From the ATTACHED picture of a sample PS script, explain the below questions 8 to 11: 8. That is the reason for the comment [#] in line one? 9. What does line three indicate? 10. What does the “node” declaration in line six mean? 11. How many DSC resource types are defined in this script and name them.
From the ATTACHED picture of a sample PS script, explain the below questions 8 to 11: 8. That is the reason for the comment [#] in line one? 9. What does line three indicate? 10. What does the “node” declaration in line six mean? 11. How many DSC resource types are defined in this script and name them.
Chapter7: Working With The Bash Shell
Section: Chapter Questions
Problem 5DE
Related questions
Question
100%
Book reference: Windows PowerShell Step by Step 3rd Edition - Ed Wilson
Chapter 21
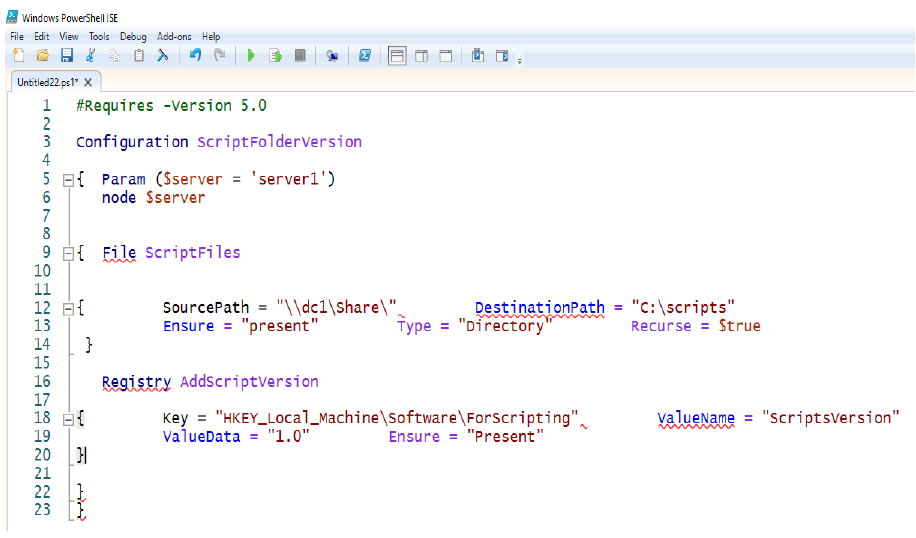
From the ATTACHED picture of a sample PS script, explain the below questions 8 to 11:
8. That is the reason for the comment [#] in line one?
9. What does line three indicate?
10. What does the “node” declaration in line six mean?
11. How many DSC resource types are defined in this script and name them.
Transcribed Image Text:Windows PowerShell ISE
File Edit View Tools Debug Add-ons Help
Untitled22 ps1" X
#Requires -Version 5.0
2
3
1
Configuration scriptFolderversion
4
5 ạ{ Param (Sserver = 'server1')
6
7
8
node $server
9 H{ Eile scriptFiles
10
11
12 B{
13
SourcePath = "\ldc1\Share\",
Ensure = "present"
DestinationPath = "c:\scripts"
Recurse = Strue
Type = "Directory
14
15
Registry AddscriptVersion
16
17
18 É{
Key = "HKEY_Local_Machine\Software\ForScripting",
ValueData = "1.0"
valuename = "scriptsVersion"
19
Ensure = "Present"
20
21
22
23
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Recommended textbooks for you

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,