Find the Minimum Hamming distance D(min) of the following code group: 01010 10101 11111 00000
Q: Using journal-style writing, write a summary of your understanding of mindfulness and its importance...
A: Given The answer is given below.
Q: In tinkercad it is requested to use a system that reads an IR keyboard, and if it is pressed: button...
A: #include <LiquidCrystal.h> LiquidCrystal lcd(1,3,4,5,6,7); // defines pins numbers const int t...
Q: * :the output of (Print "a", "b", "c") is ab c abc O O O
A: answer is
Q: How can i convert the temperature in Fahrenheit from the degree celsius which is entered by user in ...
A: PROGRAM INTRODUCTION: Start the PHP tag. Declare and initialize the variable to store the value of ...
Q: What is not true about the kernel in SVM? Select one: a. The kernel is a soft margin where a few "n...
A: Kernel machines are a class of pattern-analysis algorithms, the most well-known member of which is t...
Q: Write a C++ program that contain a menu rto call user defined functions on a one dimendional array :...
A: I give the code in c++ along with output and code screenshot
Q: Solve this attachment
A: Data dependencies are also termed Instruction Hazards. It arises when an instruction is trying to re...
Q: Trace the output. externint p=5%; void main() p=1; printf("%d", p); ans. Compilation error None of t...
A: Given program contains a variable p which is declared as extern int p=5, then in main function the p...
Q: This is how you write a CALL statement that calls a procedure called MyProc in an outside link libra...
A: Introduction: Use the ESQL CALL command to execute a procedure stored in a database. A CREATE PROCED...
Q: In what way would a procedure work if the RET instruction was left out?
A: The ret instruction transfers control to the return address located on the stack. This address is us...
Q: What are the issues that can prevent a transaction processing system from scaling up linearly? In ea...
A: Factors against linear scale up in a transaction processing system Parallel database architecture i...
Q: Write a program to create a new key pair, and then use the new key pair to launch an EC2 instance, w...
A: Lets see the solution in the next steps
Q: Identify five (5) threats to modern security architecture and design and Identify the possible vulne...
A: Five threats are given below: - 1. Spyware: - Typically, spyware tries to attack computers by instal...
Q: In the blocko
A: given - In the blockchain, what is a fork? Describe the two types of forks.
Q: Define the characteristics that are required for test-driven development. In the event that you wish...
A: According to the question essential principles of check pushed improvement TDD and assuming that you...
Q: used for declaration for all forms global O dim form
A: form
Q: What is a good way to quickly find the nearest neighbor to a given query point in an R-tree?
A: What is a good way to quickly find the nearest neighbor to a given query point in an R-tree?
Q: Write a java code to get the number of electrons passing through a heater wi minute, if it carries a...
A: Lets see the solution.
Q: For the following situation, please indicate whether we should focus on having a very low false posi...
A: 1) An inspection for food in a restaurant in which we decide to skip a final test before serving it ...
Q: Write a C++ program that contain a menu rto call user defined functions on a one dimendional array :...
A: Solution: Given, 1- fill the array with integers >20 2- print the content of the array 3- find ...
Q: An attribute is a characteristic or property of an entity. If person is an entity, would the same at...
A: An attribute is a property of an entity that defines the entity. In the question, a person is consid...
Q: I need help with coding this for matlab please. Plotting Discrete-TimeSignals Use stem to plot th...
A: Code: clear all; close all; clc n=-10:10; a1=(n>=0); a2=((n-4)>=0); f=a1-a2 stem(n,f);OUTPUT:-
Q: Comment on the current status of IPV4 and identify the major emerging problems for IPV4 and discuss ...
A: The answer is
Q: Write a php program to take the current room temperature from the user in degree celsius and try to ...
A: Required:- Write a PHP program to take the current room temperature from the user in degree celsius ...
Q: solve problem b y using rogram to remove the ith occu ist where words c an repeat. xample Output: nt...
A: Lets see the solution.
Q: If Moore's Law is to hold, Rock's Law must fal
A: Find the answer with reason given as below:
Q: Relate the layers of TCP / IP Model with layers of OSI Model.
A: Let's understand both of hem separately: TCP/IP: TCP/IP is not a single networking protocol – it is ...
Q: Please match the following situations with a more likely problem of a high bias or a high variance. ...
A: Overfitting is more likely to happen when there will be low bias and high variance. In Overfitting t...
Q: Computer Science A procedure "myproc" was called using jal R13,myproc[R0]. Assume myproc never calle...
A:
Q: This can happen even if the primary (master) copy of a database has a "exclusive lock" on updates. I...
A: In-database replication: It is the process of copying data from a central database to several databa...
Q: Write a JAVA program in which the user enters the initial velocity u, time of travel t, and the acce...
A: Actually, the formula for finding the final velocity is : v=u+at, where v is final velocity, u is in...
Q: When you think about a bank's database, think about how the database system uses "snapshot isolation...
A: Let's see about how the database system uses "snapshot isolation in the next steps in detail
Q: What Is SDLC?
A: This question comes from Software Engineering which is a paper of Computer Science. Let's discuss it...
Q: Why do we focus on conflict serializability instead of the view serializability of a schedule that c...
A: Serializable Schedule : A transaction schedule is serializable if its outcome is equal to the outcom...
