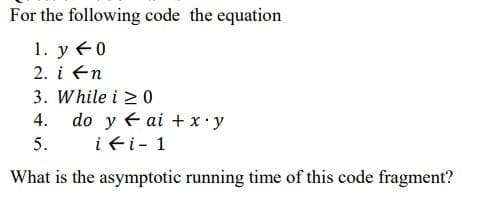
For the following code the equation 1. y 40 2. i fn 3. While i 20 4. do y ai + xy i fi- 1 5. What is the asymptotic running time of this code fragment?
Q: Define how Internet of Things protocols are standardized. When analyzing the IoT, it is useful to…
A: Introduction: Standardization is one of the most crucial obstacles in the progress of the Internet…
Q: Provide an explanation of how one goes about acquiring and archiving files in Microsoft World.
A: Introduction An archive is a collection of data that has been relocated to a repository for…
Q: Most IP datagram reassembly algorithms have a timer to avoid having a lost fragment tie up…
A: The receiver will have no record left of fragments with this identifier, so it will buffer it,…
Q: How many times will the loop below repeat? for (int i = 1; i <= 10; i+=2) { } //Some codes...
A: Background information: For loop is utilised when we want to replicate the execution of a piece of…
Q: 4. Convert the following hexadecimal numbers to their binary equivalents: a. 1C b. 1F.C C. C67 d.…
A: Answer the above question are as follows
Q: Q3. The given coordinates are (0,0), (0,2),(2,0),(2,2) for representing a rectangle/square ,you are…
A: To execute x- and y-shearing on the provided object is the query. old square/rectangle corner…
Q: Chef loves lucky numbers. Everyone knows that lucky numbers are positive integers whose decimal…
A: Input/Output Parameter: The first line contains a single positive integer T, the number of test…
Q: How about listing three options for minimizing your time spent sitting in traffic? How do you tell…
A: Institution: US PIRG reported in 2013 that the average amount of miles travelled by the typical…
Q: Describe the multiple subsystems that work together to form the Internet of Things (IoT).
A: Introduction: The Internet of Things consists of two main parts. a thing or item that you want to…
Q: Consider an input image of shape 512 X 512 X 3. You run this image in a convolutional layer of CNN…
A: If we use N×N×N3, a f×f×3filter, a bias, and a "k" number of filters in CNN. The outcome will then…
Q: What is the type of the object of the evt function parameter in the following JavaScript code.…
A: Introduction: In this question, an event listener is given and we have to choose the correct…
Q: With the AVR ATmega16 microcontroller, a circuit has a servomotor (PC0), three pushbuttons, two…
A: The answer is given in the below step
Q: A seven-story office building has 15 adjacent offices per floor. Each office contains a wall socket…
A: What is LAN? A local area network is a computer network that interconnects computers within a…
Q: Architecture's advantages include... Compare a project with and without architecture. How will it…
A: Project-planning for softwareA software project is an extensive series of programming tasks.…
Q: Why is it that the start and stop bits can be eliminated when character interleaving is used in…
A:
Q: A company has two locations: a headquarters and a factory about 25 km away. Inc factory has four…
A:
Q: Here, you may choose from two different theories: the Path-Goal Theory and the Leader-Member…
A: As stated in the introduction: a leader is someone who encourages people to work hard, assists them…
Q: Problem 1.8 The following code segment, consisting of six instructions, needs to be executed 64…
A:
Q: What is the correct DOM method to update the src attribute value of the HTML img element. Please…
A: The textContent property alters or retrieves the text content for the specified node and all of its…
Q: Explain the function of scrambling in the context of digital-to-digital encoding techniques.
A: Modern data communication techniques employ scrambling, a digital encoding technique that helps with…
Q: How many times will the loop repeat? for (int x = 10; * >= 1; x++) ( } //Some codes...
A: Introduction: In this question we need to show the programming approach and solve the question which…
Q: A company has two locations: a headquarters and a factory about ɔ km away. The factory has four…
A: Here is the company is considering installing TDM equipment so that only one line with be needed.
Q: Which part of a client/server setup really handles the data storing function?
