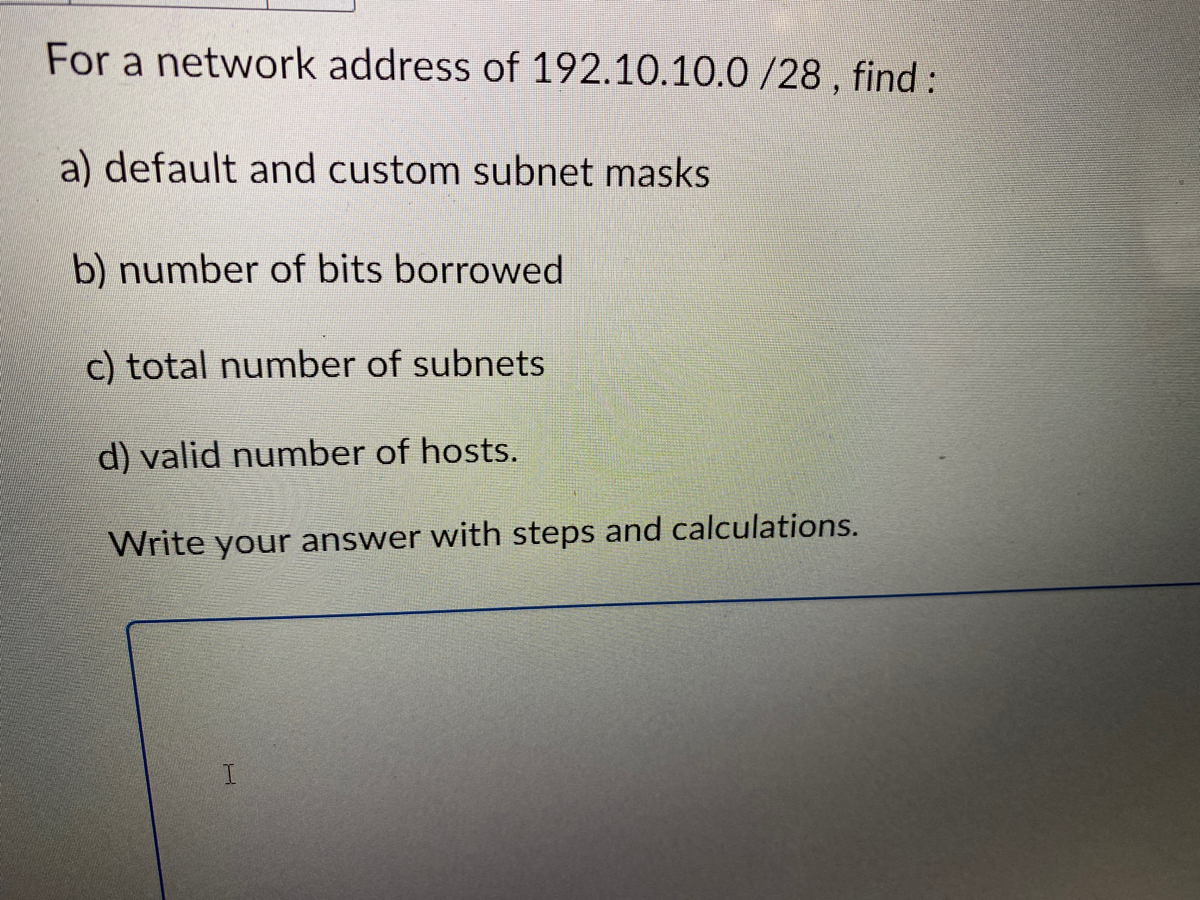
For a network address of 192.10.10.0/28, find: a) default and custom subnet masks b) number of bits borrowed c) total number of subnets d) valid number of hosts. Write your answer with steps and calculations. I
Q: What should be written in Q1? (Adjust nUnits) nUnits = getReverse(nRev); nUnits = 1; nUnits = 0;…
A: B. nUnits = 1
Q: Do you have any suggestions for network topology?
