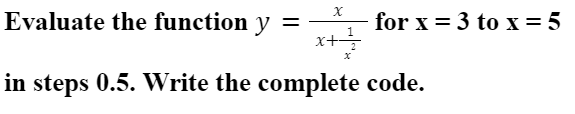
for x = 3 to x = 5 x+ Evaluate the function y in steps 0.5. Write the complete code.
Q: lass C” network is div
A: Subnet Mask and IP Address On an IP network, a 32-bit IP address uniquely identifies a single device...
Q: In nodejs. Add a new GET endpoint, /hello/name, which takes as query parameters a first and last par...
A: firstName with the value of first and last Name with the vale of last
Q: What is the command “make" and the file "Makefile" ? can you execute the c program without prefixing...
A: Solution: The 'make' command and 'makefile' : The make command requires the file for the execution, ...
Q: Differentiate between two widely utilised system development techniques. What are the key advantages...
A: The question is differentiate between two widely utilised system development techniques and what are...
Q: write a JAVA program to input a positive integer from the user and print true in the output if the n...
A: Required:- write a JAVA program to input a positive integer from the user and print true in the outp...
Q: What is the normal relationship between an untrusted network, a firewall, and a trusted network, and...
A: Introduction: Because of powerful firewalls, computers on trusted networks are more safe and secret....
Q: When referring to the GOTO saga and spaghetti code, What was demonstrated by the Structured Programm...
A: Introduction: With regard to spaghetti code and the GOTO issue, we must explain what the Structured ...
Q: What is the objective of Access Security Software?
A: Introduction: The idea is to give people access to only the data that is considered necessary for th...
Q: What is the point of leaving a data object out of a data model?
A: Introduction: The foundation of an object data model based on object-oriented programming is the ass...
Q: Which transport protocol (connectionless or connection oriented) is used to implement the HTTP appli...
A: Which transport protocol (connectionless or connection oriented) is used to implement the HTTP appli...
Q: Write a Java program to print the given pattern: GHIJ DEF ВС
A: Java is one of the languages, which is considerably used in many sectors of Computer. In older time...
Q: How do you verify that each machine in an IPsec network utilises its own private key pair if you're ...
A: The Internet P Security Architecture (IPsec) gives cryptographic insurance to IP datagrams in IPv4 a...
Q: Explain and describe the fundamental goals of artificial intelligence (AI) systems.
A: Given To describe the primary objective of artificial intelligence (AI) systems.
Q: computer science -Why aren't technological advancements like computers and phones regarded as adapta...
A: Introduction: The world is changing at breakneck speed as a result of technological advancements in ...
Q: I have a code for an assignment, but the code isn't working please help me. The code of the resourc...
A: The exception shown in the picture occurs when we try to access the file which is not available in t...
Q: A home security company for an apartment complex, HSS, wants to automate its manual functions using ...
A: Racial bias and misinformation, racial discrimination in law enforcement, privacy, lack of informed ...
Q: Given the fact that the globe is running out of IP addresses, what is likely to happen with IP addre...
A: Introduction: From small to big businesses, there were often more computers than IP addresses availa...
Q: Write the following in machine language or low level language
A: Full Name 01000110 01110101 01101100 01101100 00100000 01001110 01100001 01101101 01100101 Index Nu...
Q: What is regression testing?
A: Introduction: In this instance, regression refers to a previously fixed software bug that has return...
Q: Identify and describe two of the predicted virtualized operating system consequences.
A: Introduction: Virtualizаtiоn is a teсhnоlоgy that isolates an application, guest operating system (g...
Q: What difference does clustering (k-means) with and without normalisation make?
A: Introduction: K-means clustering is a vector quantization method for dividing n observations into k ...
Q: Which of the following are other key aims of operating systems, in addition to virtualization, concu...
A: Operating system is the key driver of a system.
Q: In what capacity does a router function?
A: Capacity: A home router might theoretically have 254 devices connected to it. This is due to the IP ...
Q: Computer science A cybersecurity vulnerability can be analysed in a variety of ways.
A: Introduction: A cybersecurity vulnerability can be analyzed in a variety of ways. Its purpose is to ...
Q: Describe briefly why the usual Method (Non-Formal) of software development will not be effective for...
A: Introduction: Non-formal software development is a way of software development that relies on the vi...
Q: What is a database, and what are the applications of databases?
A: Introduction: In the 1960s, the first database was built. Early databases employed network models, i...
Q: write a JAVA program to input a positive integer from the user and print true in the output if the n...
A: import java.util.Scanner; public class Main{ //Function to count number of digits in a number. ...
Q: Explain the difference between the limited and unbounded implementations of the stack.
A: A stack is an abstract data type. It is a container that follows the last in first out (LIFO) rule. ...
Q: It is common practice in the system development process to use the computer-aided software engineeri...
A: It is common practice in the system development process to use the computer-aided software enginee...
Q: A computer's central processing unit (CPU) is in charge of executing software instructions.
A: Defined the given statement
Q: What does the digital gap in the United States look like in comparison to the worldwide digital divi...
