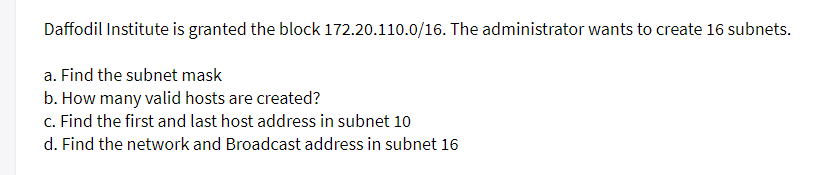
Daffodil Institute is granted the block 172.20.110.0/16. The administrator wants to create 16
Q: When should a firm utilize PaaS and when should they consider IaaS, according to you? Why?
A: Introduction: When should a firm utilize PaaS and when should they consider IaaS, according to you?…
Q: What happens if a process attempts to visit a page that hasn't been cached? What are the phases in…
A: Memory Demand: Memory Demand is calculated using performance counters and represents the amount of…
Q: To improve network quality, talk about metrics in your own terms.
A: To evaluate or improve the performance of your network, you can use numerous distinct indicators to…
Q: What function does TCP/IP serve in local area networks? Let's have a look at two samples.
A: Introduction: Here we are required to explain what function does TCP/IP serve in local area…
Q: Consider a two-link network where Host A is connected to the router by a 1 Mbps link with 10 ms…
A: The answer is
Q: a) You are a new project manager at an IT firm. Your task is to develop an application that is…
A: a) Declared Facts: Need to develop an application for an information system organization where other…
Q: Why would you use a Web Service instead of a traditional application?
A: Web Service Definition Language(WSDL): The Web Services Definition Language (WSDL) is an industry…
Q: Given the expression: 9116-11x -778 0100 10112 = What is the value of x? 07
A: To find the value of X, first we will convert the equation in decimal system. Hexadecimal to…
Q: Jhon and Tom earned money from their first drug contract. There is an N type of dollar such as A1,…
A: Algorithm: First line will contain T, number of testcases. Then the testcases follow. Each testcase…
Q: Do you know how to tell the difference between network diagrams AOA and AON? Explain.
A: Answer
Q: Provide an example of a word processor or presentation software that is open source vs proprietary.…
A: A database management system (DBMS): Is software that enables you to store, modify, extract, and…
Q: What does "The values of exponent term B are continuous rather than discrete" indicate in the…
A: The solution to the given question is: Value of the exponential term B are continuous rather than…
Q: What is Direct Memory Access (DMA)? Describe briefly. In the operating system)
A: DMA- Direct Memory Access. Fundamental to this method is that it primarily allows the input or…
Q: Which method is better, the synoptic or incremental?
A: Introduction: Synoptic formalism (Rationalism) and Incrementalism are two significant schools of…
Q: Decrypt the message MAXLJGTEAX which was encrypted using the affine cipher: f(p) = (5p+6) mod 26
A: The answer is
Q: a) You are a new project manager at an IT firm. Your task is to develop an application that is…
A: a) Facts: We need to design an application for an information system organization in which other…
Q: List and describe all the words related to the quantification of data, such as bit, byte, and…
A: There are many units of information. We will list down some of them units(step2) with It's binary…
Q: explain why you choose time-sharing processing over batch processing.
A: Introduction: Time-sharing allows multiple individuals to utilise a computer system at the same time…
Q: Explain ISA (Instruction Set Architecture) and the several types of ISA (Instruction Set…
A: As part of the abstract concept of a computer, an Instruction Set Architecture - (ISA) outlines how…
Q: A. Modified TRUE of FALSE. Write T if the statement is TRUE and CHANGE the underline word if the…
A: There is only one way to determine whether a business is going to be profitable or not. FALSE
Q: Explain CentOS and its characteristics in terms of server operating systems
A: CentOS Linux is a free and open-source operating framework in light of Red Hat Enterprise Linux. It…
Q: What are some effective strategies for preventing data loss?
A: Here are some strategies to help you prevent them:
Q: How is an embedded computer different from a general purpose computer?
A: Embedded computers are built to perform a particular function: General-purpose computers are…
Q: Explain the importance of operating systems and whether or not it is possible to communicate with a…
A: An operating system is the most important software that runs on a computer. It manages the…
Q: He usually does not -- easily to his competitors. give in O give away
A: He actually does not give away easily to his competitors. Option 2
Q: Question--Identify the management, organization and technology factors affecting adoption of…
A: Answer
Q: Use a normalised histogram to compare and contrast. Surely, a normalised histogram is okay if it…
A: The Advantages of a Normalized Histogram include: This kind of histogram displays the probability…
Q: Discuss how the information system is influenced by the organization.
A: The answer of this question is as follows:
Q: Cryptography Diffie-Helman Key Exchange
A: What is the Diffie-Hellman key exchange? The Diffie-Hellman key exchange was the first widely used…
Q: Discuss how the information system is influenced by the organization.
A: Organisational Influences: Organisational influence refers to an organisation's qualities or…
Q: Explain the characteristics of Ubuntu OS in terms of server operating systems.
A: The above question that is characterstics of ubuntu os in terms of server operating system is…
Q: What are the kernel components of a typical operating system and how do they work?
A: System software: A user interface divides a vast, complicated system into manageable portions, which…
Q: What are some of the most important supplementary terminology linked with the use of Web services?
A: Web services: With HTML, XML, WSDL, SOAP, and other open standards, a web service allows many…
Q: Give examples of real-time operating systems. Describe how it functions differently from a typical…
A: The solution to the given question is: INTRODUCTION A real time operating system, abbreviated as…
Q: What distinguishes the software development process from software modeling? Describe how one aids…
A: Methodology of Software Development: In software engineering, a software process divides development…
Q: What exactly do you mean when you say "MS Word"?