A: Introduction: End users are connected to servers and data centres via network architecture, which…
Q: - Use predecessor instead of successor. - When there are choices between single or double rotate,…
A: A Binary tree is the tree of the data structure at which the each node has the at most the two…
Q: The a. b. is the physical path over which a message travels. MEDIUM SIGNAL
A: The correct answer is given in the below step with an explanation
Q: Your home network consisting of 1 desktop computer, 1 wireless laptop, 1 network printer, 1 wireless…
A: Given that, the network consists of total 3 hosts and 1 router. The router is wireless and there are…
Q: Using 8-bit representation, what is the 2’s complement of the result of ((45 base 10) + (44 base…
A: We have , First Number = 4510 Second Number = 4410 Now , performing the addition of…
Q: The reason why you subscribed the internet plan for cybercafe (the download and upload speed) and…
A: Many people do it because public access locations have better equipment than they do at home, which…
Q: Please translate the following English sentence into a sentence of FOL: use quantifiers "Lucia owns…
A: Quantifiers are a language of fundamental computers that helps in the generation of quantification.…
Q: What can be done to reduce the risk of identity theft?
A: ANSWER IS GIVEN BELOW:
Q: Using emu8086 write a full code that does the following - write your name in the middle of the…
A:
Q: Assume function call below will replace the comment in the main(). What should be the actual…
A: Typdef is a keyword in programming language that provides meaningful names to already esisting…
Q: Frame rate and line rate have what influence on picture quality?
A: The Answer is in step-2.
Q: 3. With the help of program show how to declare and initialise a string in C++ without using the…
A: Solution: Using the constructor-like function in C++, we can initialise a string. The value of the…
Q: • Prompts user to enter 2 values A and B. • If the first number A is less than the second number B,…
A: As per the requirement program is developed. Note: In the question programming language is not…
Q: What is the follow up action after performing each testing? (black box testing and white box…
A: Introduction: Testing is a component of a larger interaction of software verification and approval.…
Q: Indicate five factors that an entity will need to consider when making a decision regarding the use…
A: The question has been answered in step2
Q: An authentication challenge-response mechanism should be shown. With password protection, how much…
A: Start: A question and a response are required to validate a dubious response.The challenge or…
Q: DBMS increases the integrity of data Select one: True O False
A: Permanent records are kept in a variety of files in a typical file-processing system. To extract…
Q: The below is considered as an action: int x=7; Select one: O True O False
A: Answer:
Q: What are the reasons for the organization's desire to implement big data technologies?
A: Introduction: Hadoop and NoSQL are only two examples of the big data technologies that are used in…
Q: What are the best practises for using computer-aided decision-making?
A: Introduction: Computer-aided decision-making innovation, which comes from applications that arrange…
Q: These concepts, "rectification" vs. "repudiation," should be explained.
A: Rectification:The word "rectification" generally refers to the action of making something right; in…
Q: When you insert a graphic into the header and footer of a document to create a watermark, you also…
A: The question has been answered in step2
Q: Write a C program using only stdio.h library that prints asterisk (*) on the screen according to the…
A: SOLUTION:
Q: Access Control Lists are used by firewalls (ACL). Describe what an ACL is and what it usually…
A: Intro Firewalls employ Access Control Lists (ACL). Firewalls employ ACL(access control lists) to…
Q: program provides a simple example of Spliterator. Notice that the program demonstrates both…
A: The Answer start from step-2.
Q: Write a Java program in NetBeans consisting of a Java class with a thread that implements the run()…
A: Answer:
Q: What are the primary functions of an operating system?
