erage seek tim 60 rpm (round sk has 512
Q: What are the advantages of using metrics in software development
A: Answer:
Q: this cod >>7*DThe .----((6&1) result of executing + (~0.00) +(0&5)); is 7 Ο Ο Ο Ο Ο Ο 49 48 error…
A: Find the required with explanation given as below :
Q: Using the Boolean Algebra laws, prove that: (WX(Y+XZ) + WX )YZ = YZ
A: Answer: Answer of the given problem is provide in step 2 Truth Tables for the Laws of Boolean
Q: 4. Write a Matlab program to compute the value of 30*10 without using the operator. Attach the…
A:
Q: What is a model in the context of System Analysis? Use logic and physical models to distinguish…
A: In system analysis, the design, definition, and analysis of a model may be used to relate particular…
Q: File extensions and the applications that create them are the subjects of this article. It's…
A: File Extension Explanation: The nature of a file may be ascertained by a computer by inspecting its…
Q: An index may speed up queries, but it's usually a terrible idea to create an index for every…
A: Index: Increasing the number of indexes in a database may significantly boost the pace at which…
Q: Describe the differences between for services in cloud
A: The complete solution is given below:-
Q: On Assignment 4 you were tasked with taking a bunch of spaghetti code and changing it to nice code…
A: Please refer beloe for your reference: Language used is C:
Q: When and what applications are responsible for the creation of a file extension? Give examples of…
A: File extension: An identifier used as a suffix to a name of a computer file in an operating system…
Q: Write a C++ program to print the text "C++ Programming." in the output along with the quotes.…
A: Coded using C++.
Q: What is the concept of an infrastructure-based wireless network? Other than infrastructure, what…
A: When operating in infrastructure mode, each wireless host is connected to the remainder of the…
Q: Given the following PDA a, $a$ b, a → a b, a → € $ start A B b, a → a a, a → aa Which of the…
A: Answer the above question are as follows
Q: the following protocol used to Synchronous serial interface Select one or more: O 0 O O 0 a.…
A: Answer: Introduction: SSI stands for a synchronous serial interface which is a point-to-point…
Q: Based on "Why computers are so powerful," incorporate the four qualities of a computer into today's…
A: Introduction: In the modern educational system, a computer must possess all four of the following…
Q: Identify the infix expression from the list of options given below. a) a/b+(c-d) b)…
A: According to the question below the solution
Q: If you've ever worked on a commercial software system, describe in as few words as possible the…
A: Software testers must pay close attention to the minor details to do the assignment successfully.…
Q: From the outside, what can be done to address the problem of fragmentation?
A: Given: When the overall amount of empty memory space is insufficient to meet all of the allocation…
Q: Evaluate the following infix expression using algorithm and choose the correct answer. a+b*c-d/e^f…
A: The answer is given in the below step
Q: There is a reason for this: computers have become so powerful. How can we establish that computers…
A: Computers: Computers have been reliable ever since they were first developed, but today they are…
Q: Write a java program in Java to display the multiplication table of a given integer.
A: import java.io.*; public class Main { public static void main(String[] args) { try{…
Q: Access to shared memory is simplified in multiprocessor systems. Clusters and grids don't have…
A: Answer: The server creates a shared memory map in its address field and regains access to sync…
Q: What are some examples of cloud collaboration apps? Workplace collaboration is facilitated thanks to…
A: INTRODUCTION: Using cloud-based documents, staff can collaborate in a team environment on tasks.
Q: I need instructions for my replit game but I don’t know how to do it ( the game is tic tac toe) user…
A: The algorithms used in java for the tic tac toe are given below: Whenever you want to make a move…
Q: What are the essential components of an organization’s IS infrastructure?
A: The complete solution is given below:-
Q: What are the best ways to ensure the long-term viability and availability of a local area network?
A: Given: In order to get a complete understanding of resilience, it is necessary to first dissect it…
Q: What are the benchmarks for software maintenance?
