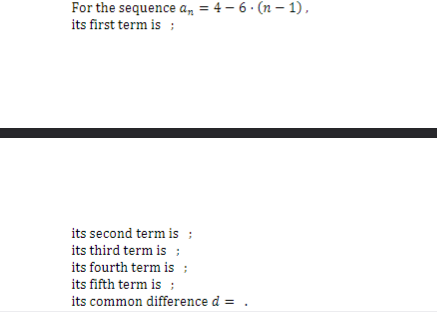
For the sequence a₂ = 4-6. (n-1), its first term is : its second term is ; its third term is : its fourth term is : its fifth term is : its common difference d
Q: What is the difference between encryption and hashing? Explain their respective use cases and why…
A: AspectEncryptionHashingPurposeProtects data confidentiality during transmission or storageEnsures…
Q: What do the cornerstones of software engineering neglect to account for? Explain?
A: The creation of high-quality software is governed by fundamental principles and best practices in…
Q: I am at wit's end on how to incorporate File I/O into my C++ program. After learning on Udemy I am…
A: Include necessary header files: iostream, fstream, and string.Define the function mixColors that…
Q: See how emerging countries utilize wireless networks. Several firms have abandoned their LANs and…
A: In recent years, emerging countries have increasingly embraced wireless networks as a means of…
Q: Could you provide more detail on the metrics that are considered over the course of the software…
A: In the software development various metrics are used to assess progress,quality,and efficiency.These…
Q: In your daily life, do you use databases or applications that use databases? Consider if you use…
A: I can provide insights into how databases are commonly used in various scenarios, including work,…
Q: ava program that will display the student's information. The program should perform the folowing: •…
A: The question is about creating a Java program to display a student's information and calculate the…
Q: What is a default and conversion constructor?
A: In object-oriented programming, a constructor is a special member function within a class that is…
Q: Matlab: How do I convert a matrix into a cell array? When I try to convert for some reason my cellA…
A: For the above code something is not defined properly . That is the matrix A and B Because in MATLAB…
Q: C++ 1 year = 15 months 1 month = 30 days write a function that takes an int parameter that…
A: logic:- number of days as per the given requirement will be calculated by multiplying 15 months*30…
Q: Because you have the benefit of, using pre-written software packages is the most convenient option?
A: Software reuse is a way where available software resources are used to build out of bed new…
Q: What is the importance of linux partitioning?
A: Linux partitioning is the process of splitting a physical disc into distinct areas or partitions,…
Q: How can the method of doing a literature review be used to enhance the development of an IT system?
A: The development of an IT system involves the process of designing, building, and implementing…
Q: Why is a modem needed when a phone line may be directly connected to a communication device?
A: A modem, short for modulator-demodulator, is essential to modern computer networking.It converts…
Q: 3. Write an if/elif/else sequence. 4. Use elif in a function definition. The command elif can be…
A: 1. Start the program.2. Define a function called `find_capital` that takes a parameter `state` (the…
Q: When acquiring proficiency in a novel programming language, what are two prevalent activities or…
A: 1) A novel programming language refers to a programming language that is new, innovative, or…
Q: What are the advantages of writing documentation for source code?
A: 1) Documentation for source code refers to written information and explanations that accompany the…
Q: It is necessary to provide a more in-depth description of the metrics that are used in the process…
A: Software development metrics are standards used to measure different aspects of a software…
Q: s are involved in the Data Loading test in Database testing?.
A: Data Loading test in Database testing is a specific type of testing that focuses on verifying the…
Q: For a programmer who possesses proficiency in multiple programming languages, it is imperative to…
A: In an ever-evolving technical landscape, learning new-fangled indoctrination language is a dangerous…
Q: 12 Explain the framework in software development?
A: A framework is a pre-established structure or set of guidelines that provide a foundation for…
Q: How do you characterize the steps used to start up the router?
A: The router performs a Power-On Self Test (POST) during startup to ensure the device's basic hardware…
Q: What are your four primary justifications for the significance of continuous event simulation?
A: Continuous event simulation has become increasingly popular in recent times due to its ability to…
Q: What is the most effective methodology for acquiring Application Programming Software? Is it…
A: Application Programming Software, refers to a specialized set of tools and programs that enable…
Q: ny individuals in so many different professions use comput
A: In our contemporary world, computers have become an integral part of life, transcending boundaries…
Q: What are three different applications of discrete event simulation?
A: Manufacturing is one of the substantial areas where disconnected event simulation (DES) plays a…
Q: The following recursive method get Number Equal searches the array x of n integers for occurrences…
A: The concept of recursion in programming refers to a situation where a function, in the process of…
Q: Code for implement insertion sort in java.
