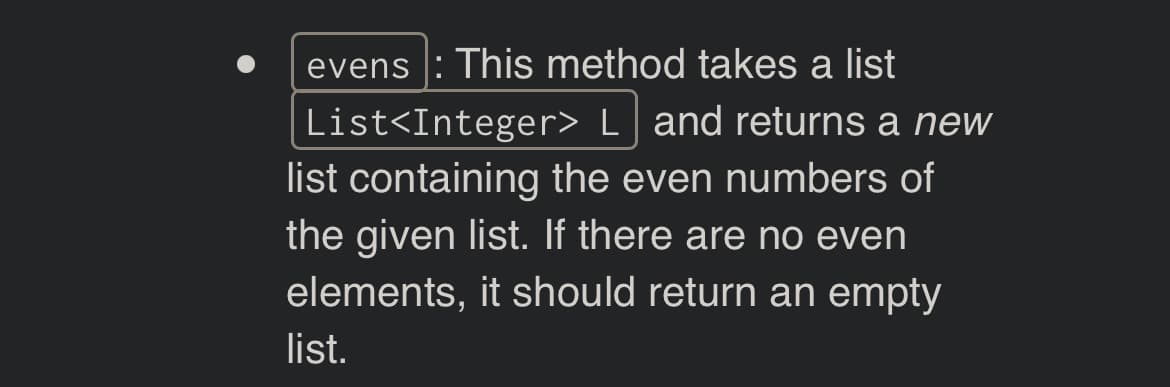
evens: This method takes a list List L and returns a new list containing the even numbers of the given list. If there are no even elements, it should return an empty list.
Q: What does GSM stand for? Tell me about the capabilities of your SIM card.
A: GSM stands for Global System for Mobile communication. A subscriber identity module, or SIM card, is…
Q: When it comes to embedded systems, why are watchdog timers so important?
A: The watchdog timer (WDT), a part of the most basic kind of embedded system, is crucial because it…
Q: Choose WPA2 as your wireless security protocol of choice. How is this alternative better than the…
A: Security Protocol: A security protocol is a set of rules and guidelines that define how users,…
Q: Methodologies for object-oriented design should be structured to prioritize modeling over procedure.…
A: Object-oriented design is a method of design that encompasses the process of object-oriented…
Q: It is helpful to convey non-systems analytical techniques using structured language.
A: Introduction A structured language has a structure that, in addition, to fitting the requirements of…
Q: What do you understand as a network student about the concept of letting users access software or…
A: A remote access process also enables organisations to acquire the greatest talent regardless of…
Q: If you're working on a software project, what are the distinctions between cohesion and coupling?
A: The solution to the given question is: EXPLANATION A module's connectivity is a measure of its…
Q: Is there proof that interrupt-driven OSes outperform their non-interrupted counterparts, or vice…
A: Introduction: The user may better manage their computer by using interruptions. If interrupts aren't…
Q: Which of these describes how an item in a linked data structure is accessed? a.accessed by hashing…
A: Linked data structures are data structures that contain a set of nodes that are connected by edges.…
Q: To what extent does the TPC diverge from the SPEC?
A: Computer performance which refers to the one it is the amount of useful work that a computer system…
Q: Which method of scheduling tasks has been shown to work best in the computer science research?
A: Introduction Scheduling algorithms:Scheduling algorithms are applied to allocate resources among…
Q: Given below is a UML diagram for address class. Address -Street: String -City: String -State: String…
A: The question does not specify any particular programming language for the solution. We have done the…
Q: The 15-puzzle problem The 15-puzzle is a larger version of the 8-puzzle. Goal: 15 14 13 12 11 10 9 8…
A: The 15-puzzle is a classic problem in artificial intelligence and computer science. It is a sliding…
Q: Write a C++ program that reads integers from standard input and keeps a running sum of all the…
A: c++ coding to that reads integers from standard input and keeps a running sum of all the positive…
Q: What would happen if several different processes competed for the same CPU time by setting the same…
A: CPU: A Central Processing Unit (CPU) is the central processing unit of a computer system. It is the…
Q: What effects has the proliferation of the internet had on software systems and software systems…
A: The proliferation of the internet has had a significant impact on software systems and software…
Q: What may possibly cause a resumption of the previously completed instruction in the event of a…
A: The instructions that must be followed make up the software that must be run: Pages that are kept in…
Q: In certain cases, end-to-end encryption may be a problem with application proxies. You are asked to…
A: Introduction: End-to-end encryption is a system of communication where only the communicating users…
Q: Include a thorough list of kernel parts after providing a short explanation of each.
A: Introduction: A computer operating system's kernel is its essential component. It is in charge of…
Q: Operating systems store identical file segments on the same physical disk block. How come using…
A: INTRODUCTION: An operating system, sometimes known as an OS, is a kind of software that, after being…
Q: To what extent have wireless networks improved in security over the last three generations? What…
A: Wireless networks: Wireless networks are computer networks that use wireless data connections…
Q: a. Compute the swing weights associated with each means objective b. Combine the four SDVFs (from #…
A: Use the given hints to find the weights. Use the Single Dimensional Value function to find the value…
Q: The connection between the object-oriented programming paradigm and design patterns has to be…
A: The object-oriented programming paradigm, as well as design patterns, will be discussed: A design…
Q: To put it simply, "yes." Operating systems need to insert consecutive file blocks in the same…
A: Operating System: An operating system (OS) is a group of programs that controls computer…
Q: In this section, we'll go through the testability hint and provide a brief description of the…
A: "Fight the temptation to code"—what does that mean? Software engineers must understand the problem…
Q: In the realm of technology, there is a vast chasm between architecture and computer-based…
A: Introduction of technology: Technology is the application of scientific knowledge for practical…
Q: Test out Java's title, button, and text-based UI components.
A: Examine user-interface components with titles, buttons, and text content. User Interface Elements…
Q: In a distributed system, data is kept in or accessible from a number of different locations. There…
A: Introduction Information may be stored or retrieved from several locations in a distributed system.…
Q: Distinguishing between computer and information literacy may be a nebulous concept to explain.
A: Introduction: Computer literacy is the ability to use computers and related technologies…
Q: Where would you typically look for evidence of a violation of the DRY principle?
A: Given: What are the names for the DRY principle violations? Where do they normally reside?
Q: This is the case because of the rapidly growing processing capabilities of today's computers. How…
A: There are a number of ways to provide evidence for the claim that computers have been increasingly…
Q: While designing the framework, it is important to recognize and assess the complications and…
A: When creating an information system, there are a few challenges that must be solved; they will be…
Q: For analytical methods that do not involve systems, a structured language may be useful.
A: Structured languages are helpful for analytical methods that do not involve systems because they…
Q: When and why should you use a throw statement as opposed to a throws clause?
A: The solution along with the explanation is given below: The throw and throws is the concept of…
Q: Is there a connection between cohesion and coupling and effective software design?
A: The link between modules is represented by cohesion. The coupling shows the modules' relative…
Q: What is the relevance of testing, and can you give me an overview of the compiler?
A: Software development: The process of developing and maintaining computer programs and…
Q: In contrast to architectural design, a computer-based organization is controlled by machines rather…
A: Computer architecture is a functional statement of requirements and design implementation for…
Q: Generally, operating systems will try to keep successive file blocks on the same disk block as the…
A: Given: As a file is read from, operating systems try to maintain subsequent blocks on the same disc…
Q: Throughout this session, we'll talk at length about why architectural design is so crucial in the…
A: Introduction: Architectural design is the process of creating a plan for the structure and…
Q: Operating system functionality is a black box that we cannot describe. When people refer to…
A: An operating system (OS) connects the hardware of a computer to its user. A computer's operating…
Q: Q1. The following figure shows a shipping ticket sent to a customer. Draw an ERD reflecting the data…
A: 1. ERD
Q: Operating systems need to insert consecutive file blocks in the same physical location on the disk.…
A: A magnetic disk is a type of storage device that uses magnetism to store and retrieve digital data.…
Q: Which shortcomings of the Whetstone, Dhrystone, and Linpack benchmarks do the SPEC CPU benchmarks…
A: The Answer is in given below steps
Q: Which of the following are categorized as functional areas in security? (Check all that apply.) O a.…
A: Introduction: A group of security objects defines a Functional Area. Functional Regions are used to…
Q: The area of software engineering suffers from a lack of fundamentals. Explain?
A: EXPLANATION: The area of software engineering is facing a software crisis, which is caused by a…
Q: Write a program named TestsInteractive that prompts a user to enter eight test scores and displays…
A: Algorithm of the code: 1. Start 2. Declare variables test1, test2, test3, test4, test5, test6,…
Q: We will demonstrate how to recognize and prevent malicious malware that spreads itself from being…
A: Introduction: The security policy comes first. At the very least, your security policy should…
Q: Walk me through the steps of a top-down design.
A: Top-down design: Top-down design is a software development approach in which a complex system…
Q: Write a JavaScript including statements for variable declaration and assignment that will calculate…
A: Given data, The requirement is to write a JavaScript including statements for variable declaration…
Q: Discuss the potential operating system challenges posed by simultaneous computer processes.
A: - We need to talk about the challenges of operating system because of simultaneous computer…
Using Java. Import ArrayList
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 1 images

- Suppose that you want an operation for the ADT list that adds an array of items to the end of the list. The header of the method could be as follows: public void addAll( T[ ] items) Write an implementation of this method for the class LinearLinkedListWrite an equals method for the LBList class. Return true if the lists have the same number of elements and the elements in each position of the lists are the same; otherwise return false. DO NOT USE ANY OTHER METHODS OF THE LBLIST CLASS.java program java method: Write a method replace to be included in the class KWLinkedList (for doubly linked list) that accepts two parameters, searchItem and repItem of type E. The method searches for searchItem in the doubly linked list, if found then replace it with repItem and return true. If the searchItem is not found in the doubly linked list, then insert repItem at the end of the linked list and return false. Assume that the list is not empty. You can use ListIterator and its methods to search the searchItem in the list and replace it with repItem if found. Do not call any method of class KWLinkedList to add a new node at the end of the list. Method Heading: public boolean replace(E searchItem, E repItem) Example: searchItem: 15 repItem: 17 List (before method call): 9 10 15 20 4 5 6 List (after method call) : 9 10 17 20 4 5 6
- Java Given main() in the ShoppingList class, define an insertAtEnd() method in the ItemNode class that adds an element to the end of a linked list. DO NOT print the dummy head node. Ex. if the input is: 4 Kale Lettuce Carrots Peanuts where 4 is the number of items to be inserted; Kale, Lettuce, Carrots, Peanuts are the names of the items to be added at the end of the list. The output is: Kale Lettuce Carrots Peanuts Second image is ItemNodeFor the following code, indicate the weighted edge values. List<WeightedEdge> list = new ArrayList<>();list.add(new WeightedEdge(1, 2, 3.5));list.add(new WeightedEdge(2, 3, 4.5));WeightedEdge e = java.util.Collections.max(list);e.u = e.v = e.weight =Creates the initial "grid" of sequences by taking the initial * sequence and taking the difference iteratively until it reaches * a sequence where all the numbers in the sequence are the same. * @param sequence Seed sequence that dictates the other sequences * @return A list of sequences where each subsequent sequence is the difference of the previous one */ private static List initializeGrid(Sequence sequence) { return null; }
- Answer for.Write a Python Code for the given constructor and conditions: Given Constructor: def __init__ (self, a) Pre-condition: Array cannot be empty. Post-condition: This is the default constructor of MyList class. This constructor creates a list from an array..java Write a program that implements the methods of a list using LINKED LISTS. Send source code END(L) PRINT_LIST(L) INSERT(x,p,L) LOCATE(x, L) RECOVER(p,L) DELETE(p, L) NEXT(p,L) PREVIOUS(p,L) DESTROY(L) FIRST(L) EMPTY(L ) * This is a function that returns true if the list is empty and false if the list is not empty. Create a menu with an option for each of the list methods. Validate p(position) between 1 and the size of the list.Given main.py and a PersonNode class, complete the PersonList class by writing find_first() and find_last() methods at the end of the PersonList.py file. The find_first() method should find the first occurrence of an age value in the linked list and return the corresponding node. Similarly, the find_last() method should find the last occurrence of the age value in the linked list and return the corresponding node. For both methods, if the age value is not found, None should be returned. The program will replace the name value of each found node with a new name. Ex. If the input is: Alex 23 Tom 41 Michelle 34 Vicky 23 -1 23 Connor 34 Michela main.py(can not edit) from PersonNode import PersonNodefrom PersonList import PersonList if __name__ == "__main__": person_list = PersonList() # Read input lines until encountering '-1' input_line = input() while input_line != '-1': split_input = input_line.split(' ') name = split_input[0] age =…
- Java programming In the Java programming language, write a method that lists all the elements of the list in reverseorder!JAVA please Given main() in the ShoppingList class, define an insertAtEnd() method in the ItemNode class that adds an element to the end of a linked list. DO NOT print the dummy head node. Ex. if the input is: 4 Kale Lettuce Carrots Peanuts where 4 is the number of items to be inserted; Kale, Lettuce, Carrots, Peanuts are the names of the items to be added at the end of the list. The output is: Kale Lettuce Carrots Peanuts Code provided in the assignment ItemNode.java:Apart from the main list in the list above, elements with the same value are also linked. According to this; a) Write the Generic Node class. b) Write the method that adds a new element to the end of the list.

