For the given allocation and max below, what is the need matrix? Allocation A 3 3 2 R S 2 C 1 1 1 D 4 1 0 2 5 3 3 4 6 Max A B 5 3 2 D ए
Q: What is network virtualization, and how does it facilitate the creation of virtual networks?
A: Network virtualization is a technology that allows the creation of multiple virtual networks, also…
Q: How does virtualization contribute to resource optimization and cost savings in data centers?
A: Through the use of virtualization technology, computer resources like servers, storage, and…
Q: Discuss the role of virtualization in disaster recovery and business continuity planning.
A: In the ever-changing landscape of technology, disaster recovery (DR) and business continuity…
Q: Describe the concept of tiered storage and its benefits in optimizing data access.
A: The concept of storage is based on the recognition that not all data is equal and diverse types of…
Q: Explain the principles of tiered storage and automated storage tiering in enterprise storage…
A: Data Tiering and Automated Storage Tiering are strategies used in enterprise storage systems to…
Q: Discuss the concept of tiered storage and the use of SSD caching in storage systems. How does this…
A: Tiered storage is a data management strategy that classifies data into different tiers based on its…
Q: How does HTTP (Hypertext Transfer Protocol) differ from HTTPS (HTTP Secure), and what are their use…
A: HTTP (Hypertext Transfer Protocol): A common protocol for data transport between a web server and a…
Q: Discuss the role of hypervisors in virtualization and categorize them into different types.
A: A hypervisor, sometimes referred to as a virtual machine monitor (VMM), is a layer of hardware or…
Q: Discuss the concept of live migration in virtualized environments and its impact on system…
A: A crucial component of virtualized systems is live migration, which permits the transfer of an…
Q: What are the main benefits of server virtualization in a data center environment?
A: A data center environment is where a ton of data is handled, coordinated, and put away. It comprises…
Q: How does ICMP (Internet Control Message Protocol) contribute to network troubleshooting and error…
A: An essential network protocol for issue reporting and network troubleshooting is ICMP (Internet…
Q: Discuss the various types of optical storage devices, such as CD, DVD, and Blu-ray, and their…
A: Optical storage devices are data storage mediums that use laser technology to read and write data.…
Q: Explore the concept of containerization and how it differs from traditional virtualization. Provide…
A: Containerization and traditional virtualization are both technologies used in the world of IT to…
Q: Explain the importance of cache memory in storage devices and how it improves overall system…
A: Cache memory is vital for both storage devices and system’s efficiency. A little fast memory that…
Q: Describe the concept of Infrastructure as Code (IaC) and its role in automating system management…
A: Infrastructure, as Code (Isac) is a concept in the field of computer science and system…
Q: Explain the basic structure and functioning of the Internet, including the role of ISPs and DNS.
A: The Internet, a global network of networks, has become an integral part of modern life, connecting…
Q: Describe the concept of tiered storage and the management of data across different storage devices.
A: Tiered storage, also referred to as storage is a strategy used for organizing and managing data…
Q: What is Network Attached Storage (NAS) and how does it differ from Storage Area Network (SAN)?…
A: In the following steps, I have provided complete answer to the question....
Q: Define tape storage and its use in long-term data archiving. What are the characteristics that make…
A: Tape storage, in the realm of computer science and data management, is a venerable yet highly…
Q: age Queuing Telemetry Tran
A: MQTT stands for Message Queuing Telemetry Transport. MQTT is a lightweight messaging protocol that…
Q: Emerging storage technologies such as Non-Volatile Memory Express (NVMe) and Storage-Class Memory…
A: NVMe is a high-speed and efficient storage protocol and interface designed for…
Q: Explore the concept of NVMe (Non-Volatile Memory Express) storage technology and its impact on…
A: In the following steps, I have provided complete answer to the question........
Q: Explore the concept of live migration in virtualization. What are the prerequisites for live…
A: Live migration is a crucial feature in virtualization that allows for the seamless movement of a…
Q: Containerization and virtualization are two related but distinct concepts. Explain the differences…
A: Containerization:A containerization is a lightweight form of virtualization that allows you to…
Q: What is a NAS (Network-Attached Storage) device, and how does it differ from a SAN (Storage Area…
A: This question comes from computer storage and data management which is a topic in Computer…
Q: How does cloud storage work, and what are the key providers in the cloud storage industry? What are…
A: Data is sent and put away on far-off storage frameworks utilizing cloud storage, a help model that…
Q: What is the role of a virtual machine monitor (VMM) in virtualization? How does it enable the…
A: 1) A Virtual Machine Monitor (VMM), also known as a hypervisor, is a software layer that allows…
Q: What are the key considerations in selecting an appropriate storage device for a specific use case,…
A: When it comes to selecting the storage device for a purpose there are several key factors that need…
Q: Describe the importance of remote wipe and lock features in mobile device management. How do they…
A: In today's fast-paced digital world, the use of mobile devices has become ubiquitous, both in…
Q: Discuss the role of Magnetic Tape in data storage and its use in archival and backup scenarios.
