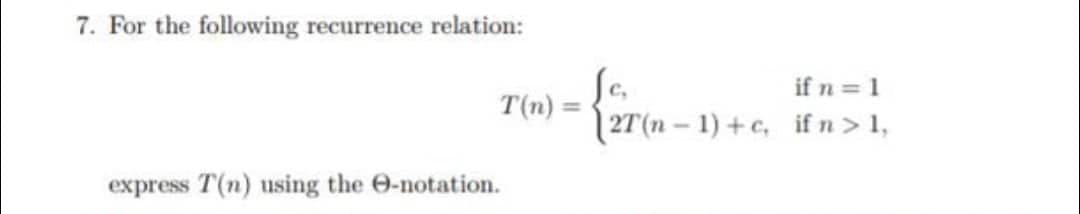
For the following recurrence relation: express T(n) using the e-notation. T(n) = if n = 1 {2T(n- 2T(n-1)+c, if n > 1,
Q: Is there any other method for Peter to avoid password loss other employing key recovery?
A: Introduction: A passphrase is similar to a password. A password, on the other hand, is often used to…
Q: 2. Consider the following network address: 209.15.6.0/28
A: The answer is
Q: Given the Heap in the original state (before running Build Max Heap) as [10, 2, 20, 13, 1, 5, 6, 7,…
A: Task : Given the data values : 10,2,20,13,1,5,6,7,9
Q: What distinguishes a Type 1 hypervisor from a Type 2 hypervisor?
A: Introduction: A hypervisor is a piece of software that allows you to build virtual computers. An…
Q: Do you know what it means to be "debugged?" For testing, what is the connection?
A: Debugging is a multistep process in computer programming and engineering that includes recognizing a…
Q: Does Amazon Web Services work for businesses?
A: answer is
Q: What is the hexadecimal value of the binary number 1101011?
A: => i have provided my logic in step-2.
Q: You've been asked to prepare and present a case to nontechnical management for hiring a system…
A: Introduction Given that we have been asked to prepare and deliver a presentation to a non-technical…
Q: All characters are alphabetical characters and a certain character won't exist more than once in its…
A: Nested for loops need to be used to solve this problem. Finally using selection sort the char array…
Q: What are the outcomes of conceptual data modelling?
A: Introduction: There are three types of data models in database management systems:
Q: uppose you need to store data for a very large number of students in MongoDB. Suppose that the data…
A: Storing Nested Data Structures Perhaps the most powerful feature of document databases is the…
Q: Which element has the greatest memory address?
A: The number of elements in the given array is 6. All the elements are placed in rowwise manner in…
Q: to Microsoft Excel 2016. Which feature in Excel 2016 do you find most useful? In a few phrases,…
A: Word 2016, similar to each past incarnation of this much-adored Office staple, adds a couple of new…
Q: Constraints All characters are alphabetical characters and a certain character won't exist more than…
A: We need to write a c program to find unique characters of 2 arrays.
Q: Assembly language instructions may be optimized by writing compilers and assemblers that rearrange…
A: Assembly language is a kind of programming language that may be used to communicate directly with…
Q: What were the THREE primary reasons you chose Microsoft Excel over the competition?
A: answer is
Q: Wireless networks' role in today's emerging countries, particularly in Africa, should be addressed.…
A: Development: Phone users may access real-time data while roaming the perimeter of your organization…
Q: nclude some of the choices to be taken, the proper business model, payment alternatives, and the…
A: Actually, various ways for establishing e-commerce over the Web are provided below: E-commerce…
Q: Malicious traffic may be redirected across VLANs, which is one method of infiltrating a network.…
A: Introduction: A virtual local area network (VLAN) shares a physical network while creating virtual…
Q: You've been employed as a project manager at an information technology company. Your objective is to…
A: On larger and more complex projects, an undertaking controls group that focuses on both cost and…
Q: SCENIRO :-FOR HEALTH CARE CLIENT YOU ARE DESIGNING and developing a platform that caters to…
A: - We need to select the service with end to end security. In end to end security, the data of the…
Q: Computers create heat when they work. Is there anything you'd like to know about computer cooling…
A: Introduction: Computers are powered by electricity. Computer circuits have electrical resistance.…
Q: Why is it always preferred to have a balanced dataset?
A: Your answer is given below. Introduction :- A balanced dataset is the one that contains equal or…
Q: Write a C++ program to convert temperature in degrees Fahrenheit to degrees Celsius. Your program…
A: Algorithm for temperature conversion Declare variable temp and insert temperature in Fahrenheit .…
Q: "Mpho is very excited about the new information system to be built for his spaza shop. In this…
A: - We have to talk to Mpho about a database and benefits of database for Mpho's shop.
Q: Conduct an analysis of the effect of cloud computing and Web 2.0 technologies.
A: Introduction: The primary goal of Web 2.0 is to improve the interconnectedness of Web applications…
Q: Player Team W L ERA SO/IP HR/IP R/IP Verlander, J DET 24 5 2.40 1.00 0.10 0.29 Beckett, J BOS 13 7…
A: Explanation: This is your regression model. R/IP = β0 + β1 SO/IP + β2 HR / IP + ε Null hypothesis :…
Q: Why would the search process used in the text to solve the eight-puzzle not be applicable in cases…
A: Please find the answer below in second step:-
Q: What are the many methods of debugging?
A: A debugger, sometimes referred to as a debugging tool or debugging mode, is a tool that may be used…
Q: a) What is the 5-bit 2's complement of -X?