A: Microsoft word is a word processor software ,it was developed by Microsoft in 1983. It is the most…
Q: What is the significance and function of the central processing unit (CPU)? Explain your point of…
A: We must describe the purpose and function of the CPU in order to answer the question. Central…
Q: Can an AES key be encrypted using a shared secret? Defend your response Compare hash function with…
A: Can an AES key be encrypted using a shared secret? Defend your response Compare hash function with…
Q: What are some of the most often used CLI troubleshooting commands for diagnosing and resolving…
A: According to the question CLI command always helps to the network for repair and the diagnosis or…
Q: How can ICT and technology tools assist teaching and learning? Why is it vital?
A: ICT promotes student engagement and information retention in the classroom: Students become more…
Q: Write a C++ program that lets the user guess whether a randomly generated integer would be even or…
A: As per question statement, we need to write c++ program which generates the random number and find…
Q: Alice and Bob use the ElGamal scheme with a common prime q= 131 and a primitive root a = 6. Let…
A: The Answer is in Below Steps
Q: How can a communication be authenticated using a hash value? Is Is recovering the secret key…
A: How can communication be authenticated using a hash value? Answer: Yes, defiantly the communication…
Q: Distinguish hash from MAC. Show how they may be used to authenticate communications. What…
A: Answer: Hash Vs MAC: The principal distinction is applied: while hashes are utilized to ensure the…
Q: What are some of the most often used CLI troubleshooting commands for diagnosing and resolving…
A: At times, time outs, lengthy buffering, and poor quality online calls are all typical in any user's…
Q: What is the difference between asymmetric and symmetric encryption approaches for network data…
A: Asymmetric and Symmetric Encryption: Symmetric encryption encrypts and decrypts an email using a…
Q: Explain how a URL and a domain name are similar and different.
A: URL: The term URL refers to - Uniform Resource Locator. It is used to represent the resource address…
Q: Using a Health band as a real-world example, discuss the advantages and disadvantages of an IoT…
A: 1. Internet of Things :IOT is known as the Internet of Things where things are said to be the…
Q: Is there a specific reason for a release procedure? What is version control, and why does it matter?
A: Asked: Why release procedure. Define Version control.
Q: xactly what do you mean and how do you define "network security?" Justify the use of…
A: Network security is a broad term that covers a multitude of technologies, devices and processes. In…
dont dont dont answer or post existing or copied one sure strict dislike answer if 100% sure else dont dont answer
Step by step
Solved in 2 steps

- THINKING CRITICALLY Which of the following hosts on a corporate intranet are on the same subnet? a. b. c. d.21.) Consider the following configuration. Computer “A” IP address: 172.16.100.100 Subnet mask: 255.255.0.0 Computer “B” IP address: 172.16.200.200 Subnet mask: /16 What should be done to allow these computers to send and receive data to and from each other? A.) Nothing needs to be changed. B.) Delete the subnet mask from each computer. C.) A router must be configured and placed between the two computers. D.) Remove the hub between the two computers and replace it with a switch.Consider the IP address : 157.110.88.0. We need 30 subnets in such a way that each subnet may host up to 64 hosts. i) This address is of which type? ii) How many bits will be required for subnet ID? iii) How many usable subnets will be there? iv) What will be the subnet mask? v) What will be the address of 47th host of 25th subnet?
- 56- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method; What will be the subnet mask of Subnet C? Select one: A. 255.255.128.255 B. 255.255.192.0 C. 255.255.255.240 D. 255.255.255.192 E. 255.255.255.128Given 192.168.31.0 a. How many bits are in the host field for this network? _ b. If we need to set up 30 subnets, how many bits must be used for subnetting? _ c. How many bits are left over that can be used for host addresses? _ d. How many subnets can we create from this? _ total subnet? usable subnet? e. How many hosts could be assigned on each subnet? _ total possible host? Usable hosts? f. What subnet mask will be used? _g. What is the network address for this entire network? _ h. What is the broadcash address for this entire network? _ Show Solution52- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method; What will be the subnet mask of Subnet A? Select one: A. 255.255.255.192 B. 255.255.128.255 C. 255.255.255.128 D. 255.255.192.192 E. 255.255.192.0
- 58- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method What will be the network address of Subnet D? Select one: A. 192.168.15.232 B. 192.168.15.191 C. 192.168.15.112 D. 192.168.15.24055- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method; What will be the network address of Subnet C? Select one: A. 192.16.15.128 B. 192.168.15.191 C. 192.168.15.96 D. 192.168.15.32Given 200.5.1.0/24. Create 10 subnets from the address space given. Answer the followingquestions:(i) How many bits are required to borrow in order to create 10 subnet? How many subnets are created? How many usable host addresses per subnet? Compute the decimal value of the new subnet mask.
- Q5 A network of a class C 250.250.220.0 uses a subnet mask with 30 bit of one's - How many subnets exist with this network?- Write 4 different subnet addresses related to this network with their broadcast addresses.- Take one of the subnets of the previous question and specify 4 valid Host IP addresses lay on this subnet“Daffodil Computers” has granted the block 15.13.180.0/8. The administrator wants to create 32subnets. Do not consider “0” as first subnet. 10I. Find the custom subnet maskII. Find the number of host addresses in each subnetIII. Find the first and last host addresses of subnet 20IV. Find the Network and Broadcast address of subnet 10.57- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method; What will be the range of usable (assignable) host addresses in Subnet C? Select one: A. 192.168.15.64 to 192.168.15.128 B. 192.168.15.97 to 192.168.15.110 C. 192.168.15.140 to 192.168.15.191 D. 192.168.15.128 to 192.168.15.139 E. 192.168.15.193 to 192.168.15.254