A: In the ever-expanding digital landscape, the need for efficient and reliable data storage solutions…
Q: What are the challenges associated with managing and monitoring virtualized environments, and how…
A: Managing and monitoring virtualized environments has become an integral part of modern IT…
Q: What is virtualization sprawl, and how can it be mitigated in a virtualized environment?
A: The process of creating virtual instances or representations of physical resources, such servers,…
Q: Explain the role of a hypervisor in virtualization. What are the primary responsibilities of a…
A: Hypervisors play a role in virtualization technology by acting as a layer between physical hardware…
Q: What are the main types of storage devices commonly used in modern computing, and how do they differ…
A: Modern computing relies on a variety of storage devices, each with different characteristics in…
Q: Describe the concept of user and group permissions in file and system management.
A: In the intricate world of file and system management, user and group permissions stand as the…
Q: Discuss the concept of shingled magnetic recording (SMR) in hard drives and its impact on storage…
A: Shingled Magnetic Recording (SMR) is a significant advancement in hard drive technology that has had…
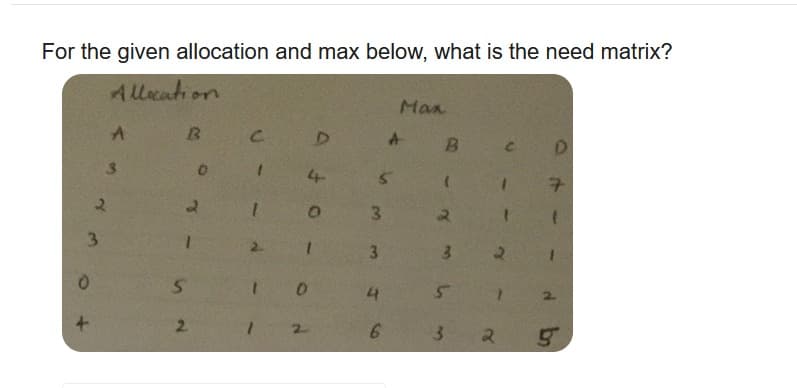
Q: For the given allocation and max below, what is the need matrix? Allocation 3 A B 5 2 0 с 1 D 4 O 1…
A: Allocation Matrix: The allocation matrix, which is a two-dimensional matrix, shows how many of each…
Q: OSI model
A: A theoretical framework known as the OSI (Open Systems Interconnection) model splits the functions…
Q: Discuss the role of magnetic tape storage in archival and backup systems, and its specific…
A: Because magnetic tape storage offers some benefits over other storage technologies, it has long been…
Q: Describe the concept of software-defined storage (SDS) and its advantages in modern data centers
A: Software-defined storage (SDS) is a management approach that decouples the software layer…
Q: Explain the purpose of routing protocols in computer networking. What are the key routing protocols…
A: Routing protocols have a role in computer networking as they enable data transmission across…
Q: Explain the concept of tunneling protocols and provide real-world examples of their applications in…
A: Tunneling protocols have a role in computer networking in Virtual Private Networks (VPNs). These…
Q: What is a network protocol, and why are they essential for data communication?
A: Network protocols are fundamental components of computer networks, serving as the foundation for…
Q: Describe the different types of hypervisors (Type 1 and Type 2) and their use cases.
A: Hypervisors are critical components in virtualization technology. They enable the creation and…
Q: Explore the challenges and solutions involved in managing distributed systems and cloud-based…
A: A distributed system in a cloud environment is a network of interconnected computers and resources…
Q: Discuss the role of hypervisors in virtualization technology. Compare and contrast Type 1 and Type 2…
A: The ability to create and maintain virtual machines (VMs) is what makes hypervisors essential to…
Q: What are the benefits of using virtualization in data centers and cloud computing?
