9. Matrices can be used to send encrypted messages. Say you have a message matrix M and an encryption matrix E. The encrypted message will be the product of those two matrices, i.e. A = EM. In the matrix A, the numbers of M will be mangled with those of E. Unencrypting the message requires performing the reverse operation to retrieve M from A. You have been sent an encrypted message: A = m - 20 -m+ 24 and two possible encryption keys E1 = t - 5v a - 5e a +6e -t+6v (18). 1 E₂ = -8 3 h-5a -h+6a) 4 21 16 -2 1 (a) Without performing any calculation, determine which of the encryption keys was used to encrypt the message. (b) Decrypt the message, i.e., find M from A using either E₁ or E2 in an appropriate way.
9. Matrices can be used to send encrypted messages. Say you have a message matrix M and an encryption matrix E. The encrypted message will be the product of those two matrices, i.e. A = EM. In the matrix A, the numbers of M will be mangled with those of E. Unencrypting the message requires performing the reverse operation to retrieve M from A. You have been sent an encrypted message: A = m - 20 -m+ 24 and two possible encryption keys E1 = t - 5v a - 5e a +6e -t+6v (18). 1 E₂ = -8 3 h-5a -h+6a) 4 21 16 -2 1 (a) Without performing any calculation, determine which of the encryption keys was used to encrypt the message. (b) Decrypt the message, i.e., find M from A using either E₁ or E2 in an appropriate way.
Linear Algebra: A Modern Introduction
4th Edition
ISBN:9781285463247
Author:David Poole
Publisher:David Poole
Chapter3: Matrices
Section3.7: Applications
Problem 41EQ
Related questions
Question
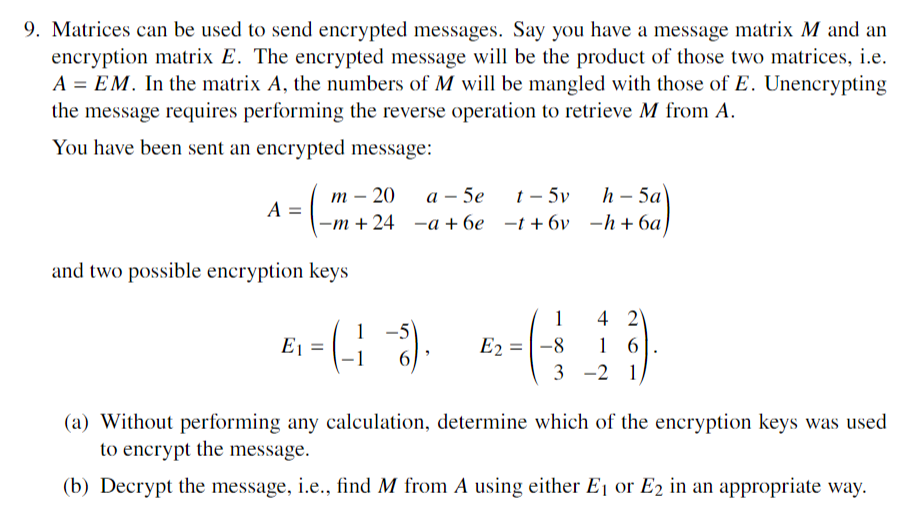
Transcribed Image Text:9. Matrices can be used to send encrypted messages. Say you have a message matrix M and an
encryption matrix E. The encrypted message will be the product of those two matrices, i.e.
A = EM. In the matrix A, the numbers of M will be mangled with those of E. Unencrypting
the message requires performing the reverse operation to retrieve M from A.
You have been sent an encrypted message:
A =
m - 20
-m+ 24
and two possible encryption keys
E1 =
t - 5v
a - 5e
a +6e -t+6v
(18).
1
E₂ = -8
3
h-5a
-h+6a)
4 21
16
-2 1
(a) Without performing any calculation, determine which of the encryption keys was used
to encrypt the message.
(b) Decrypt the message, i.e., find M from A using either E₁ or E2 in an appropriate way.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 5 steps

Follow-up Questions
Read through expert solutions to related follow-up questions below.
Follow-up Question
for part b), how can you multiply the E1^-1 and A as they are not the same size matrix? is that possible?
Solution
Follow-up Question
for part (a) i don't understand how e2 can be used as the encryption key as the dimensions don't match either of the keys given as the message is a 2x4, while the keys are 2x2 and 3x3. they arent 2x4, so how could either of them be used?
Solution
Recommended textbooks for you

Linear Algebra: A Modern Introduction
Algebra
ISBN:
9781285463247
Author:
David Poole
Publisher:
Cengage Learning

Algebra & Trigonometry with Analytic Geometry
Algebra
ISBN:
9781133382119
Author:
Swokowski
Publisher:
Cengage
Algebra for College Students
Algebra
ISBN:
9781285195780
Author:
Jerome E. Kaufmann, Karen L. Schwitters
Publisher:
Cengage Learning

Linear Algebra: A Modern Introduction
Algebra
ISBN:
9781285463247
Author:
David Poole
Publisher:
Cengage Learning

Algebra & Trigonometry with Analytic Geometry
Algebra
ISBN:
9781133382119
Author:
Swokowski
Publisher:
Cengage
Algebra for College Students
Algebra
ISBN:
9781285195780
Author:
Jerome E. Kaufmann, Karen L. Schwitters
Publisher:
Cengage Learning

Elementary Linear Algebra (MindTap Course List)
Algebra
ISBN:
9781305658004
Author:
Ron Larson
Publisher:
Cengage Learning

College Algebra
Algebra
ISBN:
9781305115545
Author:
James Stewart, Lothar Redlin, Saleem Watson
Publisher:
Cengage Learning