A: Introduction: An operating system, often known as an OS, acts as a link or interface between a user…
Q: The development of personal computers and the World Wide Web, for example, has had a significant…
A: Introduction: Usability allows the user to define a system's efficacy, efficiency, and satisfaction…
Q: What should be written in Q3? (computeTrainCost, condition 1) if (fDistance = 5) if (fDistance > 5)
A: C program: C is a general purpose programming language. It was developed by Dennis Ritchie in the…
Q: Backup protection briefly
A: Dear Student, Brief definition of Backup protection is given below -
Q: Assuming a 4-KB page size (4096 bytes), what are the page Numbers and offsets for the following…
A:
Q: Code in a sequence structure and code in a decision (if) structure are distinct.
A: Sequence Structure: A sequence structure may include one or more sub diagrams, sometimes known as…
Q: A computer user finds that his wireless router transmits data at a rate of 75 Mbps (megabits per…
A: ANSWER:
Q: Load the diamonds.csv file, and make 80% of the data in the order of the data as the training data.…
A: CODE:
Q: Please answer Values 1-5. Complete the following Incomplete LMC program by filling out the vacant…
A: An instruction model of the computer called Little Man Computer. It has simple von Neumann…
Q: How can I mine cryptocurrency on my laptop?
A: Introduction: The cryptocurrency may be used without being traced. Another cryptocurrency that may…
Q: Write a complete C program to calculate total pay which includes net salary and bonus. The sample of…
A: Solution code :- #include <stdio.h> // double basicSalary() function to ask user to enter…
Q: The development of personal computers and the World Wide Web, for example, has had a significant…
A: Introduction: By determining whether a system accomplishes the stated goal, usability helps the user…
Q: Given a single link of length 800 Km and transmission speed of 49 Mbps between a client and a web…
A: Answer:- Given : Distance between sender and receiver over a link = 800 Km => 800,000 m (1…
Q: MCQ26: Which of the following is a software process model? a. b. Glassboxing Timeboxing
A: Given question is based on software process model.
Q: 1. Construct a Turing machine for the language L3. Write down the complete 7-touple defining the TM.…
A: Please check the step 2 for detailed solution of the question
Q: Who is "the human computer," exactly?
A: Introduction: A woman is known as "the human-computer," because of her capacity to mentally do…
Q: The text states that MIS is the most important class in the business school. Choose whether you…
A: Information technology is the study of the people ,the technology which is use of the systems which…
Q: In order to build a mobile network, wireless technology must be used in some form at some point…
A: Backhauling is defined as the transmitting of a signal from a remote network to another site and it…
Q: What sorts of issues are most suited to dynamic programming, and why? Give instances or facts to…
A: Given: Why do we choose to use dynamic programming, and under what circumstances might it be more…
Q: Provide a description of an authentication challenge–response scheme while bearing in mind the…
A: Encryption: The fact that challenge-response systems are more secure than password-based systems is…
Q: • Prints on the screen your name, your student ID and your section number. For example, if your name…
A: Here is the approach : In the first part just print everything in format In the second part just…
Q: When would you use static route configuration as a network administrator?