A: The answer is
Q: a write through cache coherency policy, will either of the above organizations make a difference in…
A: A cache is organized as a 4 way set associative cache Each set's cache line consists of 4 words…
Q: What exactly do you mean when you say "web pages"?
A: Web Pages: A web page is a basic document that a browser may view. HTML is the language used to…
Q: Microsoft Excel is the spreadsheet application of choice for you, therefore please outline three…
A: Here are some points:
Q: Distinguish the roles, technology, and management practises of wide-area and local-area networks.…
A: LAN: A local area network connects computers and peripherals in a school, laboratory, house, or…
Q: A web server is a special kind of computer that is used to store and manage online pages.
A: Web Server: A web server is a computer that manages and hosts websites. It's a computer software…
Q: Is the word "debugging" relevant in the context of software development?
A: Please check the step 2 for meaning of debugging relevant to the software development
Q: To collect and save this data, why should I use Access instead than Excel?
A: here in the question ask for why we use Access instead of Excel. i have given some of my point of…
Q: 1. Predict the output from the following d a) 1 F=? 0 MUX 0 1 T 1 0
A: Here in this question we have given a multiplexer and we have asked to find the output of this…
Q: What are the deep web's benefits for businesses that depend on information systems?
A: Given: Information management systems (or management information systems) are corporate tools that…
Q: 1. Design a page that outputs the following: Enter your First name Enter your Last name Get Value 2.…
A: Code Html + JavaScript validation: <!DOCTYPE html> <html lang="en"> <head>…
Q: In your own words and with examples (to receive full credit), contrast table-based and model-based…
A:
Q: Make the code output sentence starts with a capitalization, and ends with a period. public class…
A: Send your complete code. I will answer. Have a great day.
Q: On her computer, a student is doing research for an assignment. Is she mainly an operator at the…
A: A brief overview: She mostly operates at the network edge, since the link between the client and…
Q: Is end-to-end encryption of data and connections possible? What advantage does this provide? Give an…
A: - We need to talk about end to end encryption and it's advantages.
Q: Briefly describe the BFS algorithm's usage of colour codes. Describe the meaning of each colour in…
A: Algorithm of Breadth First Search (BFS): It's a graph traversal method that begins at the root node…
Q: Microsoft Excel is utilised widely in the healthcare industry in how many ways, and what are the…
A: - We need to talk about microsoft excel being used in healthcare industry.
Q: It is critical to provide a list of the most common network topologies. Which one do you believe is…
A: Topologies: Topology is a geometric depiction of how computers are related to one another. There…
Q: Is it possible to encrypt an AES key using a shared secret? Justify your answer Consider the hash…
A: Introduction: The Advanced Encryption Standard (AES) is a symmetric block cypher that the United…
Q: Explain CentOS and its characteristics in terms of server operating systems
A: CentOS Linux is a free and open-source operating framework in light of Red Hat Enterprise Linux. It…
Q: When establishing our tables in Microsoft Access, which model should we utilize to guide us?
A: Microsoft Access is a database management system. It is a relational database management system. To…
Step by step
Solved in 2 steps with 1 images

- Exercise 4 Given the following recurrence relationT(1) = −1 T(2) = 7 T(n) = −4T(n − 1) − 3T(n − 2) for n ≥ 3 Indicate a methodology you can use to evaluate the closed form expression Provide the closed form expression and show the procedure to obtain itConsider following recurrence relation. What will be the number next in series in place of question mark? 0, 3, 8, 15, 24, 35, 48, ?Could you tell a step by step procedure of finding a super key for A relation R(A,B,C,D, E) having FD's AB → D, AC → E, BC → D, D → A, and E → B?
- Convert the following relation to 2NF, and then to 3NF. Show both conversions. (h, n, c, a, f, k, p, r, g, i, m, b, o, d, j, l, s, e) Functional Dependencies: p → j m, b → l h → g n → p n → o c → i n → j p → o h → d s → e a → rNOTE: This is a multi-part question. Once an answer is submitted, you will be unable to return to this part. Let an be the number of bit strings of length n that do not contain three consecutive 0s. Identify the initial conditions for the recurrence relation in the previous question. (You must provide an answer before moving to the next part.) a0 = 1, a1 = 2, and a2 = 4 a0 = 1, a1 = 2, and a2 = 3 a0 = 2, a1 = 1, and a2 = 4 a0 = 2, a1 = 1, and a2 = 3give a recurrence relation that describes the sequence, answer both boxes.
- The p operation eliminates duplicate tuples in the resulting relation. So: p Gender, Salary (EMPLOYEE); If several female employees have salary SEK30.000; only a single tuple would have been retrieved.recurrence relation recurrence relationrecurrence relationFor each of the following pairs of expressions, give instances of relations thatshow the expressions are not equivalent. ΠA(r − s) and ΠA(r) − ΠA(s).
- 36. In a relation a. Ordering of rows is immaterial b. No two rows are identical c. a and b both are true d. None of theseDevelop recurrence relations for the last 3 columns of table 1. Use the recurrence relation you developed to complete the table for these months: • Month 59 • Month 60 • Month 61 • Month119 • Month 120 • Month 121 Show your calculations and completed table.Consider the following parameters of a relation r (A, B, C) in which A be the primary key. nr = 20000 V (B, r) = 120 max (C, r) = 500 min (C, r) = 0 Estimate the size of the following selection operations. a)σ A = k (r) b)σ A = k1 ∨ B = k2 (r) c)σ C >= Z ∧ C <= 105 (r)



