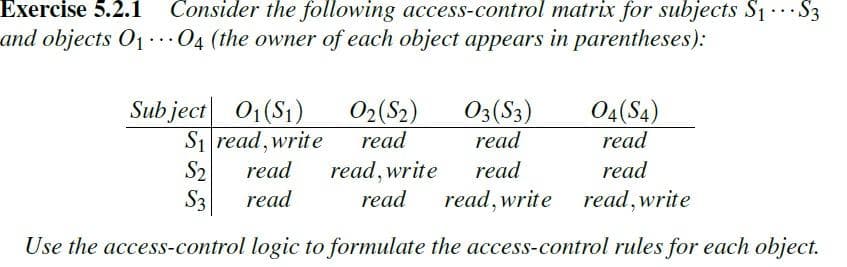
Exercise 5.2.1 Consider the following access-control matrix for subjects S1 S3 and objects O1 04 (the owner of each object appears in parentheses): Sub ject 01(S1) S1 read, write 02(S2) read 03(S3) 04(S4) read read S2 S3 read, write read read read read read read, write read, write Use the access-control logic to formulate the access-control rules for each object.
Q: Select ALL the correct Java statements for the following hierarchical diagram. Assume C1 and C2 are…
A: An interface in Java is a blueprint of a class. It has static constants and abstract methods but it…
Q: Explain how to limit the occurrences of coupling in the following systems. a) The public class…
A: Coupling refers to the interdependencies of the classes which enhances the strength of coupling. If…
Q: Define a class in C++ for the “Hospital”? 1. The Hospital has members (Hospital ID, Hospital name,…
A: Constructor is invoked while creating an instance Destructor is called while exiting program
Q: 1. Consider machines which accept a stream of 1 or more bits (the alphabet is limited to l's and…
A: - We will use the 'or', 'and' and 'xor' operators for this problem.
Q: Consider the following sequence of virtual memory references (in decimal) generated by a single…
A: Page size are as follows 0 -> 0 to 1023 1 -> 1024 to 2047 2 -> 2048 to 3071 3 -> 3072…
Q: In Wumpus World, the following propositions are used as atomic assertions: Wij: The Wumpus is in…
A:
Q: Accomplish the following for the given class diagram. Arithmetic - num1: int num2: int 1. Create the…
A: Program approach: Define the class named Arithmetic. Define the member variables. Define the…
Q: Consider two machine states show beloW. State acc pc ir m (base,bound) pm S1 a Cu (d,e) pm1[1] =…
A: Given : Given the instruction i. The task is to find the type of instruction.
Q: explain counting semaphores, binary semaphores, monitors and mail boxes techniques for achieving…
A: Semaphores: A variable that has an integer value upon which only the operations.…
Q: What distinguishes a class adapter from an object adapter? Can the relevance of both notions be…
A: A class adapter is a "data-level" adapter that is specific to a particular version of the data…
Q: 7. Write a program for the paper computer that will read two numbers and print the absolute value of…
A:
Q: Computer Science Complete the program 'Ring-1.c' to make the program work well for any number of…
A: The code for c languae is
Q: Exercise 10 The porgram su enables a UNIX user to acces another user's account. Unless the first…
A: let us see the answer:- conceptual introduction:-The superuser is a privileged account on a Unix…
Q: Accomplish the following for the given class diagram. Elevator 1. Create the class implementation…
A: Program code: //include the required header files #include<iostream> #include<string>…
Q: Consider the following allocation of a resource. Let the total number of instances of this resource…
A: Introduction :Given , table for the allocation of the resources and two statements are given related…
Q: C++ program
A: Program code: //include header files #include <iostream> using namespace std; //create the…
Q: Create a class diagram in VPE . that have a famliy ,with name ,address of parents . enter name add…
A: Сlаss diаgrаm is а stаtiс diаgrаm. It reрresents the stаtiс view оf аn аррliсаtiоn.…
Q: Accomplish the following for the given class diagram. Arithmetic num1; int num2: int 1. Create the…
A: PSEUDO CODE: Start //Initializing Declare: int…
Q: Write a description (maximum four sentences) for the below subroutine. Specify what exactly the…
A: Given data, Write a description (maximum four sentences) for the below subroutine. Specify what…
Q: If classes C1 and C2 both implement an interface Cint, which has a method whichIsIt, and if C1 c =…
A: Java is a programming language. It contains extensive libraries (package). It can be used to create…
Q: Draw a resource allocation graph for the following processes and resources. There are four processes…
A: Deadlock: Deadlock is a condition in which the given processes are blocked as each process is…
Q: 20. Consider the UML diagram below. It shows (1) a client class (Advisor), (2) a superclass…
A: In the given uml diagram , --------------------------- we make public behaviour as student with…
Q: Q1: a) Construct a RE which accepts all strings that contain one a, or one b. b) Build an FA that…
A: Q1. a. Regular expression which accepts all strings that contain one a or one b: ∑ = {a,b}…
Q: Write the implementation level steps of a single tape deterministic TM which accepts the following…
A: The correct answer for the above mentioned question is given in the following steps for your…
Q: Show that, if the wait() and signal() semaphore operations are not executed atomically, then mutual…
A: Answer: A semaphore is an approach particularly known to be in charge of all the concurrent…
Q: The function PowerRecursive below takes inputs r and n, wherer is any real number and n is a…