A: With the assistance of cloud computing, IT arrangements can be made more versatile and versatile by…
Q: What is the output of the following program? list_1=[] list_1.append([1,(6,3),4]) print(list_1[0]…
A: Let's break it down step by step:list_1 is initialized as an empty list.list_1.append([1, (6, 3),…
Q: What is SAN (Storage Area Network), and how does it differ from NAS in terms of architecture and…
A: Block-level storage for high-performance, mission-critical applications is provided via a Storage…
Q: Discuss the role of hardware-assisted virtualization (VT-x/AMD-V) in virtualization. How does it…
A: Virtualization:Virtualization is a technology or process that allows you to create multiple virtual…
Step by step
Solved in 3 steps

- 357. An allocation that uses a proportional allocation scheme using priorities rather than size. a. Priority allocation b. File allocation c. Preference allocation d. Simple allocation[15 marks] Let M be the NDFSM below. Construct a DFSM that accepts ¬L(M). Show your work using the algorithm ndfintodfsm (Rich 2008, page 75). 8, 6 2 b b a.b aWhat does the following code segment and subroutine do? .equ SIZE =128.equ TABLE_L =$60.equ TABLE_H =$00 rjmp RESET .def A =r13.def B =r14.def cnt2 =r15.def cnt1 =r16.def endL =r17.def endH =r18 mystery: mov ZL,endLmov ZH,endHmov cnt2,cnt1i_loop: ld A,Z ld B,-Z cp A,B brlo L1 st Z,A std z+1,BL1: dec cnt2 brne i_loop dec cnt1 brne mystery ret Converts temperature values from one scale to another Adds a constant to a table of bytes Sorts numbers in ascending order Converts ASCII characters from lower case to upper case
- Given R ( A int, B int, C int ). Consider this select statement: Select R1.A, R1.B, R1.C from R R1 join R R2 on R1.A = R2.B where R1.A mod 2 = 0 and R2.B = R2.C Show the EXPLAIN PLAN for the table and statement Identify one or more indexes that might improve performance. Show the EXPLAIN PLAN and describe if you have made improvements in the execution.In elementwise multiplication A.*B each value in one matrix is paired up with a buddy value in the other and they are multiplied together.In matrix multiplication A*B each row in matrix A is dot-producted with each column in matrix B.The value in the upper left corner of the matrix C is the same as which of the following?C = A*B; options: A(1,1) * B(1,1) dot(A(1,:),B(:,1)) A = [3 1; 5 2];B = [1 -1; 4 0];C = A*Bthe value in the upper left corner of the matrix C is which of the following? % Starting with this code:a = [1 2 3]b = [-1 0 1]% All of the following are identical, except which one? Question 4 options: dot(a,b) a*transpose(b) b*transpose(a) sum(a.*b) They are all identical Fill in the blank to calculate the dot product of amounts and costs.amounts = [2 1 2 5 1]costs = [3.5 1.25 4.25 1.55 3.15]____________ Question 5 options:…Hello, I am having an error and cannot figure out how to solve this question. Could someone please assist? Please be advised, I am using PostgreSQL as that is what was used in class. Thus, I must use PLPGSQL Code CREATE OR REPLACE FUNCTION Moreno_03_bankTriggerFunction()RETURNS TRIGGERLANGUAGE PLPGSQLAS$$CREATE TRIGGER Wise_12_bankTriggerAFTER DELETE ON accountFOR EACH ROW EXECUTE PROCEDURE Moreno_15_bankTriggerFunction();
- Given code that reads user IDs (until -1), complete the quicksort() and partition() functions to sort the IDs in ascending order using the Quicksort algorithm. Increment the global variable num_calls in quicksort() to keep track of how many times quicksort() is called. The given code outputs num_calls followed by the sorted IDs. Ex: If the input is: kaylasimms julia myron1994 kaylajones -1 the output is: 7 julia kaylajones kaylasimms myron1994 I am having issues getting the count correct. What should I be looking at to adjust the count?When is a binary search best applied?Fill in the tables using scheduling algorithms mentioned. Use priority 1 as lowest and 4 highest
- 1. Given the following hash function for storing records on courses:f(title) = ASCII value of first character in the title - 64Example: f(Biology I) = 66 – 65 = 1 (ASCII value of B is 66) a. Explain why this is or is not a good hash function.b. What improvement(s) could be made? 2. Assume that the hash function is: f(key) = key % Ba. What is the problem if B is too small?b. What is the problem if B is too large?c. What is the big-0 run-time if there are n records?d. What does the run-time for a find, insert, and delete each approach as B gets verylarge?Modify pipe4.cpp so that it accepts a message from the keyboard and sends it to pipe5. //pipe4.cpp (data producer) #include <unistd.h> #include <stdlib.h> #include <stdio.h> #include <string.h> int main() { int data_processed; int file_pipes[2]; const char some_data[] = "123"; char buffer[BUFSIZ + 1]; pid_t fork_result; memset(buffer, '\0', sizeof(buffer)); if (pipe(file_pipes) == 0) { //creates pipe fork_result = fork(); if (fork_result == (pid_t)-1) { //fork fails fprintf(stderr, "Fork failure"); exit(EXIT_FAILURE); } if (fork_result == 0) { //child sprintf(buffer, "%d", file_pipes[0]); (void)execl("pipe5", "pipe5", buffer, (char *)0); exit(EXIT_FAILURE); } else { //parent data_processed = write(file_pipes[1], some_data, strlen(some_data));…Read on the functions and operations of numpy and pandas. Load the given data set into Google Colab python 1. In USD, find the average salary of Data Scientists as well as the standard deviation. 2. List each unique Job Title 3. For each unique Job Title, find their average salary (USD) and standard deviations. 4. Download the file as .ipynb to pass it on this activity file: https://uc-bcf.instructure.com/courses/28339/files/5680123/download?download_frd=1&verifier=fXym8nGyMe7CmvKYy7QmRDfcunF4DZwhuqakH1rL