A: introduction: All computers have specific roles in this design. Data is provided and stored by a…
Q: Chef loves lucky numbers. Everyone knows that lucky numbers are positive integers whose decimal…
A: Input-Output: The first line contains a single positive integer T, the number of test cases. T test…
Q: Q6: Consider the following segment table: What are the physical addresses for the following logical…
A: A) <1,120> Here segment number is 1 For segment #1, the limit is 100<120 So it's a segment…
Q: Indicate whether each of the following statements is true or false and justify your answer with…
A: The CPU computations and I/O operations cannot be overlapped in a multiprogrammed computer- "FALSE"…
Q: Consider a two-link network where Host A is connected to the router by a 1 Mbps link with 10 ms…
A: The answer is given in the below step
Q: What's wrong with expressions such as necessary prerequisite and small in size?
A: Answer is
Q: Just what are the upsides of adopting design patterns in software development? What are three…
A: Answer is given below
Q: Define a situation where magnetic stripe cards are insufficient for authentication and smart cards…
A: Access to a resource is controlled using physical, electronic authorization devices called ICC or IC…
Q: 1. Calculate the bandwidth-delay product for the following networks: (1) T1 (1.5 Mbps). (2) Ethernet…
A:
Q: Architecture's advantages include... Compare a project with and without architecture. How will it…
A: Project-planning for software: A software project is an extensive series of programming tasks.…
Q: Consider an input image of shape 512 X 512 X 3. You run this image in a convolutional layer of CNN…
A: The correct answer for the above mentioned question is given in the following steps for your…
Q: When it comes to software development, what role do design patterns play? Do you have a particular…
A: A repeatable design pattern for software engineering response to a frequent problem in software…
Q: When it comes to software development, what role do design patterns play? Do you have a particular…
A: introduction: A repeatable design pattern for software engineering response to a frequent problem in…
Q: Why have object-oriented techniques taken off with the systems developer community?
A: Several factors have led to the need for system engineers to use an object-oriented methodology for…
Q: Which of the following function signatures could be used as an overload of the >> operator as a…
A: The above question is solved in step 2 :-
Q: USER INTERFERENCE QUESTION Imagine that you’ve been tasked with redesigning (you being a…
A: 1. What is the user (you, the redesigner) trying to accomplish? Alter the website's aesthetic.…
Q: Chef loves lucky numbers. Everyone knows that lucky numbers are positive integers whose decimal…
A: Input/Output Parameter: The first line contains a single positive integer T, the number of test…
Q: Answer in C++ only In order to expand its reach to the outer universe and ensure universal peace,…
A: Find Your Code Below
Q: How much do the benefits of object-oriented analysis and design outweigh those of more conventional…
A: Introduction: OOAD, or object-oriented analysis and design, is a technical approach that makes use…
Q: Cryptocurrencies and the blockchain are currently very hip. Outline the impact of blockchain…
A: Given: A blockchain is a distributed ledger records all of the transactions that take place inside a…
Q: QUESTION 20 In RC4, what is the size of array S in term of bytes? QUESTION 21 181 and 211 are…
A:
Q: Why did the creators of the first version of Linux decide to create a non-preemptible kernel? What…
A: Introduction: One is DOS-based and non-preemptive. It was built this way for devices without…
Q: What are the advantages of object-oriented system analysis and design over competing approaches?
A: introduction:Benefits of object-oriented design and analysis include:Reusability of code This will…
Q: In this section, we will provide a quick overview of the two primary roles that an operating system…
A: Introduction: Running System: It is computer system software that runs on a computer. An operating…
Q: copy else report.
A: First main class is defined that implements runnable which is actually interface that is used for…
Q: Where does Model-View-Controller fit into the bigger picture of what makes up modern online…
A: MVC is an architectural paradigm that divides an application into three fundamental logical…
Q: Cryptocurrencies and the blockchain are currently very hip. Outline the impact of blockchain…
A: A blockchain records all group transactions decentralised. Members may confirm transactions without…
Q: Most IP datagram reassembly algorithms have a timer to avoid having a lost fragment tie up…
A: The fourth and final fragment is considered by the receiver as a new datagram. This fragment is…
Step by step
Solved in 2 steps

- (Program) Write a program that tests the effectiveness of the rand() library function. Start by initializing 10 counters, such as zerocount, onecount, twocount, and so forth, to 0. Then generate a large number of pseudorandom integers between 0 and 9. Each time 0 occurs, increment zerocount; when 1 occurs, increment onecount; and so on. Finally, display the number of 0s, 1s, 2s, and so on that occurred and the percentage of time they occurred.Copy and simulate the given code below:c++ Implement a function that recursively calculates the nth number in the Fibonacci sequence of numbers. The Fibonacci sequence starts at 0 and 1. Each number thereafter is the sum of the two preceding numbers. This gives us the following first ten numbers: 0,1,1,3,5,8,13,21,34, .... Input Expected output0 01 17 139 34
- The goal is to rewrite the function, below, such that passes in a different list of parameters, particularly eliminating the need to pass low and high for each recursive call to binary_search. defbinary_search(nums,low,high,item): mid=(low+high)//2iflow>high:returnFalse #The item doesn't exist in the list!elifnums[mid]==item:returnTrue# The item exists in the list!elifitem<nums[mid]:returnbinary_search(nums,low,mid-1,item)else:returnbinary_search(nums,mid+1,high,item) The new function should be prototyped below. The number of changes between the given version, and the one requested is not significant. defbinary_search(nums,item):pass# Remove this and fill in with your code Tip: If you consider that high and low are used to create a smaller version of our problem to be processed recursively, the version requested will do the same thing, just through a different, more Pythonic technique.How do I write the code for Fibonacci Function in C program? This is done in Macbook Terminal in Linux! I need to only print out by 5 each Fibonacci number (0, 5, 10, 15, 20, 25, 30, 35, 40, 45) and this code needs to be written using recursion. The Fib() function should return an unsigned long, which is the final calculation of the Fibonacci sequence sent to it. So, Fib(5) should return the value 5. Please include the output resultsEstimate the execution time of the following code:MOV DI, FHAgain: ADD [1234H+DI],ALDEC DIJNZ Again
- Write a code in C++ that calculates the times for each of the algorithms (functions). The code must execute the result showing the largest size n of each algorithm (function) that can be solved in time tWhat is the big-O behavior of the following code segment? Explain. i = n; while ( i > 0 ) { for (j=1; j<n; ++j ) { . . . } i = i / 2; }Show that the given argument is either valid or invalid using resolution. If Sally does her homework, people call Sally a wimp. However, nobody calls Sally a wimp. Therefore, Sally doesn’t do her homework.
- Determine the order of growth of the following snippet of code:The answer must be a Racket Code snapshot with output with the correct answer or a Downvote will be done and the answer Reported to Chegg for investigation Finish the Code bellow for Racket function named (n-list? obj) that takes one argument, returns true if and only if obj is an n-list. n-list? should be mutually recursive with the function num-expr?, which returns true if its argument is a number expression and false if not. (define n-list?(lambda (obj))) in Racket codePlease explain Crime Wave more clearly for me please there's a picture of the decription and also please comment on each line if possible on the code below to for me to have a better understanding of what each line is doing. It is in C++. Please also give the space and time complexity and the reason why. #include <stdio.h>#include <string.h>#include <math.h>#define eps 1e-6double W[105][105];int N, M;int mx[105], my[105]; // match arrdouble lx[105], ly[105]; // label arrint x[105], y[105]; // used arrint hungary(int nd) { int i; x[nd] = 1; for(i = 1; i <= M; i++) { if(y[i] == 0 && fabs(W[nd][i]-lx[nd]-ly[i]) < eps) { y[i] = 1; if(my[i] == 0 || hungary(my[i])) { my[i] = nd; return 1; } } } return 0;}double KM() { int i, j, k; double d; memset(mx, 0, sizeof(mx)); memset(my, 0, sizeof(my)); memset(lx, 0, sizeof(lx)); memset(ly, 0, sizeof(ly));…

