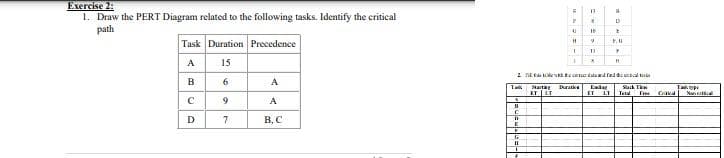
Exercise 2: 1. Draw the PERT Diagram related to the following tasks. Identify the critical path Task Duration Precedence A 15 2 E te d ted Ta Wack T IT L e F Mat atke D В. С
Q: Which of the following server roles is automatically installed when the Active Directory Domain…
A: Introduction Active Directory: It is made to ensure security in the hierarchical organization that…
Q: Do data breaches have the ability to significantly impact cloud security? Does anybody know how to…
A: Significantly: The major distinction between significance and importance is that the former refers…
Q: Write a class to defi Programmer .. with t llowing attributes: nam ess, salary. Then use th
A: We are to use C++ to write a class to define four Programmer.s.. with the following attributes:…
Q: Objectives • Implement loop in MIPS assembly code • Implement decision statement in MIPS assembly…
A: The answer is
Q: Total latency is equal to a summation of network delay contributors such as frame transmission time,…
A: The solution as given below:
Q: are the mechanis ine operations? ine
A: Interrupts are the signals created by PC system (software or hardware) to tell that a specific…
Q: Distinguish between unary, binary, and ternary relationships, and provide an example of each kind of…
A: The following are the most prevalent forms of relationships: Unusual (one entity is involved in the…
Q: Is there a connection between supply chain sustainability and operational planning and scheduling?…
A: Introduction: Here we are required to explain Is there a connection between supply chain…
Q: true or false fossil release oxides and nitrogen when they are burned
A: Nitrogen oxides are produced in engines as a side effect of fuel combustion, the reaction at high…
Q: The laptop contains an Intel i7-8750H 64 bit CPU. Write about the things below. Specifications for…
A: Given: 1 I/O device management is so vital to the operating system that whole I/O subsystems are…
Q: What are the best practices for data security breaches in the healthcare industry?
A: Answer to the provided questionA data breach exposed confidential, sensitive, or protected…
Q: Which approach of elicitation was utilized to collect the functional requirements for the…
A: Introduction: Biometric authentication can be used to obtain functional requirements for Fingerprint…
Q: Please List three motivations Intentional mdicaoes tation of socurity tikety expt Vulnerabitities.
A: Cyber Crime - Cybercrime is also called computer-oriented crime. Cybercrime is basically done using…
Q: This extensive tutorial addresses DNS records, authoritative servers, and iterated and non-iterated…
A: DNS records: DNS turns domain names into IP addresses so that web browsers can access resources on…
Q: Why are mental models crucial in interface design? Give five notable advancements in virtual display…
A: Mental models are one of the most fundamental ideas in human–computer interaction. Instructions,…
Q: Distinguish between unary, binary, and ternary relationships, and provide an example of each kind of…
A: Relationship Type: Binary: A binary connection is a relationship of degree two. A binary connection…
Q: What are some of the most beneficial character attributes for an analyst who is participating in the…
A: Introduction: An analyst is someone who is in charge of acquiring information about a system. He is…
Q: What are the supply chain metrics for the supply chain's core processes?
A: Launch: Supply chain management, which encompasses supply planning, product planning, demand…
Q: Distinguish the differences between the two ways for archiving data in the company.
A: Identify and discuss differences and similarities between the two ways of archiving data used by the…
Q: Data-flow diagrams may be utilized in business process reengineering, but how do they work?
A: Discuss the Business Process Re engineering: The drastic revamping of essential business processes…
Q: What factors influence managers' decisions on which alternative design approach to pursue?
A: Introduction: To proceed with the design approach, the management should consider the following…
Q: Assume you've been requested to facilitate a JAD session. Make a list of 10 rules you'd follow if…
A: JAD session: JAD (Joint Application Development) is a way of including the client or end user in the…
Q: Consider an array of 6 elements (keys should 180612). Apply quick sort steps manually, and show the…
A: Quick Sort /** * The main function that implements quick sort. * @Parameters: array, starting index…
Q: S Hyp
A: Option b (file server) is correct.
