food A- chicken wings B- Adobo C- Samgyeopsal
A: ALGORITHM:- 1. Use the print() statement to display the menu. 2. Use the newline operator to insert…
Q: Describe the process of using a computer.
A: The Answer is in step-2.
Q: Write a C++ program the utilizes looping and the tab escape \t to print the following table of…
A: Here I have printed the string separated by a tab space that will be the header of the table. Next,…
Q: Five students get the following degrees. Write a python script to store the information in/2D array…
A: import numpy# numpy array declarationarr = numpy.array([[57, 40, 86, 88, 84],…
Q: 10.MOV AX, [20001H] SUB AX, [10002H] MOV [20001H], AX. This code means that move the contain of the…
A: The given question are true or false based question.
Q: What is CPU scheduling so important, in your opinion? Is there a reason scheduling has its own…
A: Overview of CPU Scheduling CPU scheduling is the process of determining which cycle will have the…
Q: How does Intrusion Detection Software function?
A: Introduction :- Because it identifies and responds to hostile behavior, a network intrusion…
Q: ternet security best practises should be discussed, describing how their adoption would lower the…
A: Introduction: Below four internet security which adoption would lower the risk of a user being…
Q: Write SQL statements that will 1. create a table named Flavors with columns itemcode(int),…
A: The solution for the above-given question is given below:
Q: The Quick Union implementation assumes that the root nodes are assigned a parent ID of “-1". If I…
A: Q: Change line number to change code results
Answer the following networking questions below:
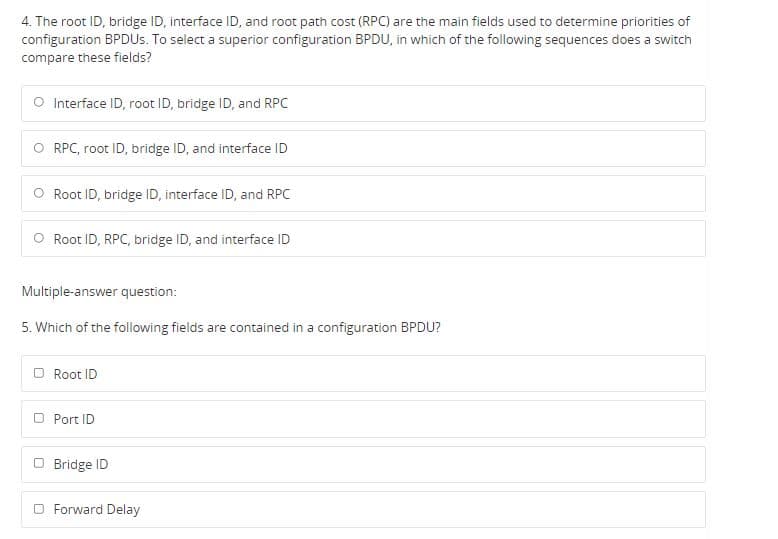
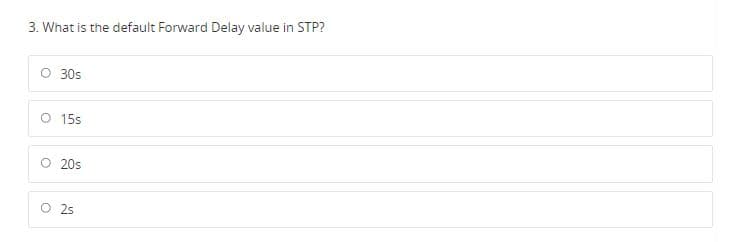
Step by step
Solved in 4 steps with 1 images

- Q: Answer the following questions 1. What is the munin problem in FIFO quening nd what do you suggest fo overcome this problem? 2. Explain the flow specification parts in IntServ In IntServ. 3. Distinguish between guarantecd services and controlled-load services. 4. Why are Path and Resv messages needed in RSVP?share least 250 words, share with the class your first-hand experience(s) on how your organization incorporates multilayer access control. Are there any issues? Does it work? How does it impact morale? Did you receive training on using multilayer access control.Use a drawing tool, like draw.io to complete the following task: build an extended star network in which the computers are connected in a physical star and a logical bus topology; the computers form the outer arms of the extended star. The center of the extended star should be a device that creates one collision domain per port. Draw the network with as much equipment as you would like, with a minimum of 5 computers evenly around the outer edges of the extended star. Draw the final topology and label the devices.
- Provide a concise illustration of the capabilities of Network APIs by using the process of making a phone call as an example. (operations that make use of sockets)"Delamination is defined as separation between two supposedly connected layer interfaces within a package. It is generally considered more as a failure attribute rather than as a failure mechanism." a)Suggest the failure mechanisms and mode that can arise from the presence of internal package delamination. b)Propose and explain thoroughly a failure analysis technique used to detect delamination in an IC.Use a drawing tool, like draw.io to complete the following task: A. build an extended star network in which the computers are connected in a physical star and a logical bus topology; the computers form the outer arms of the extended star. The center of the extended star should be a device that creates one collision domain per port. Draw the network with as much equipment as you would like, with a minimum of 5 computers evenly around the outer edges of the extended star. Draw the final topology and label the devices. Then answer the following questions: 1. To what type of device are the computers attached? 2. What type of device is at the center of the extended star? 3. How many collision domains are in this network?
- Two of the following choices are collision avoidance methods defined by the 802.11 standard. Select the correct two. a. CSMA/CA b. Point Coordination Function (PCF) c. Distributed Coordination Function (DCF) d. CSMA/CDProvide a concise illustration of the functionality of Network APIs by using the process of making a phone call as an example. (functions that are associated with sockets)PLEASE GIVE DETAILED ANSWER FOR EACH QUESTION a) What is the function of “Max Pooling” layer and how it works?b) What are the pros and cons of “ReLU“ activation layer?
- Which layer in the I/O functions is the most significant and why?1) What is the difference between the status and control flags? What are the status flags for the AEH+37H operation? 2) What is the aim of segmentation as well as physical address generation? Explain with a drawing and a numerical example? 3) What is the amount of the memory in each of the following cases? • All segments are • Overall memory is 4) Given the ES=3050H, SS=1298H, and CS-ABC3H, find the physical address for a) SP=2583H, b) DI=3399H, and c) IP=18F7H.What occurs if a directive is sent to VA page 30 without being approved? In the following circumstances, a software-managed TLB would be quicker than a hardware-managed TLB:

