Expected Result: J 1-2-3 4.5.6 له 7.8.9 له Enter-move: 1.4. d X. 2.3 4-5.64 له 7.8.9 له له - 2:Enter.move ل X0003 4.5.64 له 7.8.9 له له 3:Enter.move له X0X 4-5-64 له 7.8.9 له له 40 :Enter.move X0X 0-5.6 له 7.8.9 له Enter-move: 5. X0X له 0X06 له 7.8.9
Q: Compared to other types of data, why does video need a larger quantity of storage space?
A: Compared to the other types of data such as audio, images, pdf files etc. The video needs a large…
Q: What is Brute Force algorithm? List two Pros and two Cons of using Brute Force. Apply the brute…
A: To define Brute Force algorithm And to apply the brute force algorithm to find the shortest path…
Q: In your perspective, what are the top five reasons why some people dislike or are opposed to using…
A: Introduction: The use of computers can make people less sociable. An enormous amount of privacy has…
Q: Compilers and assemblers can rearrange assembler instructions to reduce pipeline risks as much as…
A: The hardware does not support certain combinations of instructions in its current state (two…
Q: Create order from the chaos of DNS data by classifying them. Give a quick rundown on what they are…
A: Globally, IP addresses are converted to domain names that can be read by humans via DNS. A user's…
Q: This is a consequence of the ever-increasing power of computers in recent years. How did computers…
A: The power of computers has been with us ever since they were invented, but these days you can find…
Q: Give a comprehensive account of how a programming language was created.
A: Explanation: In the world of computers, there are over 500 different programming languages, each…
Q: Complete function Print PopcornTime(), with int parameter bagOunces, and void return type. If…
A: We need to write a function in C++ for the given scenario.
Q: Given a time in 24-hour notation, write a function that adds 2 times, a function that substracts 2…
A: Code: #include <iostream> using namespace std; class time24 //Class for Time Functions. {…
Q: Provide a summary of, and explanation for, the wide variety of preventive steps that may be taken…
A: Phishing is a type of fraud in which a criminal uses email or other forms of contact to pose as a…
Q: write socket to connect between cerver and client by using C or python to calculate area of…
A: The solution is done using Python programming. Please refer to the following step for the complete…
Q: A better design would be one with the following tables: Patient : | pid | name…
A: GIVEN: Patient : | pid | name | dob | addr | tel | Exam…
Q: Please send me answer within 10 min!! I will rate you good for sure!! Please send me typed answer!
A: For q1, I have provided C++ CODE along with CODE SCREENSHOT and OUTPUT…
Q: Make a document detailing the various DNS records, labeling each one with the sort of record it…
A: A mail exchanger (MX) record refers to a domain's mail server, referred to as the mail server.…
Q: function
A: Solution - In the given question, we have to Write a function that returns the greatest common…
Q: This is for Python. Now create a new file named MSPaint_PA51 in your IDLE. Find an image on the…
A: Python is a dynamically typed programming language. Python is an object-oriented and structured…
Q: Define a function drawCircle. This function should expect a Turtle object, the coordinates of the…
A: Solution to the given question Algorithm 1. Import math and turtle libraries 2. Define function…
Q: Make a document detailing the various DNS records, labeling each one with the sort of record it…
A: When establishing Content Delivery Networks, the CDN's address is often added as a CNAME record to…
Q: Check whether the following 8086 instructions are valid or no
A: A) ADD AX,100HB) MOV BL, AXC) ADD CX,1234H The 8086 instructions (A) ADD AX,100H and (C) ADD…
Q: Our method will involve analyzing a string and picking the 5 most common letters in that string. We…
A: Define find_common_letters() function to find the five most common letters in a string. Define…
Q: I ANALYSIS. Read the following situations and analyze the fundamentals of multimedia elements. 1. A…
A: Solution for the given question, Note: Since you have posted a question with multiple parts, we…
Q: Follow up question 1.please convert the above code into Class Using object-oriented approach. 2.…
A: In this question we have to convert the previous code into OOPS based code using classes approach…
Q: Suppose the following function has been defined: string concatenateWith Self(string inputString) {…
A: Function: It is mainly used to repeatedly use the block of statements of a function by just calling…
Q: What does the characters L, A, L, R and 1 in the name LALR(1) parser stand for? course. Marks: 1]
A: Answer LALR(1) stands for "Look- Ahead Left-to-Right parser with 1 token of look-ahead" It is a type…
Q: 3. Common Data Types Consider the following code snippet: interface X { I V put (K key, V value); V…
A: Dear Student, The answer to your question is given below -
Q: java question
A: In step 2, I have provided ANSWER with brief explanation----------- In step 3, I have provided…
Q: Please answer fast Detail explanation about deadlock in OS.
A: A deadlock occurs when two computer programs or applications that are using the same resource…
Q: make Algorithm for Outline of collection Input: a pc presentation with generators {a 1, a2 ..... an…
A: algorithm given in next step:
Q: Complete a program that reads a vector index as input and outputs the element of a vector of 10…
A: Please find the answer below :
Q: Please code in MASM 7. Prime Number Program Write a procedure named IsPrime that sets the Zero…
A: MASM which refers to the one it is Microsoft Macro Assembler (MASM) provides several advantages over…
Q: The ability to operate a computer effectively may open many doors. What are the possible benefits of…
A: In contemporary civilization, computer-related technologies have been extensively accepted. The…
Q: Determine the first occurrence of "2" in "CO2 H20" MUST BE IN PYTHON
A: In Python, we will use string.find( ) method to search for the occurrence. If more than 1…
Q: How do you feel about using computers and technology in your daily life? Technology has many more…
A: Our lives are significantly impacted by computers. The daily usage of computers with internet…
Q: Complete the function definition to return the hours given minutes. Output for sample program when…
A: Here I have defined the function named GetMinutesAsHours(). In this function, I have converted the…
Q: In what ways might a Trojan horse be used, and what does one entail? Justify your answer using three…
A: Trojan horse: A Trojan horse is a piece of malware or software that looks good but is harmful and…
Q: Main memory contains a total of 24 frames and each frame is 2³ bytes. How many bits are in the…
A: As per our company guidelines, only 3 sub parts will be answered. So, please repost the remaining…
Q: C++ Define an "Expression" class that manages expression info: operand1 (integer), operand2…
A: #include <iostream>#include <vector>#include <string> using namespace std; class…
Q: rk with source s and t sink. We say that an edge e is a bottleneck if it crosses every…
A: observation as an s-t overflow network G= (V, E). Given font node s and sink node t, we can add…
Q: Where do DNS records, authoritative servers, root servers, and iterative and non-iterative queries…
A: Introduction: Dummy.com is the domain name for a website with an IP address of 255.225.117.112. The…
Q: Write a function that converts a given min heap which is implemented by arravs to a max heap. The…
A: Min heap:In data structures concept an min heap is a binary tree in which the value in each internal…
Q: How to generate segmentation mask from thermal images without temporature information?
A: Answer Segmentation mask generation from thermal images without temperature information is possible…
Q: The amount of potential pipeline failures may be reduced with the help of compilers and assemblers,…
A: A pipeline executes many instructions concurrently.A pipeline processor consists of linear sections…
Q: ANDROID Your project must have at least one _____. manifest string TextView…
A: A TextView is used to displays text to the user and optionally allows them to edit it. An activity…
Q: Question 12 kana . Full explain this question and text typing work only We should answer our…
A: Dear Student, The answer to your question is given below -
Q: Discuss how design patterns relate to the object-oriented programming paradigm.
A: Intro Object orientated paradigm is not any programming language, but a set of concepts that is…
Q: Provide the names of three different server types that a regional bank may utilize.
A: Here, we'll talk about the three types of servers that a local bank could utilise: In today's…
Q: Naming the various parts of a high-level programming language allows for their easy identification.
A: Answer Syntax: The structure and rules of programming language used to define the language…
Q: Car.h" #include "Station.h" #include using namespace std; extern void te
A: Dear Student, The complete program with completed function is given below -
Q: Write an if-else statement with multiple branches. If givenYear is 2101 or greater, print "Distant…
A: I have provided JAVA CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOT-------------
Q: What are the many steps involved in the programming process? What factors should be thought about…
A: Programming Programming is the most common way of making a bunch of instructions that advise a…
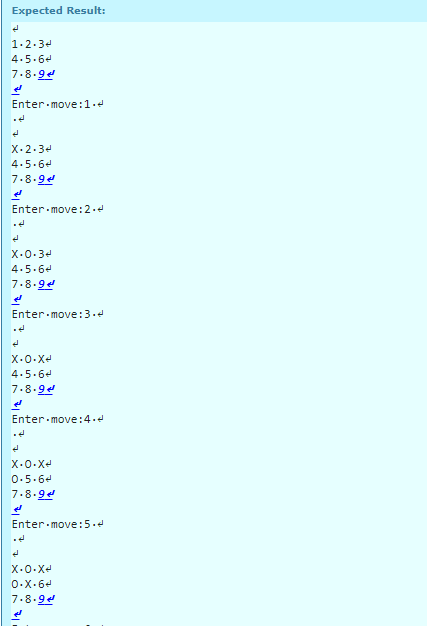
7.10: Tic Tac Toe (sort of)
Write a program that will allow two users to play
tic-tac-toe. The program should ask for moves
alternately from player X and player O. The
program displays the game positions as follows:
123
456
789
The players enter their moves by entering the
position number (a single digit, 1-9) they
wish to mark. After each
move, the program re-displays the changed board.