A: What is benchmarking? Benchmarking is a process of evaluating a company’s performance by comparing…
Q: 2.) Simplify the following Boolean equation into the simplest sum of products form using Boolean…
A: Answer the above questions are as follows
Q: Should the security needs of society, the owners of the information system, and the users of the…
A: Given: It safeguards the company's operations. It ensures the safety of IT applications. It…
Q: How array of strings can be represented in main memory? Compare and contrast between different…
A: C programming is an object oriented programming languages. It is very useful to fix the problems to…
Q: Define issue resolution rate.
A: Lets see the solution.
Q: The following instruction is used for: GPIO PORTA_DIR_R&= -0x20; Select one:
A: "&=" specify input If there is "|=" instead of "&=" . It means direction output . The I/O…
Q: Dissect the system's growth, giving special attention to the influential people and events that…
A: Information system: Discuss the evolution of information systems while focusing on the significant…
Q: What types of worries and challenges are brought up by the use of an information system that is not…
A: Computer failure and loss are significant computer difficulties that lead to excessively high…
Q: Problem 1 Draw the following binary tree. Where only the key is shown (disregard 2xDOB or 3xMOB if…
A: “Since you have posted a question with multiple sub-parts, we will solve first three subparts for…
Q: What is the difference between reloading a service and restarting it
A: Difference between Reloading and restarting service of linux are as following:
Q: : Complete the following phone conversation. A: Good morning. The British Tourist Authority. B:…
A: Here it is English conversation we can fill in different words but correct match and phrase is very…
Q: Examine the evolution of the internet and its underlying technology.
A: The Answer is given below step.
Q: Describe the internet of things in your own words. This distinction is what separates these two…
A: The Internet of Things is described by computer technology as the notion of linking ordinary things…
Q: You need to know in code how to tell if you've picked a RadioButton or a CheckBox control.
A: In code, use a CheckBox or a Radio Button control: Select from the following Radio Button and…
Q: True/False Questions (. 1. If the "Primal" objective function is a "maximization" problem, then the…
A:
Q: Use Input to print "< =" and stop the program until the user enters a value and presses the Enter…
A: #include <iostream> using namespace std; int main() { cout<<"Do you want to stop :…
Q: Q2)All the following sentence are incorrect; re-write the sentence alt the underlined phrases: 1-…
A: As per the Bartleby rules, we are answering 3 questions with proper explanation As Question 2…
Q: The system project is a mobile application that monitors children to reduce kidnapping. The system…
A: The system can identify the child’s face and voice through the mobile through artificial…
Q: What is meant by the term virtually unrestricted?
A: Lets see the solution.
Q: * The means if a sample is compressed in one direction it tends to get thicker in the lateral…
A: Answer 1: At the point when an example of material is extended in one course it will in general get…
Q: What is the catastrophe recovery process's principal objective?
A: Please find the answer below :
Q: An explanation of the concept of a system model would be much appreciated. In the process of…
A: Information flows between modules are represented as impacts or flows in the systems model. A…
Q: What do you know about preprocessor directives? Describe any three preprocessing directives with…
A: The answer is
Q: Write a C program to find the range of a set of numbers. Range is the difference between the…
