Give an example for each of these macros to explain its work: Macro: int WIFSIGNALED (int status) This macro returns a nonzero value if the child process terminated because it received a signal that was not handled. Macro: int WTERMSIG (int status) If WIFSIGNALED is true of status, this macro returns the signal number of the signal that terminated the child process. Macro: int WCOREDUMP (int status) This macro returns a nonzero value if the child process terminated and produced a core dump. Macro: int WIFSTOPPED (int status) This macro returns a nonzero value if the child process is stopped. Macro: int WSTOPSIG (int status) If WIFSTOPPED is true of status, this macro returns the signal number of the signal that caused the child process to stop.
Give an example for each of these macros to explain its work: Macro: int WIFSIGNALED (int status) This macro returns a nonzero value if the child process terminated because it received a signal that was not handled. Macro: int WTERMSIG (int status) If WIFSIGNALED is true of status, this macro returns the signal number of the signal that terminated the child process. Macro: int WCOREDUMP (int status) This macro returns a nonzero value if the child process terminated and produced a core dump. Macro: int WIFSTOPPED (int status) This macro returns a nonzero value if the child process is stopped. Macro: int WSTOPSIG (int status) If WIFSTOPPED is true of status, this macro returns the signal number of the signal that caused the child process to stop.
Chapter7: Developing An Excel Application
Section: Chapter Questions
Problem 4.11CP
Related questions
Question
Please answer the following examples
ex 3 and 4 in C language and upload the code (text)
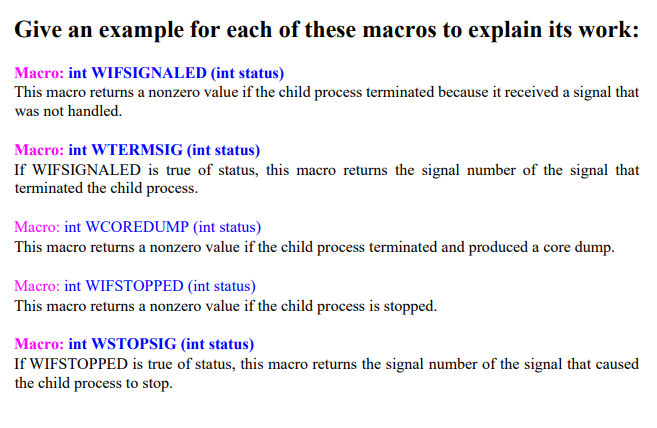
Transcribed Image Text:Give an example for each of these macros to explain its work:
Macro: int WIFSIGNALED (int status)
This macro returns a nonzero value if the child process terminated because it received a signal that
was not handled.
Macro: int WTERMSIG (int status)
If WIFSIGNALED is true of status, this macro returns the signal number of the signal that
terminated the child process.
Macro: int WCOREDUMP (int status)
This macro returns a nonzero value if the child process terminated and produced a core dump.
Macro: int WIFSTOPPED (int status)
This macro returns a nonzero value if the child process is stopped.
Macro: int WSTOPSIG (int status)
If WIFSTOPPED is true of status, this macro returns the signal number of the signal that caused
the child process to stop.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage