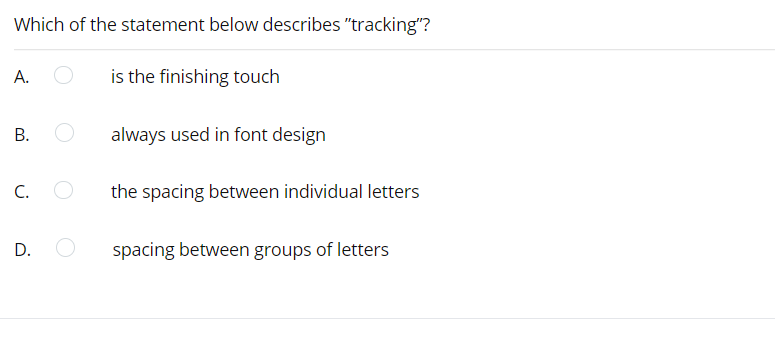
f the statement below describes "t is the finishing touch always used in font design the spacing between individua spacing between groups of let
Q: There are three most frequent problems with computers, and if you own one, you should know how to…
A: Computer A computer is a device or equipment that follows instructions from a software or hardware…
Q: What are the four main sorts of audiences that are taken into consideration, and how does the…
A: The Four Audience Types: When you're trying to persuade a group to act via your speech, there are…
Q: How were the usability and user experience goals broken down throughout the evaluation?
A: Introduction: From the information that has been presented, one can infer the following:
Q: How does starting from scratch in computer science compare to using a packaged data model on paper?
A: Introduction: How does starting from scratch in computer science compare to using a packaged data…
Q: If you had to sum up software engineering in a few words, what would they be? Who or what are you…
A: Given: Software engineering is the process of evaluating user demands and developing, creating, and…
Q: itend to enhance the security of the following URLS (hyper
A: Unsafe domains are associations with destinations that might incorporate phishing, malware, or…
Q: There have been a number of different approaches to developing a processor that can decode both…
A: Introduction In response to your inquiry, When a computer is shut down to execute instructions, the…
Q: The script has four steps: Read a list of integers (no duplicates). Output the numbers in the list.…
A: # Code import java.util.Scanner: public class LabProgram { //Read and return an array…
Q: Is CBIS suitable for all businesses? How did CBIS come into being? What's the point of a company…
A: Given: Is CBIS appropriate for usage by a company at all times?Yes An enterprise computer-based…
Q: What are the differences between testing strategy and testing methodology?
A: Testing Software testing is a collection of procedures for determining the completeness and quality…
Q: Consider the justification for "sudo" access. What are the benefits of not signing in as the root…
A: Using the "sudor" command, the current user's privileges are elevated to root. Permission is granted…
Q: Where can you get trustworthy information online, and how can you tell when you've found it?
A: Trustworthy information: The capacity of an information system to create accurate and genuine…
Q: What are the three different levels of testing that occur inside a class?
A: In the given question the software has passed through three testing levels Unit Testing, Integration…
Q: Does it matter if you're in a production or testing environment?
A: Introduction: You may execute your update against a controlled set of data in a test environment…
Q: 0. Holy digits Batman! The Riddler is planning his next caper somewhere on Pennsylvania Avenue. In…
A: Here is the approach : Create the flags to have the check for every condition . Run the while loop…
Q: In what ways are they different from one other?
A: Deep understanding: It works with artificial neural networks and recurrent neural networks and is a…
Q: What are the three different levels of testing that occur inside a class?
A: Describe the three stages of class testing. Testing Standards: In computer code testing, there are…
Q: In what cases would you advocate the use of assembly language code in the creation of application…
A: Introduction: Mnemonic codes, analogous to English words, are used in assembly language. Although…
Q: Are there tools to assist with data input aand database management that maintain data integrity?
A: When people discuss the general quality, completeness, and consistency of their data, they refer to…
Q: investigation
A: Introduction of digital forensic investigation.
Q: What will be the impact of the internet of things (IoT) on our everyday lives? Justify your position…
A: If we talk about the future of technology or of Internet of Things, frankly speaking it would be…
Q: nen you hear the word "computer," what do you
A: A computer is an advanced electronic machine that can be modified to complete successions of number…
Q: In a few short words, what is the primary objective of software engineering? What's wrong with this…
A: Utilize high-level programming languages: with built-in security measures to create applications.…
Q: Your organisation is attempting to enhance its capacity to generate funds. What type of information…
A: Business intelligence technologies.
Q: Data processing approaches that are now in use in modern systems include what two?
A: answer is
Q: Do you intend to enhance the security of the following URLS (hyperlinks) in any way?
A: Hyperlink A hyperlink is a part of an HTML page that links to another part of the document or to a…
Q: For example, what are the variations in software development in terms of the terms "cohesion" and…
A: Given: We have to discuss what are the variations in software development in terms of Cohesion and…
Q: According to the criteria, which of the following is an example of inappropriate behavior? O An…
A: Software failure: Failure in software may be defined as an inaccurate outcome relative to the…
Q: ole design into many user views while doin
A: As a general rule, a design cycle can help a designer or design group in gaining quick headway from…
Q: What is data sharing? What is a data subject?
A: Answer:
Q: What are the differences between testing strategy and testing methodology?
A: Introduction: The practice of analyzing and validating that a software product or program…
Q: This kind of geometry is known as ring topology. Why not go into more detail?
A: Geometry is a kind of ring topology: Why don't you expand on that A ring topology is a network…
Q: efits of VPN usag
A: A virtual private network (VPN) broadens a private network across a public network and empowers…
Q: A processor may decode encrypted data and system instructions in a variety of methods and then…
A: Introduction: The term "stable cryptoprocessor" refers to a type of computer processor that can…
Q: An automated testing approach has a number of advantages.
A: Introduction: Automated testing is defined as the process of testing software using real-world…
Q: What are the differences between testing strategy and testing methodology?
A: Introduction: The differences between testing strategy and testing methodology are :
Q: What are the specific Page-table requirements?
A: Introduction: What are the specific Page-table requirements?
Q: F(A, B, C, D) = Em(0, 1, 2, X-2, X+1, X+2, X+3, X+5, 15), implement the following function F by…
A:
Q: In computer operating systems, what is the purpose of a thread?
A: INTRODUCTION: An operating system (OS) is software that manages computer hardware and software…
Q: Are there any differences between computer technology and other types of technological innovation,…
A: A computer is an electronic device: that receives, processes, and outputs data. A computer may do a…
Q: What are the three different levels of testing that occur inside a class?
A: answer is
Q: you familiar with the CUDA design languay
A: CUDA (or Compute Unified Device Architecture) is an equal figuring stage and application programming…
Q: Identify two benefits of using electronic mail to communicate in today's society as opposed to…
A: Two benefits of electronic mail to communicate opposed to traditional mail with examples
Q: In a royal casino, there is a lottery at 134 number card. If a person is playing that game, find the…
A: all cards = {12,0,71,101,51,134,0,4,12,0,6,54,98,54} Probability of getting 134.
Q: our understanding of generic does dynamic testing vary fre
A: Static testing is a sort of programming testing that includes testing an application without running…
Q: Does each operating system have its own own partitioning?
A: Introduction Hard drives may be partitioned in a way that operating systems (OS) and file systems…
Q: Where do bugs come from? It's not quite apparent how a piece of software gets into trouble in the…
A: Please find the answer below :
Q: Permutation and Combination Show Solution 1. How many eight-bit strings begins either with a 101…
A: Here in this question we have asked that How many eight-bit strings begins either with a 101 or 111
Q: 5 cents (Z) 10 cents (Y) 25 cents (X) 35 cents (W)
A: Answer is given below-
Q: QUESTION 24 Which command is used to show details about the path that a packet takes from the…
A: Ans.24 a. Ipconfig Shows generally current TCP/IP network setup esteems and invigorates Dynamic…
Step by step
Solved in 2 steps

- Which of the following Visual Basic constants advances the insertion point to the next line? a. Advance b. ControlChars.Advance c. ControlChars.NewLine d. none of the aboveplease created a c++ code regarding this screenshot i add and also please add professional comments in it using the // commandSelect which of Conditional Formatting rules that will display rectangular bars? Select one: a Data Bars b. Highlight Cell Rules c.Color Scales d.Top Bottom Rules
- By using the program below: Kindly Change the color of all elements with the class "colortext", to "red". <!DOCTYPE html> <html> <head> </head> <body> <h1>This is a Heading</h1> <p>This is a paragraph.</p> <p class="colortext">This is another paragraph.</p> <p class="colortext">This is also a paragraph.</p> </body> </html>In your HTML file, please do the following: Add an h1 tag with a class of text-center and add the text of "Lesson 13 Project". Create a div class of container Inside the container, create a div id of test-input Inside the test-input, add the following: input box with an id of isValidInput button with an id of isValidBtn Outside of the test-input, but inside the container, create a paragraph tag with an id of isValidMsg CSS In your stylesheet, please add the following: Set an asterisk with a property of box sizing equal to border box.Set the body with the following properties:set a property of font-family and set it equal to sans-serif.set a minimum height of 100%.set a vertical overflow of hidden.Set a class called text-center and set it to align the text to the center.Create a container class, and add the following properties:set the display property to flexjustify the content to centeralign the items to centerset the height to 100 viewport heightset the flex direction to…The moveVertical and slowMoveVertical commands are good places to start. Use moveHorizontal to move the circle 70 pixels to the left.
- Question 01 Having trouble with the improve section, don't know how to code all the form elements. Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this lineWhich capitalization should be used for the text appearing in check boxes and radio buttons? a. sentence capitalization b. book title capitalization c. either book title capitalization or sentence capitalization d. None of the above.Create a string that has custom kerning (letter spacing) editshare?
- What does the following code do? document.getElementsById("firstLetter").style.fontSize = "18px"; a. Sets the font size of the element called firstLetter to 18 pixels. b. It sets the text of the "firstLetter" tag to "18px". c. It doesn't work because there's no document method called getElementsById().I am trying to write my name with turtle in Google colab, however the code I have here won't work, can someone help me with this Google colab code? import ColabTurtle.Turtle initializeTurtle() Turtle.color('purple') style = ('Courier', 90, 'normal') Turtle.write('Tony Montana', font=normal, align='center') Turtle.hideturtle()Which actions are required to modify the Text attribute of the form?