Q: stion are there so many different partitioning algorithms in use by operating systems, and why are t...
A: Memory partitioning is the system by which the memory of a computer system is divided into sections ...
Q: What are the issues that can prevent a transaction processing system from scaling up linearly? In ea...
A: This parallel database system aims to boost performance by parallelizing numerous tasks involving da...
Q: What is an unnormalized relation? Is it a relation according to the definition of the word relation?
A: In a database management system, a relation is a collection of interconnected tables or a single tab...
Q: *used for declaration for all forms global O dim form O O
A:
Q: There are blank 3 digit counting numbers that are made using only the odd digits 1,3,5,7,9?
A: Here in this question we have we have asked to make 3 digit numbers from 1,3,5,7,9. Note- here nothi...
Q: If you wanted to know the position of the letter v (i.e. return 2) in the String str containing the ...
A: A String is a pre defined class in Java which has various methods in it to perform the operations on...
Q: d. Perform Shannon-Fano algorithm and display in a table, the count, the entropy, the code, and the ...
A: Shannon-Fano : It is an algorithm is an entropy encoding technique for lossless data compression of...
Q: Identify five (5) threats to modern security architecture and design and Identify the possible vulne...
A: Answer:-
Q: between priva
A: given - Distinguish between private-key and public-key encryption. Include examples of when and why...
Q: Uber's big crash is most likely a failure to assess which of the following aspects of IT architectur...
A: The IT architecture has a lot of aspects like features of a certain domain, security, adaptability, ...
Q: Write a loop to display the powers of 2 exactly as shown below: 1 2 4 16 32 64 128
A: As per answering guidelines since no language mentioned using c++ language.
Q: Solve pr oblem by using PYTHON Program to remove the ith o ccurrence of the given word in list where...
A: n = int(input("Enter number of elements in list: "))lst = []for i in range(0,6): print("Enter ele...
Q: Question:: Describe the TM that accepts the language, L= {w e{a,b,c}* | w contains equal number of a...
A: Given: L = {w belongs to {a,b,c}* | w contains equal number of a's b's and c's} Logic to build Turin...
Q: iv) What will be denoted by the Python statement: chr(ord('Z')) a) 90 b) Z c) z d) A
A: Your answer is given below with an explanation :-
Q: Please convert following figure into a relational schema. In each table, the primary key and foreign...
A: Here entity Branch is a weak entity and therefore it will include primary key of bank as prime attri...
Q: Compare and contrast the advantages of imperative, functional, and declarative programming languages...
A: Introduction: Imperative programming is the earliest programming idea. A piece of software based on...
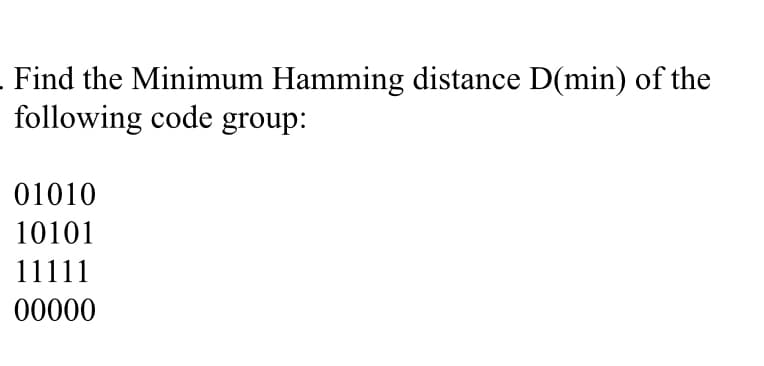
Given 4 codes
01010
10101
11111
00000
In order to calculate the dmin we need to calculate XOR codes of evety pair.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Find the Gray code sequence of 12 code words.For the weighted codes (a) 3,3,2,1 and (b) 4, 4, 3, -2 for the decimal digits, determine all possibletables so that the 9’s complement of each decimal digit is obtained by changing 1’s to 0’s and 0’s to1’sCompute the Hamming distances between the following pairs of n-tuples. a) (11110101), (01010100) b) (1001), (0111)
- Determine the CRC remainder for the data G(x)= 11001010111 and CRC Divisor polynomial P(x)= 101011A repetition code is an [n, 1] Code in which the n - 1 parity bits are repetitions of the information bit. Is this repetition code a linear code ? What is the minimum distance of the code ?please given step by step solution.Compute the Hamming distance of the following code:00100101101011010001011010011110
- Suppose the following Hamming Codes were created using even parity, determine if the code is correct or not. If not correct, find the correct Hamming Code. c.) 010101100011Suppose the following Hamming Codes were created using even parity, determine if the code is correct or not. If not correct, find the correct Hamming Code. 2.) 010101100011Given X = 10002 , Y = 111112 . Find X-Y and Y-X (justify your answer using the complement method).
- Calculate the minimum Hamming distance (d) for the following array of data: {0b001000, 0b010011, 0b101101, 0b111110}A repetition code is an [n, 1] Code in which the n- 1 parity bits are repetitions of the information bit. Is this repetition code a linear code ? What is the minimum distance of the code ?a) Using hamming code with even parity, find the sent message if the original message is 11011101110111011 b)If the received message is 11011001110111011. Using hamming code, show how to isolate the wrong bit.