A sample board configuration is as follows:
XXO
456
O89
SAMPLE RUN #1: ./ETest
Interactive Session
1 2 3
4 5 6
7 8 9
Enter move:1
X 2 3
4 5 6
7 8 9
Enter move:2
X O 3
4 5 6
7 8 9
Enter move:3
X O X
4 5 6
7 8 9
Enter move:4
X O X
O 5 6
7 8 9
Enter move:5
X O X
O X 6
7 8 9
Enter move:6
X O X
O X O
7 8 9
Enter move:7
X O X
O X O
X 8 9
Enter move:8
X O X
O X O
X O 9
Enter move:9
X O X
O X O
X O X
Game over!
Step by step
Solved in 3 steps with 7 images

- Suppose you have a knapsack that can carry up to 17 pounds. You can only put certain items, and each item has a weight and a value. You want to put the items that will give you the highest possible value, but you can only carry up to 15 pounds. Here are the items you can put and their weights and values: I Weight value Value/Weight 1 2 10 5 2 4 30 7.5 3 6 50 8.33 4 9 70 7.78 5 10 80 8 Table 1: Caption Your task is to solve the Knapsack Problem using a greedy approach.Hints:- Sort the items by their value-to-weight ratio in descending order. Start with the item with the highest value-to-weight ratio and add it to the knapsack. - Continue adding items to the knapsack in descending order of their value-to-weight ratio until the knapsack is full or there are no more items left. - Your solution should output the total value of the items in the knapsack and the list of items that you have put. -This…Before John can start, Taylor must get a head startBefore Nkosi can start, Emil must get a head startBefore Tanya can start, Nkosi and John must both have a head startBefore Taylor can start, Nkosi and Emil must both have a head start In what order should Devin’s friends start the scavenger hunt? Explain how you went about figuring out the order.JAVA: Texas Hold em poker game 2 to 8 human or computer players Each player has a name and stack of chips Computer players have a difficulty setting: easy, medium, hard Summary of each hand:o Dealer collects ante from appropriate players, shuffles the deck, and deals eachplayer a hand of 2 cards from the deck.o A betting round occurs, followed by dealing 3 shared cards from the deck.o As shared cards are dealt, more betting rounds occur, where each player can fold,check, or raise.o At the end of a round, if more than one player is remaining, players' hands arecompared, and the best hand wins the pot of all chips bet so far. What classes are in this system? What are their responsibilities? Which classes collaborate? Create the Use Cases for this systemCreate a Use Case diagram for this system Draw a class diagram for this system. Include relationships between classes (generalization andassociational).
- Using javascript getElementByClass- write a simple programe whereby each time a player gets shot by a bullet, the player loses a life and a 'live' is remove from the three 'lives'.If the player loses all three lives, display and print 'game over'.Display 'play again' message to restart th game. <ul class = "lives"> <li></li> <li></li> <li></li> </ul>In the game Rock paper Scissors, two players simultaneously choose one of three options: rock, paper, or scissors. If both players choose the same option, then the result is a tie. However, if they choose differently, the winner is determined as follows: Rock beats scissors, because a rock can break a pair of scissors. Scissors beats paper, because scissors can cut paper. Paper beats rock, because a piece of paper can cover a rock. Create a game in which the computer randomly chooses rock, paper, or scissors. Let the user enter a character, r, p, or s, each representing one of the three choices. Then, determine the winner. Save the application as RockPaperScissors.cs.The Monty Hall Cash game costs $12 to play. Once you pay, you havea choice of three doors. Behind one door is $20, behind the other twois absolutely nothing (i.e. $0). You pick a door, say number 1, andthe host running the game, who knows what’s behind the doors, opensanother door, say number 3, which has absolutely nothing. He says toyou, “Do you want to switch to door number 2?”. You can decide toswitch doors, or stay with your initial choice. You “win” whatever isbehind the door you end up choosing. Use a python Jupyter notebook to run simulations of the gameto estimate/approximate the expected value of the game if youalways switch, and the expected value if you always stay.
- In the game Rock Paper Scissors, two players simultaneously choose one of three options: rock, paper, or scissors. If both players choose the same option, then the result is a tie. However, if they choose differently, the winner is determined as follows:Rock beats scissors, because a rock can break a pair of scissors.Scissors beats paper, because scissors can cut paper.Paper beats rock, because a piece of paper can cover a rock.Create a game in which the computer randomly chooses rock, paper, or scissors.Let the user enter a number 1, 2, or 3, each representing one of the three choices.Then, determine the winner.Program should validate all user inputGame should ask the user to play again and continue if yes and stop if no.Once the user stops playing, program should print the total number of wins.In the game Rock Paper Scissors, two players simultaneously choose one of three options: rock, paper, or scissors. If both players choose the same option, then the result is a tie. However, if they choose differently, the winner is determined as follows: • Rock beats scissors, because a rock can break a pair of scissors. • Scissors beats paper, because scissors can cut paper. • Paper beats rock, because a piece of paper can cover a rock. Create a game in which the computer randomly chooses rock, paper, or scissors. Let the user enter a number 1, 2, or 3, each representing one of the three choices. Then, determine the winner. Save the application as RockPaperScissors.javaA high school has 1000 students and 1000 lockers, one locker for each student. On the first day of school, theprincipal plays the following game: She asks the first student to open all the lockers. She then asks the secondstudent to close all the even-numbered lockers. The third student is asked to check every third locker. If it isopen, the student closes it; if it is closed, the student opens it. The fourth student is asked to check every fourthlocker. If it is open, the student closes it; if it is closed, the student opens it. The remaining students continuethis game. In general, the nth student checks every nth locker. If it is open, the student closes it; if it is closed,the student opens it. After all the students have taken turns, some of the lockers are open and some are closed.The program below, when ran, will prompt the user to enter the number of lockers in the school. After thegame is over, the program will output the number of lockers and the lockers numbers of the lockers…
- Rock-paper-scissors is a game usually played between two people, in which each player simultaneously forms one of three shapes with an outstretched hand. These shapes are rock (a closed fist), paper (a flat hand), and scissors (a fist with the index finger and middle finger extended, forming a V). The code described above is A. both a digital and an analog code. B. an analog code. C. a digital code. D. neither a digital nor an analog code. Two user interface designers are working on the interface for a collaborative text editor. They are discussing the design of a proposed new feature: a button to irreversibly delete the current version and all past versions of a document. Designer A says, “Let's make a red button with the words ‘Delete permanently’ on it. Red means danger.” Designer B says, “No, let’s make a button with a drawing of a piece of paper going up in flames.” Which of the following best describes the designers' proposals? A. Designer A’s proposed sign…Texas Hold em poker game 2 to 8 human or computer players Each player has a name and stack of chips Computer players have a difficulty setting: easy, medium, hard Summary of each hand:o Dealer collects ante from appropriate players, shuffles the deck, and deals eachplayer a hand of 2 cards from the deck.o A betting round occurs, followed by dealing 3 shared cards from the deck.o As shared cards are dealt, more betting rounds occur, where each player can fold,check, or raise.o At the end of a round, if more than one player is remaining, players' hands arecompared, and the best hand wins the pot of all chips bet so far. What classes are in this system? What are their responsibilities? Which classes collaborate? Create the Use Cases for this systemCreate a Use Case diagram for this system Draw a class diagram for this system. Include relationships between classes (generalization andassociational).Jack and Jill will play a game called Hotter, Colder. Jill chooses a number from 0 to 100, and Jack makes repeated attempts to guess it. For each guess, Jill will respond with: hotter - if the current guess is closer to her number than the previous guess is colder - if the current guess is farther to her number than the previous guess is same - if the current guess is as far (to her number) as the previous guess is For Jack’s first guess, since there is no previous guess yet, Jill will just answer same. Describe an algorithm or a systematic approach that Jack can follow to win the games faster (fewer guesses). Example: Jill chooses number 40. Note: Jack can guess any number from 0 to 100 at any point of the game. Jack guesses 100. Jill responds same (first guess) Jack guesses 60. Jill responds hotter (60 is closer to 40 than previous guess 100) Jack guesses 80. Jill responds colder (80 is farther from 40 than previous guess 60) Jack guesses…