A: Recursive call PowerRecursive(r,n-1) done for n-1 to to base case. The base case of the…
Q: Draw a UML class diagram to show object hierarchy or aggregation hierarchy of the following classes:…
A: A computer consists of system box, printer, mouse, keyboard and a monitor. Therefore, these are…
Q: Let's say p contains a memory address and the 8 bytes in memory beginning at that address are (in…
A: Big-endian computer, will represent each byte from left to right order. Little endian will represent…
Q: Is the following concurrent execution sequentially consistent? write(a,1), read(b,0), computer 1:…
A: Sequential concurrent execution: for the given operation we have to form a graph to check for any…
Q: Using a repetition construct, display the following on the screen (warm-up problem). L L
A: We will solve the given problem in C++ language.
Q: 2. Give implementation-level descriptions of Turing machines that decide the following languages…
A: Answer
Q: L = {ww | w ԑ (a, b)+} design a Turing Machine that accepts L and please write down the step by step…
A: A Turing machine consists of a tape of infinite length on which read and write operations can be…
Q: Using the following access matrix tell if the asked operations is allowed or denied. P1 which runs…
A: Given matrix is an access matrix which contains four domains, three files and one laser printer. The…
Q: Draw the State Diagram and the State Table for a single-tape Turing machine that accepts a sequence…
A: We keep scanning the input and move head towards right. As long as the input scanned so far…
Q: Operating sys : In the following producer and consumer problem using semaphores, explain with an…
A: Wait(S) is used to set the semaphore variable "S" to "0" in order that no other process can enter…
Q: A stream is a path of communication between the source of some information and its destination.…
A: read() :- Reads the next byte of data from the input stream. skip() :- Skips over and discards n…
Q: Draw a State Chart Diagram describing the interaction protocol of MyTimeSheet. Here is a…
A: Lets discuss the soln in the next steps
Q: 158 CMPG 211 1-1 V 2021 Expand All Next Week 6Practical: Objects, Arrays & Text files Main…
A: The complete code is given below with the output.
Q: For each of the following page replacement policies, list the total number of page faults and fill…
A: Answer:a. LRU replacement:
Q: Using C++, Java, or C#, implement a Complex class in the spirit of Example 10.25. Discuss the time…
A: Hey there, I have read the question carefully and clearly. I am writing the required solution for…
Q: Create a program kb.py that is able to take in a file containing a knowledge base(KB) and a model…
A: Program for kb.py that is able to take in a file containing a knowledge base (KB) and a model and…
Q: b. Consider the extract from a C program below, explain what would happen to the other processes on…
A: Answer: I have done code and also I have attached code as well as code screenshot and output
Q: Draw the memory allocation structure(s) for this instruction including the content values if…
A:
Q: Answer all questions in java
A: A hard-real-time system is one in which the system must meet all deadlines without fail. Typically,…
Q: In the picture attached, the Say that the system is running 3 jobs, A, B, and C, and that all…
A: Each cycle in a PC system requires some measure of time for its execution. The CPU time is the time…
Q: The following is a Java code for a Design Patterns: Strategy Pattern in object oriented design…
A: To execute the given program code: Firstly, creating a project in the IDE and then creating all the…
Q: The concept that the same message gives different meanings to different objects is called…
A: Below is the code to demonstrate the answer to your question!!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 2 images

- What describes how the principle of least privlege applies to the use of computers? A, It guarantees that no information inifially held in an object can be used outside its execution environment B, A process is allowed access only to the resources il needs to complete Its task and limit damage from a faulty process C, It is a process that can access an object in a domain only if that domain has a key that malches one of the locks of the object D It is the use of access controls to monitor and limit access to applications, programs, and websites during specific times of use.Create a java class to represent a log message. The log message should include the following attributes:a. The severity of the message from least to most severe: DEBUG, INFO, WARNING, ERROR, or CRITICAL.b. The name of the module that has created the log.c. The timestamp at which the log was created in the format“YYYY/MM/dd HH:mm:ss.SSS” (see java.text.SimpleDateFormat).d. The message to be logged.e. A toString() method that returns a string in the format:[severity][timestamp][name] messageS1: Deadlock can be avoided by using semaphores instead of locks for mutual exclusion. S2: Periodically yielding the processor while spin waiting reduces the amount of wasted time to be proportional to the duration of a context switch. Which of the above statements are true? Do not solve if you are not sure, i have very less time remaining. Want correct answer in few minutes
- Consider a system with the four access operations read, write, grant, and revoke. You can use grant not only to give other subjects read and write access, but also to grant them the right to grant access to the objects you own. Which data structure and algorithm would you use to implement the grant and revoke operation so that you can revoke all access to an object you own?You are tasked with the development of an E-Scooter ride-sharesystem. It allows registered commuters to approach an idle E-Scooter andreserve it, following which they use the E-Scooter to commute a certaindistance (that is not known prior to use). Finally, after the commuter reachestheir destination, they end the ride, which prompts an automaticcomputation of the ride fees. which is automatically debited using thecommuters registered payment details.Suppose the following groups are defined to shorten a system’s access control lists: – Group1: Alice, Bob, Cynthia, David, Eve – Group2: Alice, Bob, Cynthia – Group3: Bob, Cynthia Suppose the access control list for File 1 is: – File 1: Group 1, R; Group 2, READ,WRITE If Alice wants to write to File 1 giving your reasoning state whether Alice will be allowed to do so if: 2.1.1 The first relevant entry policy is applied 2.1.2 The any permission in list policy is applied
- Question 3:Consider the below lines of codeString a = “Harry”;String b = “Harry”;String c = new String(“Harry”);What can be commented about the memory locations about a, b and c? Justify your answerwith proper reasons. (Hint: c uses the ‘new’ keyword )can access control be mitigated by taking certain steps?Observe the following code and answer the following questions. import java.io.*; import java.net.*; import java.util.Date; public class TimeServer{ public static void main(String args[]) throws Exception{ ServerSocket server = new ServerSocket(9876); while (true){ Socket client = server.accept(); //blocks until a client connects PrintStream ps = new PrintStream( client.getOutputStream() ); ps.println("Time from server:" + new Date()); client.close(); } } } What type of server this is? Is it single or multi-threaded? 2. What should be done according to you if the number of clients to this server increases? Modify the server code so that the increases number of clients can be handled by this server. 3. Explain where in your code you ensured that for every incoming request from a client, a new thread is…
- Please solve the following in Java Access Level In many computer systems and networks, different users are granted different levels of access to different resources. In this case, you are given a int[] rights, indicating the privilege level of each user to use some system resource. You are also given a int minPermission, which is the minimum permission a user must have to use this resource. YouaretoreturnaStringindicatingwhichuserscanand cannot access this resource. Each character in the return value corresponds to the element of users with the same index. 'A' indicates the user is allowed access, while 'D' indicates the user is denied access. Constraints users will contain between 0 and 50 elements, inclusive. Each element of users will be between 0 and 100, inclusive. minPermission will be between 0 and 100, inclusive. Examples a) {0,1,2,3,4,5} 2 Returns: "DDAAAA" Here, the first two users don't have sufficient privileges, but the remainder do. b) {5,3,2,10,0} 20…Write a Python script that uses the sys module to perform the following tasks:1. In a main method:a. Read and print the command-line arguments when the script is run.b. Print the Python path (the directories where Python is looking for modules toimport).c. Print the Python version.d. Print the platform name.2. The main() function must only run automatically if the module is being run directly, notwhen imported. Here is a screenshot of the expected behavior, testing all scenarios described above. Replicatethis functionality in your script, including the formatting and outputs of all messages. Theprogram must work for any arguments that the user provides after the name of the script.For this assignment, write a pair of programs, in C or as shell scripts, to send and receive a message. Your programs will: Send and receive a message by a covert channel on a MINIX 3 system. Hint: A permission bit can be seen even when a file is otherwise inaccessible, and the sleep command or system call is guaranteed to delay for a fixed time, set by its argument. Measure the data rate on an idle system. Create an artificially heavy load by starting up numerous different background processes and measure the data rate again.