Q: operations, including iterated and non-iterated searches, authoritative servers and root servers,…
A: How DNS WorksDNS is an overall structure for making an interpretation of IP locations to…
Q: Give an example of why ICT growth is tough, particularly for a company like Uber, which is the…
A: Explain why ICT growth is tough, particularly for a company like Uber, which is the first metered…
Q: differences between a CISC computer and a RISC computer?
A: The architecture of the Central Processing Unit (CPU) operates the ability to function from…
Q: A virus that attaches itself to an executable executable. If it is required to modify the…
A: Under attack is the Vital Information Resource. The virus may be placed onto your computer without…
Q: please Use C++, Give you a thumbs up Use a map to store a dictionary of English words and their…
A: Please find the answer below :
Q: QUESTION 47 What is {a}*? O A ( a, aa, aaa, ., a", .. О В. (Л, а, аа, а, ., a", ) OC{A} O D.Ø
A: A Regular Expression is a pattern that describes a set of strings that matches the pattern.
Q: How important do you think it is to include challenges with management and employees in your section…
A: The Advantages of Good Operations Management 1. Product QualityOperations management is the first…
Q: Create a Java program that asks the user to enter three (3) first names then display the following:…
A: The Answer is
Q: Assuming this to be true, a single central distribution center handles Internet traffic management.…
A: Introduction: Management is concerned with the coordination and administration of tasks in order to…
Q: Distinguish the differences between the two ways for archiving data in the company.
A: Archiving: The practise of relocating data that is no longer actively utilised to a separate storage…
Q: In a computer with a 32-bit data-bus, how many 4-bit wide memory components are used? the answer to…
A: The solution as given below:
Q: Give an example of how the distinction between a candidate key and an entity type identifier is…
A: Given: Explain the difference between a candidate key and an entity type's identifier. The…
Q: After a data breach, are there methods to enhance cloud security? What are some potential…
A: Given: Is it possible to increase cloud security following a data breach? What are some of the…
Q: What exactly is a cactus stack? What is its function?
A: Introduction: Data structure is the systematic structuring of information so that it can be used…
Q: Are top managers likely to be more effective if they have IT experience? Why or why not? Will online…
A: Answer 1: Effectiveness of top managers Top-level executives are in charge of an organization's…
Q: Distinguish between unary, binary, and ternary relationships, and provide an example of each kind of…
A: Relationship of opposites: A binary connection is a relationship of degree two. A binary connection…
Q: How should resources be used to suit the requirements of the consumer?
A: Establishment: Customer requirements are gathered, appraised, and converted into detailed technical…
Q: nsiderati
A: PC hardware refers to every one of the physical components of a PC, whether it's simple or…
Q: Write a php program to take the current room temperature from the user in degree celsius and try to…
A: Solution: php Program: <?php // Ask for input $cel = (float)readline('Enter the current…
Q: Is it feasible to define a digital signature, and if so, how does it function in practice? In terms…
A: Given: Digital signatures are like "fingerprints" digitally, The digital signature securely connects…
Q: It takes Google just one millisecond to return millions of relevant webpages in response to our…
A: Introduction: All contemporary PC device advances are unquestionably constrained by the speed of…
Q: In Java, objects are explicitly deallocated from the stack. True False
A: A Java object is a part (additionally called an occasion) of a Java class. Each item has a…
Q: What are the advantages and disadvantages of downloading software via the internet vs downloading…
A: DVD: Digital Video disk or Digital Versatile Disk is the full form of DVD. Due to the great quality…
Q: Take into account the following: You are a software developer working on a patient control…
A: Software developers often fulfil the following tasks: Examine user needs before developing and…
Q: What are mental models, and how significant are them in interface design? List five notable advances…
A: (vr/ar) Design During: The first VR / AR helmet mounted display (Sword of Damocles) was invented in…
Q: SQLite and Postgres both manage relational databases, but there are things each database is better…
A: SQLite and Postgres both manage relational databases, but there are things each database is better…
Step by step
Solved in 2 steps with 2 images

- 4)During communication, a common problem occurs when you encounter two stakeholders who have conflicting ideas about the software. That is, they have mutually contradictoryrequirements. Develop a process pattern that addresses this problem and suggest a practicalapproach to it.Can you explain what an ADT is and how it functions to complete tasks?Is it possible that there are consequences associated with ADT administration? Is there any other way you can think of that heredity aids in resolving problems that people face?How to answer below questions for "Sequence Diagram of a supermarket cashier system" based on object oriented modeling: a. Case: part of that system will be modeled? b. Specifications: concrete explanation about the flow to be modeled? c. Identify Interaction Partners? d. Identify Messages? e. Identify Combine Fragments? f. Final Charts?
