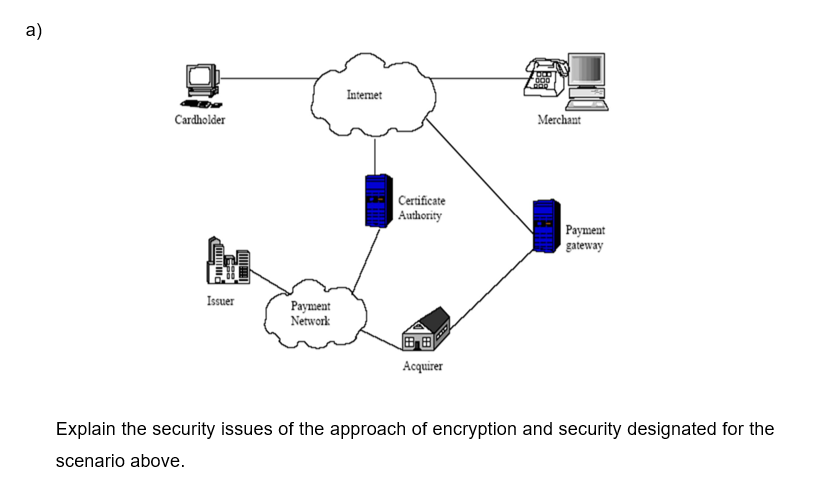
Acquirer Explain the security issues of the approach of encryption and security designated for the scenario above.
Q: Consider the following scenario and draw an E-R diagram for Mozar. Mozar has decided to store…
A: Entities: ----------------------------------- Album : Attributes: Title, Copyright date Format,…
Q: show that the two-phase locking ensures conflict serializability and that transactions can be…
A: Given: Demonstrate that two-phase locking guarantees conflict serializability and that transactions…
Q: Distinguish between differential and incremental backups, with a focus on database backups and…
A: A full backup created from within Windows, of course, backs up all the files in a partition or on a…
Q: What benefit does rigorous two-phase locking provide? How does it compare with other forms of…
A: Rigorous two phase locking is a stricter locking protocol. In this protocol, all locks are held till…
Q: Describe the three guiding principles of integrity. Explanations need to be provided for each and…
A: Integrity: Integrity is defined as the discipline of being honest, consistent, and unyielding in…
Q: What is the advantage of strict two-phase locking? What does it have in common with other types of…
A: Introduction: Rigorous two-phase locking provides many benefits over strict two-phase locking.…
Q: How about a lengthy description of the database's file system?
A: Given: Can you write a detailed note regarding the database file system?
Q: Exercise 9.9 considers the issue of encrypting certain properties. Several database systems, on the…
A: Encryption of attributes: It is a method of securing data at the access level. It stops the user…
Q: Define the terms "integrity constraints" and "authorization constraints."
A: Given :- Define the terms "integrity constraints" and "authorization constraints."
Q: Give instances of information that the Security Rule does not cover.
A: Lets see the solution in the next steps
Q: Explain how data security laws in the US and the EU are different. Is it important for your answer…
A: Security standards : Explain how the United States and the European Union have different data…
Q: List the three rules of integrity. List the justifications for enforcing each regulation.
A: Rules of Integrity: Even though integrity standards seem complex and challenging to understand, they…
Q: tingencies. Includ
A: Define the four types of contingencies. Include the difference between escape and avoidance.…
Q: Explain the differences in data security rules between the United States and the European Union.…
A: Answer: The US does not place broad restrictions on cross-border data transfers and has generally…
Q: Define integrity and nonrepudiation.
A: Integrity is the assurance that data can only be accessed and modified by those who are authorized…
Q: Given the grocery store transactions example with minimum support = 33.34% and minimum confidence =…
A:
Q: Explain, with the help of some sample schedules, how the phantom problem could appear when key-value…
A: Use sample schedules to illustrate how the phantom issue could arise when key-value locking is used.…
Q: Explain the difference between explicit and implicit locks.
A:
Q: Give an example of a surrogate key
A: In database design, it is a good practice to have a primary key for each table. There are two ways…
Q: Q2/ For the DSA signature algorithm, show the process of key generation, signing and verification by…
A: DSA algorithm Digital signatures algorithms are used to detect whether the data is modified by…
Q: Consider the following scenario and draw an E-R diagram for Mozar. Mozar has decided to store…
A: Introduction :We have to draw an ER-Diagram of the given database.
Q: Threats to data security are many. Then, consider potential defenses.
A: Data security is the practice of protecting the digital information from the unauthorized access, or…
Q: 5. What are the three general ways that a deadlock can be handled?
A: Deadlock refers to the unwanted situation that may occur in an operating system when several…
Q: Explain the possibility of the phantom problem occurring while utilizing key value locking by…
A: Phantom is a transactional error that occurs when the same query produces different sets of results…
Q: Identity theft, in which people steal personal information, continues to be a serious threat for…
A: Introduction: Theft - obtaining personal information: The majority of thefts occur in order to get…
Q: QUESTION 7 Locking grant distributed serializability Yes O No
A: SERIALIZABILITY : it is the intertwined schedule of number of transaction. the common practical…
Q: Is a stable database state possible, and if so, how can it be achieved? There is no guarantee that…
A: Given: It is specified for those that would include all of the data integrity requirements,…
Q: What are the advantages of using a rigorous two-phase locking mechanism? What disadvantages result
A: Strict two-phase locking: Like simple two-phase locking, a stringent two-phase locking protocol…
Q: Briefly discuss deferred database modification technique. (c) (а) (b) Add lock and…
A: Deferred Database Modification Technique: As per the name suggest "deferred" that means do it…
Q: . Normalize the table T up to BCNF. Clearly show your steps and state all Primary and Foreign keys.…
A: The answer for the above question is as follows
Q: Which of the following is not the approach to dealing with deadlock ? a. Prevention b. Avoidance c.…
A: Which of the following is not the approach to dealing with deadlock ?a. Preventionb. Avoidancec.…
Q: Explain the distinction between an explicit and an implicit lock.
A: Given: Explain the distinction between an explicit and an implicit lock.
Q: relation R (W,I,S,D,O,M) with the following eight functional dependencies: F: {WI → S; D → OM; S →…
A: Note: Answering the first three subparts as per the guidelines. Given : F: {WI → S; D → OM; S → W;…
Q: How does strict two-phase locking benefit me? What are the drawbacks?
A: Two-Phase Locking -A transaction is said to walk with the Two-Phase Locking convention assuming…
Q: Differentiate strict two phase locking protocol and rigorous two phase locking protocol.
A: Introduction: Strict two-phase locking retains all of its exclusive write locks until commit time,…
Q: What factors impact an orginization policies on data privacy?
A: Introduction: Data privacy is a branch of data security involved in the proper handling of…
Q: Identify security principles in data access design. (Information systems security and cryptography)
A: The security design principles are considered while designing any security mechanism for a system.…
Q: The Bell-LaPadula model implements a combination of -- with the primary concern on the…
A: Answer to the above question is in step2.
Q: Explain in detail what data security is, as well as the three categories of data ownership and their…
A: The definitions asked are:- Data security The types of data ownership
Q: Use of multiple-granularity locking may require more or fewer locks than an equivalent system with a…
A: Multiple granularity locking requires fewer locks, if a transaction needs to access a large a set of…
Q: Q. In given its own version of the database a. Snapshot b. None of the above isolation each…
A: Given mcq is related to database.
Q: What are the advantages of rigorous two-phase locking? What are the drawbacks?
A: Given: What are the advantages and disadvantages of two-phase locking?
Q: Q2 / For the DSA signature algorithm, show the process of key generation, signing and verification…
A: Solution:
Q: istency с) Backup d) Isolation e) Durability f the following Transaction Property makes sure befor ,…
A:
Q: key of Film and there is a referential integri . directorNum and Film, directorNum. Discuss all the…
A: Table Creation:
Q: Explain in detail and with examples the different levels of access available in the context of…
A: Access to the record management system on a granular level. Record management is the process of…
Q: Define the difference between integrity and authorization constraints.
A: Intro
Step by step
Solved in 2 steps

- Give a summary of the numerous preventive steps that may be done against phishing and spoofing techniques, as well as an explanation of each of these preventative measures separately, and then give an example of each of these preventative measures.It is necessary to have a conversation about best practices for internet security and how such practices may be put into action in order to make internet users less vulnerable.Provide a rundown of, and an explanation for, the many safeguards available against phishing and spoofing schemes.
- I NEED URGENTLY, PLEASE Justify the use of a range of security techniques in typical situations. It may help to consider what would happen without the security mechanisms and go from there. A- is user’s permissions B-is Encryption C- is Anti-Virus D- is FirewallAt least four (4) different types of cookies and their effect on internet security should be included in any comprehensive discussion of this topic.Q.2.1 Use suitable examples that will distinguish the three important aspects of computerand network security:• Confidentiality;• Integrity, and• Availability.Q.2.2 Briefly discuss how a worm can disrupt a computer or a network.