A: Introduction: When there are no additional choices that are necessary or available, static routing…
Q: Use the division algorithm to convert 1278 base 10 to hexadecimal: a. What is the quotient after…
A: c. What is the resulting hexadecimal number after completing the conversion? Solution: The resulting…
Step by step
Solved in 2 steps with 1 images

- 59- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method What will be the subnet mask of Subnet D? Select one: a. 255.255.255.192 b. 255.255.255.248 c. 255.255.192.192 d. 255.255.192.0 e. 255.255.128.25556- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method; What will be the subnet mask of Subnet C? Select one: A. 255.255.128.255 B. 255.255.192.0 C. 255.255.255.240 D. 255.255.255.192 E. 255.255.255.128Subnetting IP Networks - Given the address block 192.168.30.0/24, create an IP addressing scheme that would allow for 2 subnets with 126 host IP addresses per subnet. Compute for the first two subnets only
- Answer the following: a) Rewrite the given IPv4 address using dotted-decimal notation and find the class. 01011110 10110000 01110101 00010101 b) Rewrite the given IPv4 address in binary representation and find the class.1-In a network based on the bus topology, the bus is a non-shareable resource for which the machines must compete in order to transmit messages. How is deadlock controlled in this context? 2-Using 32-bit Internet addresses was originally thought to provide ample room for expansion, but that conjecture is not proving to be accurate. IPV6 uses 128-bit addressing. Will that prove to be adequate? Justify your answer’ (for example, you might compare the number of possible addresses to the population of the world).Consider a web page whose base file is of size S1 = 10 KB. Assume that the web page consists of N = 20 inline objects each of size S2 = 100 KB. Assume that the round-trip time to the web server is T = 100 ms and the bottleneck capacity is C = 10 Mbps. Ignore any packetization delays and header overhead.a. Assuming non-persistent HTTP is used with a single TCP connection, how long does it take to download the web page?b. Assuming non-persistent HTTP is used with 4 parallel TCP connections, how long does it take to download the web page?c. Assuming pipelined, persistent HTTP is used, how long does it take to download the web page? ”Pipelined” means requests for multiple objects can be sent back-to-back on the same connection.d. Assuming non-pipelined, persistent HTTP with 2 parallel TCP connections is used, how long does it take to download the web page? Assume that the 2 parallel connections equally share the total available bandwidth C.
- 7.1 In IEEE 802.11, open system authentication is accomplished via a simple two-way communication. The client requests authentication, which includes the station ID, which is provided by the server (typically the MAC address). A successful or unsuccessful authentication response from the AP/router is received in response to the previous request from the client. For instance, if the client's MAC address has been expressly omitted from the AP/router setup, a failure may occur.a. What are the advantages of using this kind of authentication scheme?b. What are the security flaws in this authentication method and how may they be mitigated?57- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method; What will be the range of usable (assignable) host addresses in Subnet C? Select one: A. 192.168.15.64 to 192.168.15.128 B. 192.168.15.97 to 192.168.15.110 C. 192.168.15.140 to 192.168.15.191 D. 192.168.15.128 to 192.168.15.139 E. 192.168.15.193 to 192.168.15.25442. Though there are practical reasons why we don't complicate our lives this way in the real world, from a theoretical perspective we could borrow non-consecutive bits for subnetting. So, when borrowing the first host bit, the second host bit and the last two host bits (counting from the left of the host bit field) from 172.1.0.0 can you determine the following: g. 1,203rd useable host address?
- A classless address is given as 177.200.180.92/27. What will be the total number addresses available? 64 30 62 32 What is the first useable host address of 168.198.171.72/27? 168.198.171.64 168.198.171.94 168.198.171.65 168.198.171.95Write aprogram to find the ip dotted decimal notation conversion from decimal to binary,octal and hexadecimal and vice versa also find the result of NOT and AND operation of ipv4 adresses. a. 114.34.2.8 Find the result of each operation: a. NOT (22.14.70.34) Find the result of each operation: a. (22.14.70.34) AND (255.255.0.0) ALso develop a program to find classes of ip adress and first and last address,subnet mask also. Develop in java4. [Socket] What is a socket? Suppose a process in Host C has a UDP socket with port number6789. Suppose both Host A and Host B send a UDP segment to Host C with destination portnumber 6789. Will both segments be directed to the same socket at Host C? If so, how will theprocess at Host C know that these two segments originated from two different hosts? 5. [Demultiplex] Define multiplexing and demultiplexing. Briefly explain how TCP demultiplexing isdifferent than UDP demultiplexing. 6. [rdt] Consider a reliable data transfer protocol that uses only negative acknowledgments.Suppose the sender sends data only infrequently. Would a NAK-only protocol be preferable to aprotocol that uses ACKs? Why? Now suppose the sender has a lot of data to send and the end-to-end connection experiences few losses. In this second case, would a NAK-only protocol bepreferable to a protocol that uses ACKs? Why?