A: Insertion sort is a sorting algorithm that works by inserting each element from an array into its…
Q: What use would it be for a programmer to learn yet another programming language if they already have…
A: Learning a new programming language, even when one has a solid foundation in several others, can…
Q: Suppose that A = {red, blue} B = {green, yellow, amethyst). Then the cardinality of AxB is A. 5 B. 6…
A: calculate the cardinality of the Cartesian product A × B.A=[red, blue) B= (green. yellow. amethyst)
Q: Could you please provide an overview of the program's functions?
A: In CPU science, a program's function represents a code segment designed to perform a specific…
Q: Why would a firm promote proprietary encryption over open-standard cryptography?
A: Proprietary encryption allows a firm to maintain complete control over its security design. This…
Q: What is the minimum number of temporary registers (i.e., in addition to R2, R3, and R5 registers)…
A: It is asked how many extra registers are needed to compute the value of R5 <-- (R5 - R3 + R5 -…
Q: What exactly is the algorithm for fingerprinting, and how does it function? Please explain how it…
A: In palmtop art and cybersecurity, a fingerprinting algorithm is a computational method that…
Q: What are error-detection protocols?
A: Error-detection protocols are methods used in computer networks to identify and detect errors or…
Q: A palindrome is a word or phrase that is identical when you read from forward or backward, such as…
A: In this question we have to write a PHP based web program which will check for the string palindrome…
Q: What are the four primary justifications for the significance of continuous event simulation?
A: A continuous event simulation is a specialized form used predominantly in fields involving ongoing…
Q: Explain how each device in a mesh architecture has its own unique topology for multipoint…
A: Mesh building refers to a type of net design where each network node a CPU, router, or switch is…
Q: Let U be the universal set, where: U = {1,2,3,4,5,6,7,8,9,10,11,12,13,14,15,16,17,18} Let sets A, B,…
A: In this question we have to perform set operations, specifically finding the union and intersection…
Q: An error-displaying four-year-old laptop won't start. The laptop's tech support verified that the…
A: When encountering a non-functional laptop with verified motherboard issues, it is crucial to proceed…
Q: What are the key differences between HTTP and HTTPS protocols, and why is it crucial for websites to…
A:
Q: Locate two online GSS software choices for group decision-making?
A: Group Support Systems (GSS), or Group Decision Support Systems (GDSS), are computer-based in…
Q: How to perform matri
A: The question is to write a Java program that performs matrix operations, including addition,…
Q: Why is it necessary to have a modem placed in between a comm adaptor and a phone line?
A: In the world of telecommunications, connecting devices to phone lines for data transfer has always…
Q: Would it be feasible for you to describe the metrics that are used in the process of software…
A: In software development, metrics are essential tools for measuring and evaluating various aspects of…
Q: What is the most effective approach to obtain access to the documentation for Visual Studio? What…
A: Visual Studio is the best integrated development environment (IDE).Provided by Microsoft and used by…
Q: In the context of technical writing, what do you think the function of screencasting may be? What do…
A: Screencasting, the digital recording of computer screen output, often audio narration, is crucial to…
Q: 1 year = 15 months 1 month = 30 days write a function that takes an int parameter that represents…
A: This function can be defined in such a way that it is used to find details by dividing the entered…
Q: For what purpose does software have to be "good enough"?
A: In software development, the idea of "good enough" means creating software that does what it needs…
Q: class Linked List ( static class Node { int data; Node next; Node (int data) { this.data = data; } }…
A: Here is the java code of the above problem.See below steps for code.
Please explain the answer and show the souloution ! f12
Step by step
Solved in 4 steps

- Dynamic programming: Find the Longest Common Subsequence (LCS) for 10010101 and 010110110. Justify your answer.Longest Common Subsequence:ExampleLCS for input Sequences “ABCDGH” and “AEDFHR” is “ADH” of length 3.LCS for input Sequences “AGGTAB” and “GXTXAYB” is “GTAB” of length 4.Implementation in Java.actoring is a powerful simplification technique in Boolean algebra, just as it is in real-number algebra. Show how you can use factoring to help simplify the following Boolean expressions: A. F = Y + YZB. F = XY’Z + XY’Z’
- With explaining pleaseSimplify the following Boolean expressions, using four-variable K-maps: AB′C+B′C′D′+BCD+ACD′+A′B′C+A′BC′DComputer Science For the following lambda calculus term, reduce it to a normal form. Be careful with parentheses and show every beta-reduction step. (lambda n. lambda m. lambda f. lambda x. m f (n f x)) (lambda f. lambda x. f x) (lambda f. lambda x. f (f x))