A: The digital gap refers to the gap between the people who can operate and access via modern technique...
Q: What exactly is technical documentation? What are the four main distinctions between technical docum...
A: Documentation Techniques The phrase "technical documentation" refers to a variety of publications th...
Q: Explain why record allocation to blocks has a significant impact on database system performance.
A: Introduction: A database system is made up of a list of tables, each of which has a row and a column...
Q: One of Vivobarefoot's recurring concerns is the quality and speed of the Internet access offered to ...
A: Introduction: To begin, we must understand cloud computing. Cloud computing is storing, processing, ...
Q: Programto compute the average of seven degree, and d if the student success, then print "pass" word,...
A: Here assume that if average is greater than or equal to 35, student is assumed to be pass. If averag...
Q: A student took four quizzes in a term and would like to compute their average. He also would like to...
A: Your question is so long, Please appreciate the work. Thank you. The answer is as follows: Answer 1:...
Q: Construct the digraph of a Moore machine with five different states that has input elements a, b, an...
A: Given: Input elements a,b and accepts the input strings end with baba.
Q: Suppose the two prime numbers p = 23 and q = 37 are used for an RSA encryption scheme. What are the ...
A: Below is the answer to above question. I hope this will meet your requirements...
Q: Which of the following terms refers to the technique of grouping redundant resources such as servers...
A: Kindly Note: As per our guidelines we are supposed to answer only one question. Kindly repost other ...
Q: Is it true or false? Use the # sign in front of a line of code to comment it out.
A: Answer: The answer to the given statement "Use the # sign in front of a line of code to comment it o...
Q: How can the usage of microchips worn by troops, sometimes known as wearable computers, be merged int...
A: Given: Utilization of microchips worn by soldiers, or wearable computers, be integrated into civil...
Q: Why isn't a data item represented in a data model?
A: It is possible to think of a data model as an abstract model that organizes and standardizes data co...
Q: A - np. array ( (1, 2, 31, (4, 5, 6), [7, 8, 9] B - np.array ( (1, 2, 31, [4, 5, 61, [7, 8, 91 1) C ...
A: flow chart for 3D array
Q: program. Again, make a flowchart, I have already coded the program all you have to do is to make a f...
A: Flow chart is a pictorial description of the algorithm.
Q: House +numberRoom:int +tyee:String. +Displaxlnto(); Bungalow +location:String +gwnerName:Striog. Ris...
A: Here is The Solution. public class House{ public int numberRoom; public String type; ...
Q: Prepared Statements are more efficient. Why?
A: Given To know about the Prepared Statements
Q: --Problem -3 -Create a flowchart design that depicts the solving of the following problem: Asks user...
A: Please refer to the following step for the complete solution of the problem above.
Q: What is vector imaging and how does it work? Give an example to elucidate your point? What are the f...
A: Vector pictures include mathematical formulae that depict lines, curves, circles, rectangles, and ot...
Q: Computer science What are some of the most fundamental database functions that a spreadsheet can't ...
A: Introduction: A database is structured in a logical, consistent, and internally consistent manner. F...
Q: When it comes to iOS, what is the difference between the IPA and.am extensions?
A: In this question we have to discuss about the IPA and .am extensions First we will look into what bo...
item#3
Step by step
Solved in 4 steps with 2 images

- Write the definition of a function that takes as input two decimal numbers and returns first number to the power of the second number plus second number to the power of the first number. (4)(Numerical) Heron’s formula for the area, A, of a triangle with sides of length a, b, and c is A=s(sa)(sb)(sc) where s=(a+b+c)2 Write, test, and execute a function that accepts the values of a, b, and c as parameters from a calling function, and then calculates the values of sand[s(sa)(sb)(sc)]. If this quantity is positive, the function calculates A. If the quantity is negative, a, b, and c do not form a triangle, and the function should set A=1. The value of A should be returned by the function.In the function XZ̅ + Y, if X is false, Z is false, Y is true then the whole statement is False Unknown Wrong True
- C++ Write a function that takes as input a positive integer n and returns the n-th harmonic number.Reminder: the n-th harmonic number is equal to 1+(1/2)+(1/3)+(1/4)+...+(1/n)Write a function that returns the average of the first N numbers,where N is a parameter.Please write out the code for this function using R.
- The correct prototype for the following function heading is void F1(int &p1, double &p2, bool &p3)Write a function that takes as inputs the 3 sides of a triangle and returns true if it is a right triangle and false otherwise.write a function that returns a value to main and identifies if an integer number is odd or even. for example your function could be: int odd_even(int num) { if (num%2==0) return 0; .......
- float theRealQuestion (int x, float y) { int z; if (x > 15) z = x; else z = y; return z; } Code the function prototype for the given function.Write a function that receives 5 integers and returns the sum, average and standard deviation of these numbers. Call this function from main() and print the results in main().Write a for loop with a range function for even numbers. Write a for loop with a range function for odd numbers. Use a variable called calc to calculate the sum of even and odd numbers. Print the computation of each even number plus the odd number equal to calc to the terminal.