- Draw a DFD that represents the processes involved in cooking and serving a three-course dinner, including all such associated tasks as laying out the table. Seeking to ensure that your solution does not impose any unnecessary assumptions about the sequencing of actions.a) Suppose a given system allows for indefinite postponementof certain entities. How would you as a systems designer provide ameans for preventing indefinite postponement? b) A system requires that arriving processes must wait forservice if the needed resource is busy. The system does not use"aging" to elevate the priorities of waiting processes to preventindefinite postponement. What other means might the system use toprevent indefinite postponement?Create an activity diagram. Use these steps to help you make your activity diagram: a. Identify activities that you need to perform to get the task completed. b. Identify other actors (people or systems) that need to do their part so that you will get yours done. Make sure to separate responsibilities among different actors. c. Identify a situation in this process that may require decision. d. Are there any aspects of this process that might require parallel action? If there are, include the modeling constructs would you need to use to express parallel action. e. Create a process model describing the situation you chose using the UML activity diagram standard.
- Qu.1: With the aid of a diagram(s), explain the importance of applying the concept of Work Breakdown Structure (WBS) in managing a typical software project using any SDLC of your choicStarting with a context diagram, draw as manynested DFDs as you consider necessary torepresent all of the details of the engineeringdocument management system described inthe following narrative. You must draw atleast a context diagram and a level-0 diagram.In drawing these diagrams, if you discoverthat the narrative is incomplete, make up rea-sonable explanations to complete the story.Provide these extra explanations along withthe diagrams.Projects, Inc. is an engineering firm withapproximately 500 engineers that providemechanical engineering assistance to organi-zations, which requires managing many docu-ments. Projects, Inc. is known for its strongemphasis on change management and qualityassurance procedures. The customer providesdetailed information when requesting a docu-ment through a web portal. The company liai-son (a position within Projects, Inc.) assignsan engineer to write the first draft of therequested document. Upon completion, twopeer engineers review the document to…Adaptive software systems will be created for dynamic environments. As a result, computational entities may join and depart the system on a regular basis through a protocol that connects them. This application is expected to be scalable and trustworthy in the long term. During the development and implementation of this program, did you have a preference for any specific architectural style?
- Read the case study below and answer the questions that follow.The Changing Roles of the Systems AnalystSource: https://pdfs.semanticscholar.org/18e7/acd07e2619b5a9051d72022fe9966ff91007.pdfA systems analyst is an ambiguous title that has been used to describe everyone from programmer to team leader. In spiteof its shortcomings, this title comes closest to defining the person (or persons) who play the most critical role in systemsdevelopment, and who have the ultimate responsibility of overseeing the system project from inception to maintenance.Although the position of a systems analyst didn’t emerge at the same time as computer technology became available, thoseinvolved in developing computer applications quickly recognized the need for such an individual. A great deal of energy andeffort was initially directed toward making the early computer systems produce output. In time, organisations and individualsbecame more demanding in terms of what the system was to do, how the system did…Adaptive software systems will be designed to work in a dynamic environment. As a result, computational entities may join and depart the system on a regular basis through a protocol that connects them. This application is expected to be scalable and reliable. During the development and implementation of this programme, did you have a preference for any specific architectural style?Which of the following is NOT true about system sequence diagram? Select one: a.It describes interactions between an actor and the system. b.It describes a single scenario of a use case. c.It takes into account the internal behaviors of the system. d.It is different from design sequence diagram. e.It is described in terms of system events and returns.