A: Here in this question we have asked to write a program which find the range of a set of…
Step by step
Solved in 3 steps with 3 images

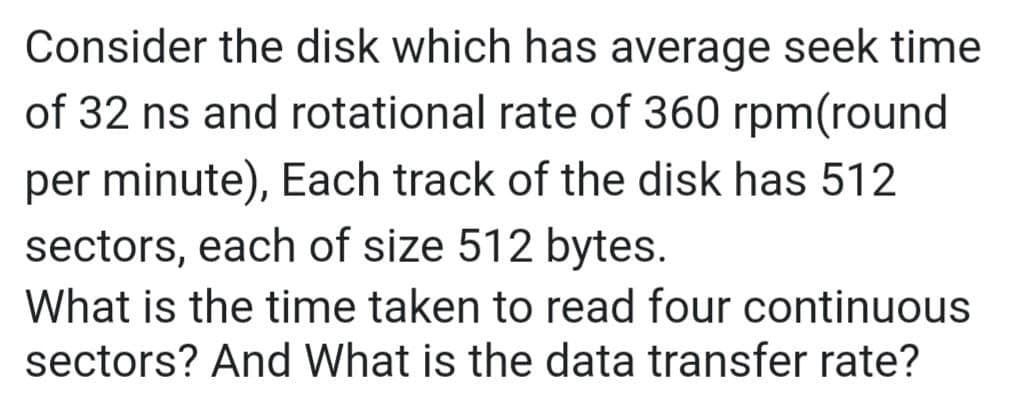
- Consider a disk with an advertised average seek time of 6 ms, rotationspeed of 7,200 rpm, and 512-byte sectors with 500 sectors per track. Suppose that we wish to read a file consisting of 2500 sectors for a total of 1.28 Mbytes. Estimate the total time for the transfer when:Suppose that a disk drive rotates at 8000 RPM. It has an average seek time of 4 milliseconds. If its transfer rate is 15 Mbps, determine the average time it takes for a 15K byte request to be transferred from the time the disk starts the seek? From this, determine its throughput.Consider a disk pack with 16 surfaces, 128 tracks per surface and 256 sectors per track. 512 bytes of data are stored in a bit serial manner in a sector. The capacity of the disk pack and the number of bits required to specify a particular sector in the disk.?
- Consider a disk pack with 32 surfaces, 64 tracks and 512 sectors per pack. 256 bytes of data are stored in a bit serial manner in a sector. The number of bits required to specify a particular sector in the disk is.Suppose that a magnetic disk has an average seek time of 4 ms, a rotation rate of 5400 RPM, a transfer rate of 50 MB/second, a sector size of 512 bytes, and controller overhead of 2 ms. What is the average amount of time to read a single sector?I will upvote . Consider a disk pack with 32 surfaces, 64 tracks and 512 sectors per pack. 256 bytes of data are stored in a bit serial manner in a sector. The number of bits required to specify a particular sector in the disk is
- If the disk is rotating at 3600 rpm, determine the effective data transfer rate which is defined as the number of bytes transferred per second between disk and memory. (Given size of track = 512 bytes).Q] Consider a disk with a sector size of 512 bytes, 2000 tracks per surface, 50 sectorsPer track, five double-sided platters, and average seek time of 10 msec.a) What is the capacity of a track in bytes?b) What is the capacity of each surface?c) What is the capacity of the disk?d) How many cylinders does the disk have?e) Give examples of valid block sizes. Is 256 bytes a valid block size? 2048?51200?f) If the disk platters rotate at 5400 rpm (revolutions per minute), what is theMaximum rotational delay?Suppose we have a computer with the following characteristics: the magnetic disk has an accesslatency of 15 milliseconds and a streaming transfer rate of 5 megabytes per second. For the disk described,what is the effective transfer rate if an average access is followed by a streaming transfer ofa. 1024 bytes
- The outer track 0 of a hard disk has a diameter of 8cm, the innermost track 36113 has a diameter of 4cm. For simplicity, let's assume that the head is moving at a constant speed of 2m/s. The hard disk rotates at 7200 rpm, the reading time of the sectors is negligible. How long does it take to change lanes from lane 0 to lane 36113? Enter the answer in milliseconds without decimal places.Consider a 4 inch disk with 64 double-surfaced platters rotating at 7200 rpm. It has a usable capacity of 16 gigabytes stored on 1024 cylinders. Assume 12% of each track is used as overhead with average seek time 10ms. compute the time required to transfer 8-K byte sectorConsider a single-platter disk with the following parameters: rotation speed: 7200 rpm; number of tracks on one side of platter: 30,000; number of sectors per track: 600; seek time: one ms for every hundred tracks traversed. Let the disk receive a request to access a random sector on a random track and assume the disk head starts at track 0. a. What is the average seek time? b. What is the rotational latency? c. What is the transfer time for a sector? d. What is the total average time to satisfy a request?

